P4: Threat Hunting with Splunk (325 pts)
What You Need for this Project
- A computer with a Web browser.
Purpose
To practice threat hunting, using
the
Boss of the SOC (BOTS) Dataset.
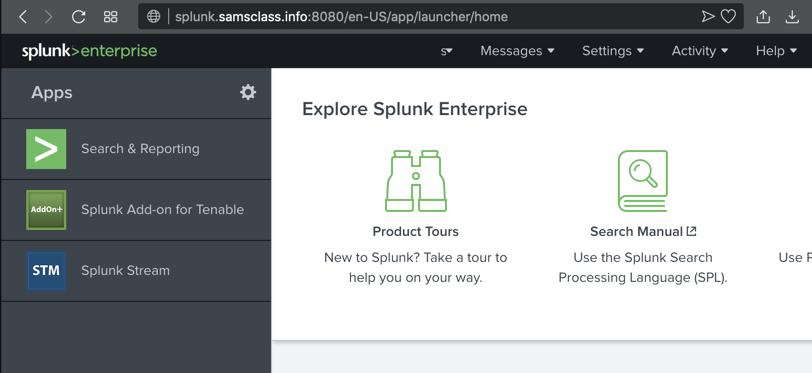
Connecting to My Splunk Server
Go
here:
https://splunk.samsclass.info
or here:
https://splunk2.samsclass.info
Log in as student1 with a password of student1
The Splunk main page opens, as shown below.
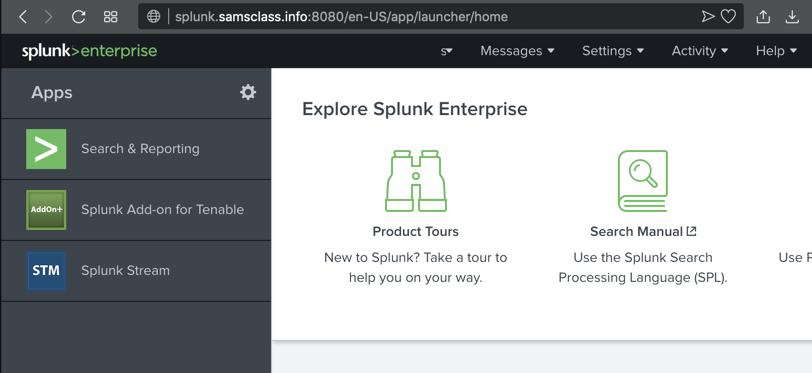
At the top left, click "Search & Reporting".
The "Search" page opens,
as shown below.
Introduction to Splunk & the BOTS Data
Sampling the Data
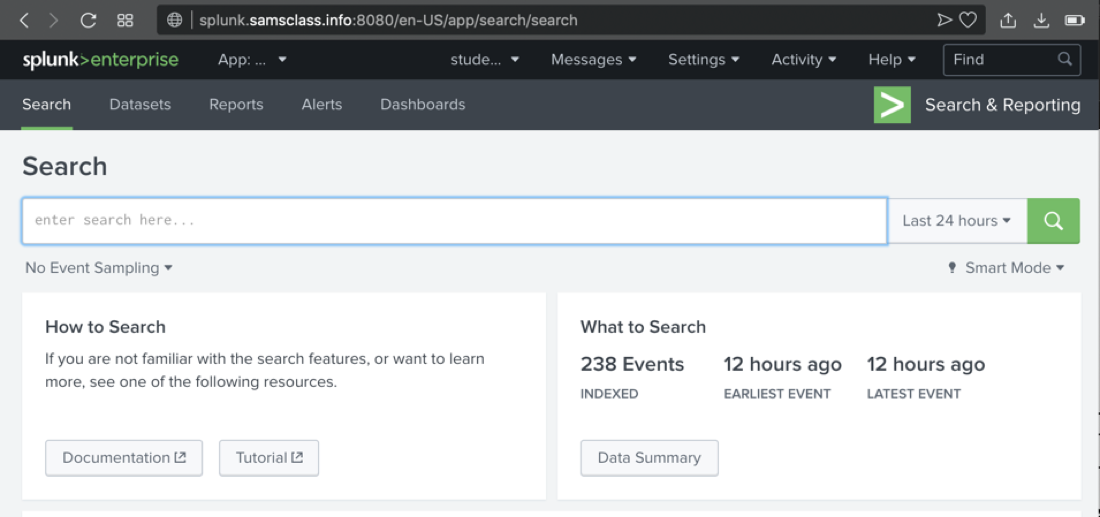
Do these steps:
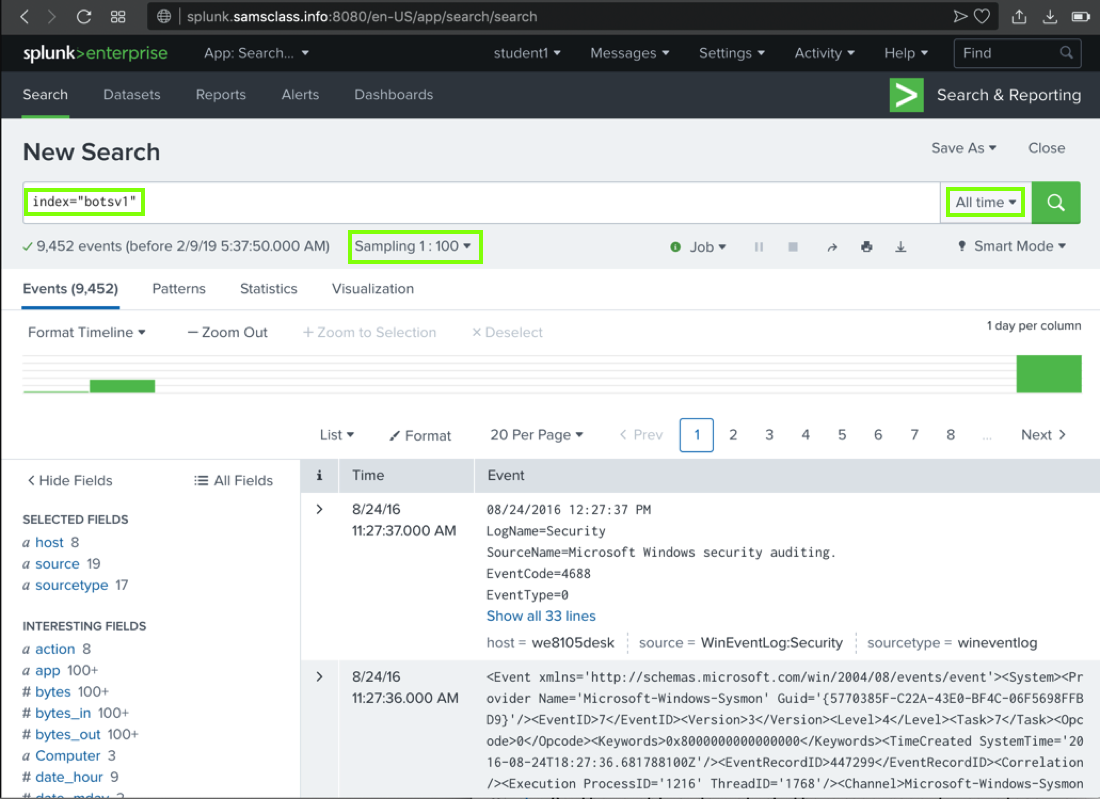
- In the Search box, type
index="botsv1"
- On the right side, click the "Last 24 hours" box and click "All time"
- On the left side, under the Search box, click "No Event Sampling" and click "1: 100"
- On the right side, click the green magnifying-glass icon
The search finishes within a few seconds, and finds
approximately 9,452 results,
as shown below.
(The number varies because
the sampling is random.)
There are actually 100x as many events, but we are only
looking at 1% of them for now.
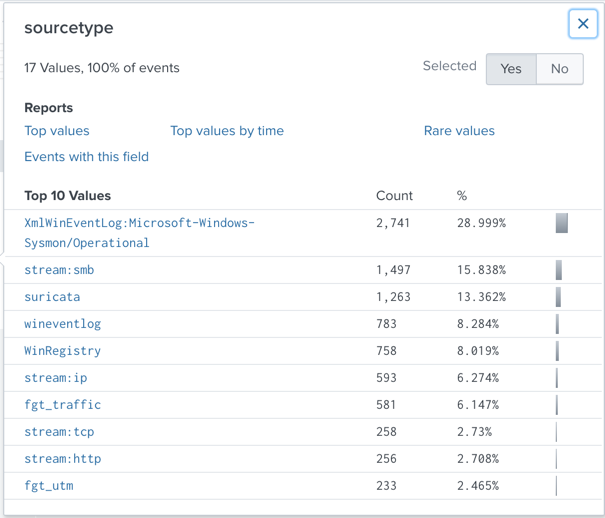
Viewing Sourcetypes
On the lower left, in the "SELECTED FIELDS" list,
click the blue sourcetype link.
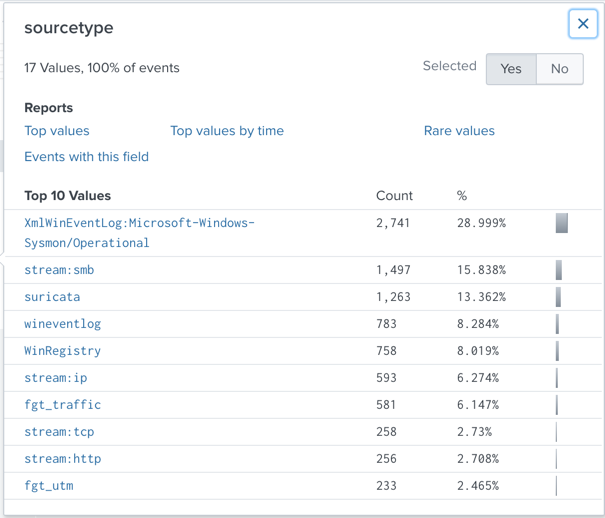
A "sourcetype" box pops up, showing the
"Top 10 Values" of this field,
as shown below.
Notice these items:
sourcetype
| | Sensor
|
|---|
| XmlWinEventLog:Microsoft-Windows-Sysmon/Operational | | "Sysmon", a Windows monitoring tool from Microsoft |
| stream:smb,stream:ip,stream:tcp,stream:http | | "Splunk Stream", which monitors live network traffic |
| suricata | | The Suricata Intrusion Detection System (IDS) |
| wineventlog and WinRegistry | | Windows OS |
| fgt_traffic and fgt_utm | | Fortigate firewalls |
Note: because the sampling is random, you may see
different items near the bottom of this list.
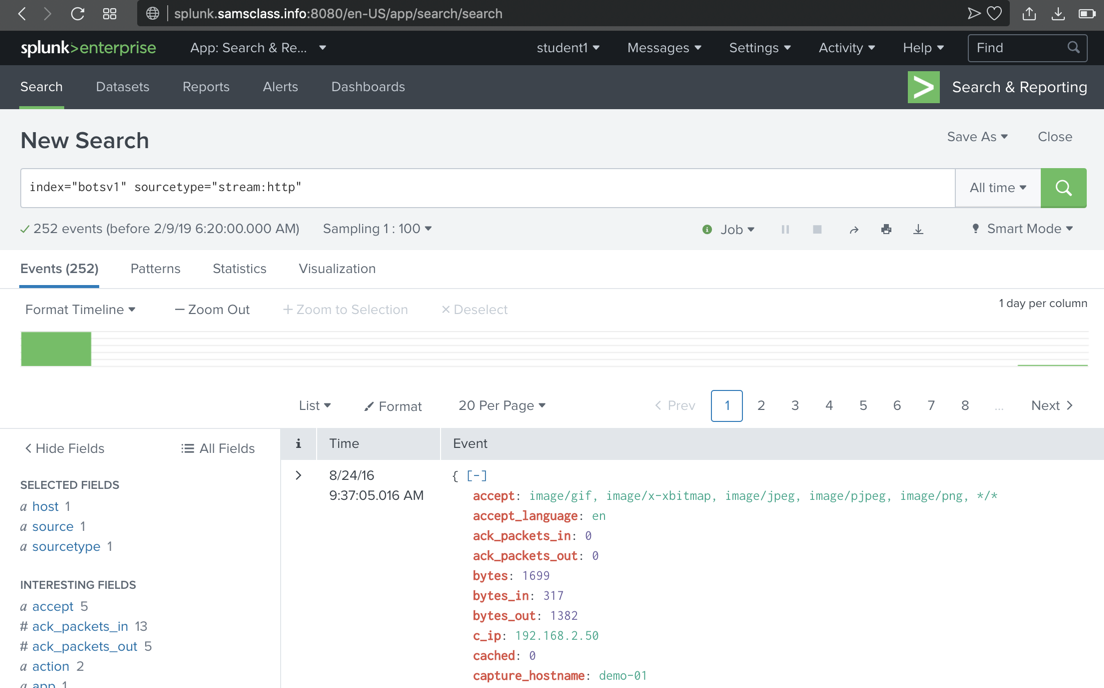
Viewing stream:http Events
In the "sourcetype" box,
in the "Top 10 Values" list,
near the bottom,
if it is visible,
click stream:http
Splunk adds
sourcetype="stream:http"
to
the search and finds approximately 252 results,
as shown below.
If there is no stream:http item in
the list, just type it into the query.
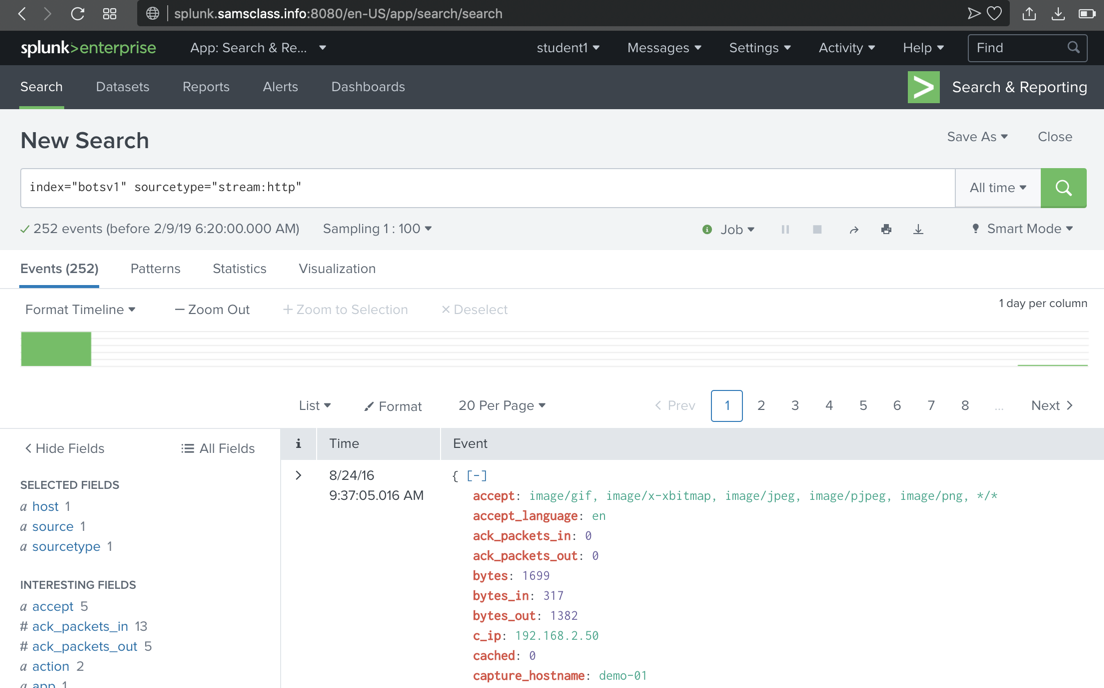
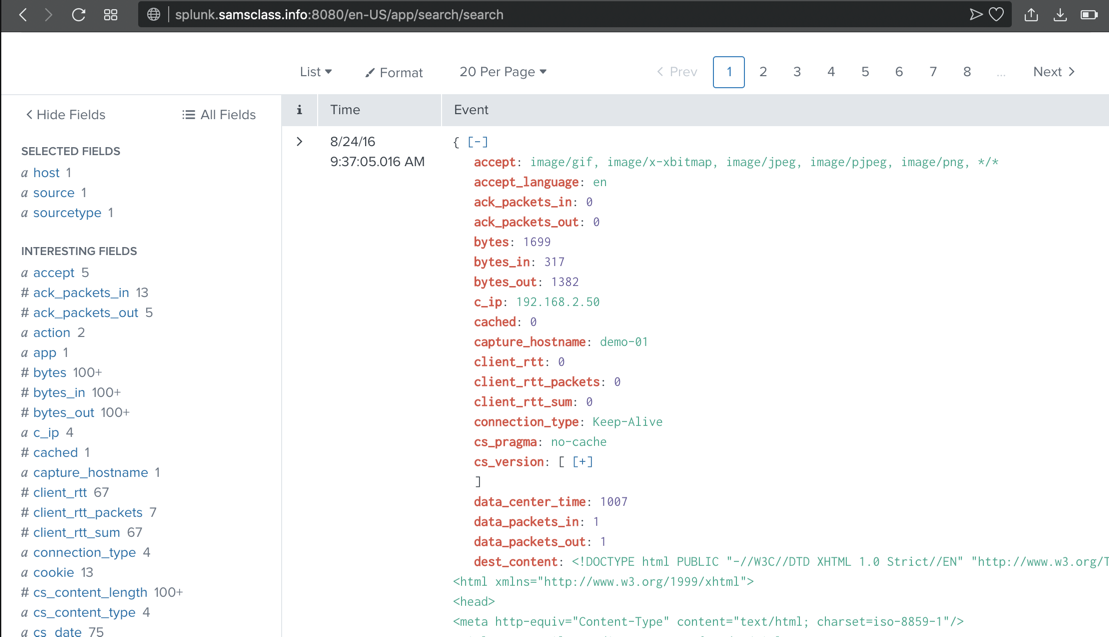
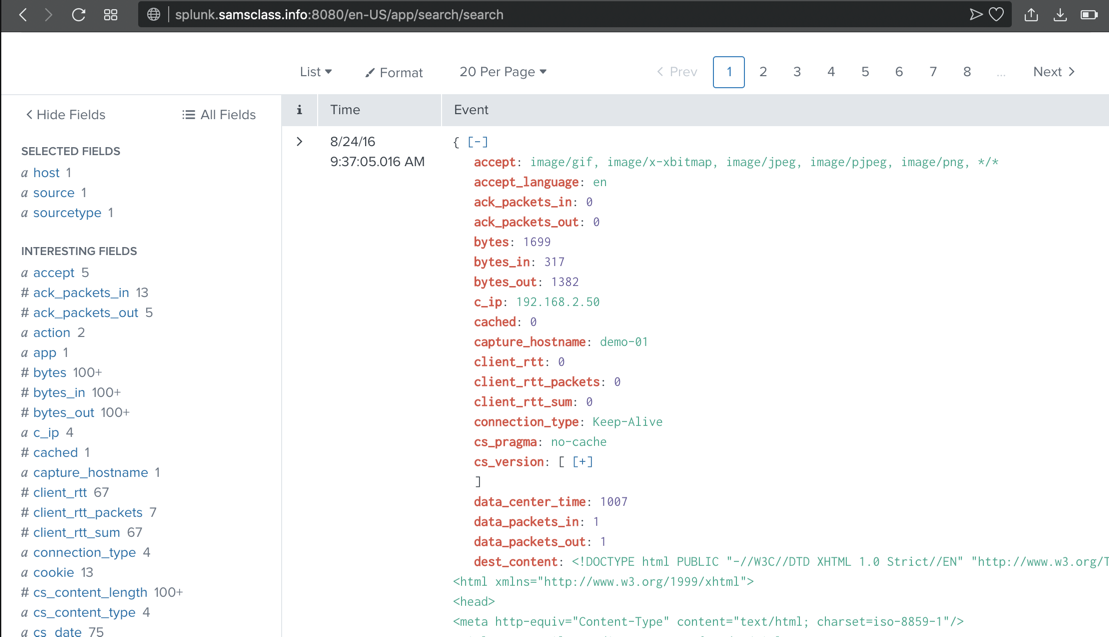
Scroll down to examine the most recent event.
Splunk has parsed this event into many fields,
shown in red, including c_ip,
the client IP address,
as shown below.
These fields are explained
here.
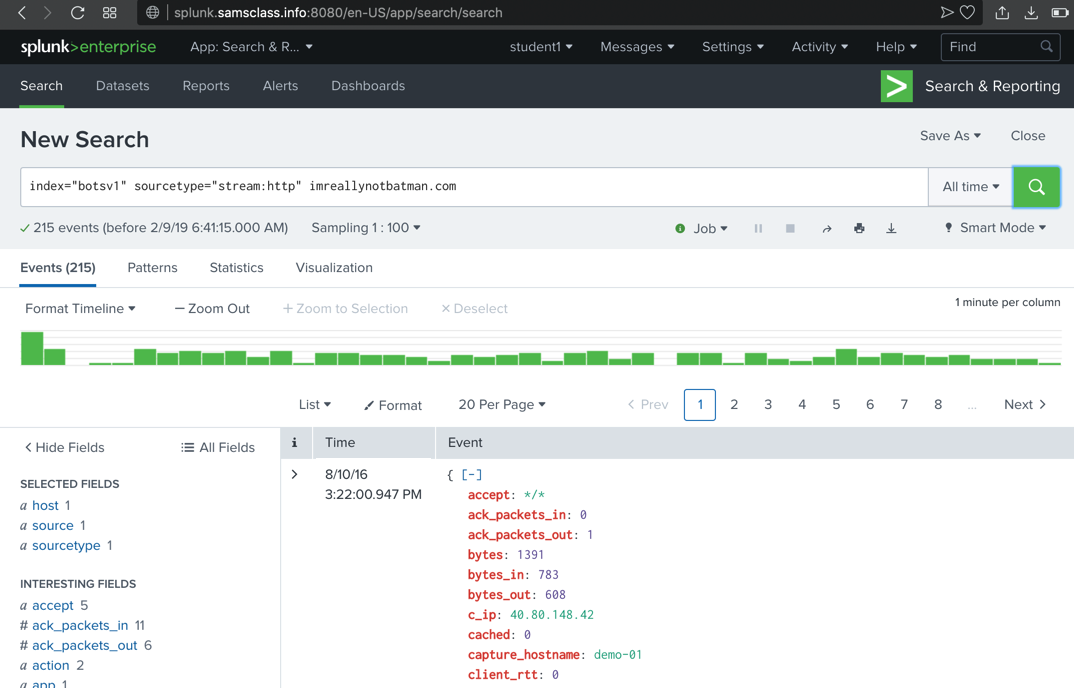
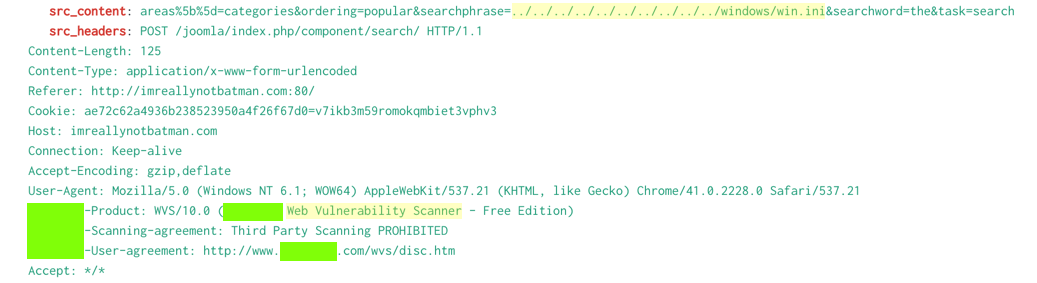
Viewing HTTP Events for imreallynotbatman.com
In the Search box, at the right end, add this text:
imreallynotbatman.com
251 events are found,
as shown below. (The sampling is
random, so you may not see the exact
events shown below.)
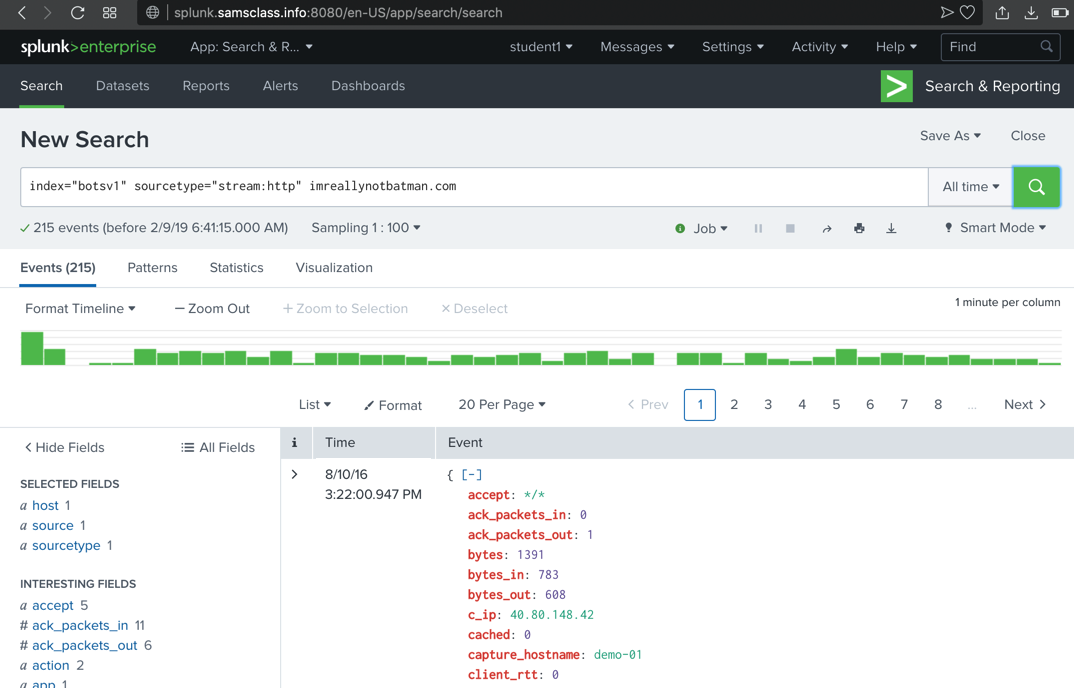
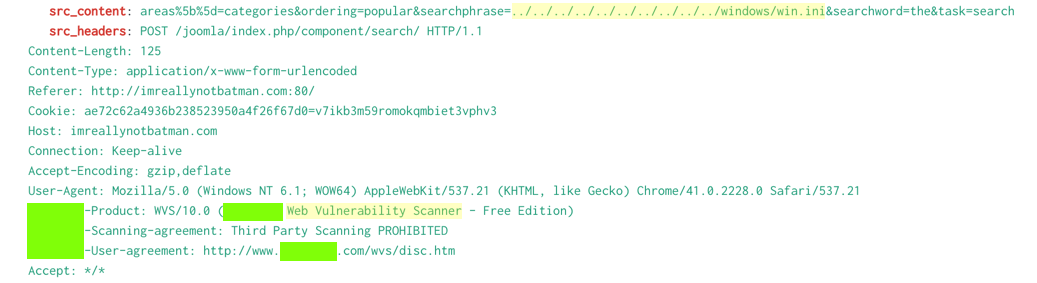
Scroll through the first few events found,
and note these items,
highlighted in the image below.
- You may see obvious attack URLs, such as the directory traversal path containing ../../../../ shown below.
- Many header fields reference a Web Vulnerability Scanner
Level 1: Finding Attack Servers (35 pts)
1.1: Scanner Name (5 pts)
Find the brand name of the vulnerability scanner, covered
by a green box in the image above.
1.2: Attacker IP (5 pts)
Find the attacker's IP address.
1.3: Web Server IP (5 pts)
Find the IP address of the web server serving "imreallynotbatman.com".
1.4: Defacement Filename (10 pts)
Find the name of the file used to deface the web server serving "imreallynotbatman.com".
Hints:
- It was downloaded by the Web server, so the server's IP is a client address, not a destination address.
- Remove the filter to see all 9 such events. Examine the uri values.
1.5: Domain Name (10 pts)
Find the fully qualified domain name (FQDN) used by the staging server hosting the defacement file.
Hints:
- Examine the 9 events from the previous challenge. Look at the url values.
Level 2: Identifying Threat Actors (50 pts)
2.1: Staging Server IP (10 pts)
In Level 1, you found the staging server domain name (used to host the defacement file). Find that server's IP adddress.
Hints:
- Search for HTTP GET events containing the target FQDN.
2.2: Leetspeak Domain (10 pts)
Use a search engine (outside Splunk) to find other domains on the staging server. Search for that IP address. Find a domain with an name in Leetspeak (like "1337sp33k.com").
Hints:
- Try just Googling the IP address
- VirusTotal Search works too
2.3: Brute Force Attack (15 pts)
Find the IP address performing a brute force attack against "imreallynotbatman.com".
Hints:
- Find the 15,570 HTTP events using the POST method.
- Exclude the events from the vulnerability scanner.
- Examine the form_data of the remaining 441 events. Add a unique string from the
attack traffic to find the 413 login events.
2.4: Uploaded Executable File Name (15 pts)
Find the name of the executable file the attacker uploaded to the server.
Hints:
- Find the 15,570 HTTP events using the POST method.
- Exclude the events from the vulnerability scanner.
- Search for common Windows executable filename extensions.
Level 3: Using Sysmon and Stream (50 pts)
3.1: MD5 (10 pts)
In Level 2, you found
the name of an executable file the
attackers uploaded to the server.
Find that file's MD5 hash.
Hints:
- Find events containing that file's name from Sysmon with Event Id 7 or 1.
- Event Id is the key when using Microsoft event logs.
3.2: Brute Force (10 pts)
What was the first brute force password used?
Hints:
- Start with 1:10 sampling.
- Find events containing "login".
- Find top values of "url".
- Examine the "form_data" values to identify the brute force attack.
3.3: Correct Password (10 pts)
What was the correct password found in the brute force attack?
Hints:
- Find the events with the "form_data" values indicating a login attempt.
- There are two different "http_user_agent" values.
3.4: Time Interval (10 pts)
How many seconds elapsed between the time the brute force password scan identified the correct password and the compromised login? Round to 2 decimal places.
Hints:
- HINT: Find the two events with the correct password in the "form_data" field.
3.5: Number of Passwords (10 pts)
How many unique passwords were attempted in the brute force attack?
Level 4: Analyzing a Ransomware Attack (180 pts)
4.1: IP Address (5 pts)
What was the most likely IP address of we8105desk on 24AUG2016?
Hints:
- Search for events containing we8105desk on the date 24AUG2016. There are 115,991 events.
- Look at the src_ip values. There are only a few choices.
- Another way is to look at sourcetype="stream:ldap" events with that hostname on that day. There are 48 events, all from the same src_ip value.
4.2: Signature (5 pts)
Amongst the Suricata signatures that detected the Cerber malware, which one alerted the fewest number of times? Submit ONLY the signature ID value as the answer. (No punctuation, just 7 integers.)
Hints:
- Search for Cerber -- you find 21,596 events.
- Examine the source field -- there are 4 values.
- Explore the source type associated with Suricata.
4.3: FQDN (15 pts)
What fully qualified domain name (FQDN) does the Cerber ransomware attempt to direct the user to at the end of its encryption phase?
Hints:
- Examine the five Suricata alerts about Cerber. View them as "raw text" in time order.
- Find a time delay and the domain lookup events after it. Note the latest time of those events.
- Search events near that time. Examine events with sourcetype=suricata.
4.4: Suspicious Domain (15 pts)
What was the first suspicious domain visited by we8105desk on 24AUG2016?
Hints:
- Find the Suricata events on that day. There are 86,579 of them.
- Examine the src_ip field. Restrict your query to the desired value.
- Examine the event_type field. Restrict your query to events that load Web pages. There are 38 of them.
- Examine the hostnames visited. There are ten of them. Investigate them with Google and find the one that's known to be malicious.
4.5: VB Script (15 pts)
During the initial Cerber infection a VB script is run. The entire script from this execution, pre-pended by the name of the launching .exe, can be found in a field in Splunk. What is name of the first function defined in the VB script?
Hints:
- Search for events with both a .vbs filename extension and an .exe extension.
- Read the events to identify normal ones and find the suspicious ones.
4.6: VB Script (15 pts)
During the initial Cerber infection a VB script is run. The entire script from this execution, pre-pended by the name of the launching .exe, can be found in a field in Splunk. What is the length in characters of the value of this field?
Hint:
- Find the length of the Splunk field, not the length of the script itself.
This may be helpful.
- The "eval length" operation adds a "length" field to the events.
4.7: USB key (15 pts)
What is the name of the USB key inserted by Bob Smith?
Hints:
- You want a "Volume Name" as discussed here.
4.8: Server Name (5 pts)
Bob Smith's workstation (we8105desk) was connected to a file server during the ransomware outbreak. What is the domain name of the file server?
Hints:
4.9: IP Address (15 pts)
Bob Smith's workstation (we8105desk) was connected to a file server during the ransomware outbreak. What is the IP address of the file server?
Hints:
- Search for the server's name. Examine the source of those events. Look for source types that record raw network data and would therefore include IP addresses.
4.10: PDFs (20 pts)
How many distinct PDFs did the ransomware encrypt on the remote file server?
Hints:
- Search for .pdf
- Restrict your search for the suspicious app
- Find all unique filenames. Remove filenames outside the time range of the attack.
4.11: Process ID (15 pts)
The VBscript found above launches 121214.tmp. What is the ParentProcessId of this initial launch?
Hints:
- Search for 121214.tmp -- you find 190 events.
- Examine the EventDescription field and focus on the one most closely related to the question.
- Examine the CommandLine field.
4.12: Text Files (15 pts)
The Cerber ransomware encrypts files located in Bob Smith's Windows profile. How many .txt files does it encrypt?
Hints:
- Find all events including.txt and find the path to Bob's Windows profile.
- Add Bob's Windows profile path to the search. To search for a backslash, enter two backslashes.
- Examine the file paths and remove the ones outside Bob's profile.
4.13: File Name (15 pts)
The malware downloads a file that contains the Cerber ransomware cryptor code. What is the name of that file?
Hints:
- Search for HTTP downloads from the Cerber-related domain you found above.
- The filename has a surprising extension. Research that filename outside Splunk to verify that it's related to Cerber.
4.14: Obfuscation (10 pts)
Now that you know the name of the ransomware's encryptor file, what obfuscation technique does it likely use?
Hints:
- Research the file using online resources, outside Splunk, to find this.
Posted 5-10-19
Scoring engine removed for WCIL 5-20-19
2.1 hint changed 6-17-19
Scores archived, links set to open new tabs 10-23-19
Hints added