
dpkg-reconfigure mysql-server-5.5
Type in a password of
password
In the next box, type in a password of
password
Warning: this is obviously an insecure password, not apropriate for use on a production system.In the Terminal window, enter this command:
service mysql start

service apache2 restart
In your Linux machine, in a Terminal window, enter these commands:
cd /var/www
rm sqlol-sam.tar.gz
rm -R sqlol
wget http://samsclass.info/123/proj10/sqlol-sam-old3.tar.gz
tar xzf sqlol-sam-old3.tar.gz
In IceWeasel, go to
localhost/sqlol/simple.php
SQLol opens, as shown below:
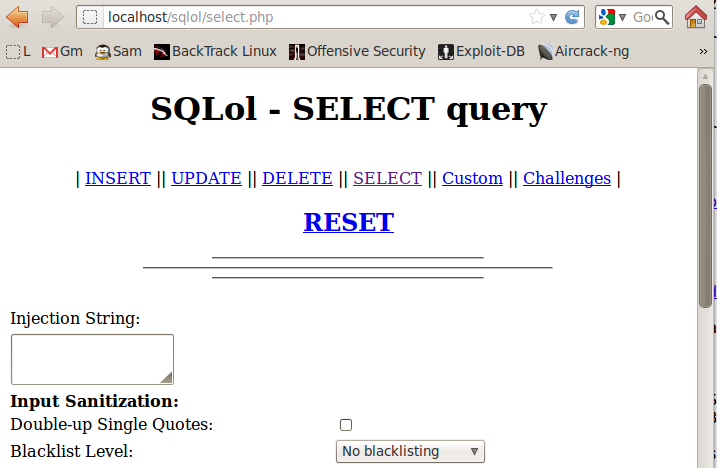
Click RESET
A message appears saying "Done!"
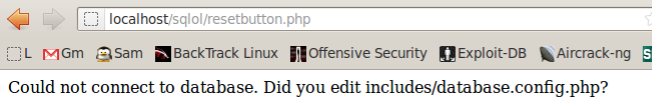
If you see the "Could not connect..." message shown below, restart mySQL with this command:
service mysql restart
In your Linux machine, in IceWeasel, go to
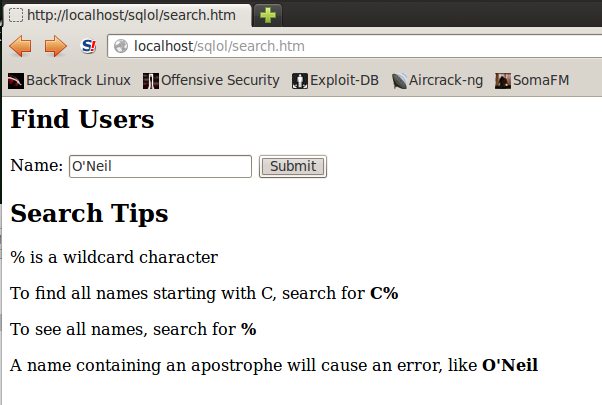
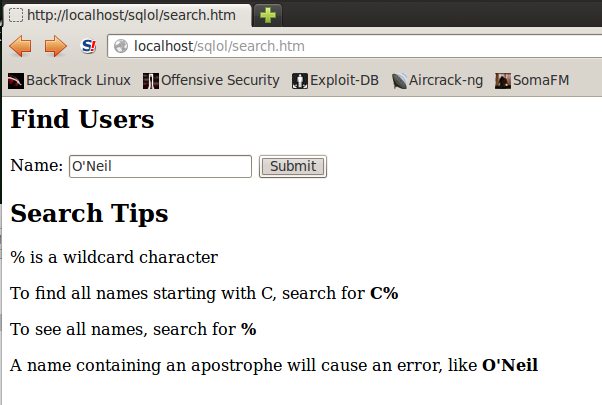
A "Find Users" page opens, as shown below:
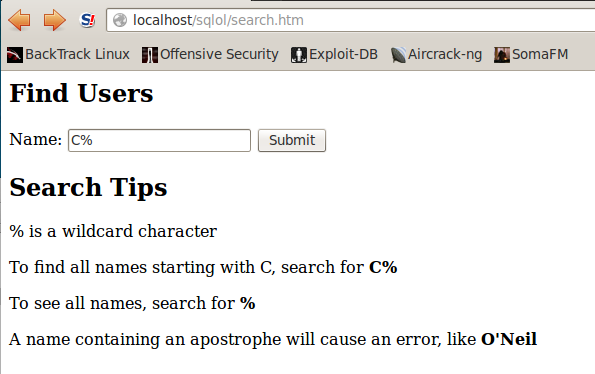
In the Name field, type
C%
You should see the username "Chunk MacRunfast", as shown below:
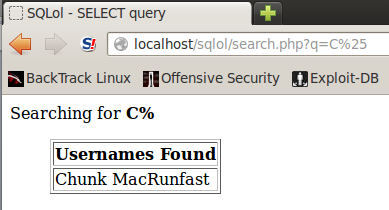
In IceWeasel, click the Back button to return to the "Find Users" page.
In the Name field, type
%
You should see all five usernames, as shown below:
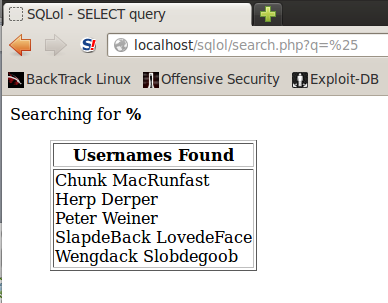
The whole point of SQL injection is that a simple form like this can be tricked into revealing more data than the designer intended to reveal.
In IceWeasel, click the Back button to return to the "Find Users" page.
In the Name field, type
O'Neil
You should see an error message, as shown below:
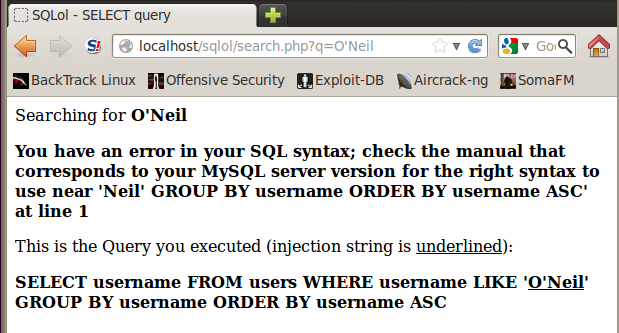
This is the kiss of death--an error like this means that you have lost control of the database, and an attacker can often extract all the data.
We'll steal the data with Havij, which is absurdly easy to use.
ifconfig
If you are using a virtual machine, it's best to use "Bridged" networking rather than NAT.
http://192.168.198.175/sqlol/search.htm
Replace 192.168.198.136 with the correct IP address of your Linux machine.
A "Find Users" page opens, as shown below:
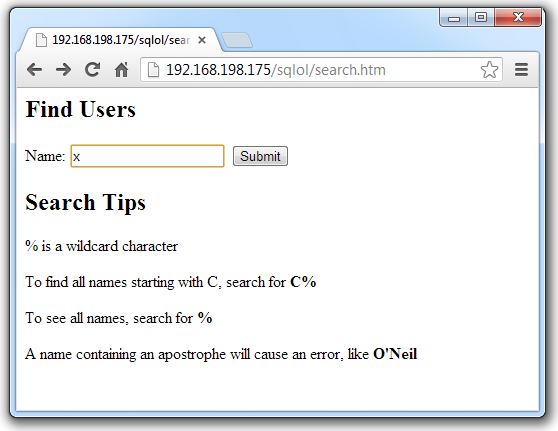
In the Name field, type
x
You should see the results page, as shown below:
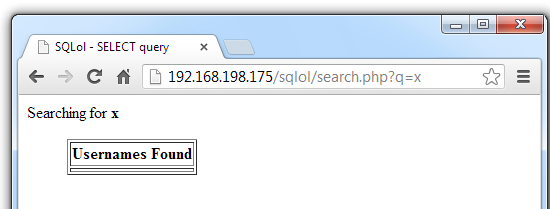
No users were found, but that's not a problem. What we really want is the URL of this page, as shown in the address bar:
http://192.168.198.175/sqlol/search.php?q=x
On the Windows machine, in the URL bar, add an apostrophe to the end of the URL, so it becomes this:
http://192.168.198.175/sqlol/search.php?q=x'
A SQL error message appears, as shown below:
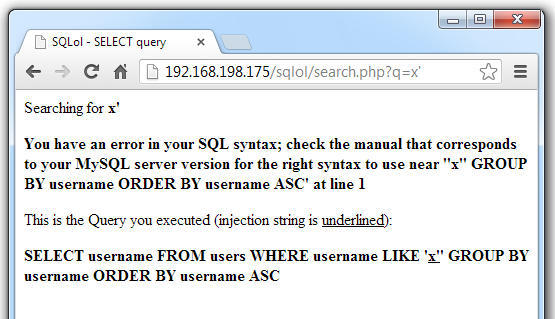
This URL is the attack point Havij needs: a URL with a vulnerable parameter.
On your Windows machine, in a Web browser, go to:
http://itsecteam.com/products/havij-advanced-sql-injection/
Look in the middle of the screen, and in the "Havij Advanced SQL Injection" section, click the "Download" tab.
Click "Havij v1.15 Free"
After the file downloads, extract it with 7-zip. If you don't have 7-zip, get it here
Install Havij with the default options.
If it doesn't launch automatically, click Start, type Havij into the Search box, and run Havij. It does not require Administrator privileges.
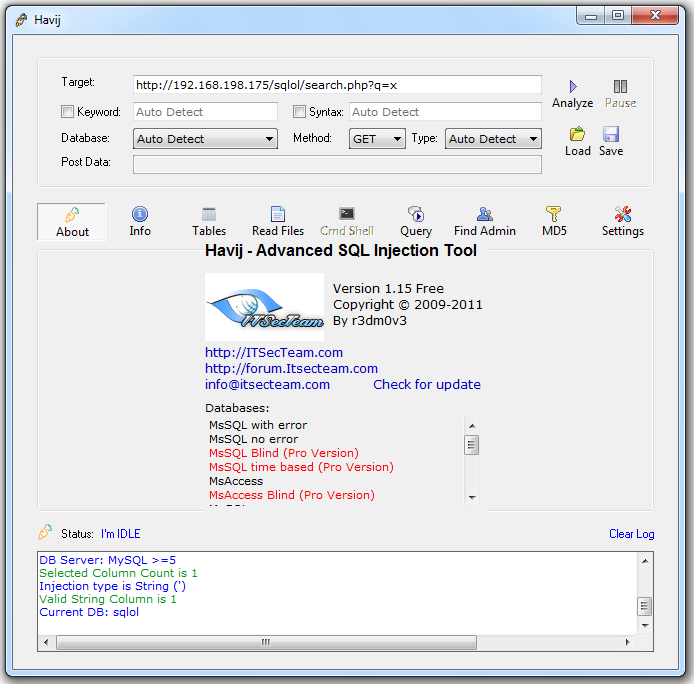
http://192.168.198.175/sqlol/search.php?q=x
In the Havij window, click the Analyze button.
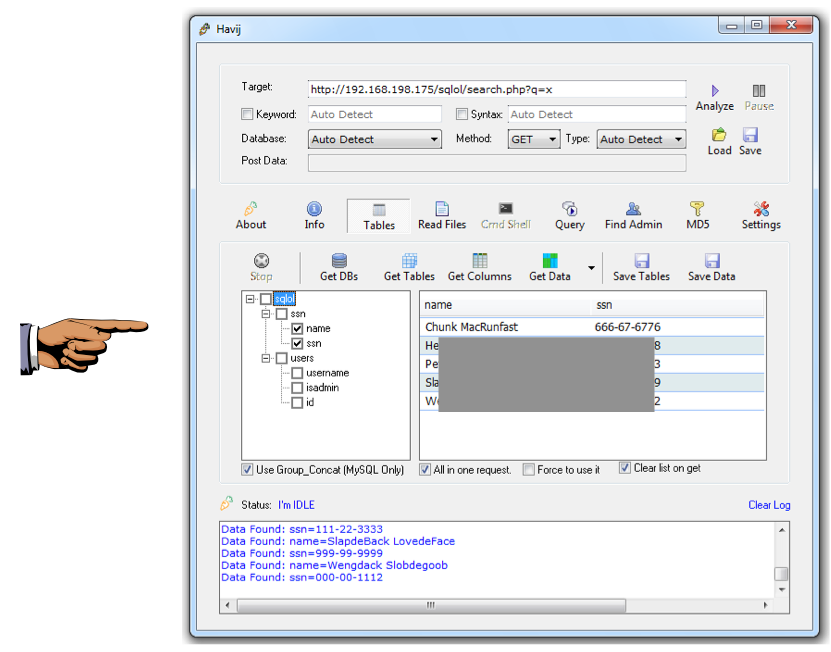
The Log at the bottom of the Havij window should show "Current DB: sqlol", as shown below:
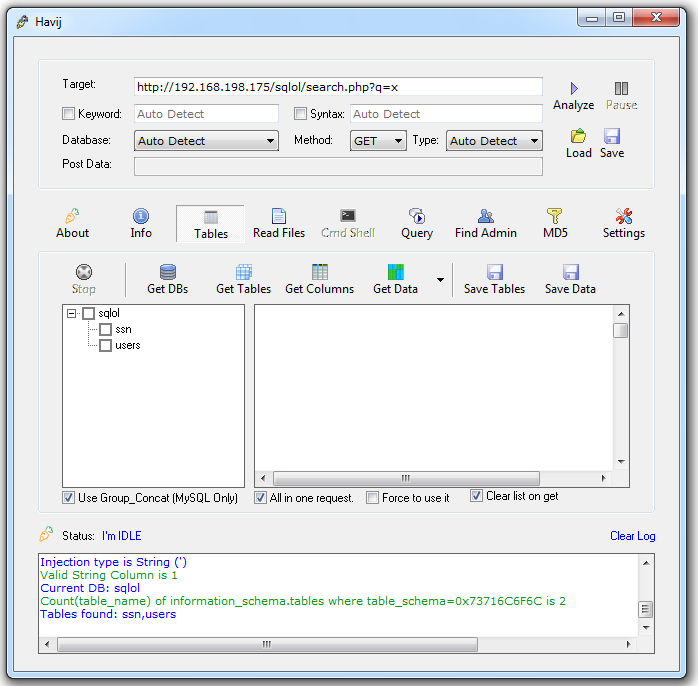
In the upper center of the Havij window, click the Tables button.
In the lower bar that appears, click the "Get Tables" button.
The tables "ssn" and "users" appear, as shown below:
In the left-center pane of the Havij window, check the ssn and users boxes.
In the center of the Havij window, click the "Get Columns" button.
The column names appear, as shown below:
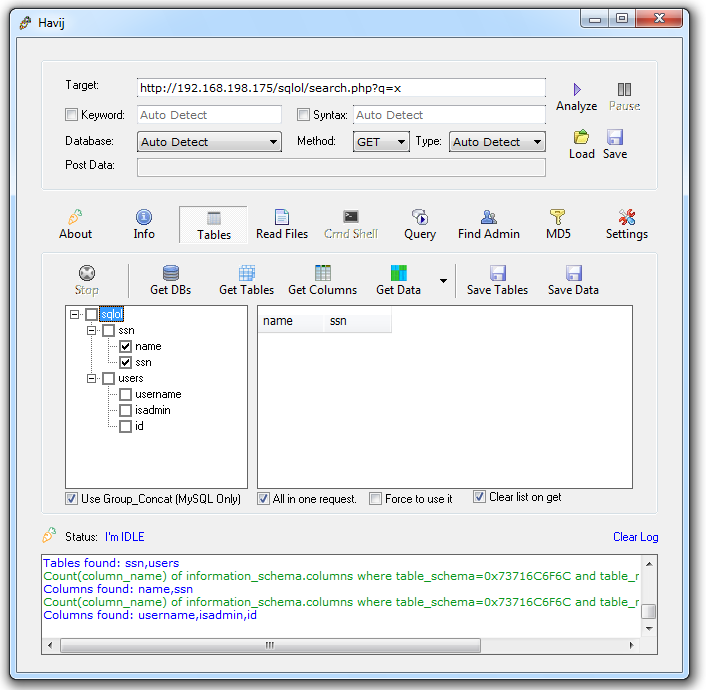
In the left-center pane of the Havij window, in the "ssn" table section, check the name and ssn boxes.
In the center of the Havij window, click the "Get Data" button.
The names and ssns appear, as shown below:
A "Find Users" page opens, as shown below:
In the Name field, type
O'Neil
You should see a SQL syntax error, as shown below:
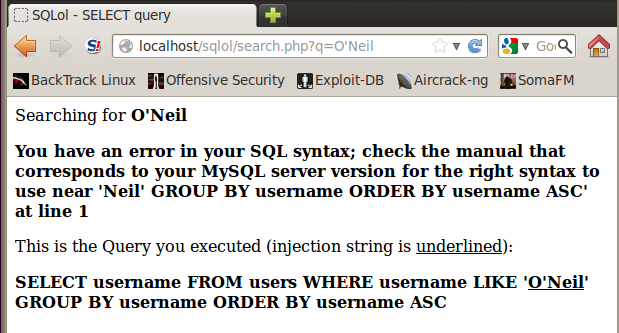
This error indicates a SQL injection vulnerability.
cd /var/www/sqlol
cp search.php old-search.php
nano search.php
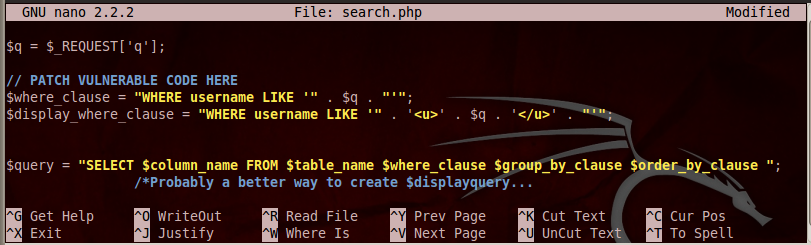
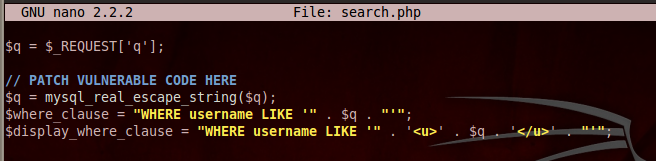
Add this line under the comment:
$q = mysql_real_escape_string($q);
Save the page with Ctrl+X, Y, Enter.
This line adds backslash characters before quotation marks, which will prevent SQL syntax errors.
A "Find Users" page opens, as shown below:
In the Name field, type
O'Neil
Now, instead of an error, you see a chart showing that no results were found, as shown below:
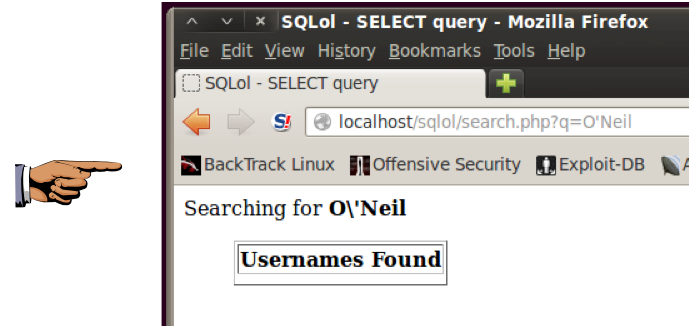
You can see how the fix works: the URL shows the original search string of O'Neil but the top of the results Web page shows the escaped version O\'Neil
http://192.168.198.175/sqlol/search.php?q=x
In the Havij window, click the Analyze button.
The Log at the bottom of the Havij window shows red error messages, as shown below, because the site is no longer vulnerable.

Last modified: 7:44 am 7-21-13