NOT RECOMMENDED
This software seems to not work with modern versions of Windows.It's here for extra credit if you want to spend a lot of time debugging, but I don't recommend wasting your time.
Skip it and go on to other projects.
In this project, we perform a sloppy installation to learn how the product works. In a real deployment, the server should be concealed behind a proxy, and secured in other ways, as explained here.
sudo apt update
sudo apt install mysql-server -y
sudo mysql_secure_installation
sudo mysql -u root -p
Execute these commands:
SET GLOBAL max_allowed_packet=41943040;
CREATE USER 'grr'@'localhost' IDENTIFIED BY 'password';
CREATE DATABASE grr;
GRANT ALL ON grr.* TO 'grr'@'localhost';
flush privileges;
exit;
wget https://storage.googleapis.com/releases.grr-response.com/grr-server_3.4.2-3_amd64.deb
sudo apt install -y ./grr-server_3.4.2-3_amd64.deb
On your Linux server, in an SSH session, execute this command:
systemctl status grr-server
Press Q to exit the status display.
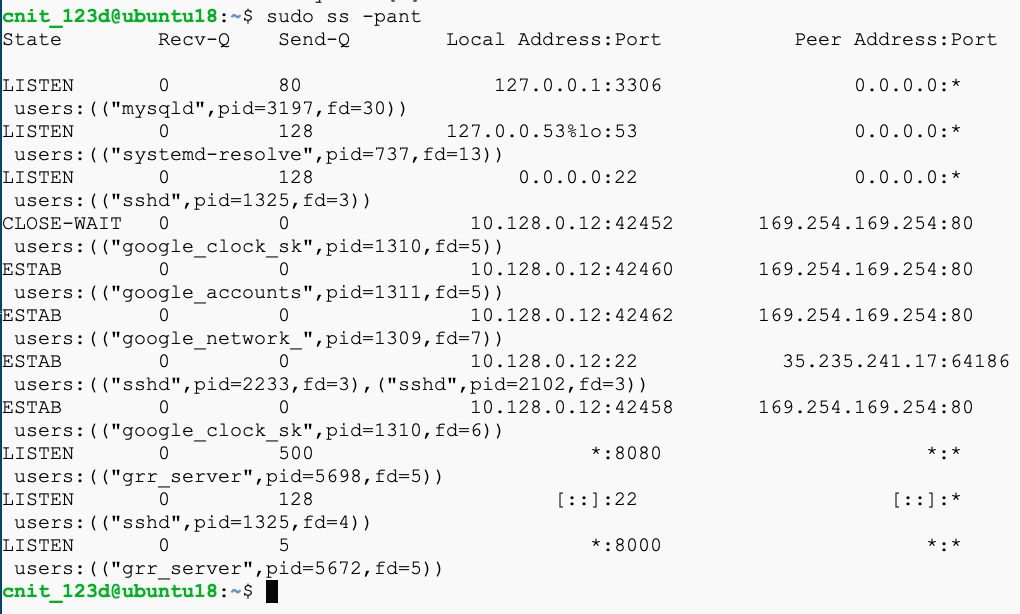
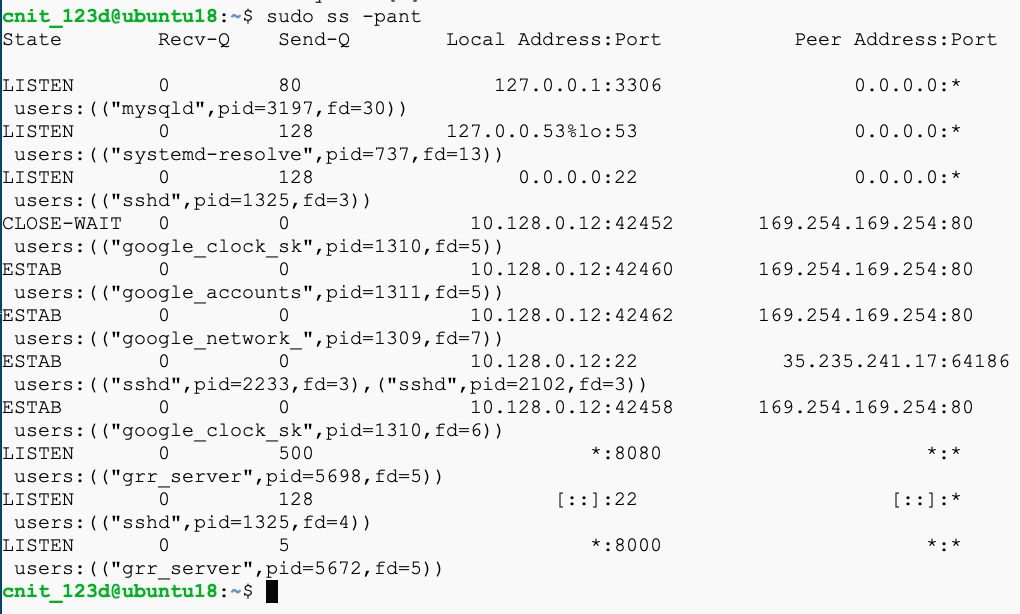
On your Linux server, in an SSH session, execute this command:
sudo ss -pant
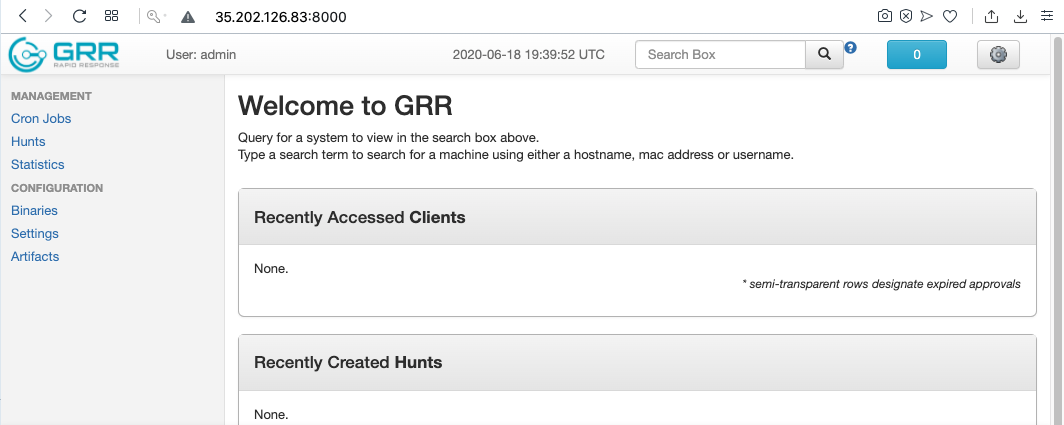
http://35.202.126.83:8000
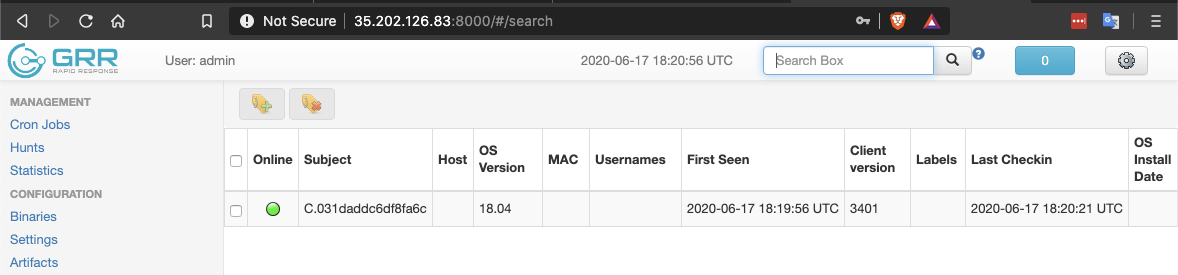
Log in with a username of admin and the admin password you chose earlier. The GRR management page appears, as shown below.
Troubleshooting: Resetting the Password
To reset the admin password, in an SSH session, execute this command:
In the GRR management page, on the left side, click Binaries, as shown below.
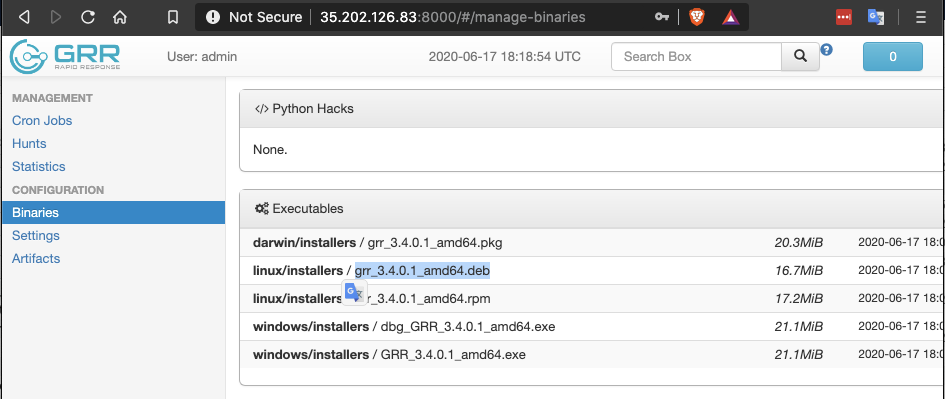
Download the Linux .deb file.
Upload it to your Linux server.
In an SSH session, execute this command:
sudo dpkg -i grr_3.4.0.1_amd64.deb
Your client appears, as shown below.
Download the Windows client.
Run it on your Windows system.
After the installation, in the GRR management page, hit Enter in the search box in the top right corner.
Your second client appears, as shown below.
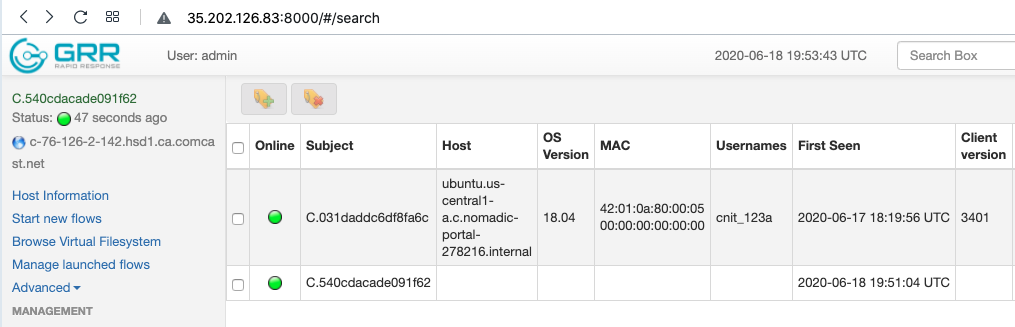
In the Subject line, click the long number on the second line.
More information about the client appears. Click the Interrogate button, as shown below.
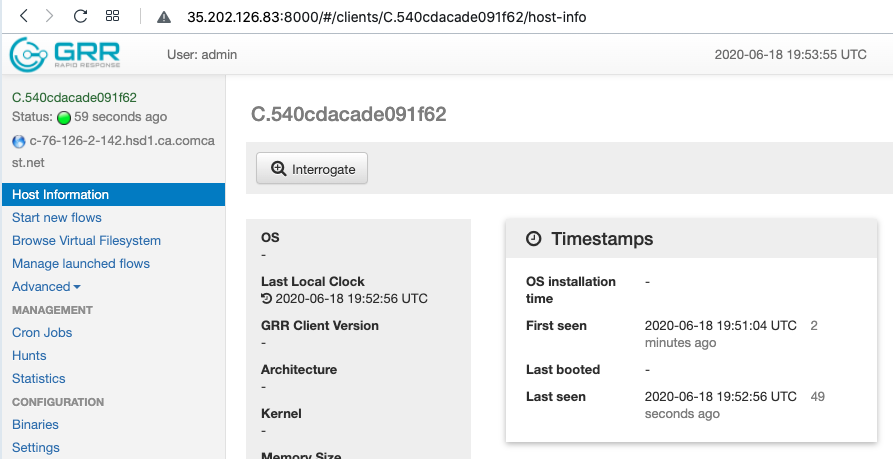
On the right side, click the "Full details" button.
Flag IR 340.1: Client Name (5 pts)
The flag is the Client name, covered by a green rectangle in the image below.
Expand the fs container and click the os container.
In the center of the screen, click the icon with two curved arrows but no R, which refreshes the current directory.
The Windows volumes appear, including C:, as shown below.
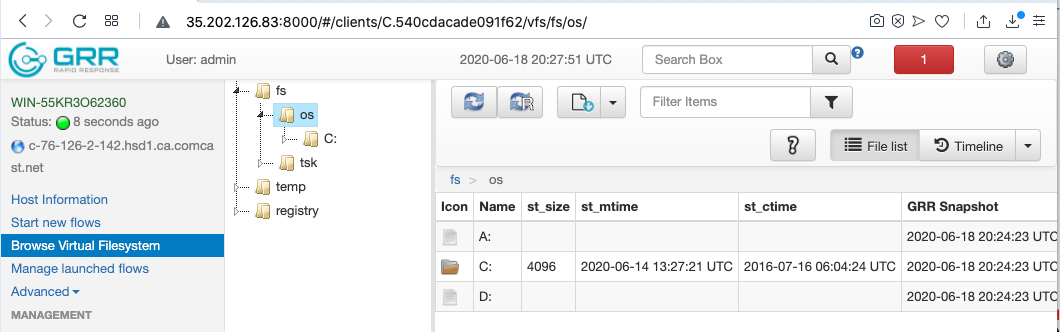
Flag IR 340.2: Version (5 pts)
The flag is covered by a green rectangle in the image below.
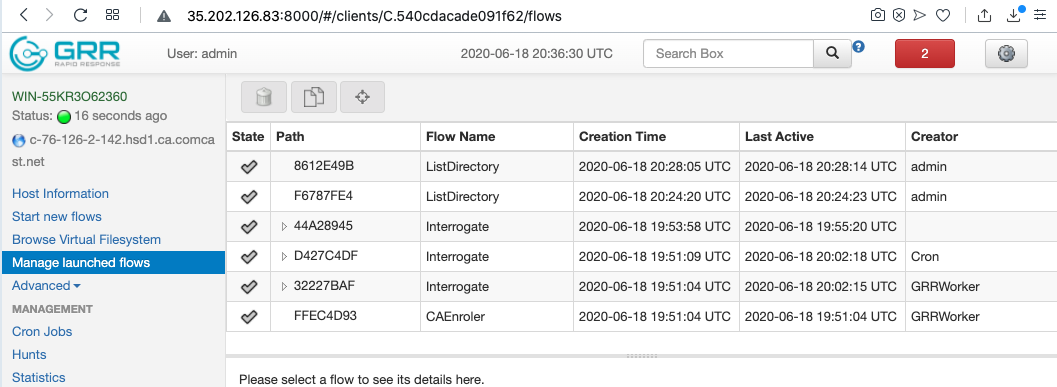
With the Windows host selected, on the left side, click "Manage launched flows".
The flows that have been used so far appear, as shown below.
Don't save the file.
Expand the containers to see the flows available, as shown below.
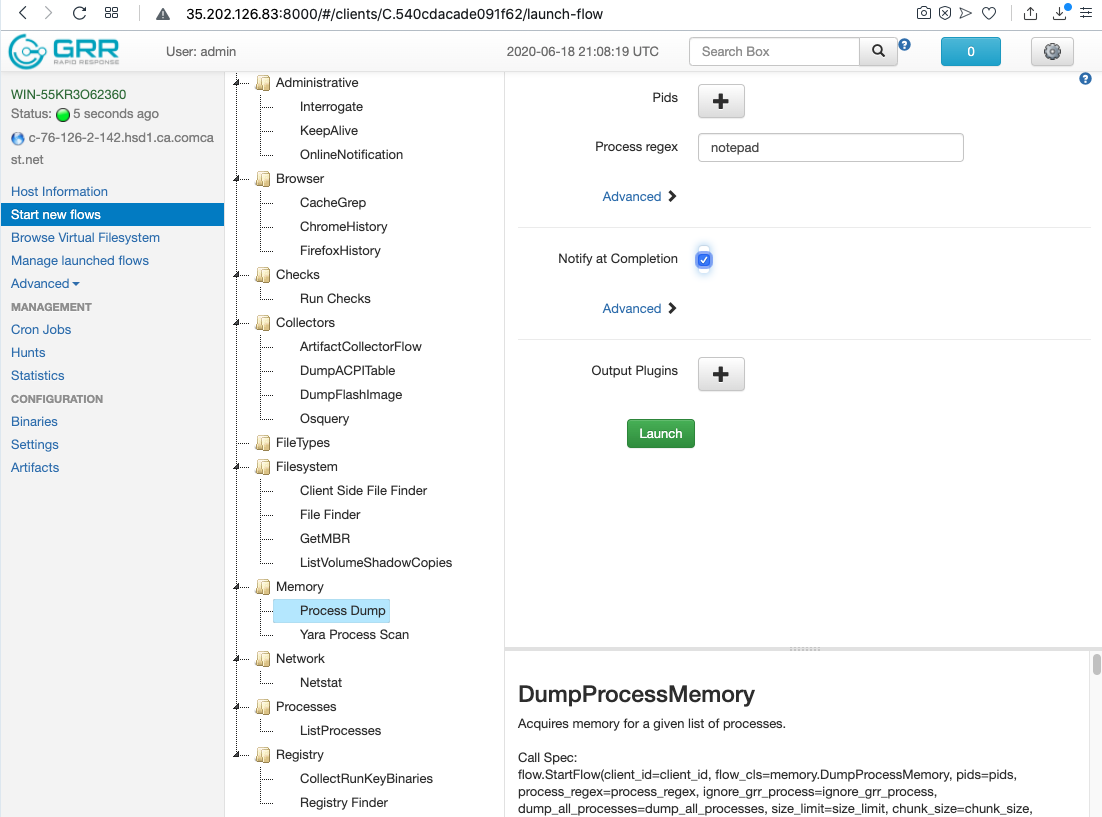
On the right side, in the "Process regex" box, enter notepad, as shown in the image above.
Note that the process name must be in lowercase!
Click the green Launch button.
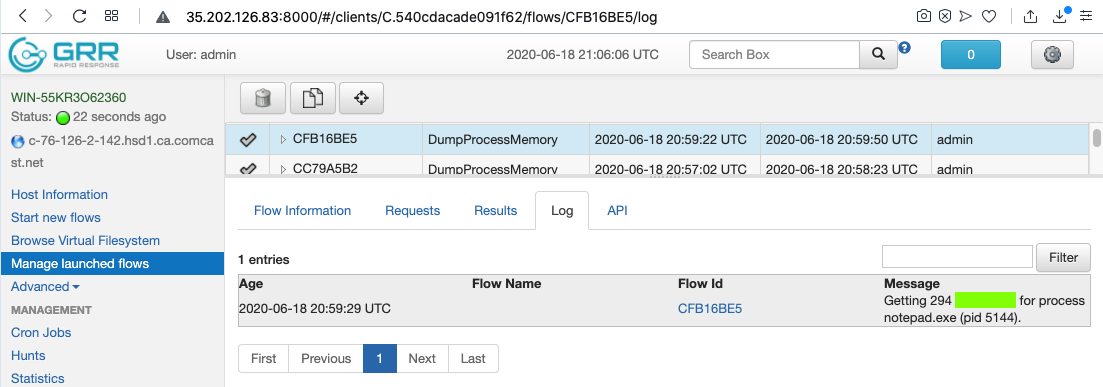
On the left side, click "Manage launched flows".
Click the DumpProcessMemory flow. Click the Log tab.
Flag IR 340.3: Message (5 pts)
The flag is covered by a green rectangle in the image below.
http://ad.samsclass.info/refresh.htm
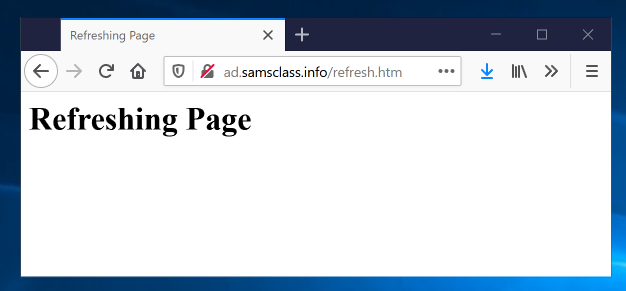
This creates a persistent connection to my server.
sudo apt update
sudo apt install netcat -y
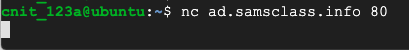
nc ad.samsclass.info 80
This creates a persistent connection to my server.
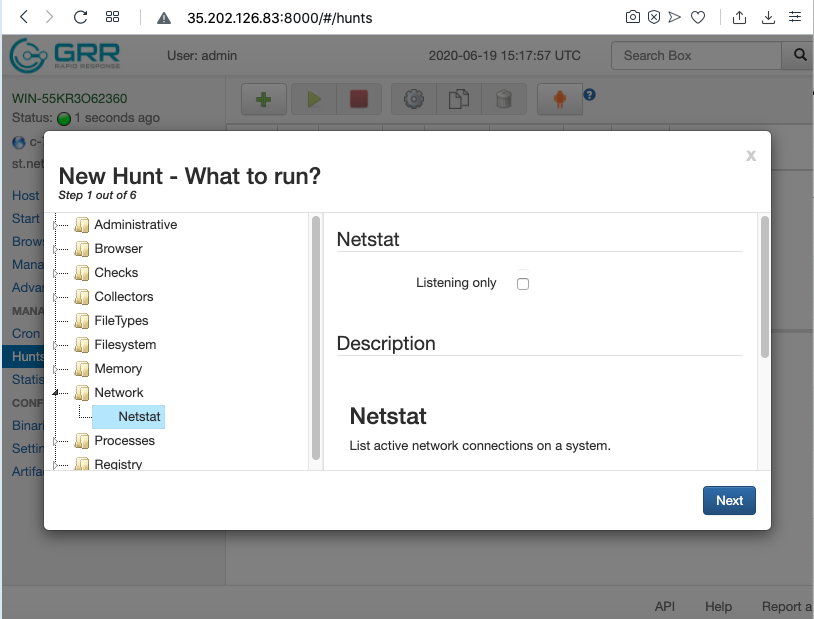
Click the green plus-sign to create a new Hunt.
In the "New Hunt - What to run?" page, expand Network and click Netstat, as shown below.
Then click Next.
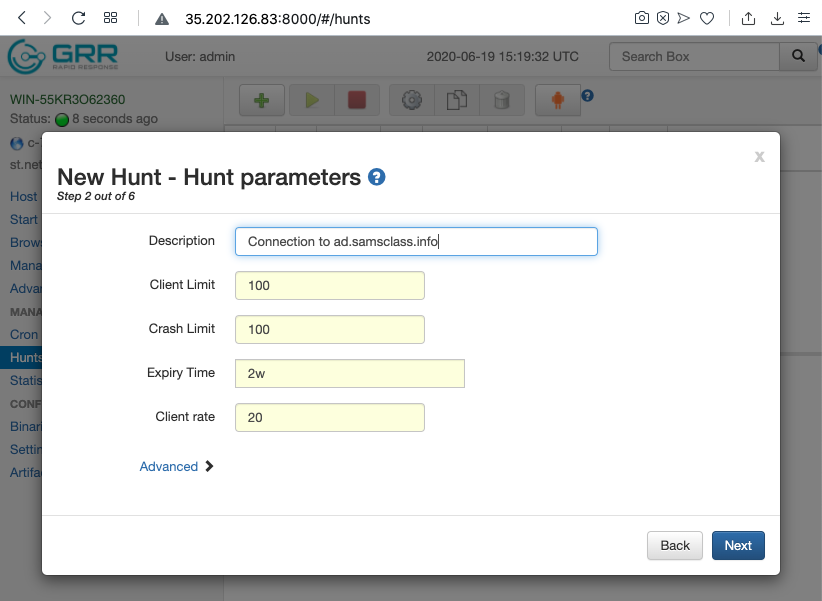
In the "New Hunt - Hunt parameters" page, enter a description, as shown below.
Then click Next.
In the "New Hunt - How to process results" page, click Next.
In the "New Hunt - Where to run?" page, click Next.
In the "New Hunt - Review" page, click "Create hunt".
In the "New Hunt - Result" page, click Done. The new Hunt appears in the list, as shown below.
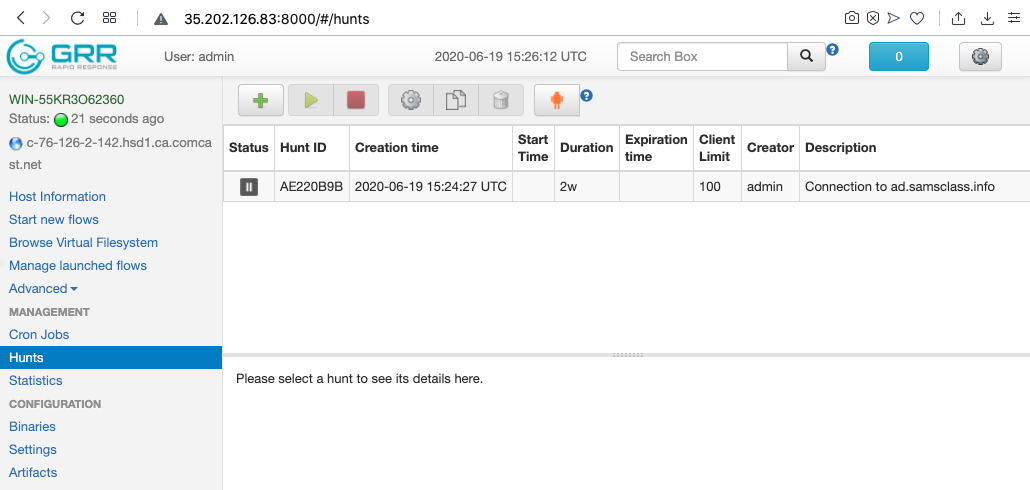
Click the hunt and click the green arrow to start it.
Click Proceed.
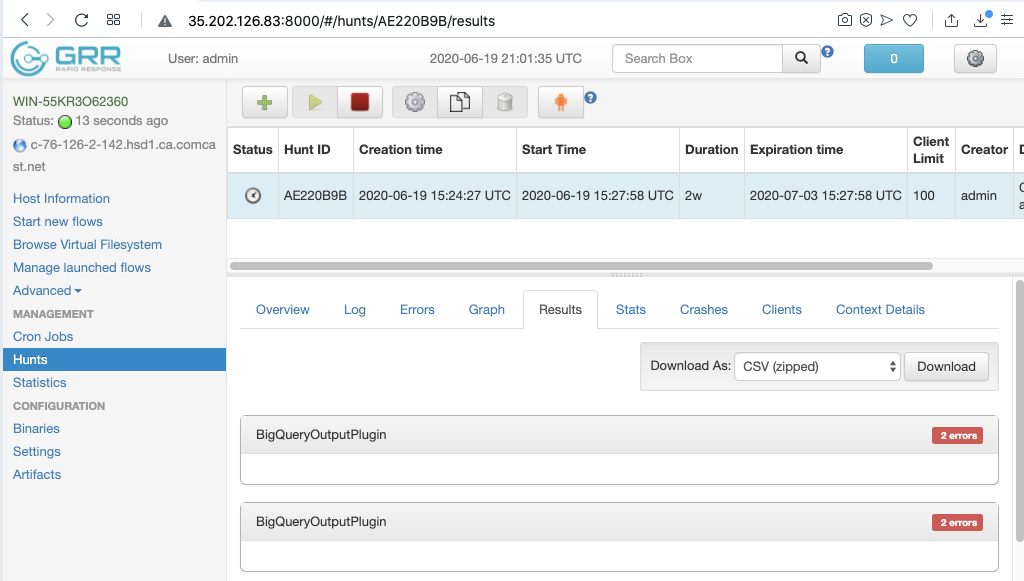
Flag IR 340.4: Filtered Results (10 pts)
Scroll down to the Filter box. Filter for this IP: 159.203.238.50The flag is covered by a green rectangle in the image below.