This is the #6 most important security flaw in mobile apps, according to OWASP.
Here's the locally-stored password, which is encrypted:
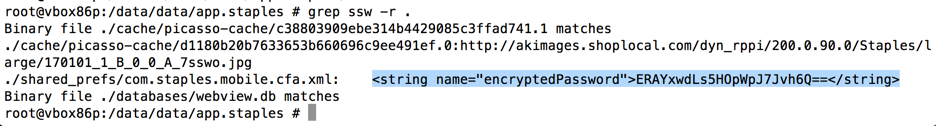
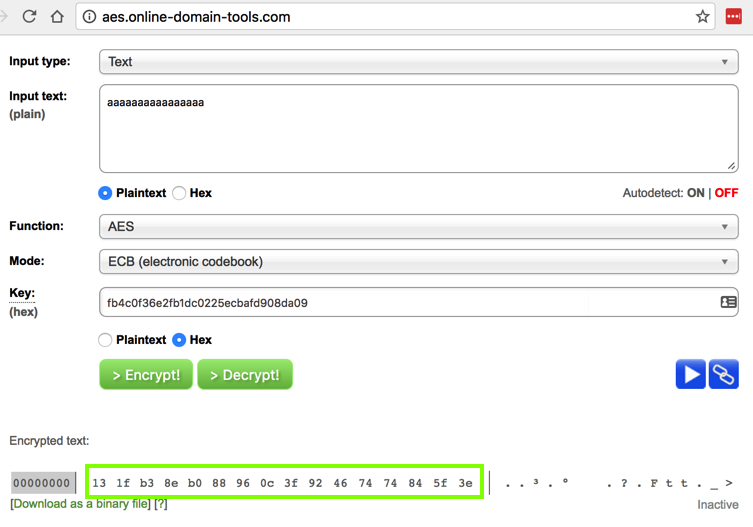
The encryption uses AES in ECB (Electronic Code Book) mode, as shown by making an account with this password:
aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa123A
Shows a longer encrypted password:
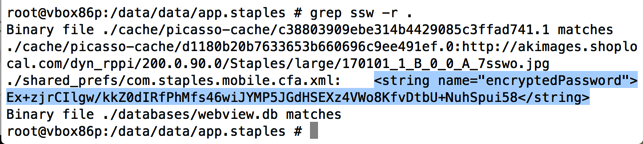
The encrypted password looks like this in base64:
Ex+zjrCIlgw/kkZ0dIRfPhMfs46wiJYMP5JGdHSEXz4VWo8KfvDtbU+NuhSpui58
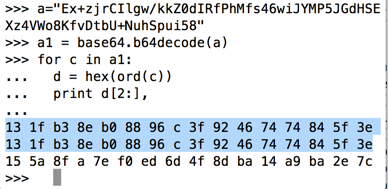
It's clear that the encrypted form of "aaaaaaaaaaaaaaaa" is
13 1f b3 8e b0 88 96 c 3f 92 46 74 74 84 5f 3e
3xtraS@lt
genericvbox86pGoogle Galaxy Nexus - API 18 - 720x1280
unknownapp.staples
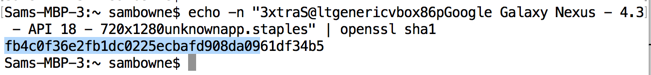
That key now reproduces the encryption of "aaaaaaaaaaaaaaaa", as outlined in green below.
Similarly, it would be easy to deduce the key from a stolen phone and recover the password.
If the password must be used to log in to remote servers, a system such as OAuth should be used to authenticate without needing to store the password itself.
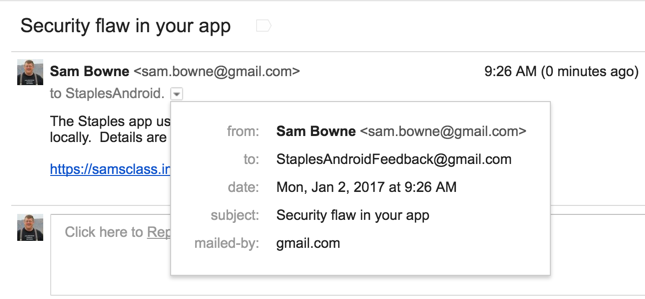
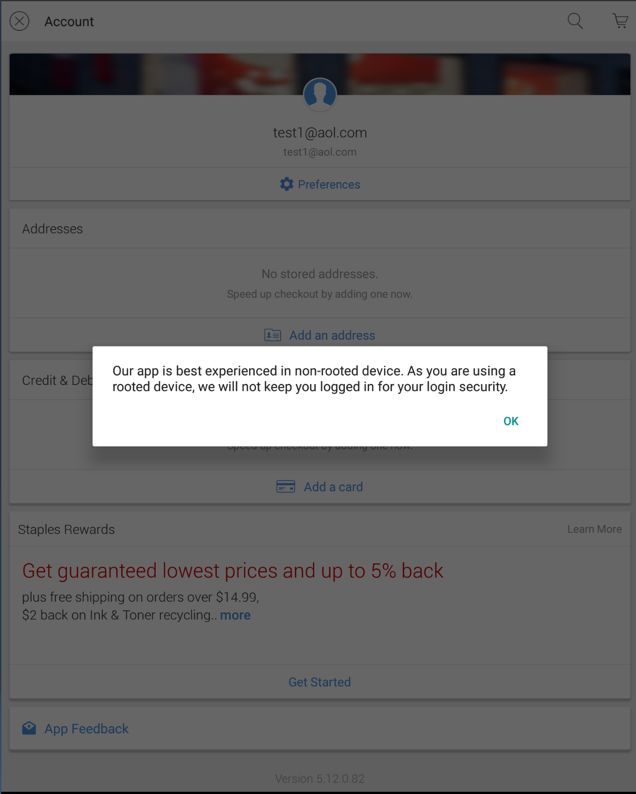
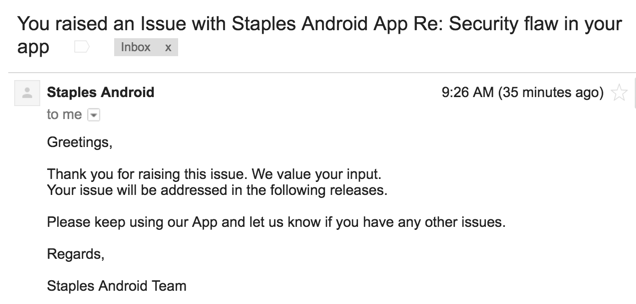
I got this automated reply immediately:
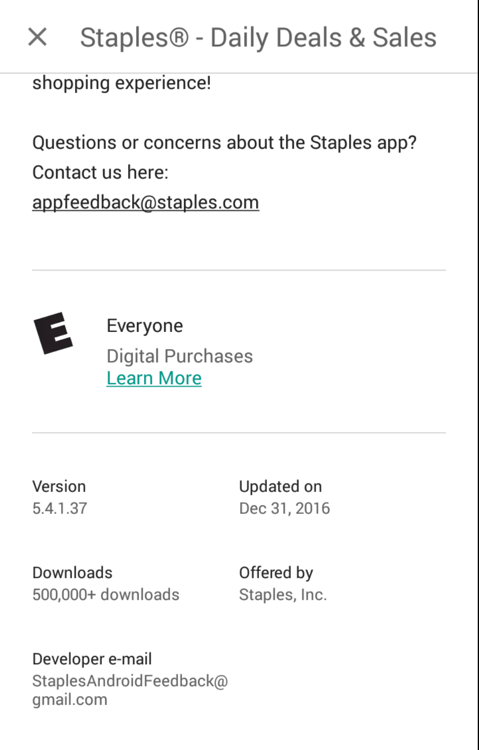
On Feb. 16, I asked them when the app would be fixed.
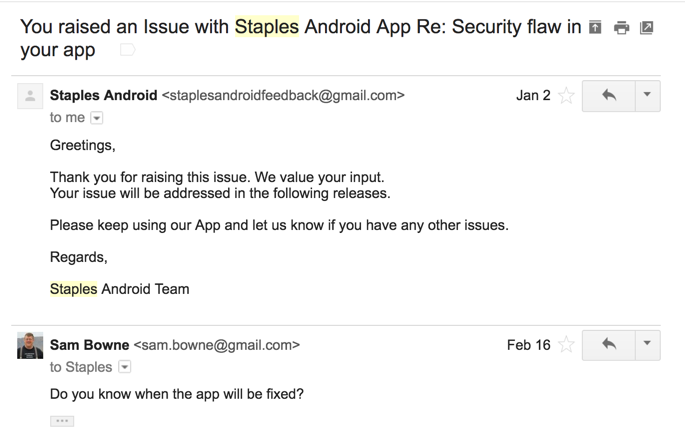
I never got any reply. I don't think anyone at Staples actually read any of my messages, and I don't believe any fix is coming. So I decided to disclose this publicly and use it for homework.
Here's the homework assignment.