Ub18-RvB-L1 Clone.ova (1.g GB)
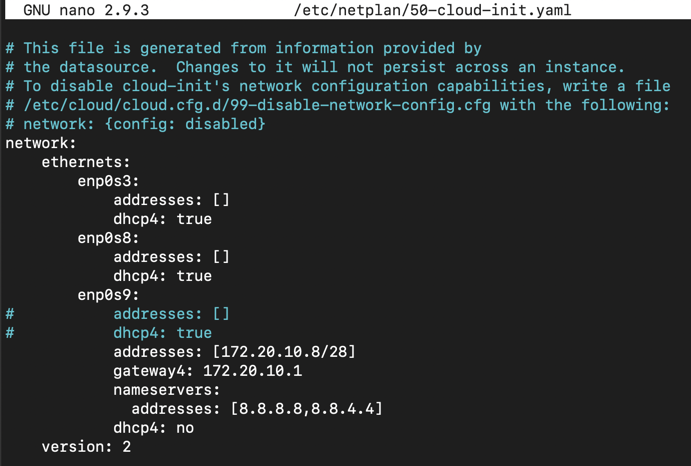
sudo nano /etc/netplan/50-cloud-init.yaml
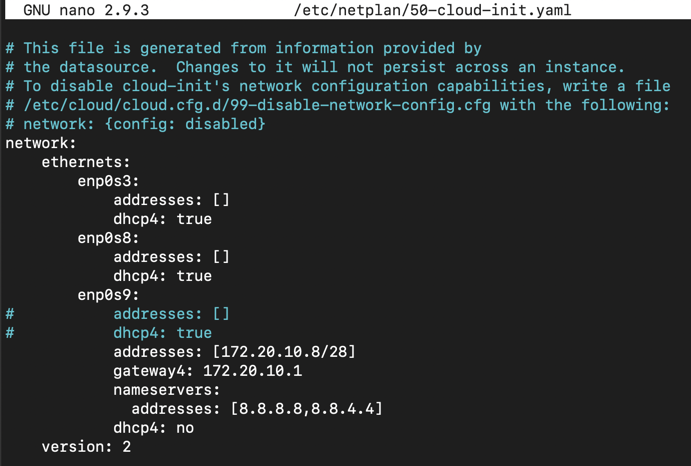
In a Terminal, execute this command:
sudo netplan --debug apply
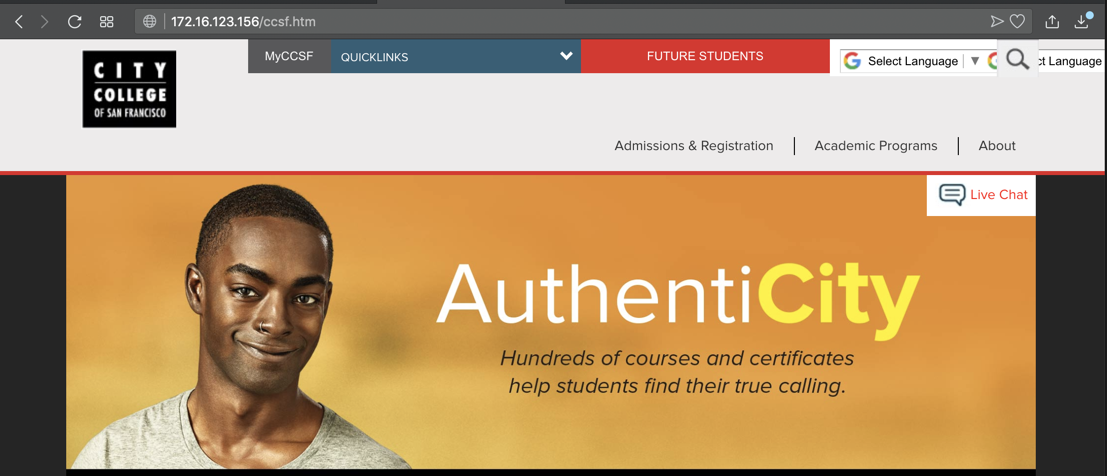
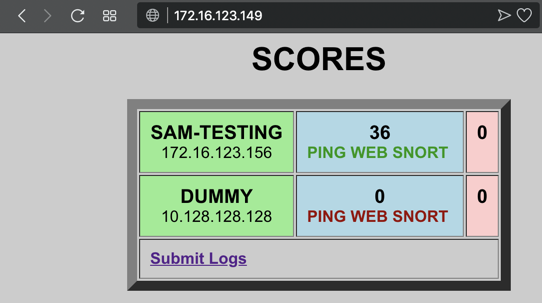
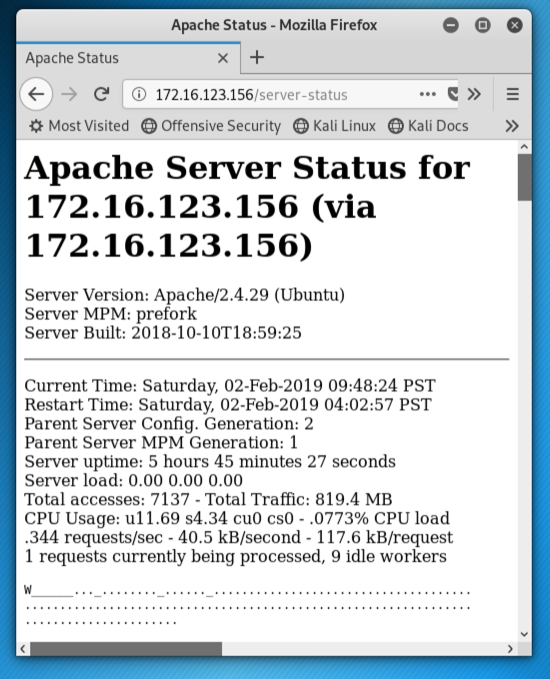
You should see the CCSf web page, as shown below.
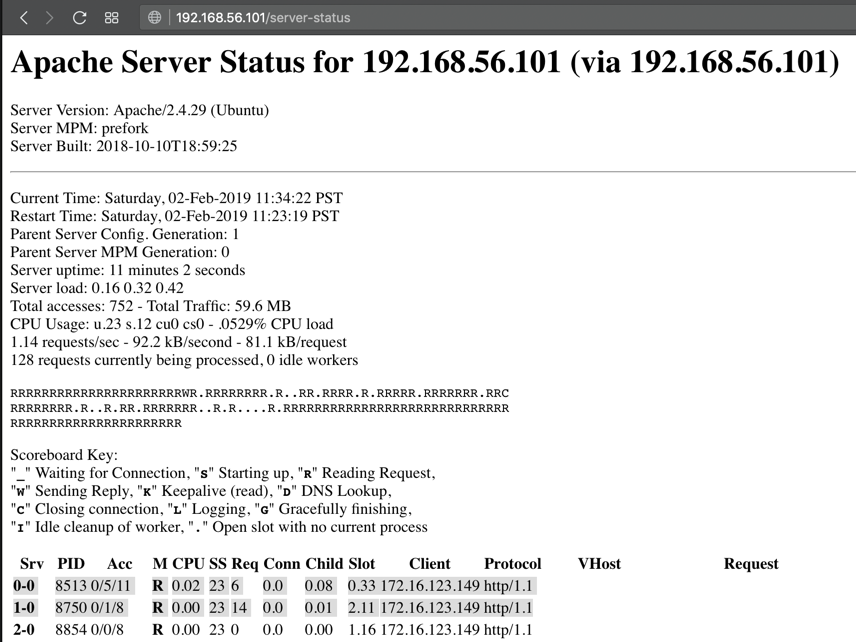
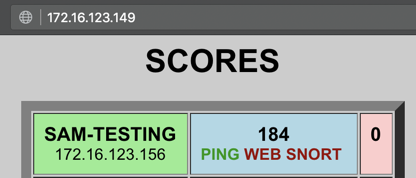
You should start getting points on the scoreboard, as shown below.
sudo mv /etc/snort/snort.debian.conf .
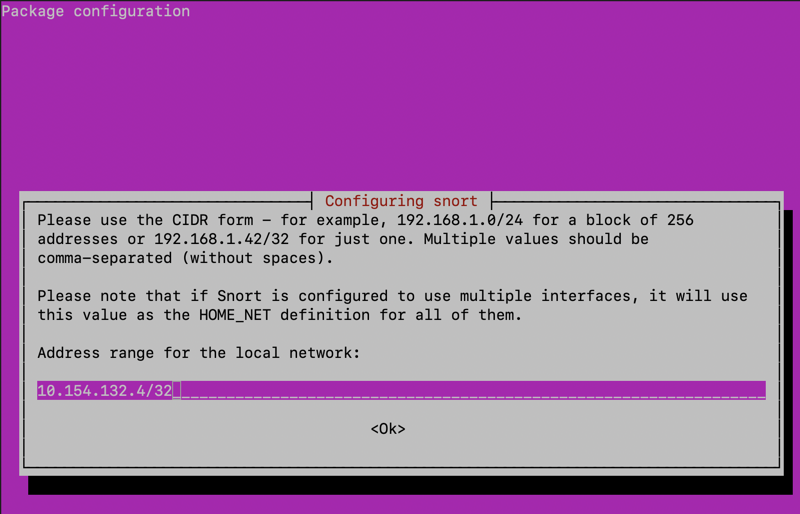
sudo dpkg-reconfigure snort
In a Terminal, execute this command:
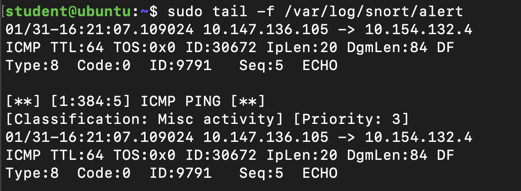
tail -f /var/log/snort/alert
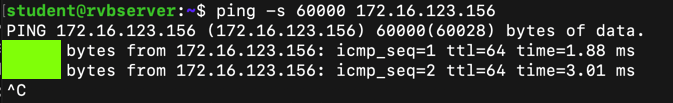
ping -s 60000 172.16.123.156
On the scoreboard, click the "Submit Logs link.
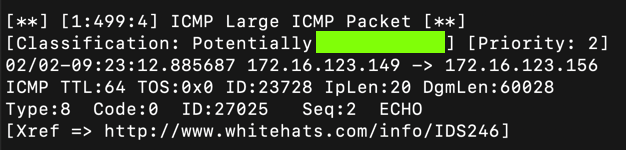
Paste in the reply size, which is covered by a green box in the image above, to collect your points.
On the scoreboard, click the "Submit Logs link.
Paste in the classification text, which is covered by a green box in the image below, to collect your points.
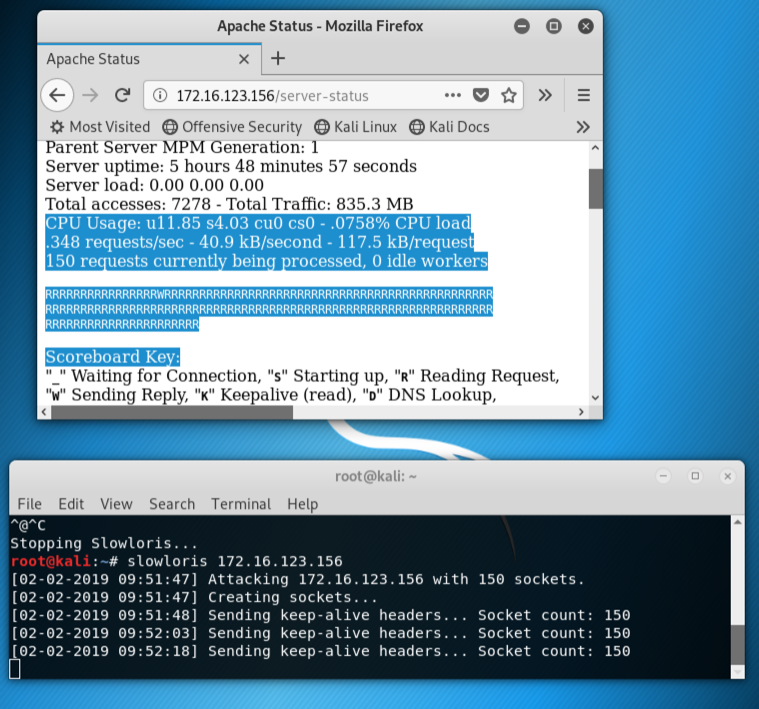
On your Kali attacker, execute these commands to start a Slowloris attack.
apt install python3-pip
pip3 install slowloris
slowloris example.com
When you see all the dots gone from the grid, replaced by 'R" or other letters, as shown below, copy the text on the page. Submit that text on the "Submit Logs" page to claim your points.
execute these commands to activate Apache's "reqtimeout" module, which resists the Slowloris attack.
sudo systemctl stop apache2
sudo a2enmod reqtimeout
sudo systemctl start apache2
Copy the first 2 lines of the connection log, as highlighted in the image below. Submit that text on the "Submit Logs" page to claim your points.