
A computer with VirtualBox
The Manager is responsible for ensuring that all the tasks are completed correctly and on time, by delegating tasks to the other team members, monitoring their progress, and reallocating resources as neeed.
The Writer records the important actions performed by the team and prepares a Report for the client.
The Researcher searches the Web to find out information about the target and any other information the team needs.
The Technicians scan and attack the target, keeping notes of what they have done.
p7firelin.ova 1.41 GB (1,401,362,432 bytes)
Import it into VirtualBox.
This virtual appliance contains one Linux server as shown below.
You can SSH into it at the "NAT IP" with the username student and a password of student.

http://ad.samsclass.info/botlist.htm
Note these facts, as shown below.

The purpose of this project is to deny the attackers control of your server, while continuing to provide service to real users, using only a firewall.
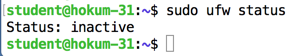
On your server, via SSH, execute this command to see your firewall status.
sudo ufw status
Let's block all incoming traffic except these three ports:
sudo ufw allow 22
sudo ufw allow 3000
sudo ufw allow 3001
sudo ufw enable
The firewall becomes active, as shown below.

Refresh the scoring webpage. After a minute or so, it should change, as shown below.
Ports 80 and 81 are now filtered, but your box is still PWNED, because you have not filtered outgoing traffic.

sudo ufw reset
sudo ufw deny out to any
sudo ufw enable
It also lets SYNs come in on unused ports, such as port 81, which will allow bind shells.


Posted 10-5-18