
Hacking Mobile Devices
Schedule · Powerpoints · Projects · Links · Home Page

Hacking Mobile DevicesSchedule · Powerpoints · Projects · Links · Home Page |
|
Catalog DescriptionMobile devices such as smartphones and tablets are now used for making purchases, emails, social networking, and many other risky activities. These devices run specialized operating systems have many security problems. This class will cover how mobile operating systems and apps work, how to find and exploit vulnerabilities in them, and how to defend them. Topics will include phone call, voicemail, and SMS intrusion, jailbreaking, rooting, NFC attacks, malware, browser exploitation, and application vulnerabilities. Hands-on projects will include as many of these activities as are practical and legal.Prerequisite skills: Security knowledge at the Security+ level, and familiarity operating mobile devices such as smartphones and tablets Upon successful completion of this course, the student will be able to:
Textbook"Hacking Exposed Mobile: Security Secrets & Solutions", by Bergman, Stanfield, Rouse, Scambray, Geethakumar, Deshmukh, Matsumoto, Steven and Price, McGraw-Hill Osborne Media; 1 edition (July 9, 2013) ISBN-10: 0071817018 Buy from AmazonExample Vulnerability Report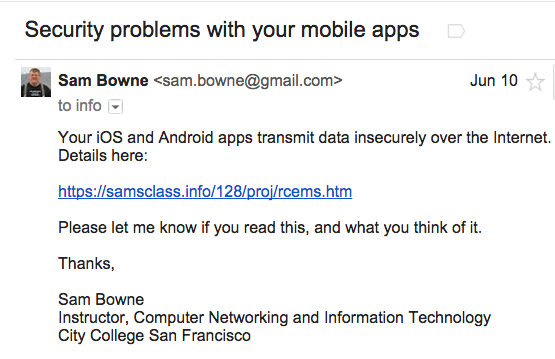
Example Proof of Concept Page for PlaintextExample Proof of Concept Page for Broken SSL |
Schedule | ||||
|---|---|---|---|---|
| Date | Topics | Projects | ||
| Mon 7-13 |
Motivation: Android Security Auditing Android and iOS Vulnerabilities Research
1: The mobile risk ecosystem | Proj. 1-3 | ||
| Tue 7-14 |
3: iOS 4: Android (Part 1) | Proj. 4-6 | ||
| Wed 7-15 |
4: Android (Part 2) 5: Mobile malware 6: Mobile services and mobile Web | Proj. 7-8 | ||
| Thu 7-16 |
7: Mobile Device Management 8: Mobile development security 9: Mobile payments | Proj. 10, 6x, 11 | ||
| Fri 7-17 | To Be Announced | To Be Announced | ||