Project 1: Command Injection (15 pts.)
What You Need
- A computer of any sort with an Internet connection.
Purpose
To understand and exploit the simplest type of vulnerability:
command injection.
Introduction to the Bash Command Line
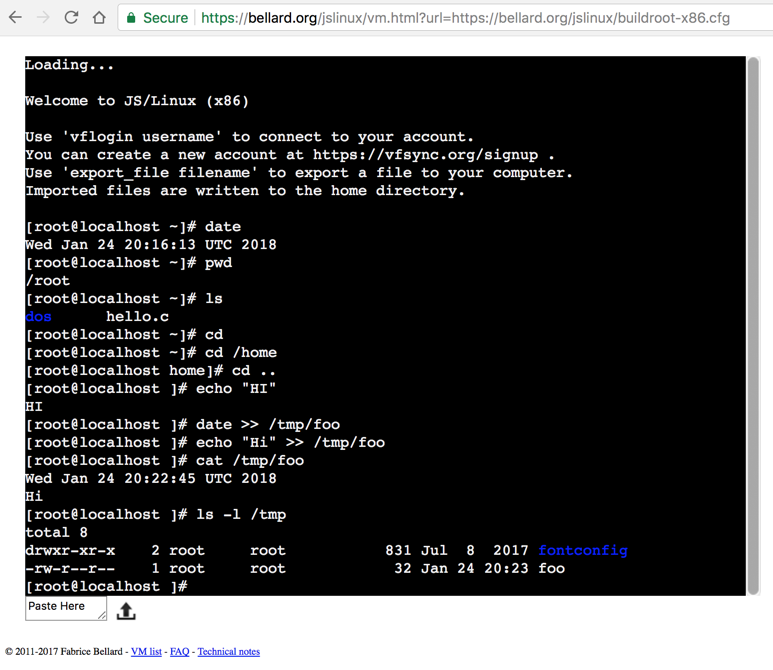
In a Web browser, go to:
https://bellard.org/jslinux/vm.html?url=https://bellard.org/jslinux/buildroot-x86.cfg
Afer a few seconds, a Linux terminal opens, as shown below. Use it to
practice these commands:
| Command | Explanation |
|---|
| date | Print out the date and time |
| ls | List files and directories in the current working directory |
| pwd | Print the current working directory |
| cd | Move to your home directory |
| cd /home | Move to the /home directory |
| cd .. | Move to parent of the current working directory |
| echo "Hi" | Print the the text "Hi" |
| date >> /tmp/foo | Print the date into the file /tmp/foo |
| echo "Hi" >> /tmp/foo | Print the text "Hi" into the file /tmp/foo |
| cat /tmp/foo | Print the contents of the file /tmp/foo |
| ls -l /tmp | List, in long form, the files and folders of the directory /tmp |
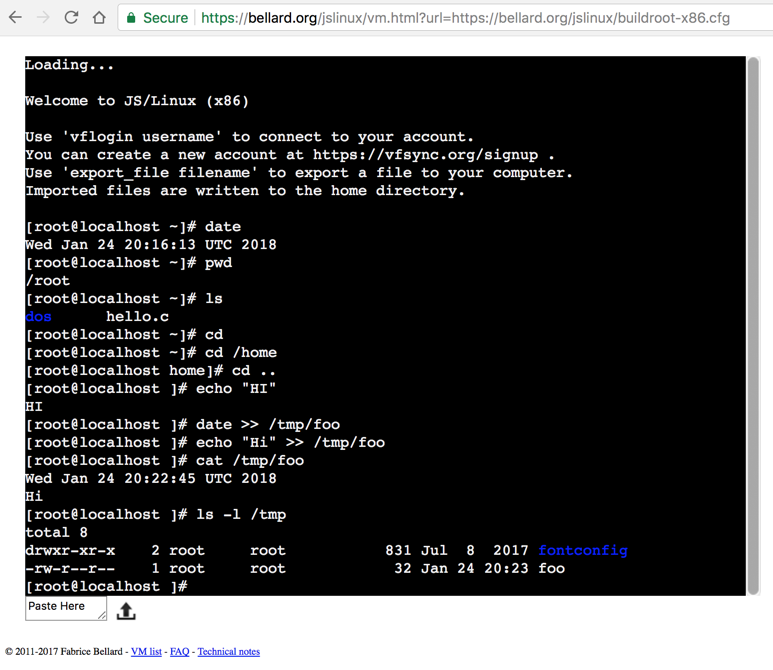
If you want more information about Bash, try
this Unix tutorial.
Task A: Create a File (5 pts.)
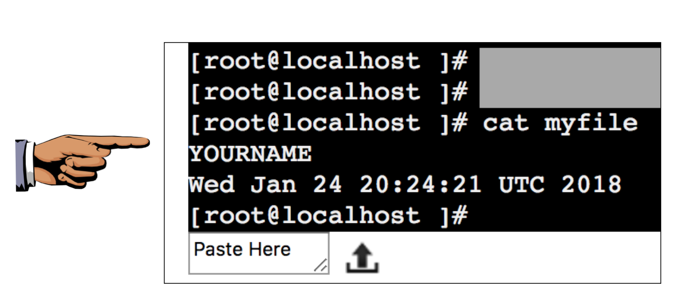
Create a file in any directory, with any name,
containing
your name and the current date and time, like this:
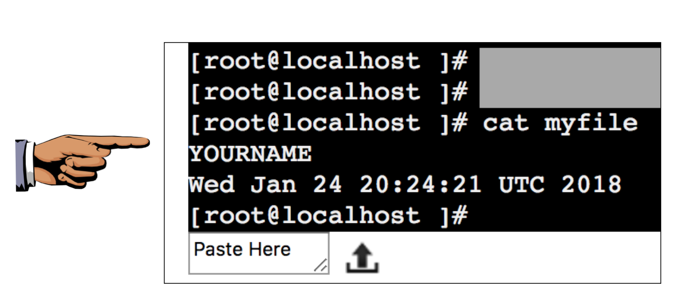
You can use any Linux or Unix system you like--you don't need to
use that online shell.
Capturing a Screen Image
Capture a
WHOLE-DESKTOP image showing the output of the cat
command, as shown above.
To capture a screen image:
- On a PC: press Shift+PrntScrn,
open Paint, and press Ctrl+V.
- On a Mac, press Shift+Ctrl+3. The captured
image appears on your desktop.
Save the image as
"Proj 1a from YOUR NAME".
Make sure your image has these required
items:
- The cat command printing the contents of your file
- YOUR NAME in the title bar
- The current date and time
- Your image must show your WHOLE DESKTOP -- not just one window.
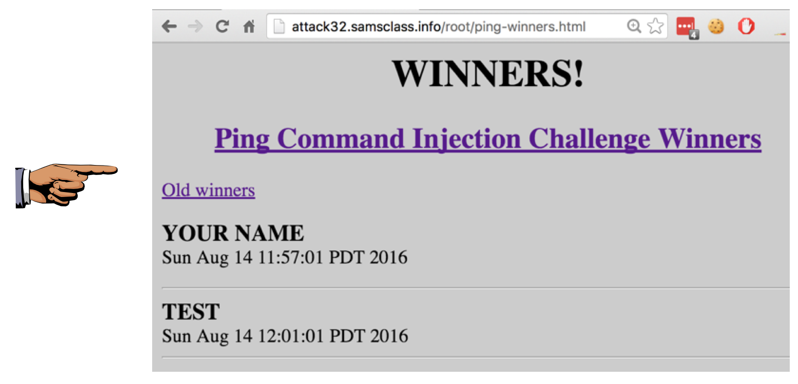
Task B: Exploit the Ping Form (10 pts.)
In a browser, go to
http://attack3214.samsclass.info/ping.htm
That form is intended to perform pings, but it is vulnerable
and can be exploited to do other things. Get your name on the
Winners board,
as shown below.
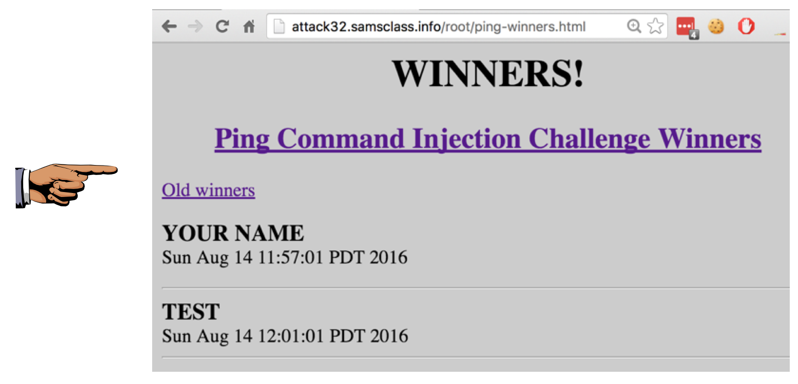
Capturing a Screen Image
Capture a
WHOLE-DESKTOP image showing
your name on the
Winners board.
Save the image as
"Proj 1b from YOUR NAME".
Turning in Your Project
Send the images to cnit.129s@gmail.com with a subject of
"Proj 1 from YOUR NAME". Send a Cc:
to yourself.
Posted 8-14-16 12:11 pm
URL updated 1-17-18 5 pm
Switched to JS Unix 1-24-18
Font changed 1-14-19