http://windows.microsoft.com/en-us/windows/change-password-policy-settings#1TC=windows-7
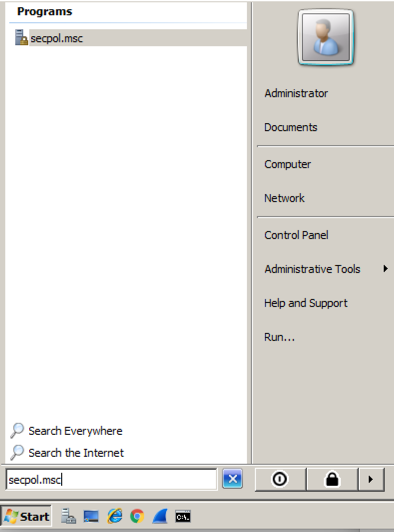
Click Start and type in
secpol.msc
In Local Security Policy, in the left pane, click the + sign to expand "Account Policies", as shown below.
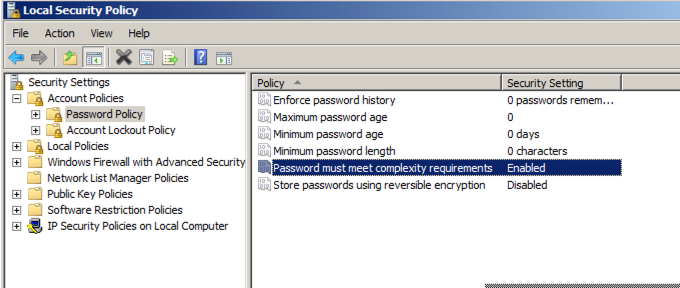
In the left pane, click "Password Policy".
In the right pane, double-click "Password must meet complexity requirements".
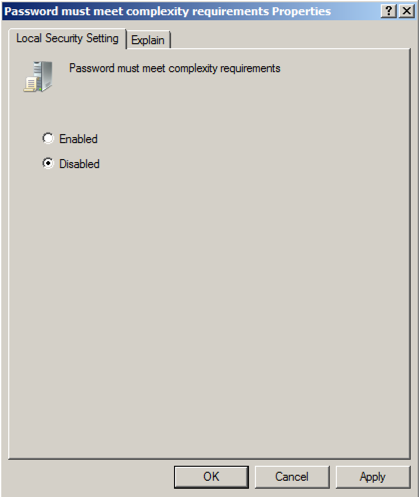
In the "Password must meet complexity requirements Properties" box, click Disabled, as shown below.
Then click OK.
In the Administrator Command Prompt window, execute these commands:
net user p3 abc /add
net user p5 abcde /add
net user p7 abcdefg /add
proj10/ca_setup-4-9-56.7zUnzip the downloaded file with 7-Zip, using the password sam
If you don't have 7-Zip, get it here:
http://www.7-zip.org/
If a "User Account Control" box appears, click Yes.
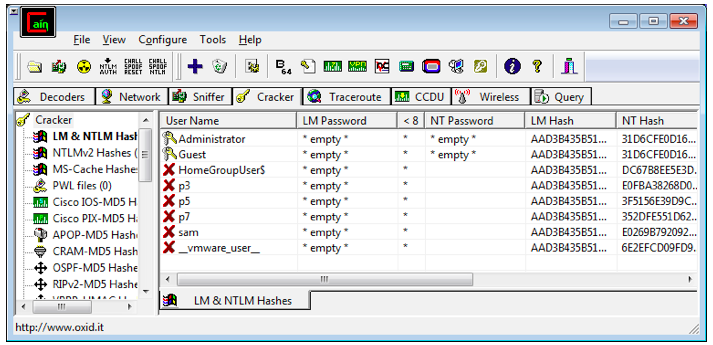
In the Cain window, at the top, click the Cracker tab. Move the mouse to the center right, where a blank white pane appears with a gray grid.
Right-click and click "Add to list". In the "Add NT Hashes from" box, click Next.
The password hashes appear, as shown in the figure below. The LM hashes will all be the same if you are using Windows Vista or later, but the NT hash contains the password information.
Troubleshooting
If Cain won't install, you may need the fix in this video:
You can download the file you need here:
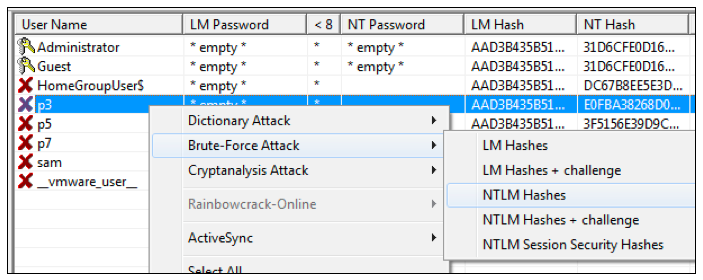
In the "Brute-Force Attack" box, click the Start button. It should find the three-letter password immediately. Close the "Brute-Force Attack" box.
In the right pane, right-click p5, point to "Brute-Force Attack", and click "NTLM Hashes".
In the "Brute-Force Attack" box, click the Start button. It should find the five-letter password within a few seconds. Close the "Brute-Force Attack" box.
In the right pane, right-click p7, point to "Brute-Force Attack", and click "NTLM Hashes".
In the "Brute-Force Attack" box, click the Start button. The seven-letter password is hard to crack, however– no answer appears immediately. It might take a long time to crack, so we'll give up. Click the Stop button. Click the Exit button.
You should see the two passwords you found, abc and abcde, in the NT Password column of the Cain window, as shown below.
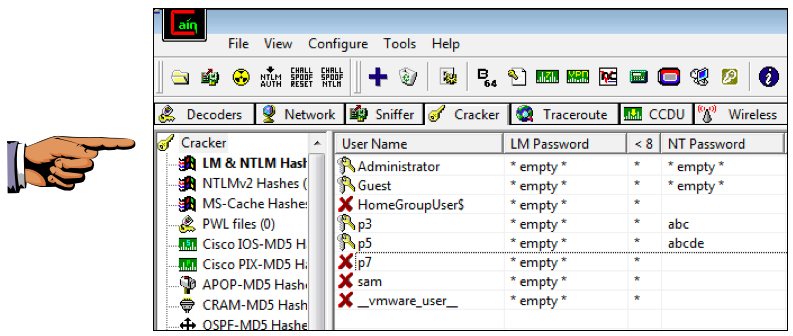
Press the PrintScrn key in the upper-right portion of the keyboard. That will copy the whole desktop to the clipboard.
YOU MUST SUBMIT A FULL-SCREEN IMAGE TO GET FULL CREDIT!
Open Paint and paste in the image.
Save the image with the filename "Your Name Proj 18". Use your real name, not the literal text "Your Name".
Last Modified: 4-21-18