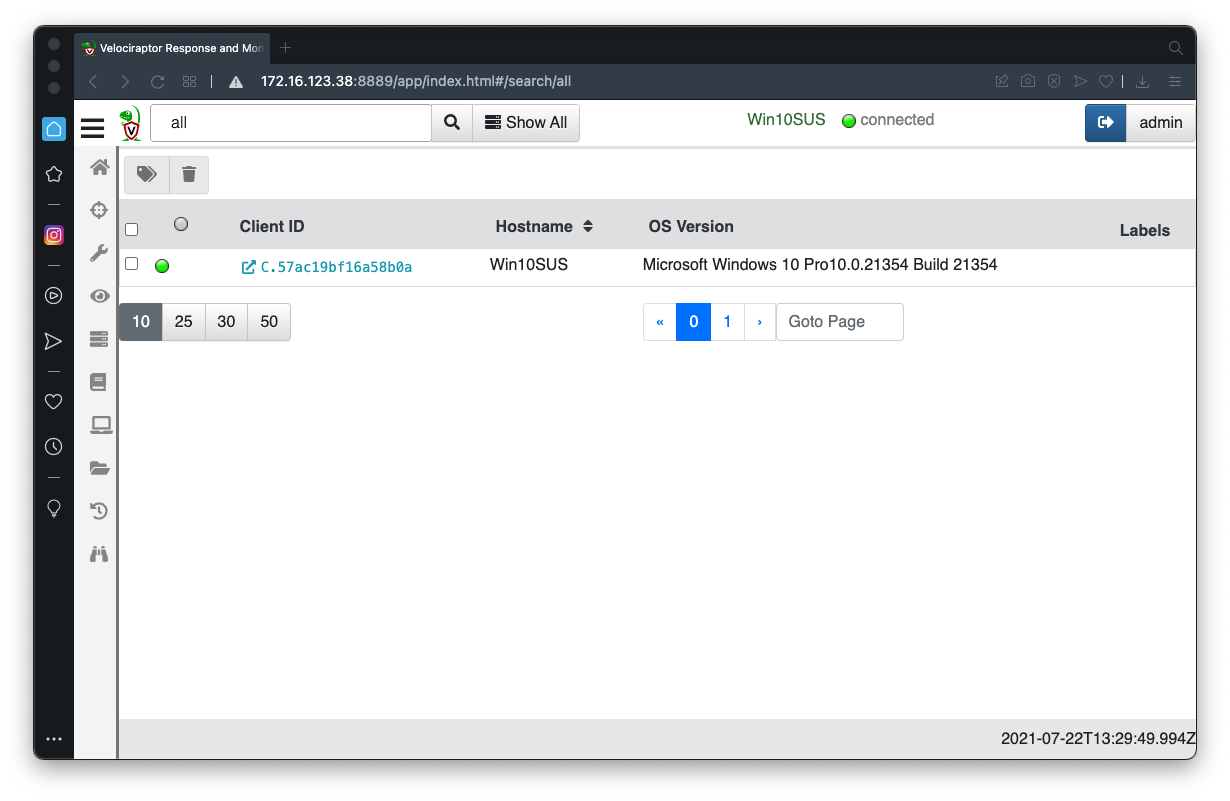
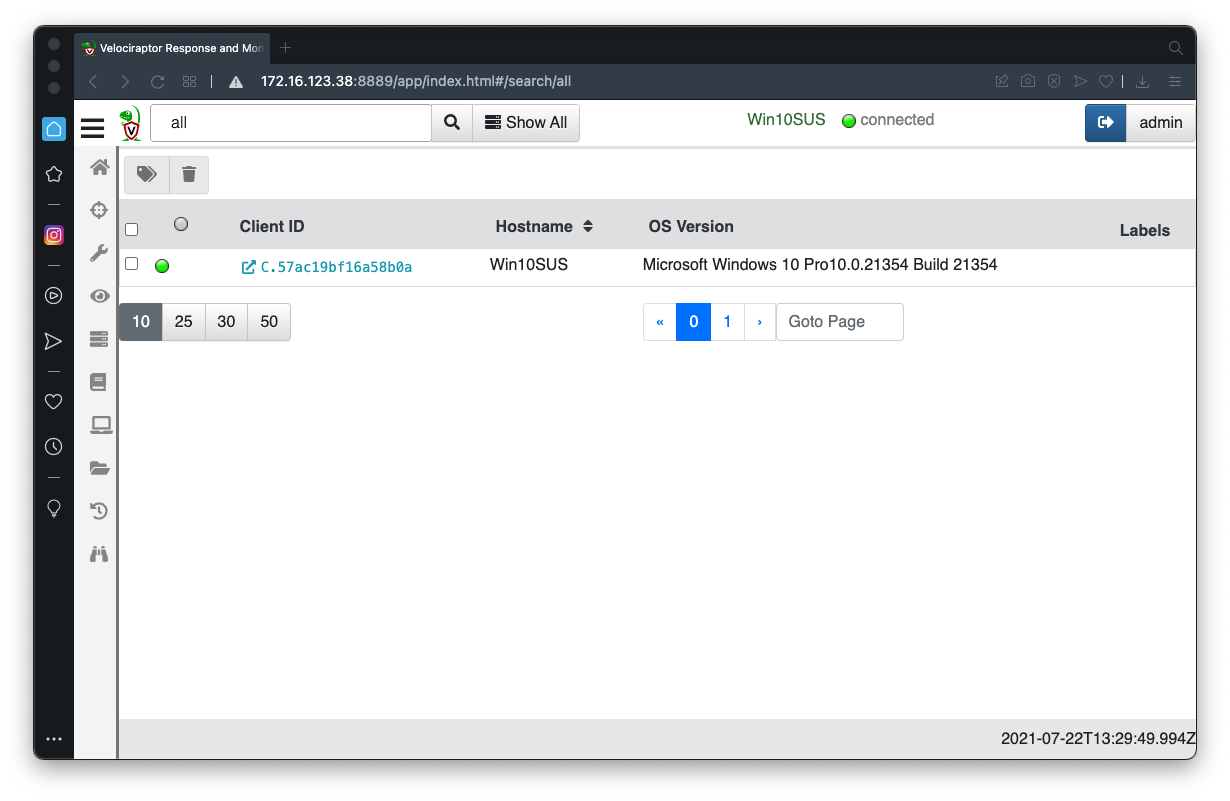
In the Velociraptor GUI, at the top center, click the "Show All" button.
Click your client's Client ID, which appears in blue text, as shown below.
Windows.Sysinternals.SysmonInstallIf you are using Windows on an Intel processor, launch this artifact without changing the parameters.
Examine the Results. This installation should succeed.
Windows on Apple Silicon (ARM)
If you are using Windows on ARM (a Mac M1 or later host), you need to manually install sysmon.At the top right of the Velociraptor page, click the green button labelled DESKTOP.
Click >_Shell.
Select a shell type of Powershell and execute these commands, one by one, as shown below:
Select a shell type of Cmd and execute the command below:Sysmon should install and start successfully, as outlined in red in the image below.
Download and install the appropriate version of 7-Zip for your hardware.
Execute the steps below on your Windows machine.
IR 374.1: Auditing Network Connections (5 pts)
Launch this collector, with no parameter changes.Windows.Network.NetstatThe flag is the port the "shellbind" process is listening on, covered by a green rectangle in the image below.
IR 374.2: Auditing Autoruns (10 pts)
Launch this collector, with no parameter changes.Windows.Sysinternals.AutorunsThere are more than 1000 results.Use the button outlined in red in the image below to download a JSON file. Search that file for shellbind.
The flag is the path to the "shellbind.exe" file, covered by a green rectangle in the image below.
Make a note of this path--you'll need it later.
IR 374.3: Creation Time (5 pts)
Note: you must first find the path in 374.2Launch this collector:
Windows.System.PowerShellIn "Confgure Parameters", do a directory of the folder containing the "shellbind.exe" file.That folder contains two files, with different timestamps. Find the more recent timestamp, outlined in red in the image below. This is the time of the attack, which will be helpful when examining logs later.
The flag is covered by a green rectangle in the image below.
IR 374.4: Prefetch (5 pts)
Launch this collector:Windows.Forensics.PrefetchIn "Confgure Parameters", enter a "binaryRegex" of shellbind.exeNote the LastRunTimes, in red font in the image below. This is the time of the attack, which will be helpful when examining logs later. I ran it twice, so I have two run times--you will only have one time.
The flag is covered by a green rectangle in the image below.
IR 373.5: Sysmon Logs (10 pts)
Launch this collector to collect the sysmon event logs:Windows.EventLogs.EvtxHunterUse this parameter:IocRegex shellbindLook through the Message column for the events until you find the event shown below, with the command line outlined in red. This command was used to extract and decrypt the shellcode.The flag is covered by a green rectangle in the image below.
Posted 9-30-21
Updated for Win 11 on 11-29-24