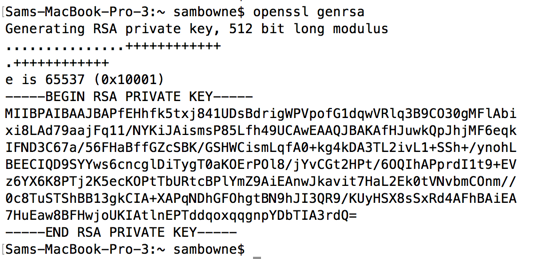
openssl genrsa
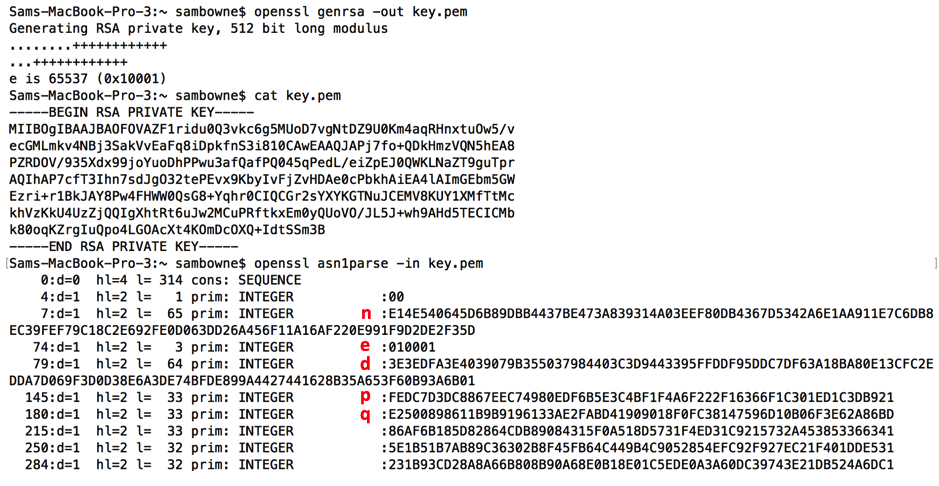
To parse it, you need to save it in a file and use the "asn1parse" command.
Execute these commands to generate a "key.pem" file, view it, and parse it.
openssl genrsa -out key.pem
cat key.pem
openssl asn1parse -in key.pem
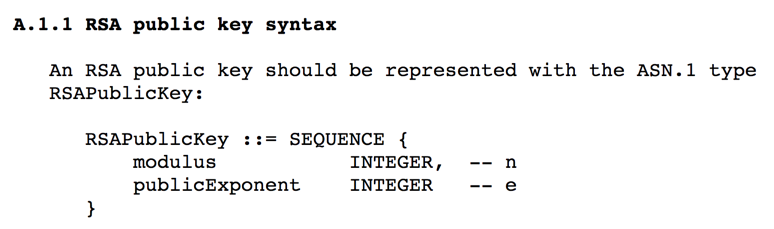
Execute these commands to generate the public key from your "key.pem" file.
openssl rsa -in key.pem -pubout
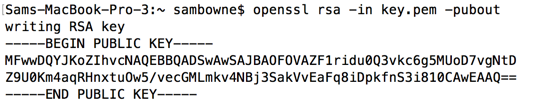
Execute these commands to save the public key in a "public.pem" file, print it out, and parse it:
openssl rsa -in key.pem -out public.pem -pubout
cat public.pem
openssl rsa -pubin -text < public.pem
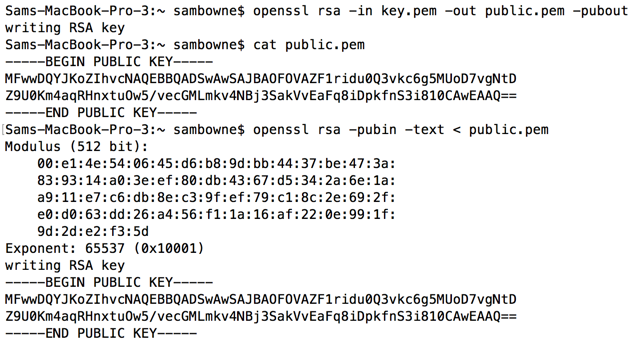
Execute these commands to make a 2048-bit private key and display it.
openssl genrsa -out key2.pem 2048
cat key2.pem
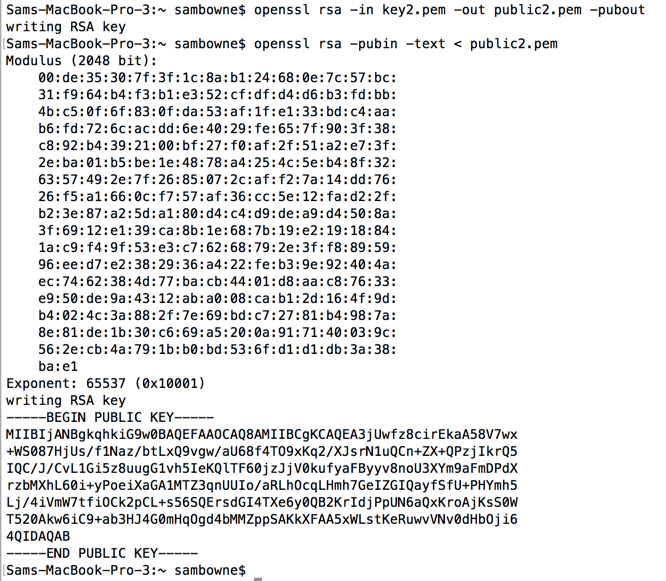
Execute these commands to see the public key.
openssl rsa -in key2.pem -out public2.pem -pubout
openssl rsa -pubin -text < public2.pem
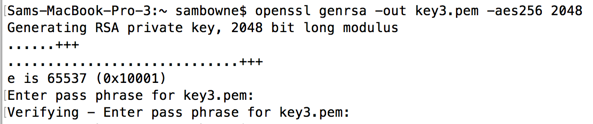
Execute this command to make a 2048-bit encrypted private key file. Enter a password, such as P@ssw0rd, when prompted to.
openssl genrsa -out key3.pem -aes256 2048
Execute this command to see the keyfile:
cat key3.pem
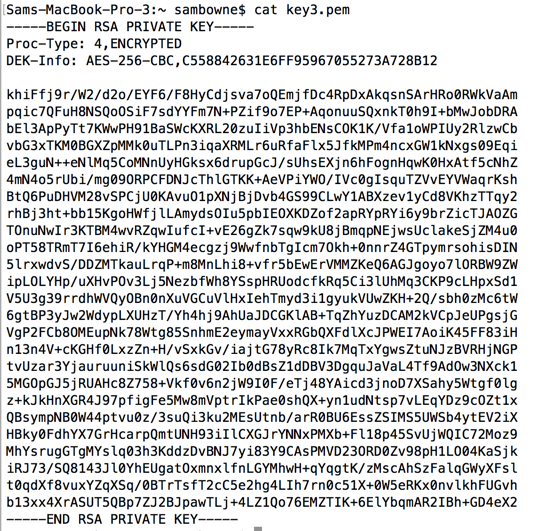
Whenever you use this private key file, you'll need to supply the password.
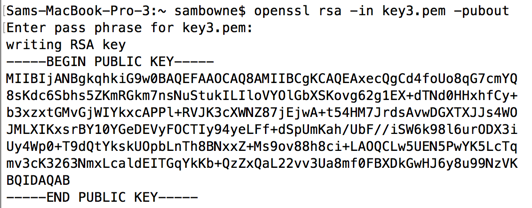
Execute this command to display the public key.
openssl rsa -in key3.pem -pubout
-----BEGIN RSA PRIVATE KEY-----
MD0CAQACCQDTPWtAKLuWbwIDAQABAgh2uVRnKpyb0QIFAP2MzVUCBQDVR/SzAgRu
u6WZAgQ2tLA1AgR2EBWK
-----END RSA PRIVATE KEY-----
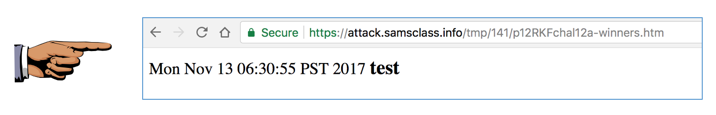
Save a whole-desktop image with the filename "YOUR NAME Proj 12a", replacing "YOUR NAME" with your real name.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
-----BEGIN RSA PRIVATE KEY-----
MD0CAQACCQDTPWtAKLuWbwIDAQABAgh2uVRnKpyb0QIFAP2MzVUCBQDVR/SzAgRu
u6WZAgQ2tLA1AgR2EBWK
-----END RSA PRIVATE KEY-----
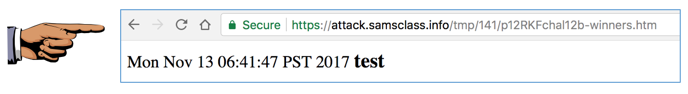
Save a whole-desktop image with the filename "YOUR NAME Proj 12b", replacing "YOUR NAME" with your real name.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
-----BEGIN RSA PRIVATE KEY-----
MIIBPAIBAAJBAOz8ZwiRyoTBYCoExLqzlnr1GJ3D1qk+yQXwSEET2mRfbU+B/cNP
cI6eQUnA4rSOHmwhsSwEXhPnzMvVjqIonPsCAwEAAQJBAIfNH3HOsaGfem65qs5e
xxxxxxxxxObZPrKzfYQlT0miNyOrzA65U3yDa6qAZgwXPJuWU6b86PTPFFUQCei9
TFkCIQD2l+VEohU9goQplYkRnpfujZ6flUm96B6biqnPk9tUTQIhAPYGr50vSZqI
xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
jDyz+KS5z68xHakCIEfyCpb/xhlvsIQZPLMj1q0eaydxrS4OxU0WuiKOCSYPAiEA
nahcVY0yHAgXLvm1vSZgzYrcs1ESCKPQ+KWy8+meq80=
-----END RSA PRIVATE KEY-----
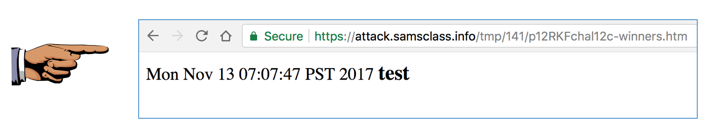
Save a whole-desktop image with the filename "YOUR NAME Proj 12c", replacing "YOUR NAME" with your real name.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
-----BEGIN RSA PRIVATE KEY-----
MIIBPAIBAAJBANY4uzFtiUFp5zL5puSWi0UVRj6U1v3uJi23d7p40VgEh1SmR0lx
JjHNgHjqzU+gUeMoipx33kYvFRteCEH36JsCAwEAAQJBAMKsuYi4l0Qn3qBXedA/
xxxxxxxxxxxxxxxxD50ZEH2frkuuDlE/IVjIvbd78Rdgdwpt+hcrRh0NPLohTins
dgECIQDr2CcsldtKiBOQxxxcVtM4IZtpqlXV2U8zFgf6/LnPmwIhAOiHgwUpMSty
xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
OUbS4KlR8bN0WwIhAJVYU8JAzp/E2j6pAGJhGbpKUnb9gZpwyXvdxFa8OWQBAiEA
41EhQq90+1NqwpMIBoqYvQvqYPTW/y9KEJDbkyXK2r8=
-----END RSA PRIVATE KEY-----
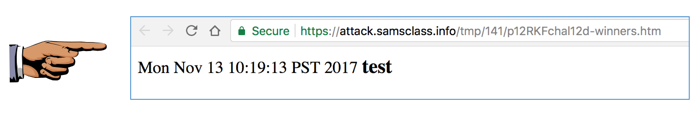
Save a whole-desktop image with the filename "YOUR NAME Proj 12d", replacing "YOUR NAME" with your real name.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!