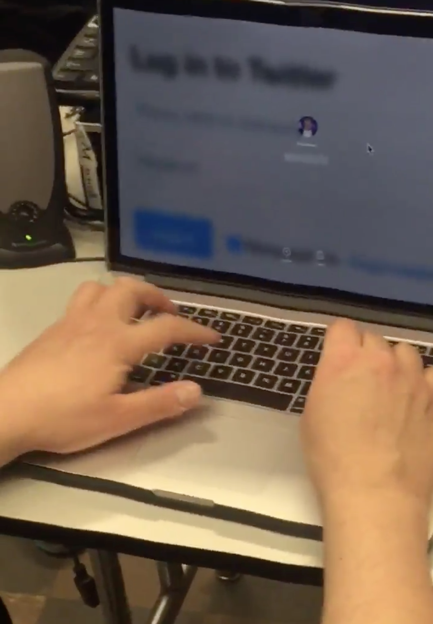

3-9-2020: @KaitlynGuru went to my unlocked and abandoned computer and got all my passwords, due to my use of an insecure SFTP program and also, I suspect, the Apple Keychain.
This motivated me to change all my passwords, implement better password storage, and start searching for good auto-lock software for my laptop.
Also, last semester, she, with tiptiptip, made an epic defacement of my vulnerable server which certainly deserves honorable mention.
5-16-16: axi0mX defaced my home page, using a stored XSS in the Announcements section. He was able to post announcements by using a password he collected during the earlier hack, and me used CSS and Mouseover to activate the red banner defacement.
5-13-16: axi0mX defaced my home page, using an RSS feed script I used to put Slashdot headlines on it. This is the same script that Ryan Carter and Irwin used in 2010 to deface my page ; at that time I had left a vulnerable diagnostic routine in it, and clearly my attempt to harden it at that time did not close all the vulnerabilities. More details are coming!
3-3-16: Charles McCarty got my password the same way:
11-24-15: Keith Kimber got my password with his cell phone
|
Really Sam? @mcsin was here too
|
|
server pwned by axi0mX :-P
|
Here is his write-up of the attack
4-15-15: Keith Kimber got into my email twice with social engineering: by waiting until I left a logged-in laptop unattended. Now I have the screen locking feature on, but if I forget to use it, there will be more such hacks.
3-28-15: @erikrberlin paid attention in class and deduced my new link authentication scheme, so he defaced my home page with an XSS. Congratulations! For educational purposes, here is the series of links he used to sneak past my filters:
<a href='https://samsclass.info/10/10_F14.shtml'>test</a><br> <a href='http://samsclass.info'>test</a><br>
<a href='http://samsclass.info'>a<script>alert(\"test\")</script></a><br>
<a href='http://samsclass.info'>a<script>alert(String.fromCharCode(116,101,115,116))</script></a><br>
<a href='http://samsclass.info'>a</a><script>alert(String.fromCharCode(116,101,115,116))</script></a><br>
<a href='http://samsclass.info'>a</a><script>alert("test")</script></a><br>
<a href='https://twitter.com/erikrberlin'>Added by Erik Berlin<script>alert(String.fromCharCode(88,83,83,32,80,79,67,32,98,121,32,69,114,105,107,32,66,46))</script></a><br>
<a href='https://twitter.com/erikrberlin'>Link added by Erik Berlin<script>alert(String.fromCharCode(88,83,83,32,80,79,67,32,98,121,32,69,114,105,107,32,66,46))</script></a><br>
3-11-15: Carlo Combes found my hidden script to save links and added a "hi" link to my news page! I upped my game to a somewhat less obvious authentication scheme :)
2-25-15: Carlo Combes found an XSS vuln on my attack server in the Trojan logging script
used in
this project. I added input validation to it.
Omar Zouai
2-18-15: Found a hidden file with a very weak password, and was able to inject links onto my news page.
1-31-15: Found a portion of my link adder that was old and had no password protection, and used it to deface this page. He then contacted me and explained it, so it's a fair cop :)
1-17-15: found a redirect loop
7-12-11: He found my one-character-long password for posting news links and posted a link. He then emailed me explaining it. No one else found it and I stayed with that system for another four years :)
c. 2010: Defaced my site through the Slashdot headlines
c. 2008: Found XSS in the comment system