Log in as student1 with a password of student1
The Splunk main page opens, as shown below.
At the top left, click "Search & Reporting".
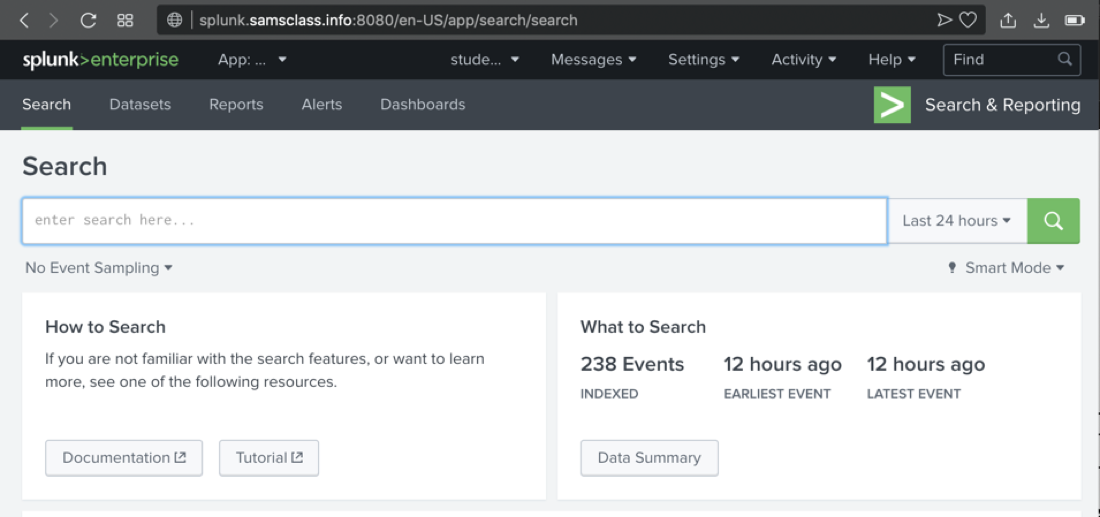
The "Search" page opens, as shown below.
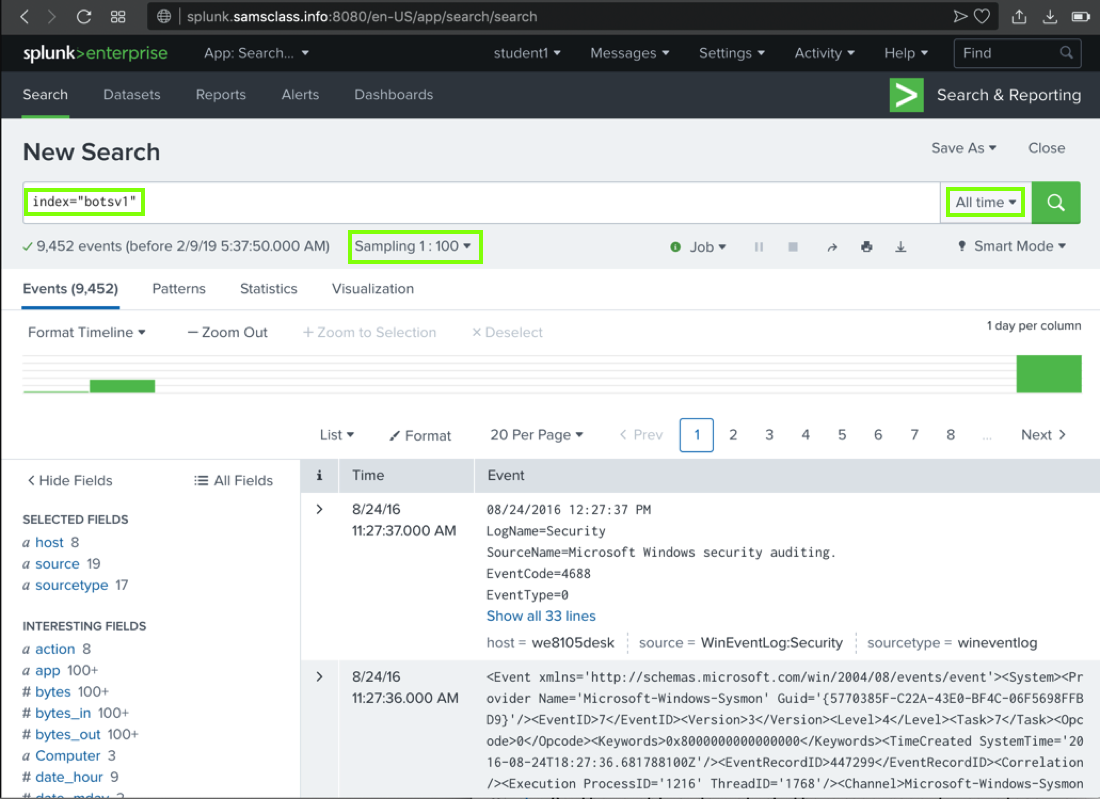
index="botsv1"
There are actually 100x as many events, but we are only looking at 1% of them for now.
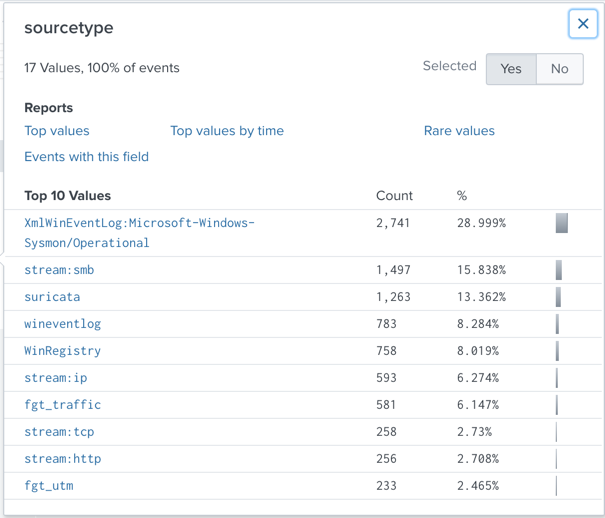
A "sourcetype" box pops up, showing the "Top 10 Values" of this field, as shown below.
Notice these items:
Note: because the sampling is random, you may see different items near the bottom of this list.
sourcetype
Sensor
XmlWinEventLog:Microsoft-Windows-Sysmon/Operational "Sysmon", a Windows monitoring tool from Microsoft stream:smb,stream:ip,stream:tcp,stream:http "Splunk Stream", which monitors live network traffic suricata The Suricata Intrusion Detection System (IDS) wineventlog and WinRegistry Windows OS fgt_traffic and fgt_utm Fortigate firewalls
Splunk adds
sourcetype="stream:http"
to
the search and finds approximately 252 results,
as shown below.
If there is no stream:http item in the list, just type it into the query.
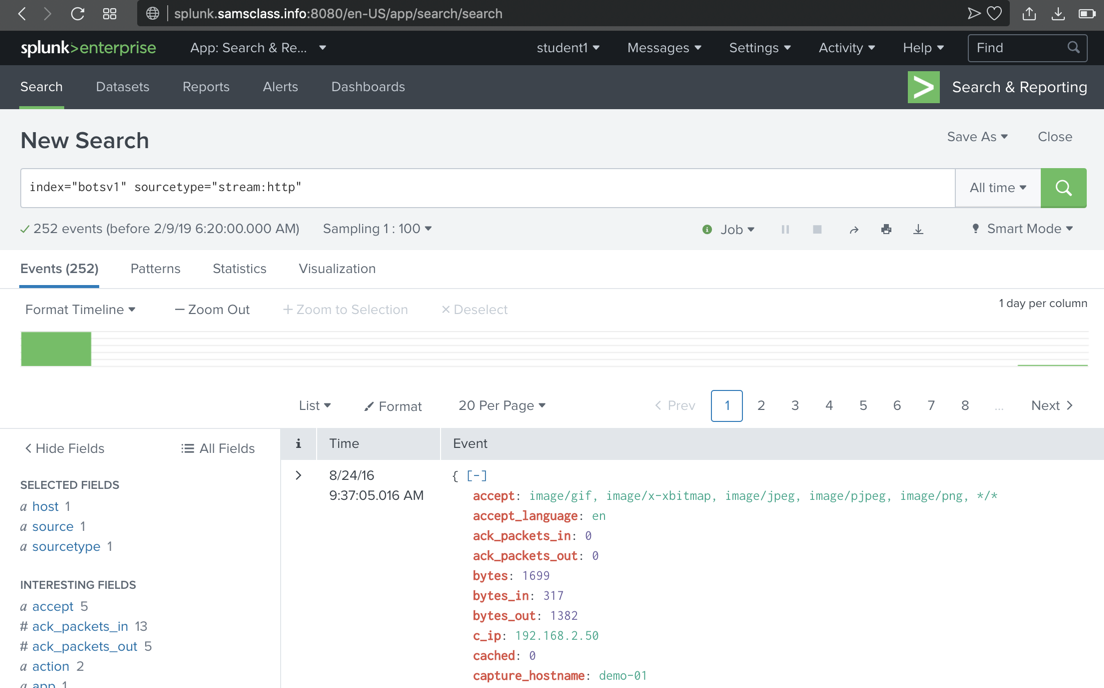
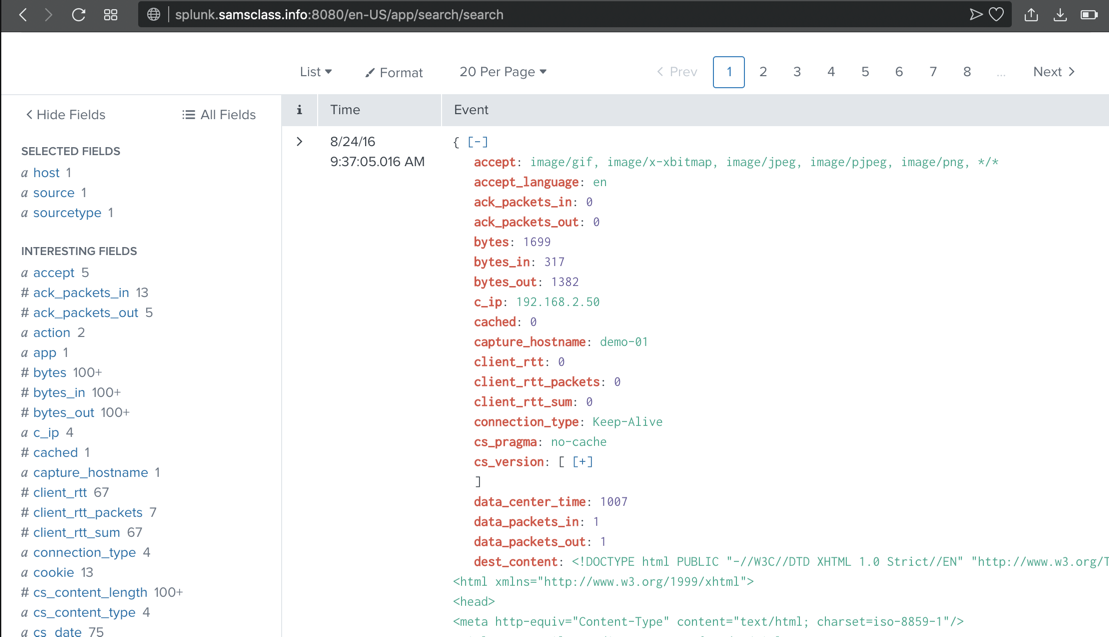
Scroll down to examine the most recent event. Splunk has parsed this event into many fields, shown in red, including c_ip, the client IP address, as shown below.
These fields are explained here.
imreallynotbatman.com
251 events are found,
as shown below. (The sampling is
random, so you may not see the exact
events shown below.)
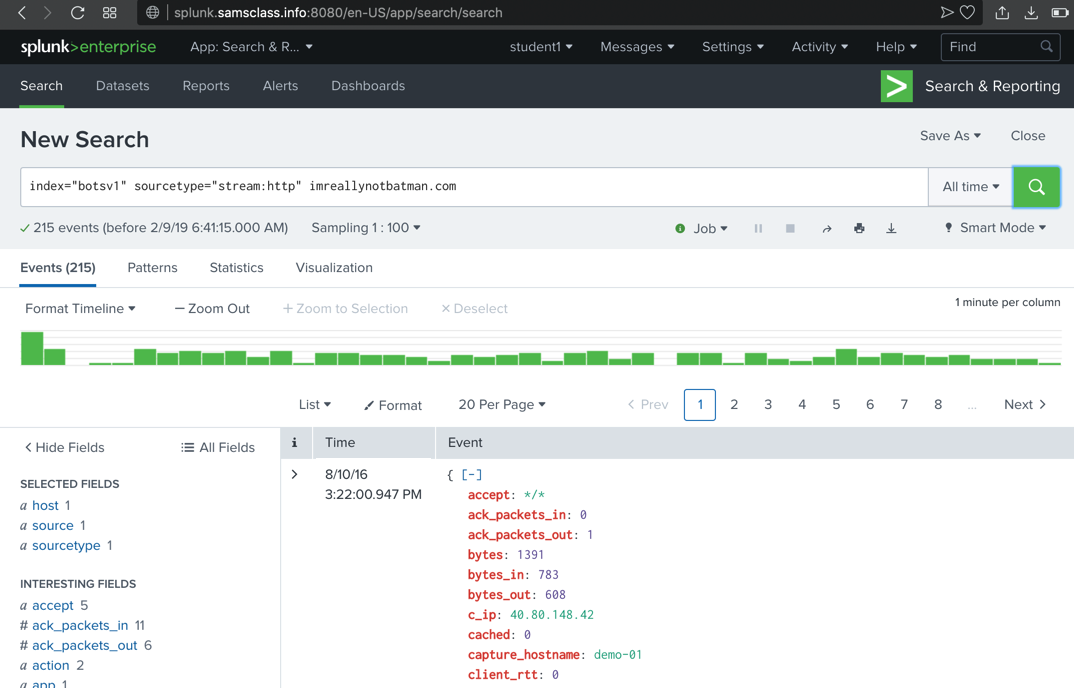
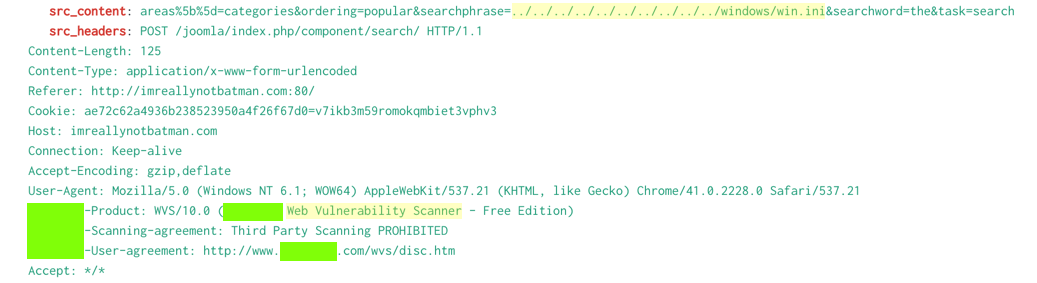
Scroll through the first few events found, and note these items, highlighted in the image below.
Splunk References