CNIT 123
Ethical Hacking and Network Defense
Fall 2015 Sam Bowne
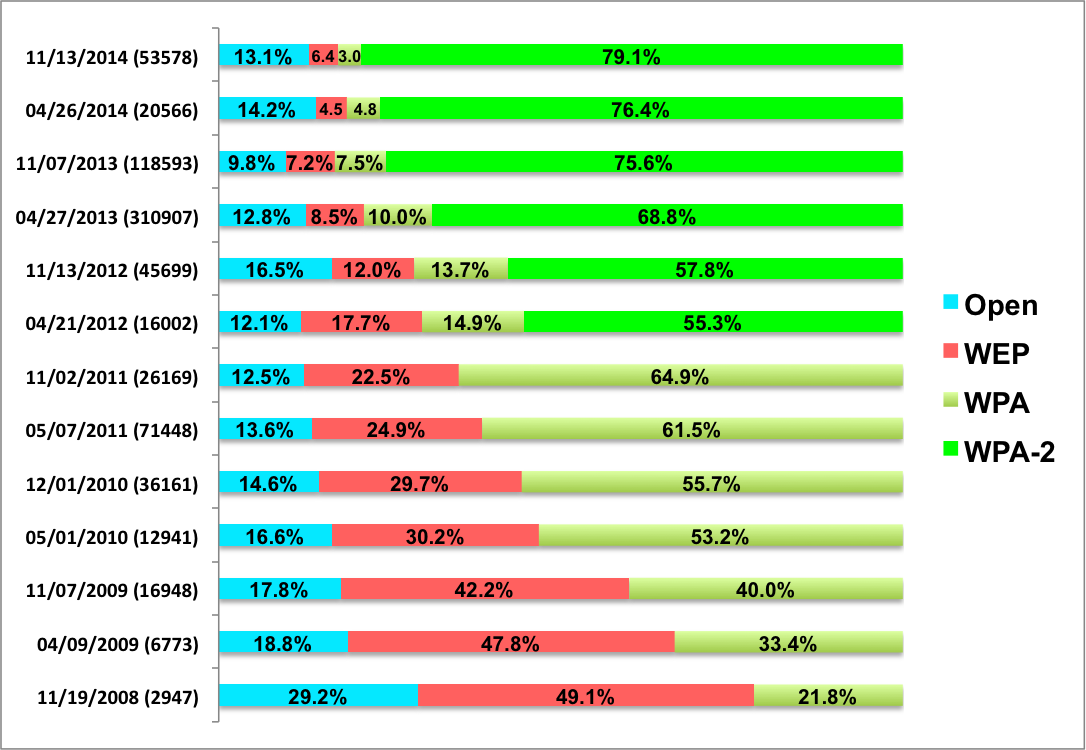
Wardriving Results
Schedule · Lecture Notes · Projects · Links · Forum · Bookshelf · Home Page
Scores
Open Lab Hours for Sci 214
CNIT 123
|
|
72250 Thur 6:10 - 9:00 pm SCIE 200
|
Catalog DescriptionStudents learn how hackers attack computers and networks, and how to protect systems from such attacks, using both Windows and Linux systems. Students will learn legal restrictions and ethical guidelines, and will be required to obey them. Students will perform many hands-on labs, both attacking and defending, using port scans, footprinting, exploiting Windows and Linux vulnerabilities, buffer overflow exploits, SQL injection, privilege escalation, Trojans, and backdoors.Prerequisites: CNIT 106 and 120 or equivalent familiarity with the fundamentals of networking and security. Upon successful completion of this course, the student will be able to:
Student Learning Outcomes (measured to guide course improvements)Perform port scans to locate potential entry points to servers and networks.Perform very simple scripting and coding tasks, specifically oriented towards the needs of network security professionals. Locate and hack into wireless networks, and protect them. TextbooksHands-On Ethical Hacking and Network Defense, Second Edition by Michael T. Simpson, Kent Backman, and James Corley -- ISBN: 1133935613 Buy from Amazon ($29) |
Schedule | ||||
|---|---|---|---|---|
| Date | Quiz | Topic | ||
| Thu 8-20 | Ch 1: Ethical Hacking Overview & Stupid Whitehat Tricks | |||
| Thu 8-27 | Ch 2: TCP/IP Concepts Review | |||
| Thu 9-3 | Ch 3: Network and Computer Attacks | |||
| Fri 9-4 | Last Day to Add Classes | |||
| Thu 9-10 | Quiz on Ch 1-3 Proj 1-3 due * |
Ch 4: Footprinting and Social Engineering | ||
| Thu 9-17 | Quiz on Ch 4 Proj 4 & 5 due |
Ch 5: Port Scanning | ||
| Thu 9-24 | Quiz on Ch 5 Proj 7 due |
Ch 6: Enumeration | ||
| Thu 10-1 | Quiz on Ch 6 Proj 6 & 9 due |
Ch 7: Programming for Security Professionals | ||
| Thu 10-8 | Quiz on Ch 7 Proj 8 & 10 |
Ch 8: Desktop and Server OS Vulnerabilites | ||
| Thu 10-15 | Quiz on Ch 8 Proj 12 |
Ch 9: Embedded Operating Systems: The Hidden Threat | ||
| Thu 10-22 | Quiz on Ch 9 Proj 11 & 13 Due * |
Ch 10: Hacking Web Servers | ||
| Mon 10-26 | Mid-Term Grades Due | |||
| Thu 10-29 | No Quiz Proj 14 & 15 due |
| ||
| Thu 11-5 | Quiz on Ch 10 Proj 16 & 17 due |
Ch 11: Hacking Wireless Networks | ||
| Thu 11-12 | Wardriving No Quiz, no Proj due |
|
||
| Thu 11-19 | Quiz on Ch 11 Proj 18 & 19 due |
Ch 12: Cryptography | ||
| Thu 11-22 | Holiday - No Class | |||
| Thu 12-3 | Quiz on Ch 12 Proj 20 & 21 due |
Ch 13: Network Protection Systems | ||
| Thu 12-10 |
All Extra Credit Proj due Proj 22 due, No Quiz |
Last Class: Intro to Malware Analysis | ||
| Thu 12-17 | Final Exam | |||
| * Project requires DVD--available in S214 | ||||
Lecture Notes | |
|---|---|
| Policy | |
| Student Agreement | |
| Code of Ethics | |
| Stupid Whitehat Tricks in the HOPE X Section Here | |
The chapter lectures are password-protected becauseCh 1: Ethical Hacking Overview Powerpoint | |
| Ch 2: TCP/IP Concepts Review Powerpoint | |
| Ch 3: Network and Computer Attacks Powerpoint | |
| Ch 4: Footprinting and Social Engineering Powerpoint | |
| Ch 5: Port Scanning Powerpoint | |
| Ch 6: Enumeration Powerpoint | |
| Ch 7: Programming for Security Professionals Powerpoint | |
| Ch 8: Desktop and Server OS Vulnerabilites Powerpoint | |
| Ch 9: Embedded Operating Systems: The Hidden Threat Powerpoint | |
| Ch 10: Hacking Web Servers Powerpoint | |
| Ch 11: Hacking Wireless Networks Powerpoint | |
| Ch 12: Cryptography Powerpoint | |
| Ch 13: Network Protection Systems Powerpoint | |
The lectures are inPowerPoint format. | |