https://www.cryptool.org/en/ct2-downloads
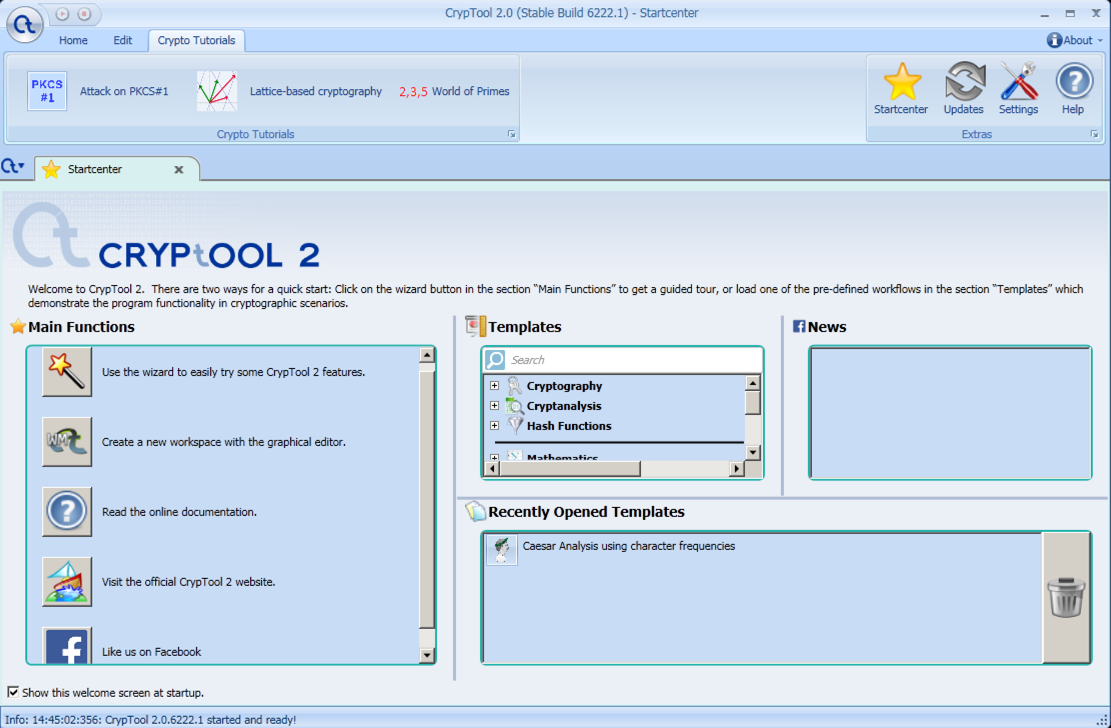
On the left side, in the "Main Functions" section, click the Wand icon labelled "Use the wizard...", as shown below.
In the "TASK SELECTION" screen, on the left side, click Cryptanalysis. Then click Next.
In the "AGE SELECTION" screen, click "Modern Encryption" and click Next.
In the "TYPE SELECTION" screen, click "Symmetric Encryption" and click Next.
In the "ALGORITHM SELECTION" screen, select AES, and click Next.
In the next screen, accept the default selection of "Ciphertext-Only" and click Next.
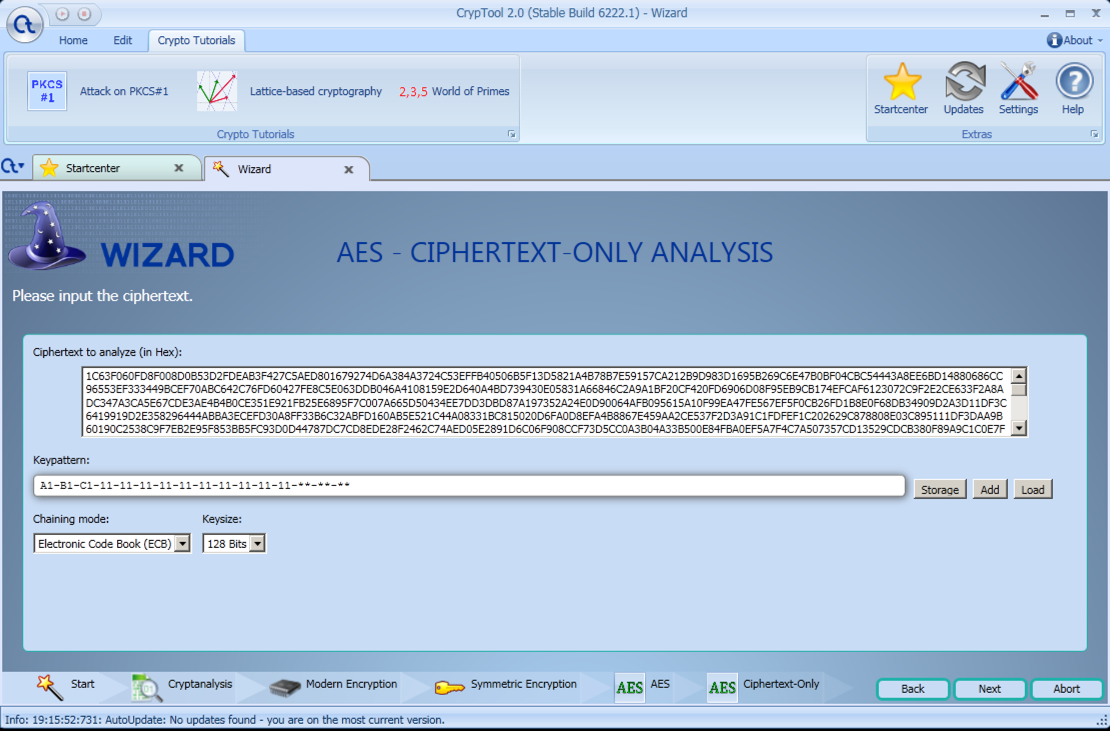
In the "AES - CIPHERTEXT-ONLY ANALYSIS" screen, some example ciphertext appears, as shown below.
Notice the "Keypattern"--most of the key is known. Only the portion shown as "*" is unknown. This is the weakness that makes the attack possible. There are six asterisks, and each is a hexadecimal character, so there are only 16^6 = 16.8 million possible keys.
Notice that there is no setting for Language. This attack will use simple entropy--encrypted text is more chaotic than text in a language.
Also note the "Chaining Mode" option. The simplest is ECB--the others are more secure. For now, accept the default of ECB.
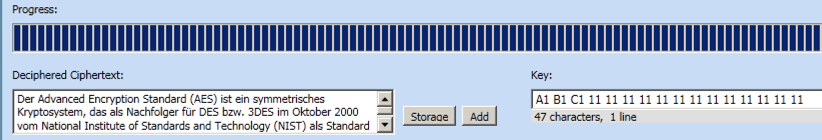
Click Next. The progress screen is very small and difficult to see, but I was able to expand it as shown below, and it is obvious how it works. It's testing about 500,000 keys per second, and the attack requires about 33 seconds, so it's testing all 16.8 million possible keys. It chooses the result with the lowest entropy, which is shown in the "Value" column. The correct cleartext has entropy 4.2, and all the others have entropy of 5.2 or larger.
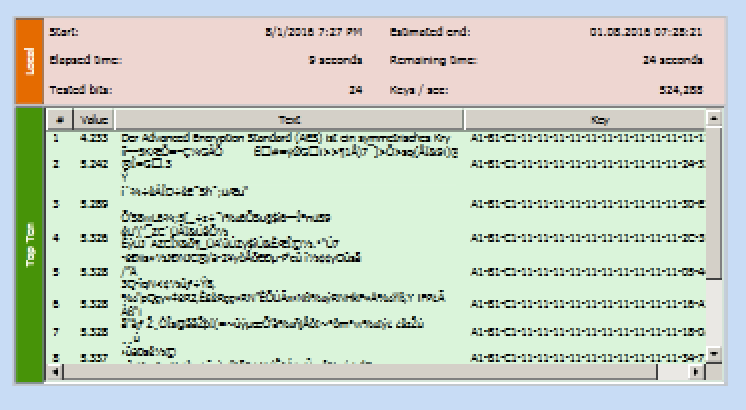
It works, finding the cleartext, which is in German, as shown below.
EF490B9CD4F92E3CA945DF24DAAFF8A0FF7FA784A50C57E296CE69C62C4F7FE6B4D1D2D144D98C8D871D4615BF2533C76DD518FAC35729D45E772B6365E5A457AE92E33922E1A5FE9E1DC5F1AEDEDD7EB32B1630AF4C5F10A453EEFF1E9C9CE0A3F9FCD0DDB2A36C016B70B76E2CFE5B4A0377AA11521F7032E308FC4954D9BB3495CE8E07F4800B7AA53B8BCD6291C7167B52F0F5F921C78CDCAB9606666543D4DEF1917CC389C20FB3E1099F0FBBCA
E34ADF1C54B33E19518AFABDB36183C37665EE1A234093395325612E97CB773D3975E69D3665C0F65E30BF2D5B9CCFC8B96290954EF6EF3B813A3E50AB637DCFD55D25D775D6360904740BCCEC800C8D5CE03ABAAE18F7D47A6C1AB32C134E3A80DDC77EB2ED1B4FADB2585020B832399B228703B1654BA09645E8ACC7A6B9DC87DAAE6AB576763D62A9EB7585AAFA16
The flag is the first four words of the decrypted text.
Hint
Don't assume it's in ECB mode.Note added Sep 28, 2020: The latest version of CrypTool, 8853.1, is broken and cannot solve this. Use CrypTool 2.0 (Stable Build 6222.1).zip instead.