https://gchq.github.io/CyberChef/
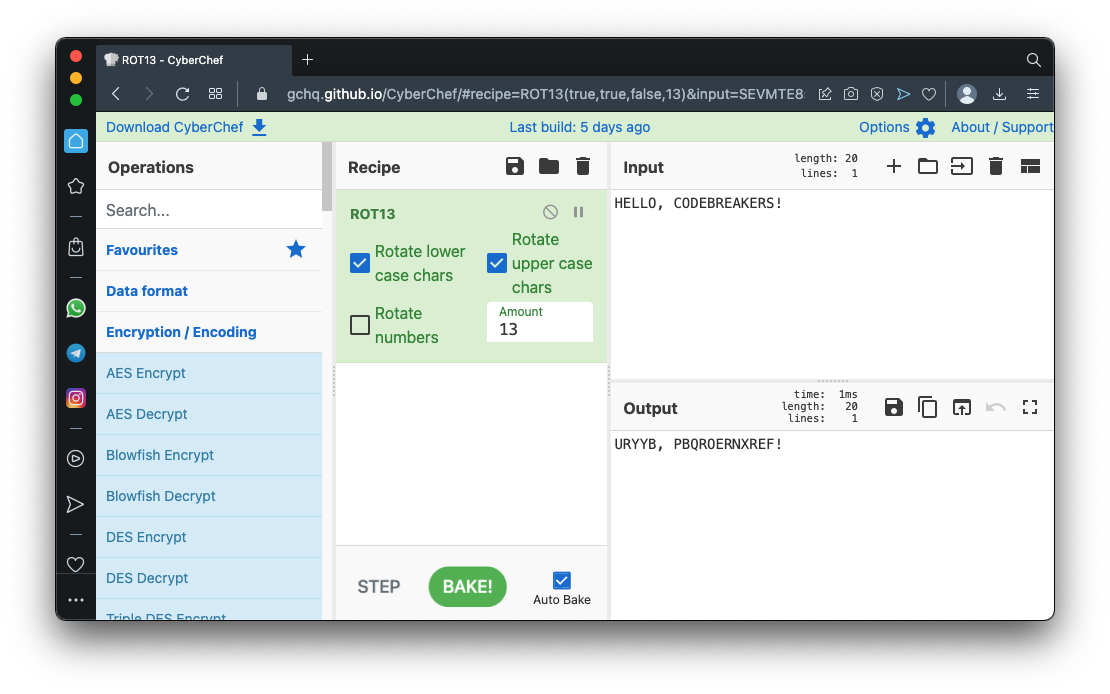
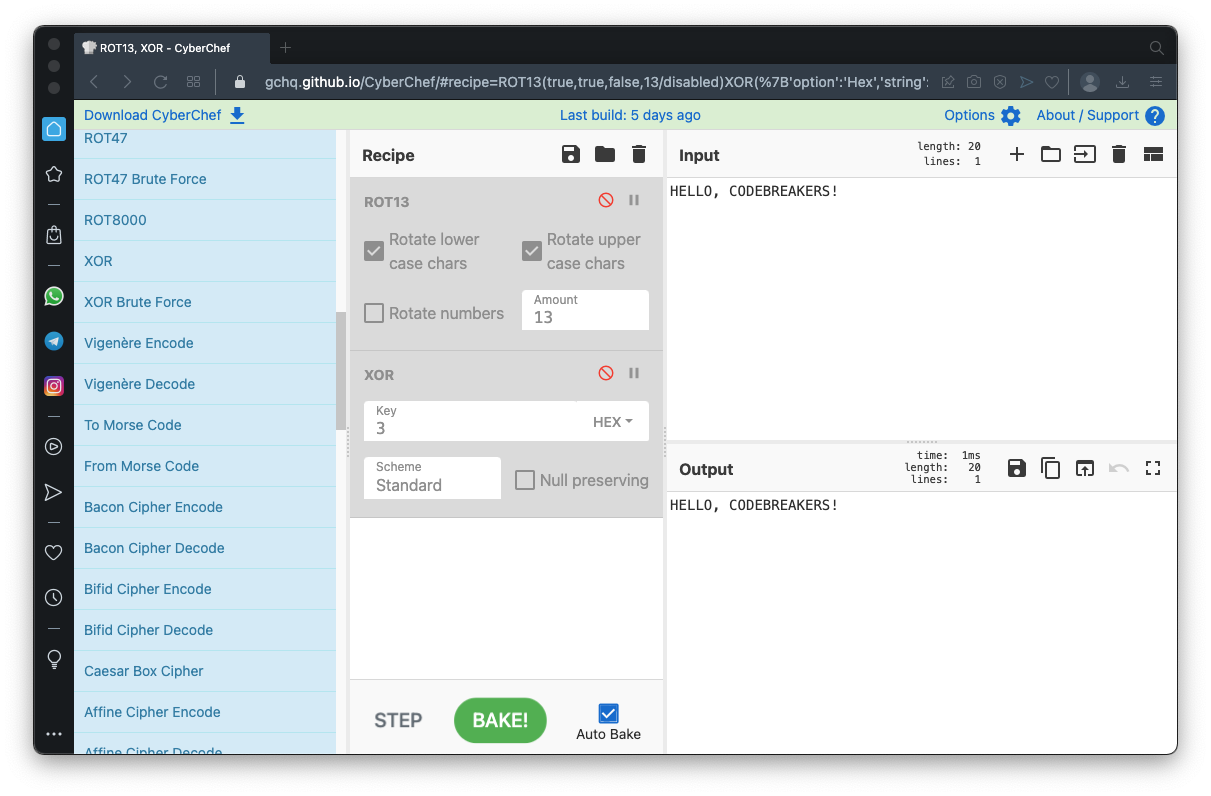
On the top right, in the Input box, enter:HELLO, CODEBREAKERS!In the left pane, in the Operations list, expand "Encryption/Encoding".
Find the ROT13 operation and drag it to the Recipe pane.
The encrypted message appears in the lower right Output pane, beginning with URYYB, as shown below.
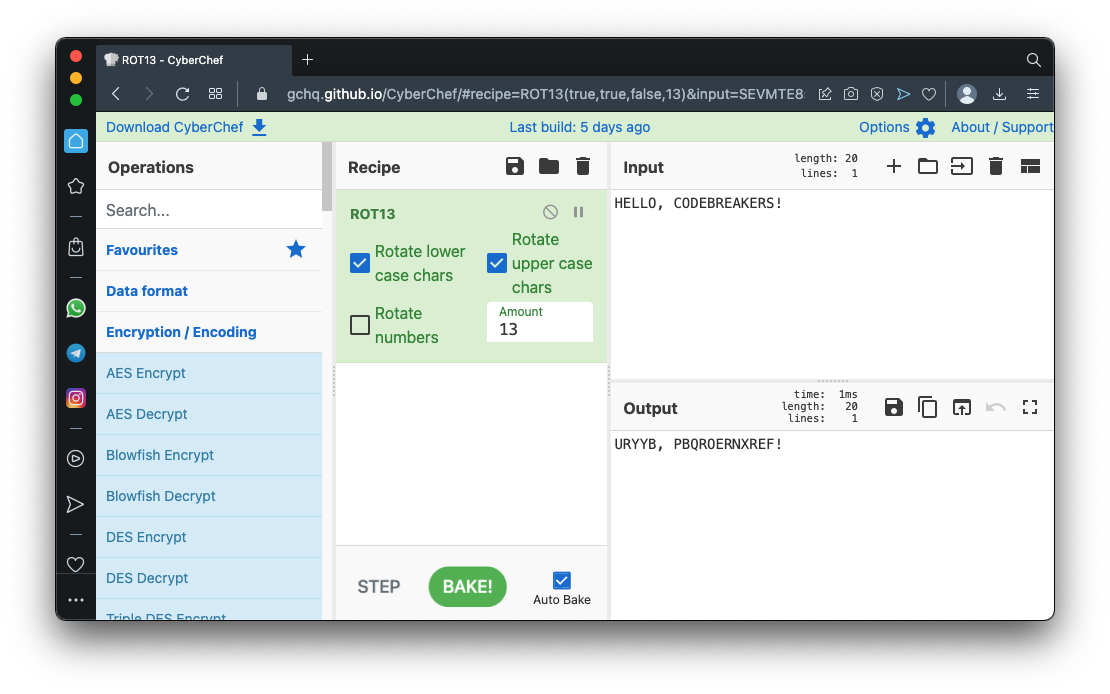
Drag the XOR operation from the Operations pane to the Recipe pane, below ROT13.
In the XOR operation, enter a Key of 3, outlined in red in the image below.
Now the Input goes through two operations: ROT13 and XOR, to produce the Output, as shown below.
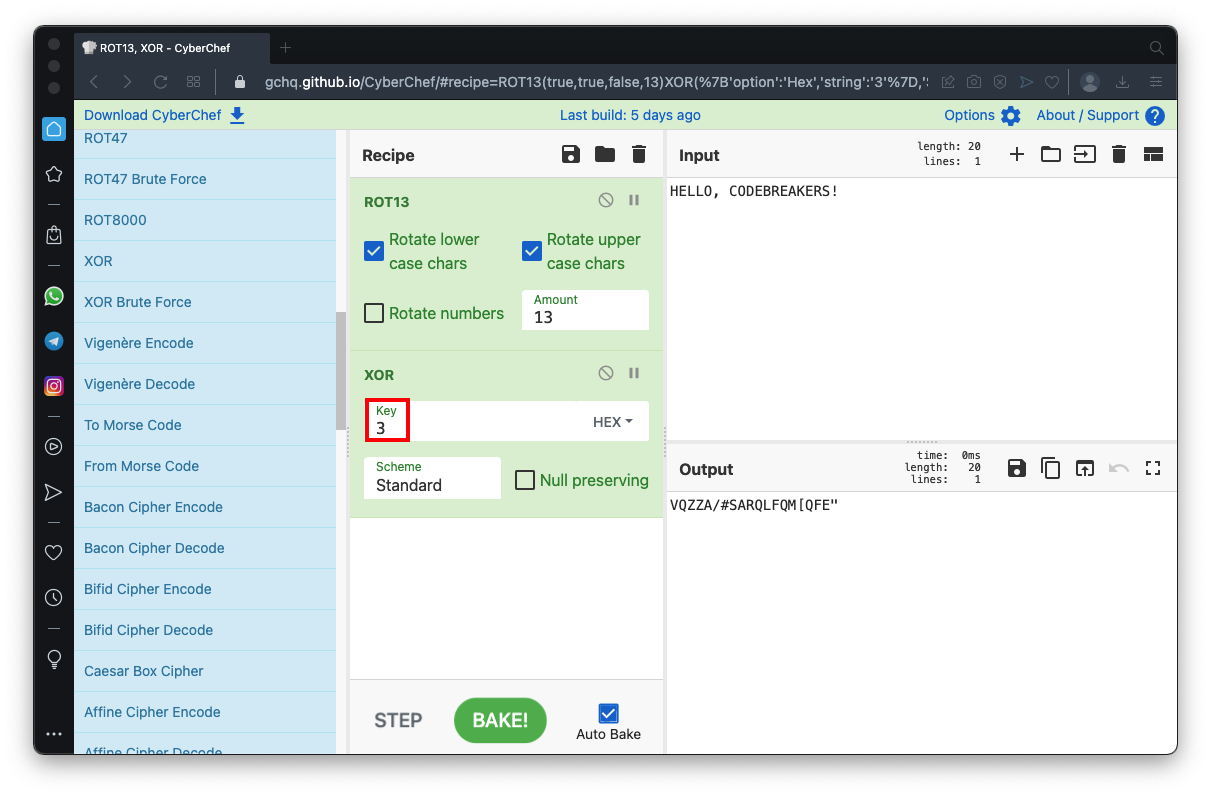
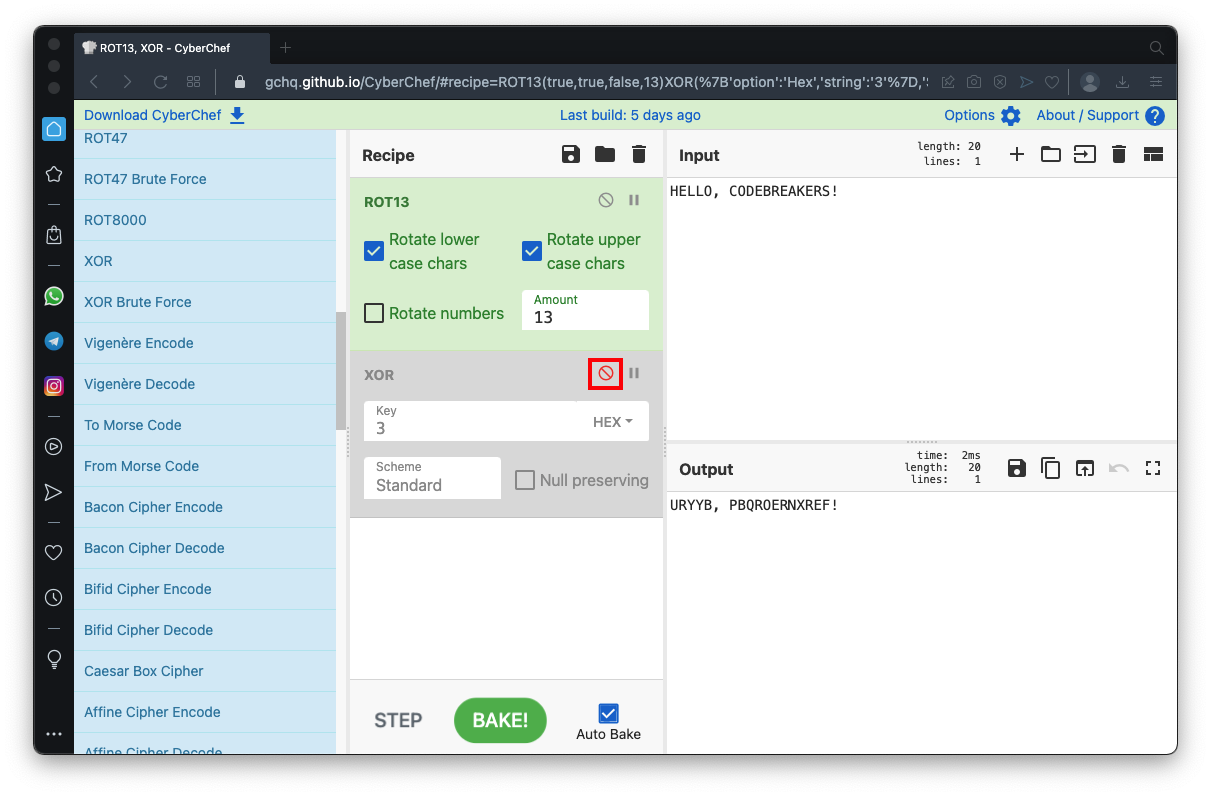
Now only the ROT13 operation is active, so the Output once again begins with URYYB, as shown below.
Disable the ROT13 operation. Now the output is the same as the input, as shown below.
Enable the XOR operation.
C 107.1 XOR (5 pts)
The flag is covered by a green rectangle in the image below.
URYYB, PBQROERNXREF!Use the "ROT13 Brute Force" operation.
This tries all possible shift amounts.
As shown below, an Amount of 13 finds the original plaintext.
You can find it by reading through the list of possible outputs and finding the one that makes sense.
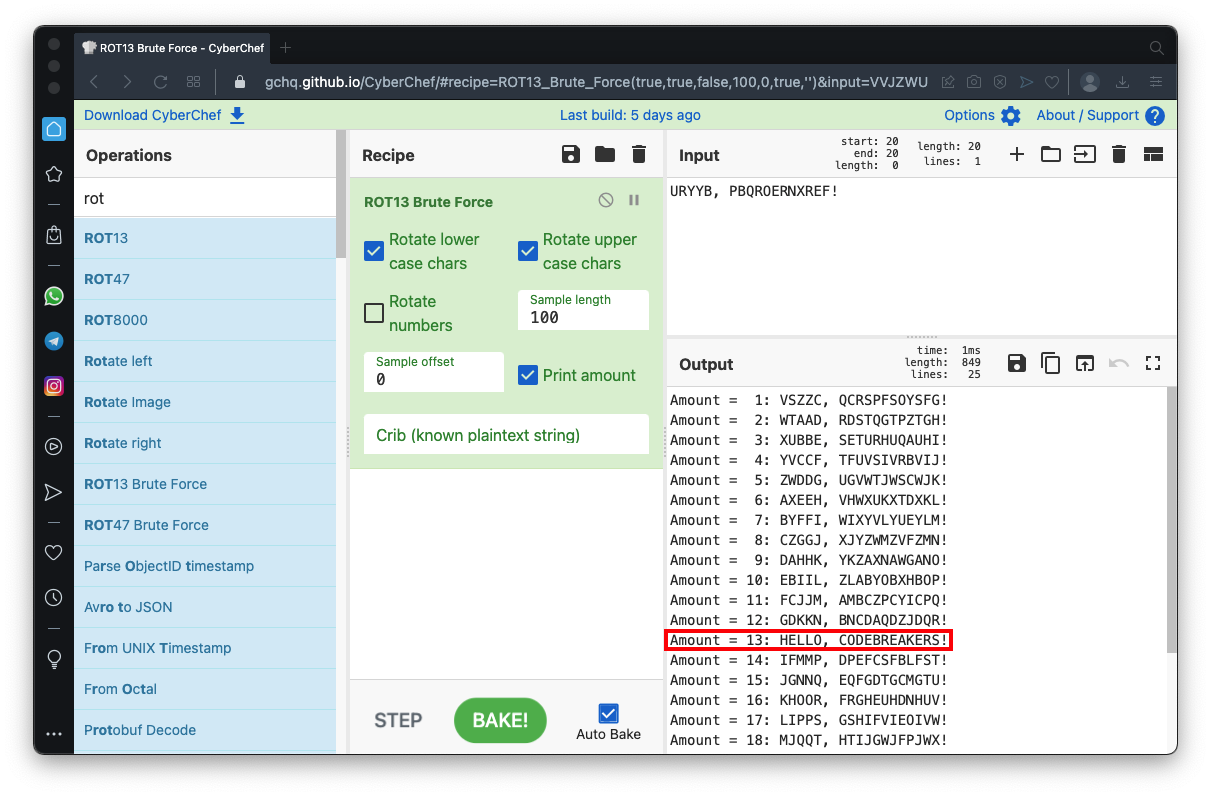
If you know a portion of the plaintext, you can eliminate outputs that don't contain it.
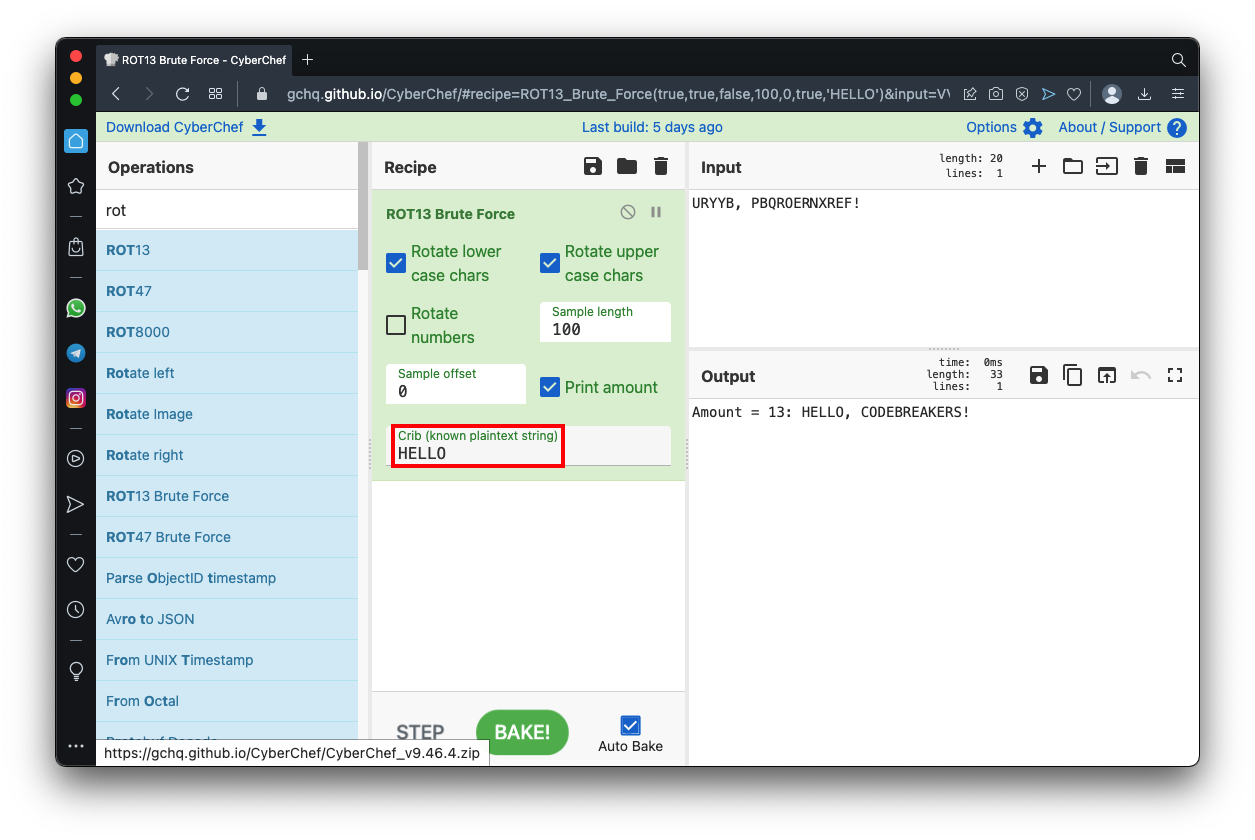
In the "ROT13 Brute Force" operation, enter a Crib of HELLO, outlined in red in the image below.
Now only the correct Amount is shown in the Output pane.
C 107.2 ROT (5 pts)
Decrypt this with the "ROT13 Brute Force" operation to find the flag.Lzw xdsy ak NWJQ WSKQ
C 107.3 XOR (5 pts)
Decrypt this to find the flag.A}p5sytr5|f5FA\YY5PTFL
C 107.4 XOR with 2-Byte Key (10 pts)
Decrypt this to find the flag.Kmz%yi~b?ll%QJK%KJP%WDMA
Posted 9-14-22 by Sam Bowne
C 107.5 XOR and Base64 (10 pts)
This plaintext is encrypted with single-byte XOR and then with Base64.Decrypt this to find the flag.
2+fqr+nj7uiv5vyv3cre2sbdytyv2MDdxA==