SC 130: Finding and Fixing Security Issues with Snyk (15 pts)
What You Need
- A computer with a Web browser
GitHub Account and Vulnerable Codebase
You should already have prepared a GitHub account with
the OWASP Juice Shop code in it in a previous
project. If you did not do that, do the steps in the
blue box below.
Make a Github Account
In a Web browser, go to https://github.com/
Create an account and log in.
Forking the OWASP Juice Shop Core
This is a deliberately vulnerable codebase from OWASP.
Instead of forking the original
code from OWASP, which may be changing, you'll copy my
version, which is frozen in the state the code was on
Mar 3, 2024.
In a Web browser, go to https://github.com/sambowne/juice-shop-orig
At the top right, click the drop-down arrow
next to "Fork". Click "Create a new fork",
as shown below.

On the "Create a new fork" page,
change the Repository name to
juice-shop-working, and,
at the bottom right,
click the "Create fork" button,
as shown below.

|
Make a Snyk Account
In a Web browser, go to https://snyk.io/plans/
Click the
"Start free" button.
Click the
Github button.
Log in to Github if you are prompted to.
When you see it, click the green
"Authorize snyk"
button.
If a "Welcome to Snyk" bos pops up, click the
"No, not right now"
button.
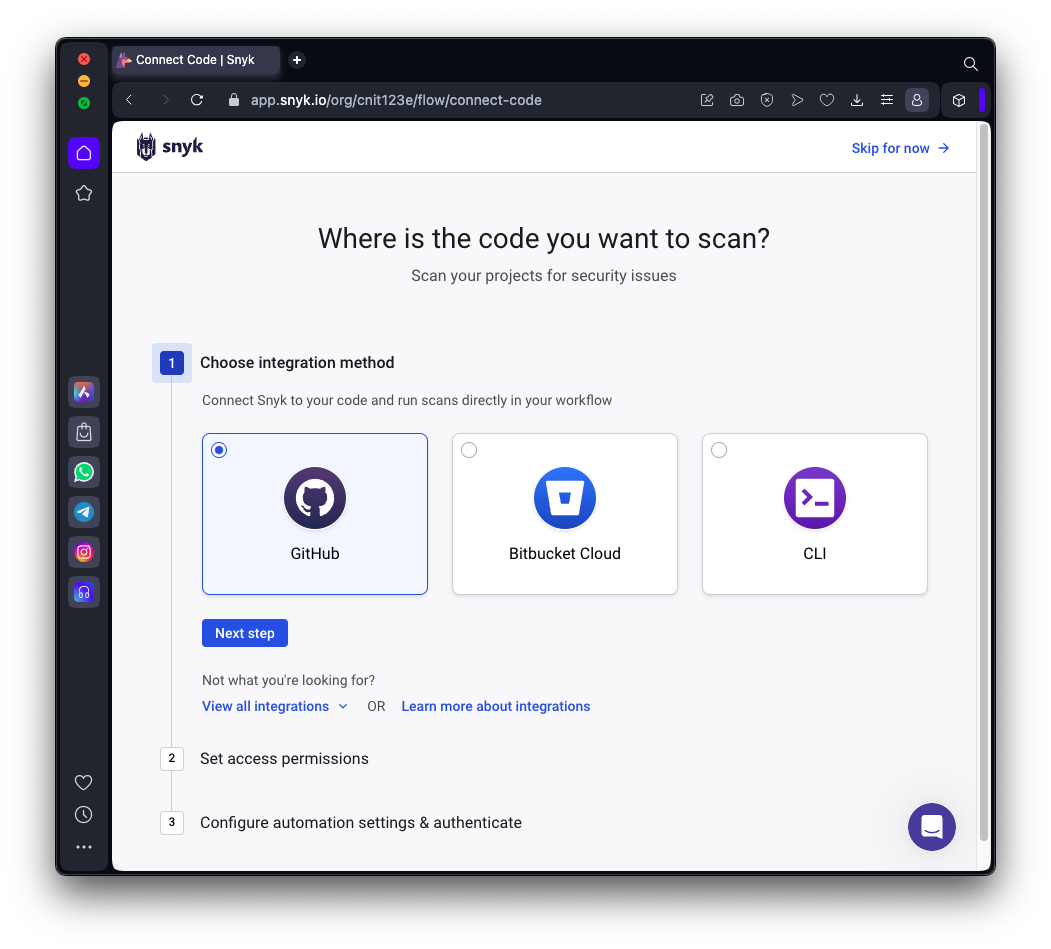
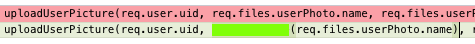
On the "Where is the code you want to scan" page,
click Github,
as shown below.
Click the "Next step" button.
At step "2: Set access permissions",
accept the default options and
click the "Next step" button.
At step "3: Configure automation settings & authenticate",
accept the default options and
click the "Authenticate GitHub" button.
Click the green
"Authorize snyk"
button.
Enter your GitHub password when you
are prompted to.
Scanning the juice-shop
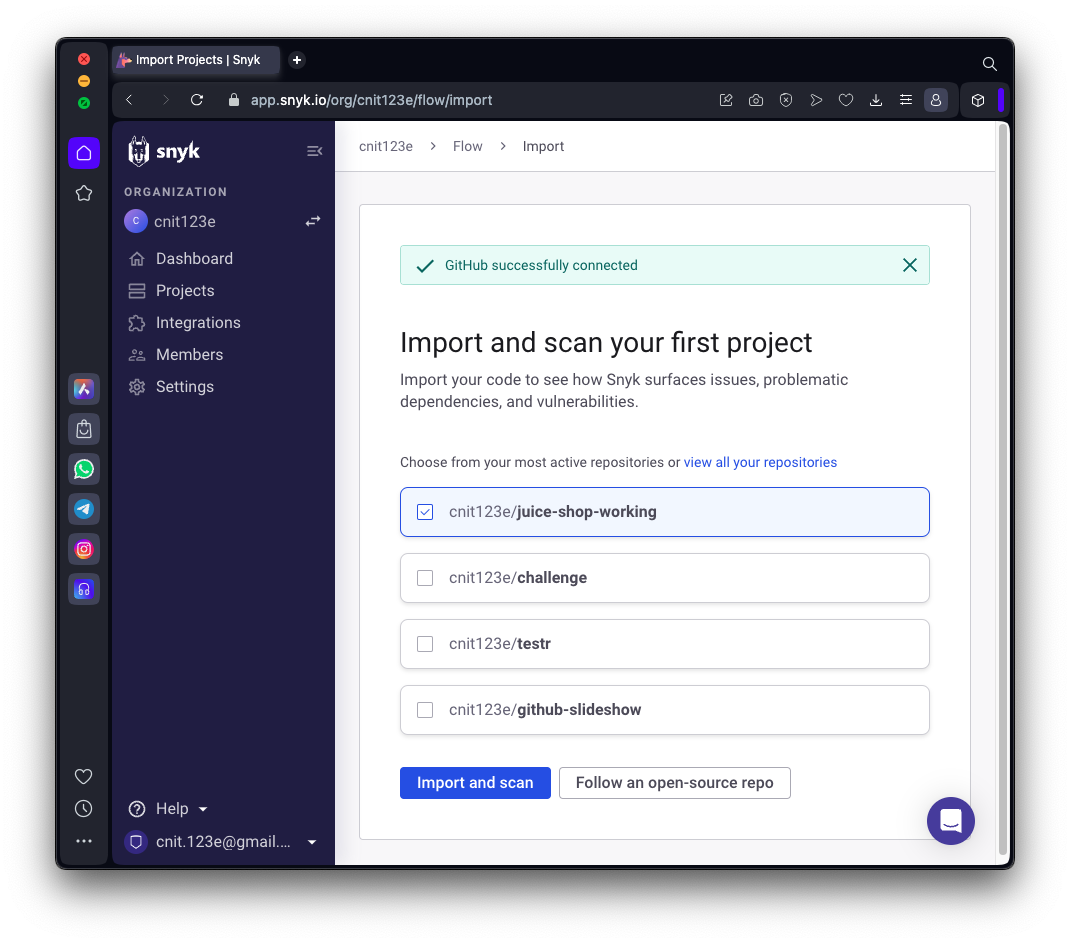
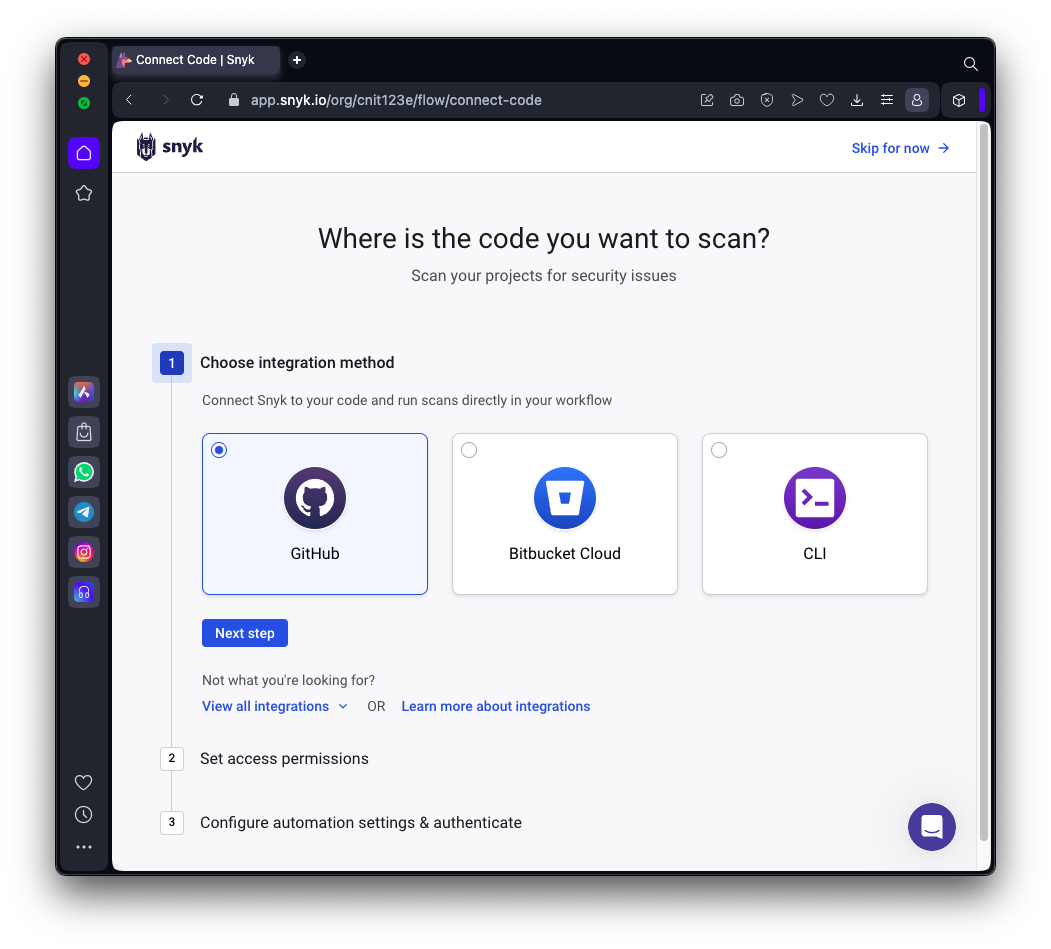
At the "Import and scan your first project"
page, verify that "juice-shop-working"
is selected and
Click the blue
"Import and scank"
button,
as shown below.
Viewing Results
Wait while the project is imported and scanned.
Click the right-arrow next to "juice-shop-working"
to see the results.
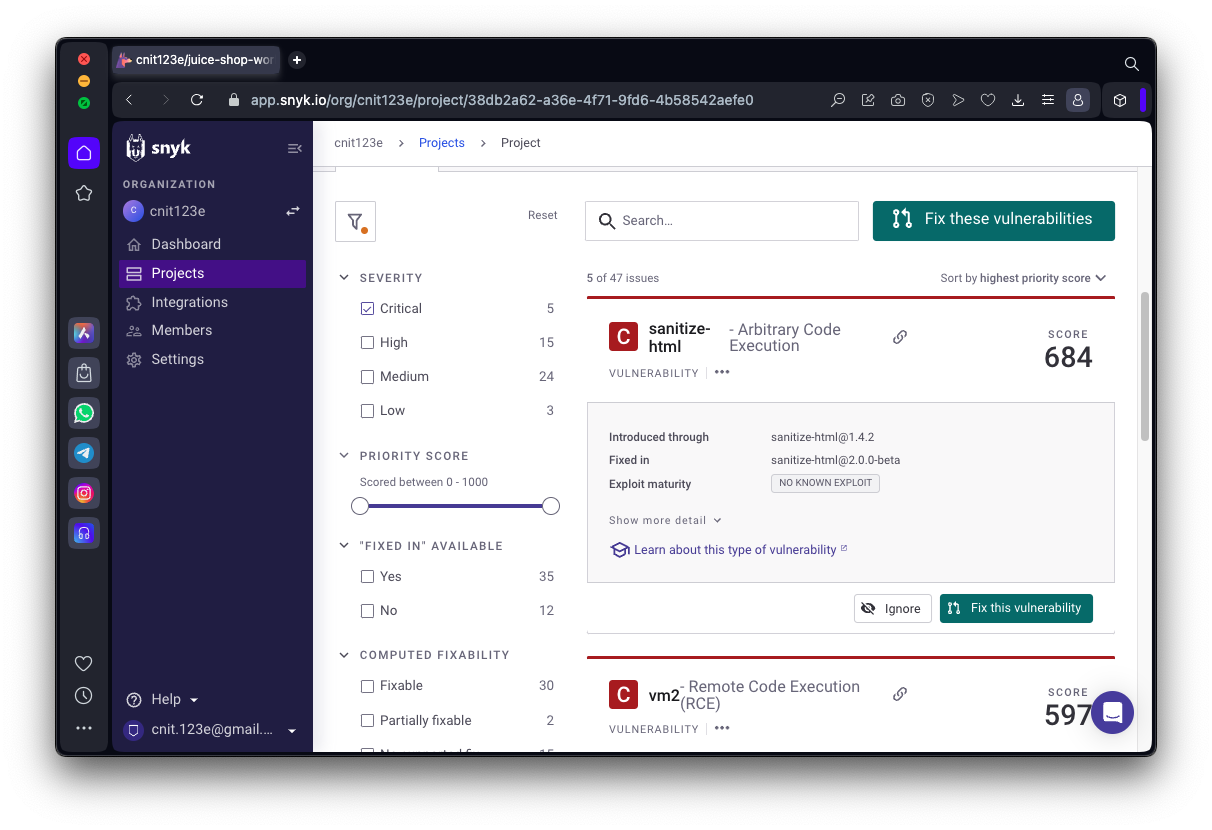
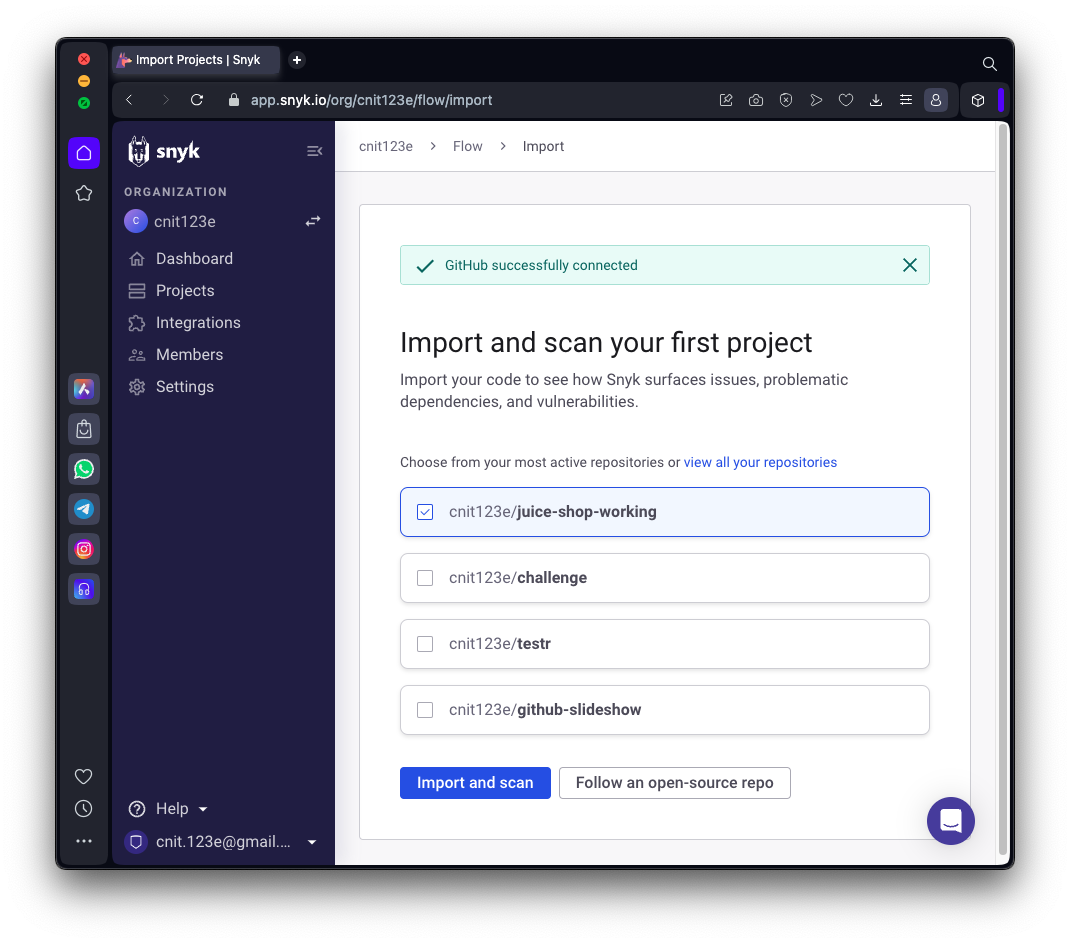
There are 5 critical vulnerabilities in
"package.json", as shown below.
Click package.json.

You see a list of issues. On the left
side, click the Critical box.
There are 5 issues, showing a priority score,
as shown below.
Fixing "sanitize-html"
In the "sanitize-html" section,
click "Show more detail".
Click the green "Fix this vulnerability"
button.
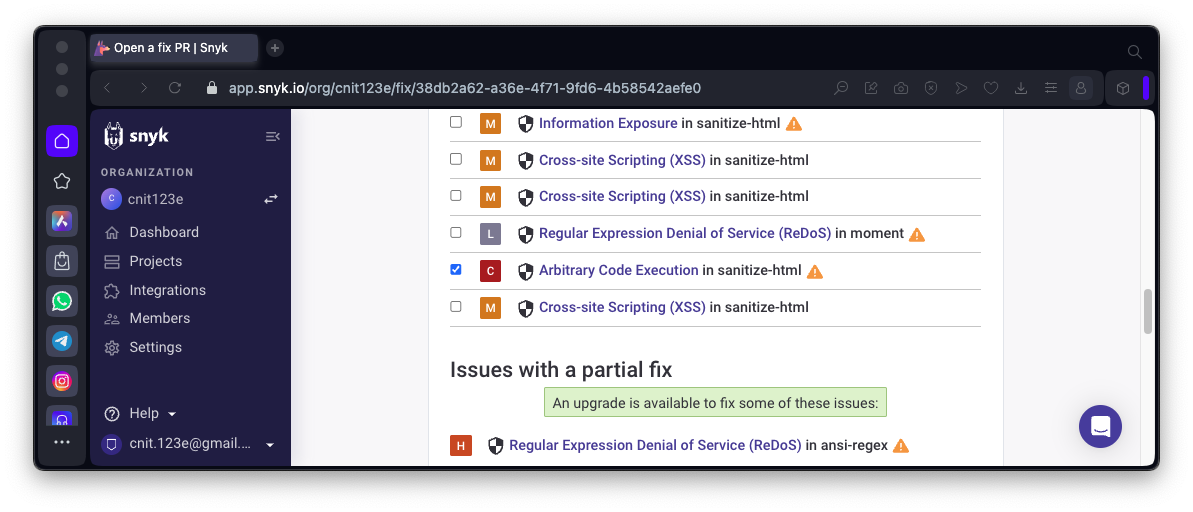
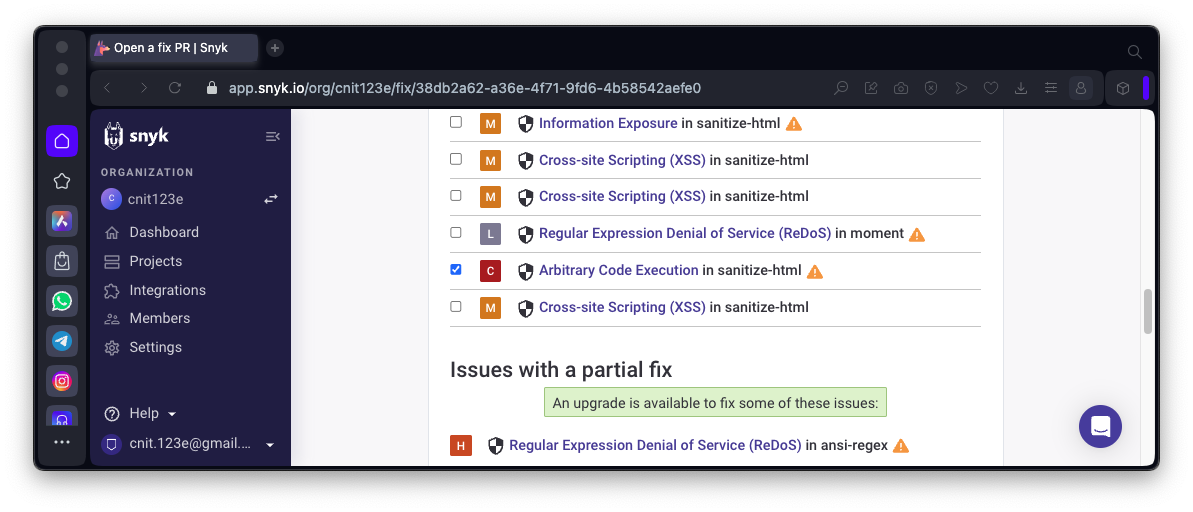
The next page is titled
"Open a Fix PR",
as shown below.

Scroll down to verify that
"Arbitrary Code Execution in sanitize-html"
is in the "Issues with a fix"
section and is selected,
as shown below.
Scroll to the bottom and click
the green
"Open a Fix PR" button.
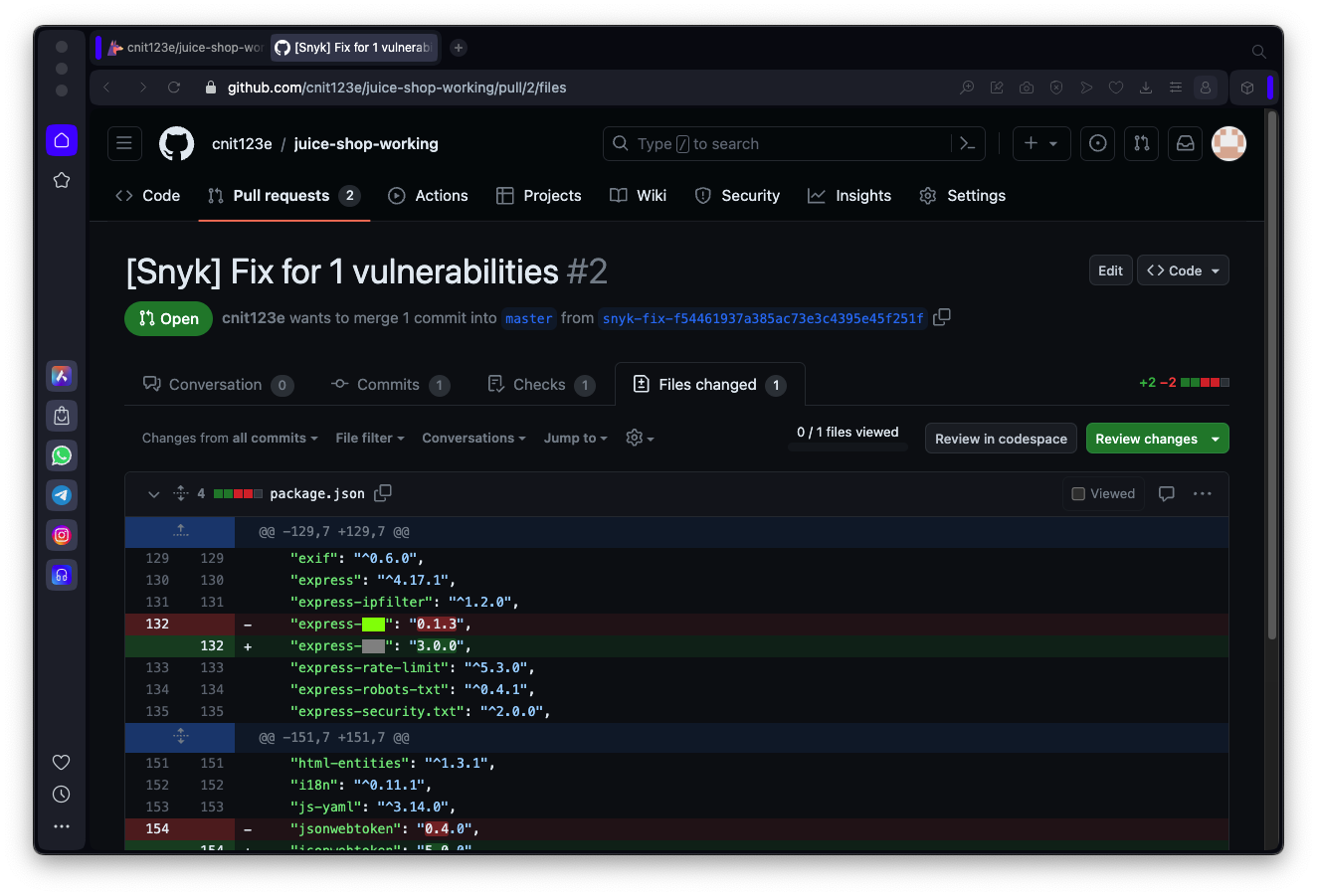
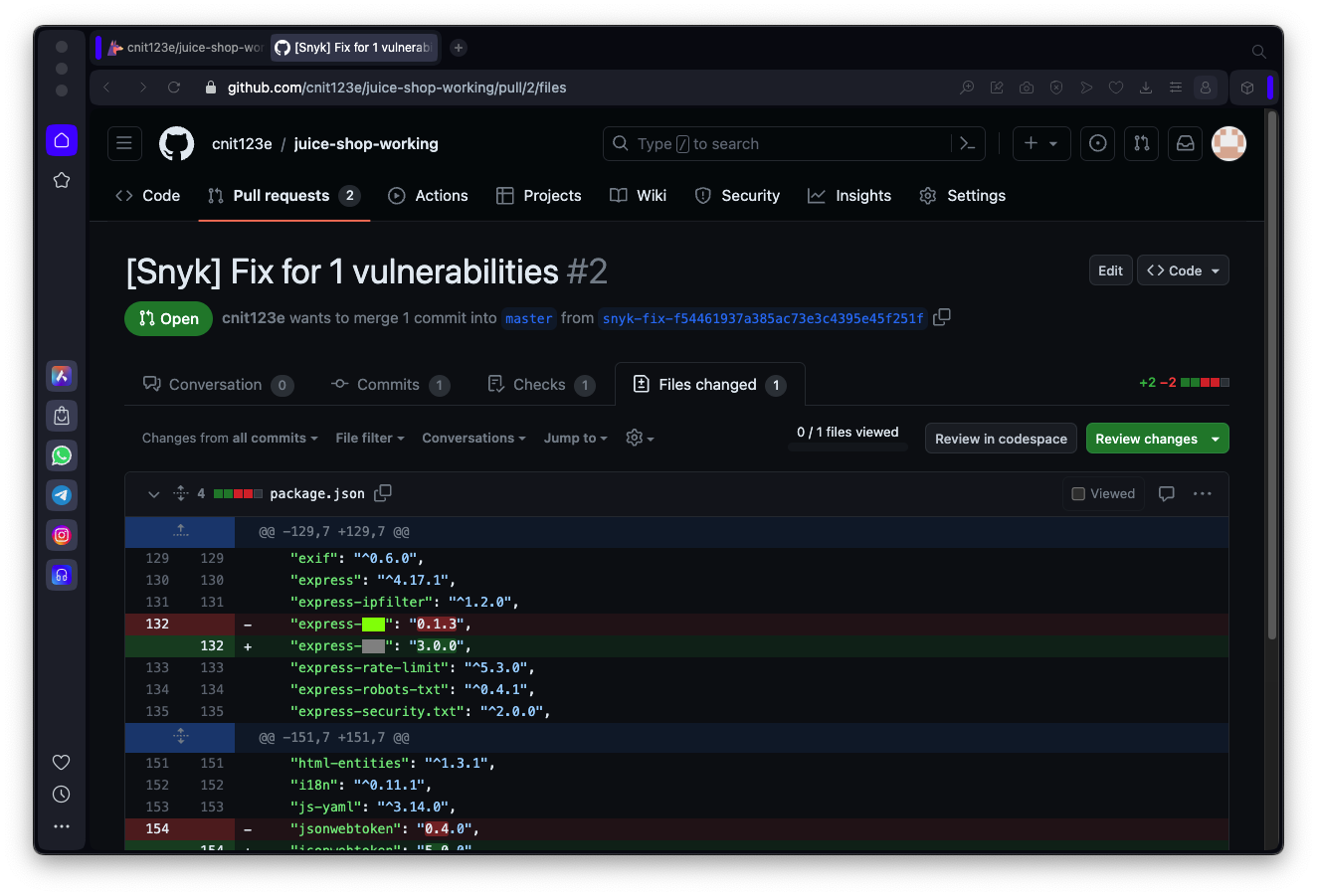
GitHib opens with a Pull Request page,
as shown below.

Click the "Files changed" tab.
Click the three dots after
"fix: package.json to reduce vulnerabilities".
As shown below, the change is just
to update the "sanitize-html" version
number.

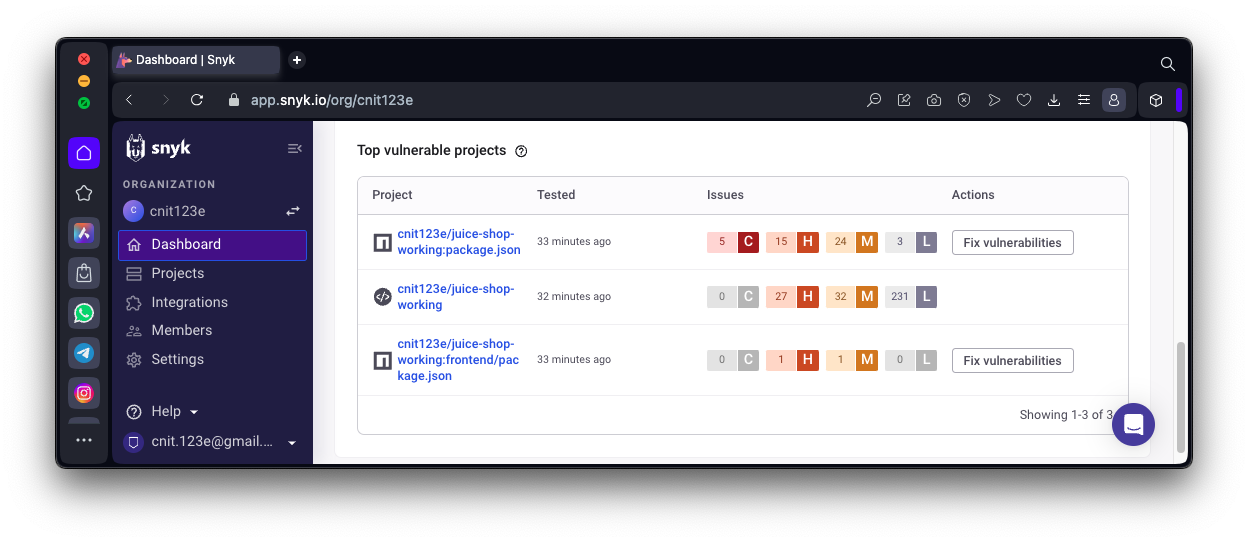
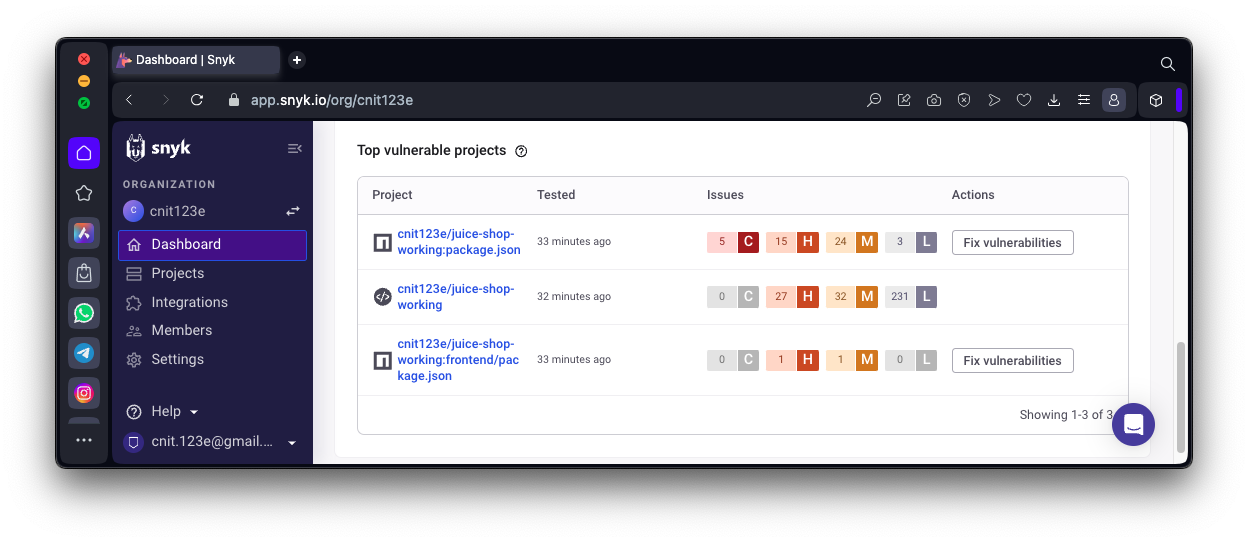
Fixing a base64url Vulnerability
In the Snyk page, on the left, click
Dashboard.
The second item shows 15 H vulnerabilities,
as shown below.
Click juice-shop-working on that line.

Flag SC 130.1: base64url (15 pts)
Find the base64url vulnerability and automatically
fix it. View the changed code.
The flag is
covered by a green
rectangle in the image below.
|
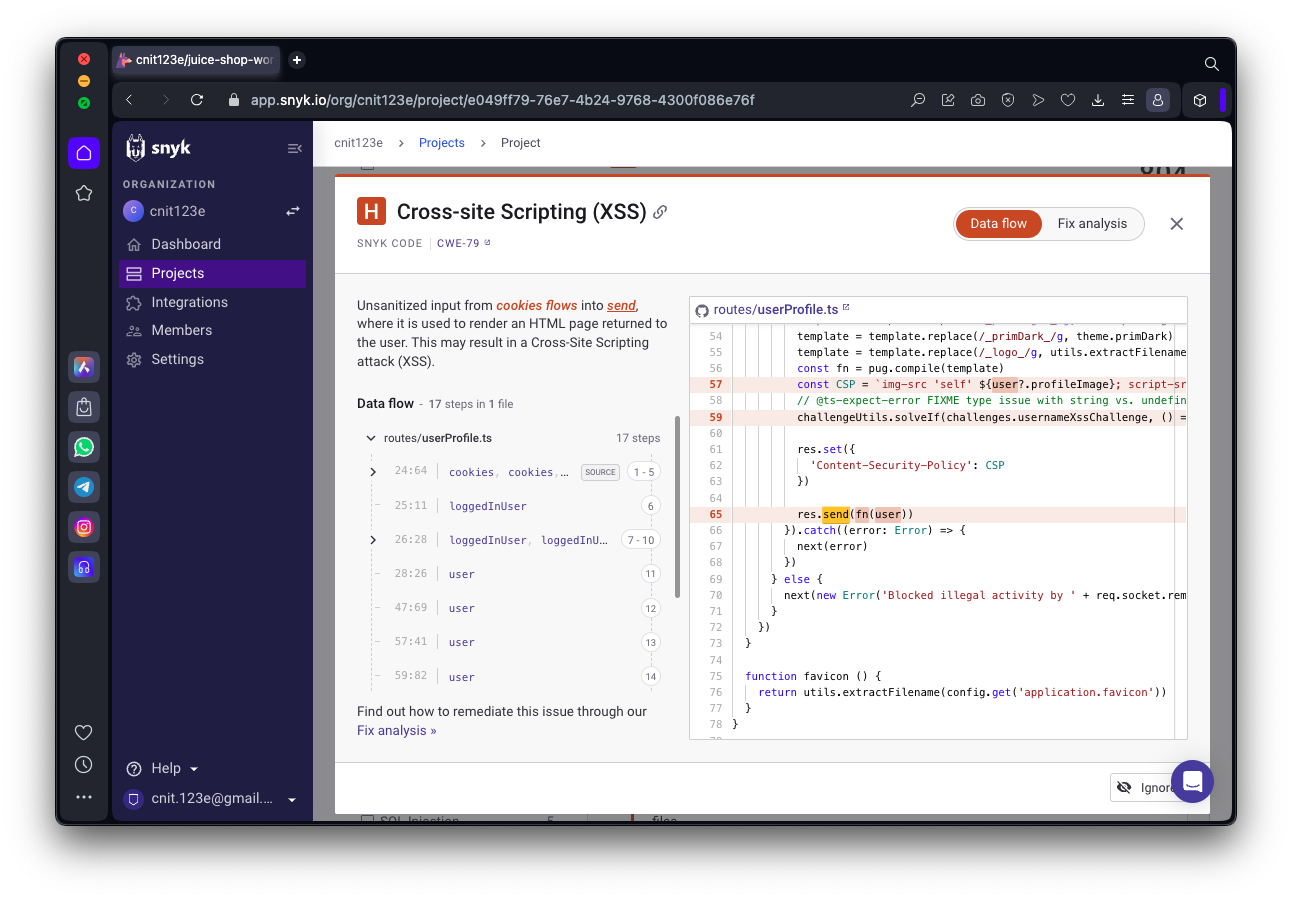
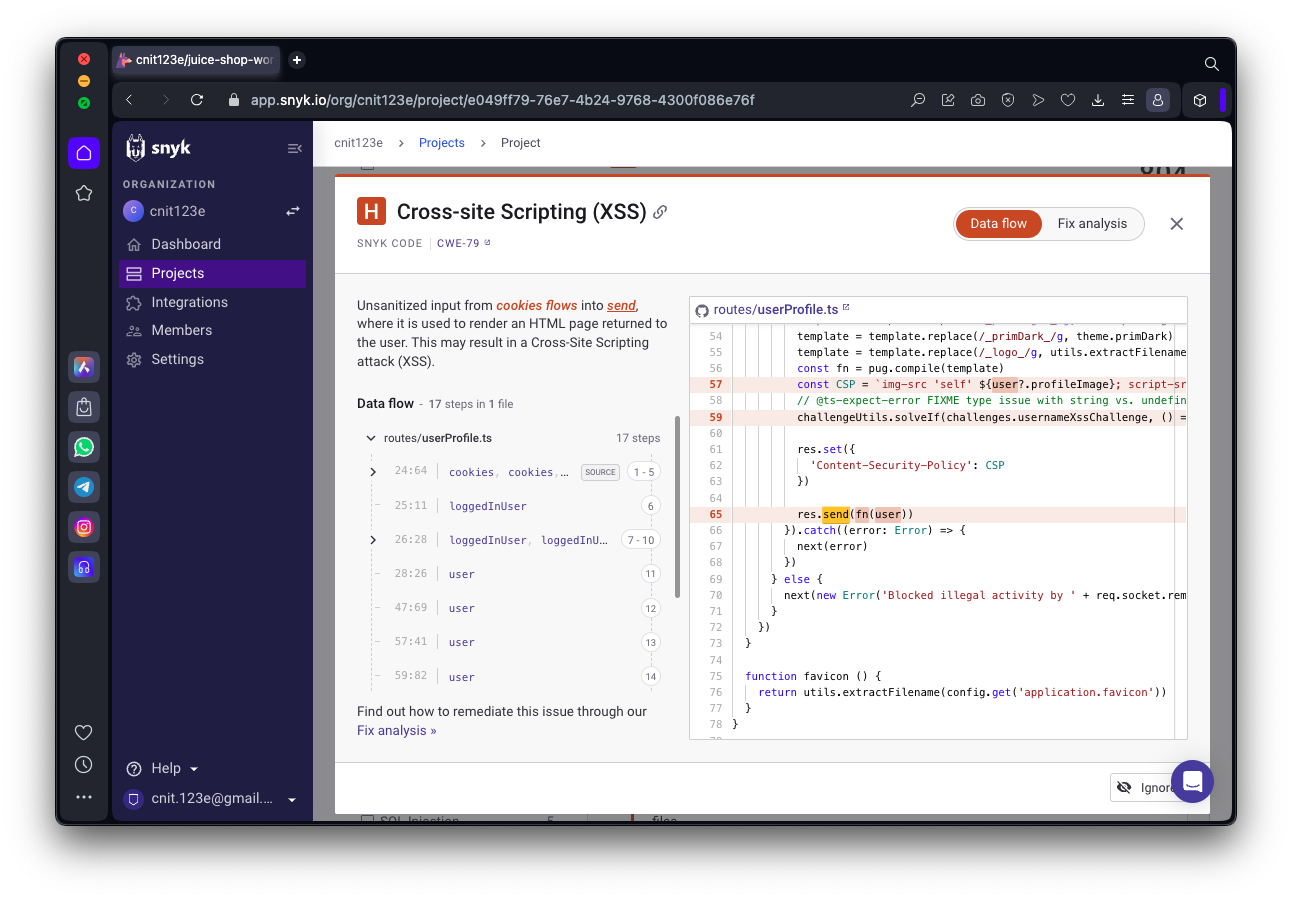
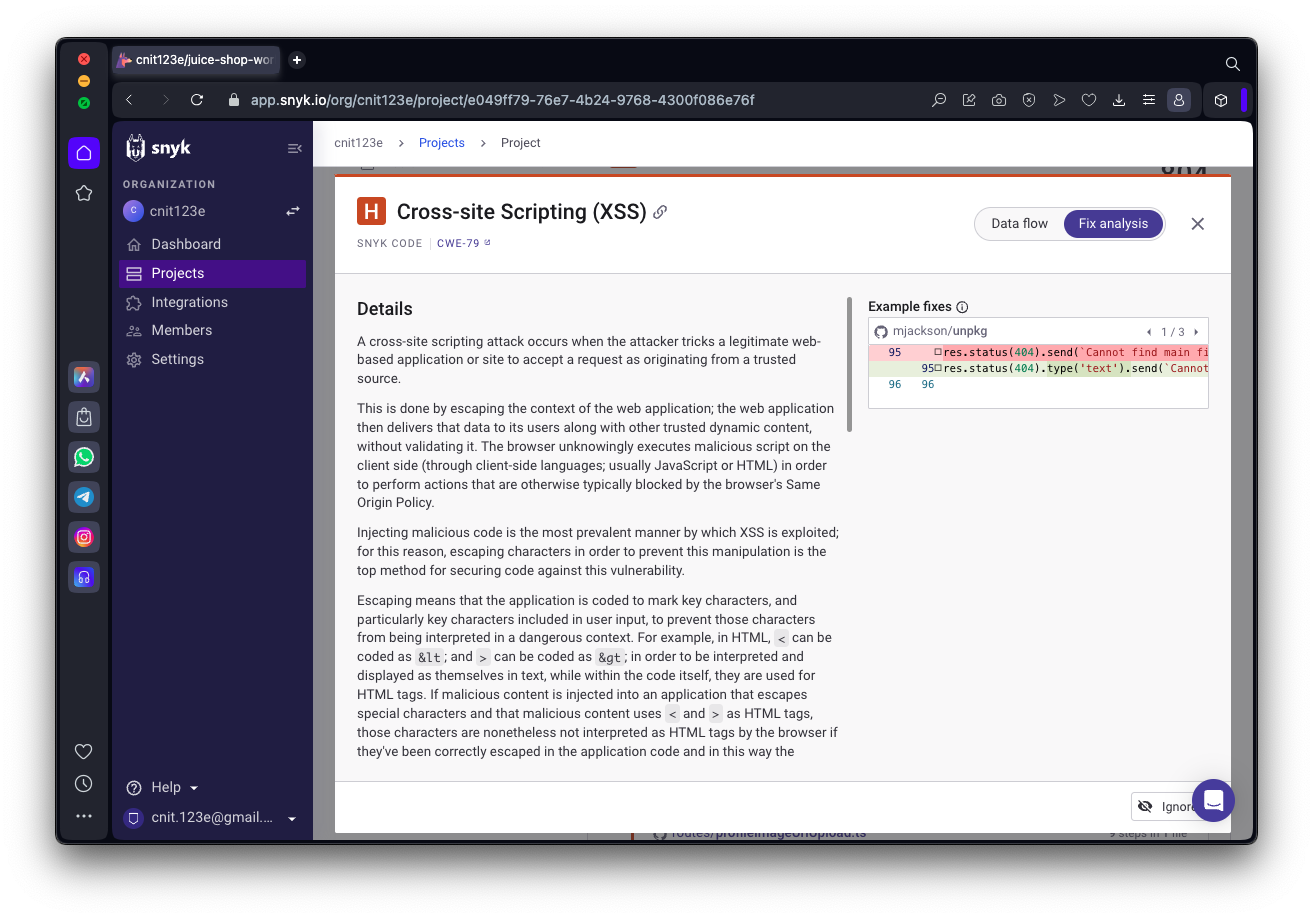
Findng a Cross-site Scripting Vulnerability
In the Snyk page, on the left, click
Dashboard.
On the next page, at the bottom, in the
"Top vulnerable projects" section,
find the Project that does not end in
"package.json".
In the image below, it is the second one.
Click that project name.
Read the description. This sounds like a
typical XSS vuln, where user data is
sent back within the HTML on a Web page,
allowing JavaScript code injection.
On the next page, find the
"Cross-site Scripting" vulnerability
shown below.
Notice that there is no automatic fix
available.

On the Snyk page,
click the green
"Full details" button.
A page appears, explaining the vulnerability
and showing the vulnerable line of code,
as shown below.
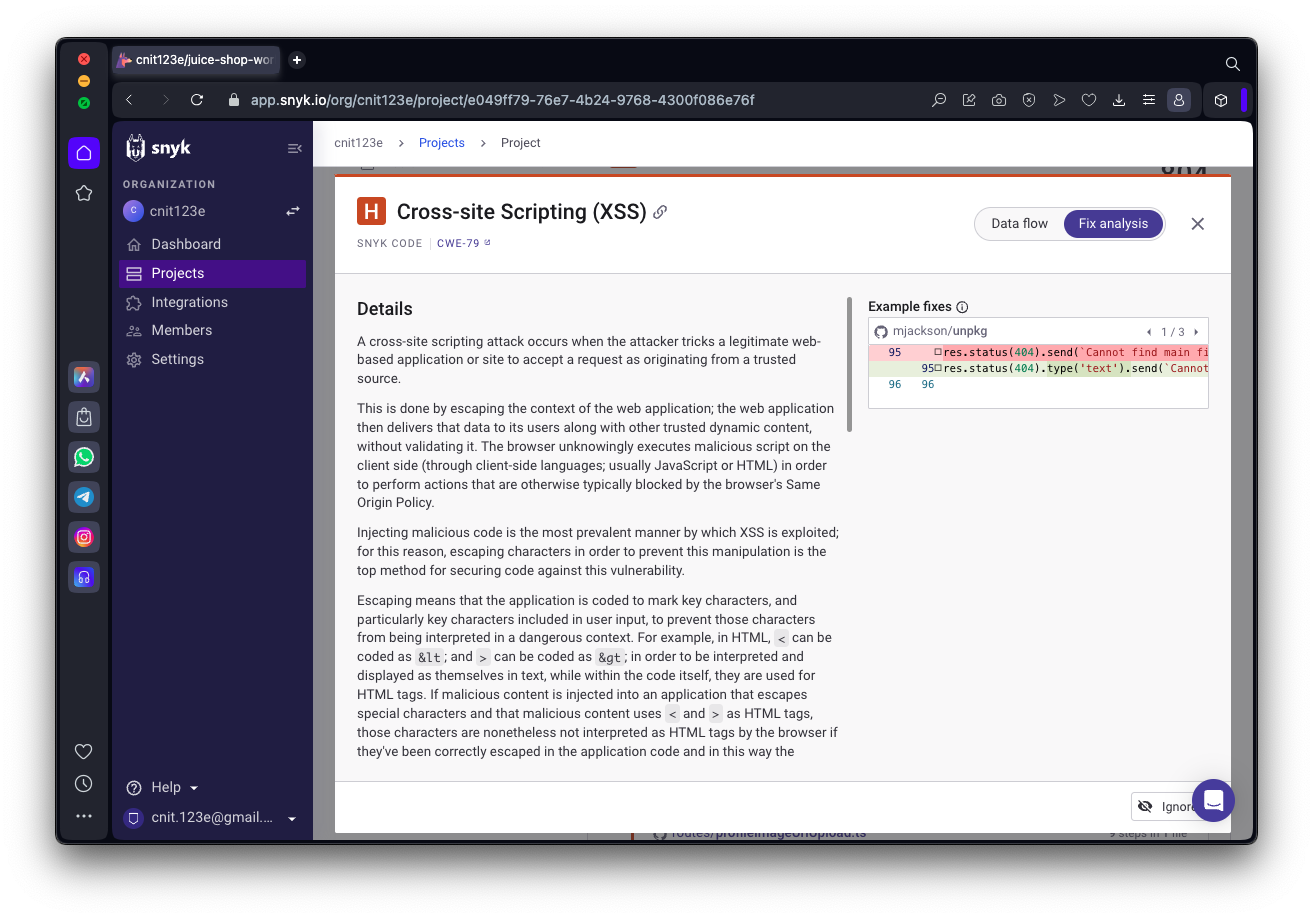
At the top right, click
"Fix analysis".
A helpful page explains the issue,
and on the right shows example
code with a fix,
as shown below.
The proposed solution is to add
".text" to the untrusted input data.
It took some Googling, but I found this
page which says that is indeed a good
way to escape special characters:
Is jQuery .text() method XSS safe?
So this seems very helpful, although
not quite as convenient as an automatic
fix.
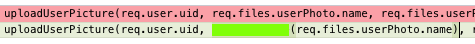
Flag SC 130.2: Path Traversal (10 pts)
Find the Path Traversal vulnerability
on line 94 of the "routes/vulnCodeSnippet.ts"
file.
Examine the Fix analysis and the
example fixes.
The flag is the added function code
needed to fix this problem,
covered by a green
rectangle in the image below.
|
Posted 3-3-24