Optional book ($35)
Scripting for IT and Security Professionals (with Blockchains)
Mon, June 27 -
Fri, July 1, 2016
Sierra College, Rocklin
Sam Bowne
Home Page
Optional book ($33)
Free online version
Optional book ($35) |
Scripting for IT and Security Professionals (with Blockchains)Mon, June 27 -
Fri, July 1, 2016
|
Optional book ($33) |
SURVEYCourse DescriptionIT and security professionals who don't know coding should take this course. Attendees will learn fast, simple coding techniques by performing hands-on projects and competing to solve challenges. These skills are appropriate for prototypes, demonstrations, and proof-of-concept code. The focus on hacking and competition helps to keep students motivated and engaged.PrerequisitesFamiliarity with networking and security concepts at the Network+ and Security+ level would be best, but it's not required. No previous coding experience is required.ScheduleMonday, Tuesday & Thursday:8:30 - 9:00 Breakfast / Registration / Welcome: In the CafeteriaWednesday Regular schedule but ending early at 3:30Friday 9:00 - 12:00 Classes, in the V building |
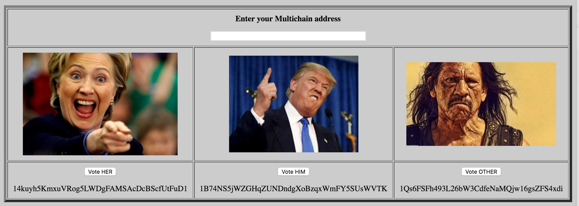
| Blockchain Voting Prototype | |
 |
|
LecturesReal Hacking (key)Data Breaches: Real and Imaginary (ppt) Bitcoin (key) Security at Colleges SSL Certificates at Banks NETLAB password insecurity Is Your Android App Secure? (ppt) Financial Android App Vulnerabilities Android App Security Auditing Workshop Hacking Mobile Devices Class Rindjael Encryption Animation (AES)
Some lectures are in Keynote format. |
Projects
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Cultural EnrichmentHow to view someones IP address and connection speed with TRACER T! - YouTube
|
DownloadsThe three machines used for the NETLAB projects are here:
|
Posted before 6-14-16 by Sam Bowne
Last revised 8-18-16