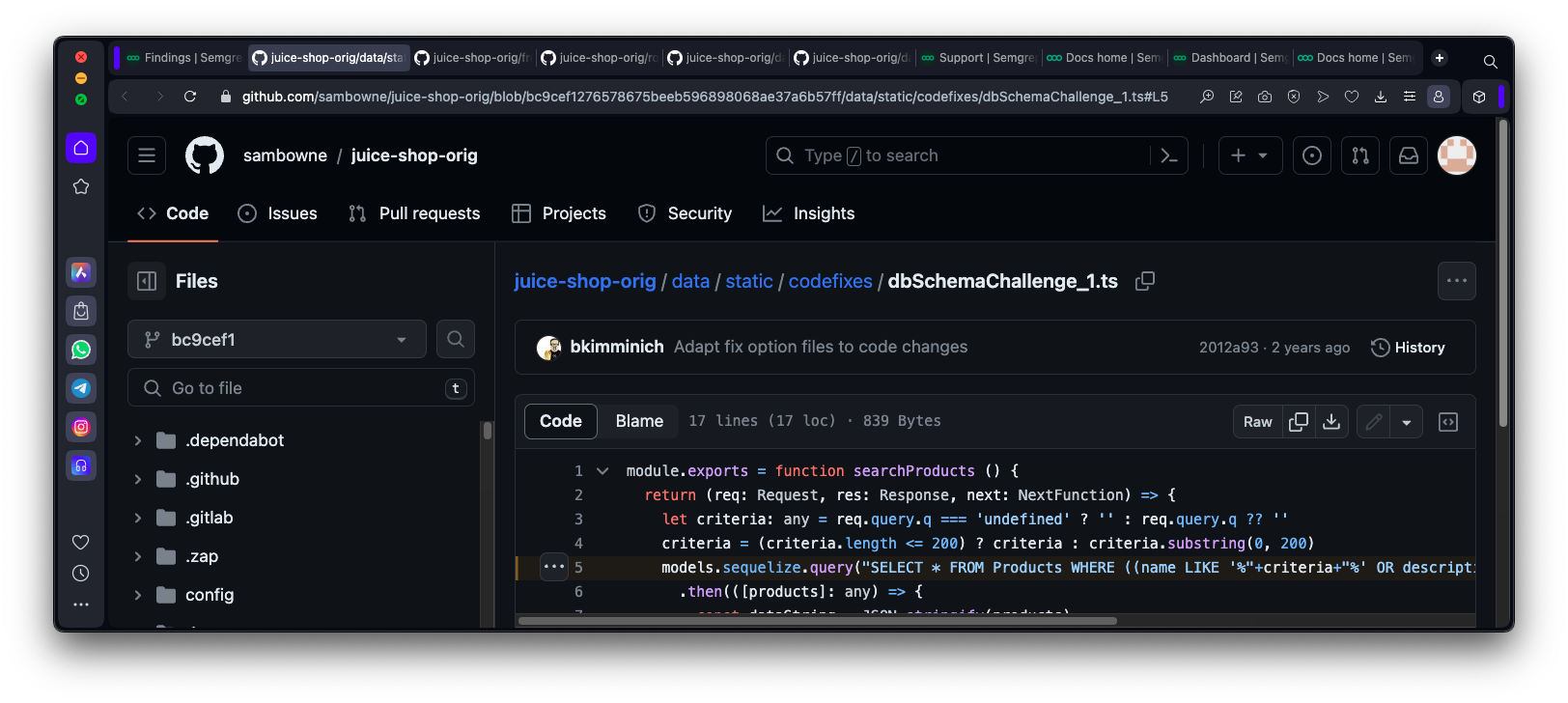
Make a Github AccountIn a Web browser, go to https://github.com/Create an account and log in. Forking the OWASP Juice Shop CoreThis is a deliberately vulnerable codebase from OWASP. Instead of forking the original code from OWASP, which may be changing, you'll copy my version, which is frozen in the state the code was on Mar 3, 2024.In a Web browser, go to https://github.com/sambowne/juice-shop-orig At the top right, click the drop-down arrow next to "Fork". Click "Create a new fork", as shown below.
|