Click the "Intercept is on" button so it changes to "Intercept is off".
Click the "Open Browser" button.
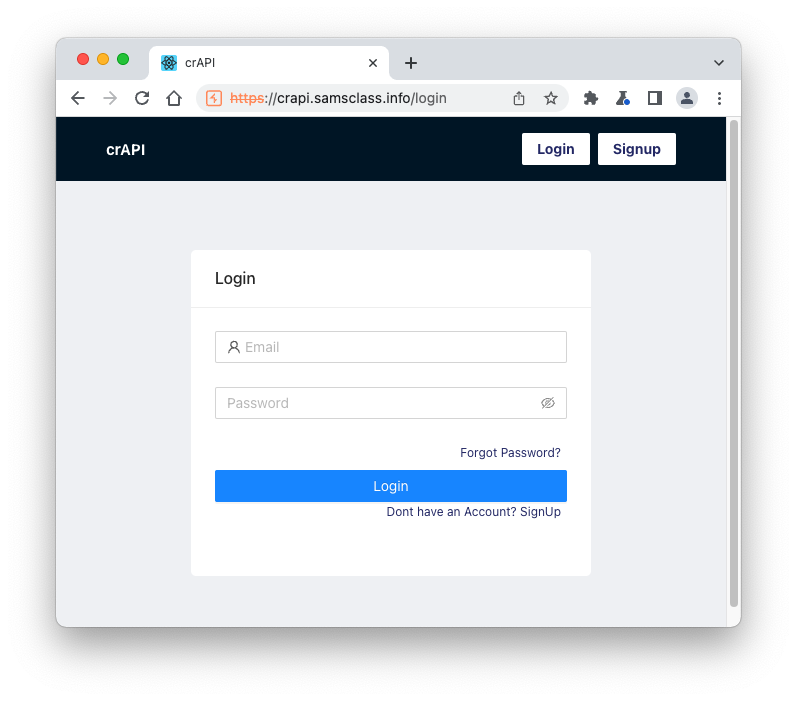
In Burp's browser, go to
https://crAPI.samsclass.info The crAPI login page opens, as shown below.
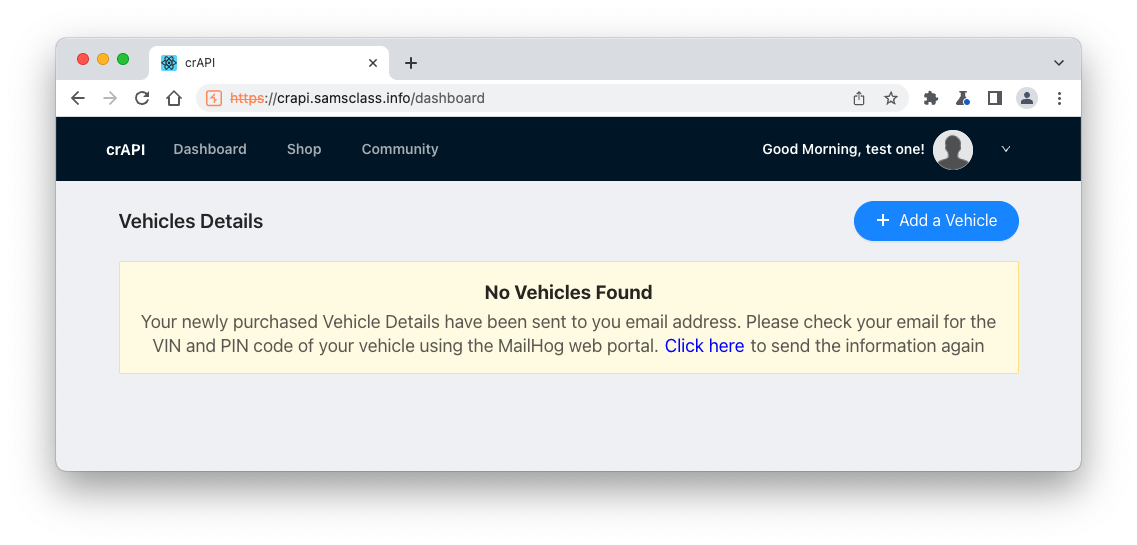
You see the "Vehicles Details" page, as shown below.
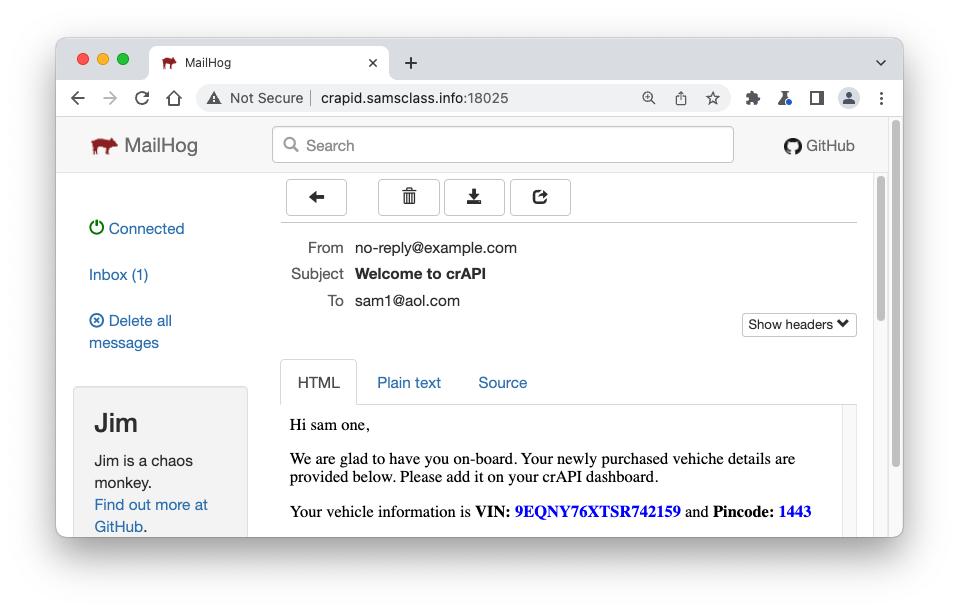
http://crAPId.samsclass.info:18025 Open the email to your address with a subject of "Welcome to crAPI".
Find your VIN and Pincode, as shown below.
Enter the VIN and Pincode from your email, and click "Verify Vehicle Details".
Click OK.
The Vehicle Details page opens, as shown below.
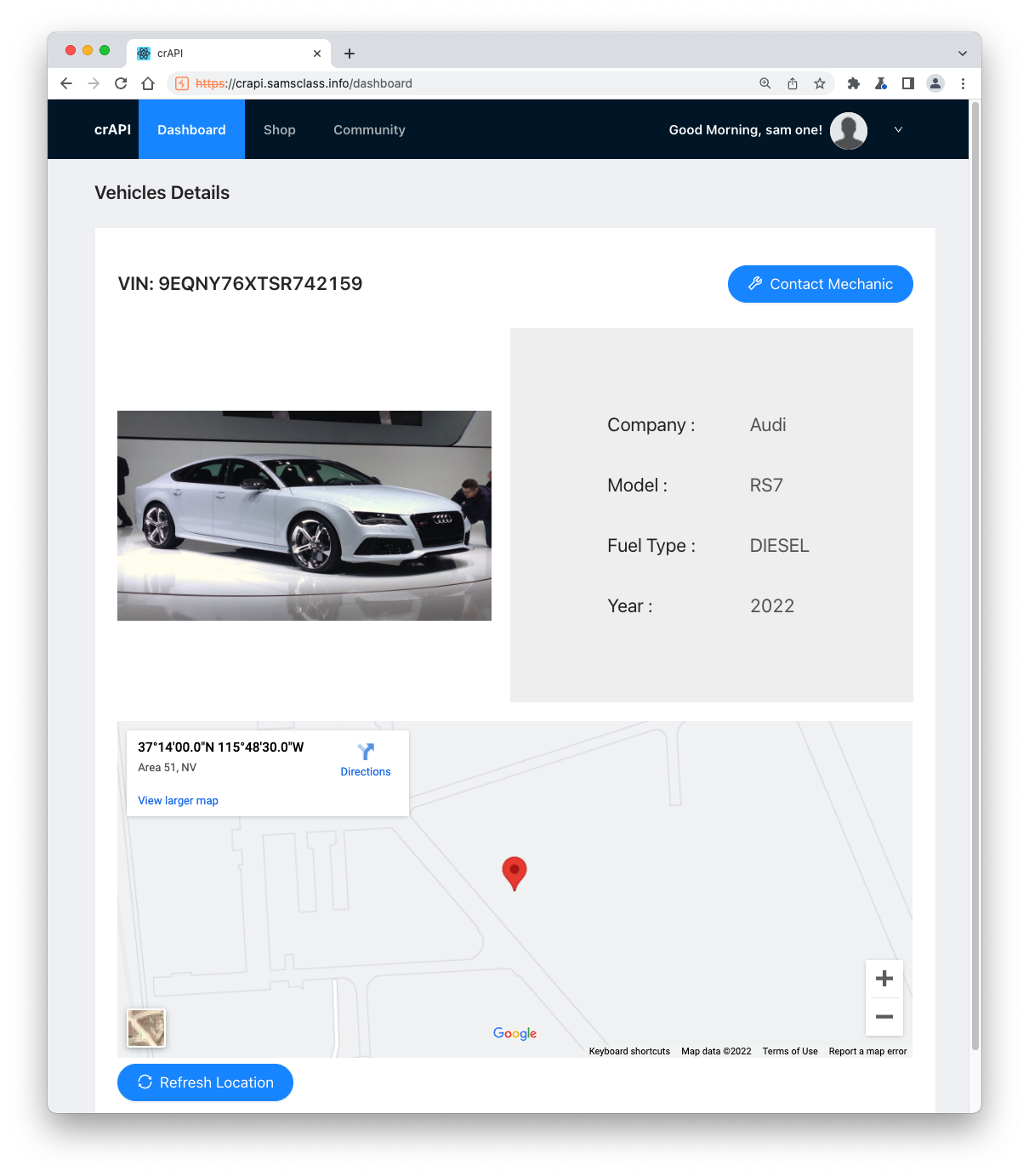
The Google Map updates with the location of your vehicle.
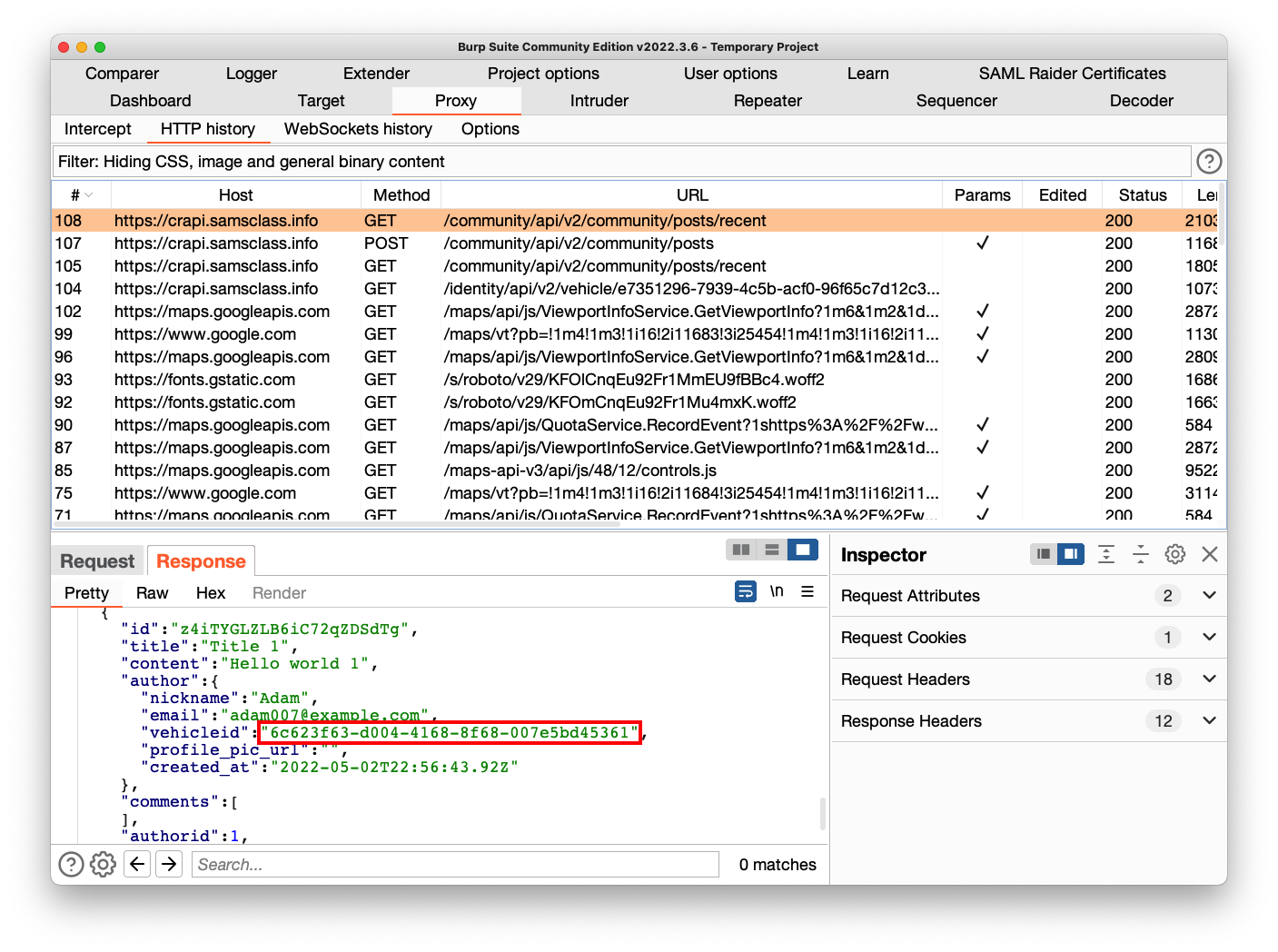
In Burp, on the HTTP History tab, find this request:
GET /identity/api/v2/vehicle/e7351296-7939-4c5b-acf0-96f65c7d12c3/location
The long number is the vehicle GUID and yours will be different from the example above.The location is sensitive data--you should not be allowed to learn the location of a different owner's vehicle.
Right-click this request and click "Send to Repeater".
A box pops up saying "Post Created". Click OK.
GET /community/api/v2/community/posts/recent
On the Response tab, scroll down and find another person's vehicleid, outlined in red in the image below.
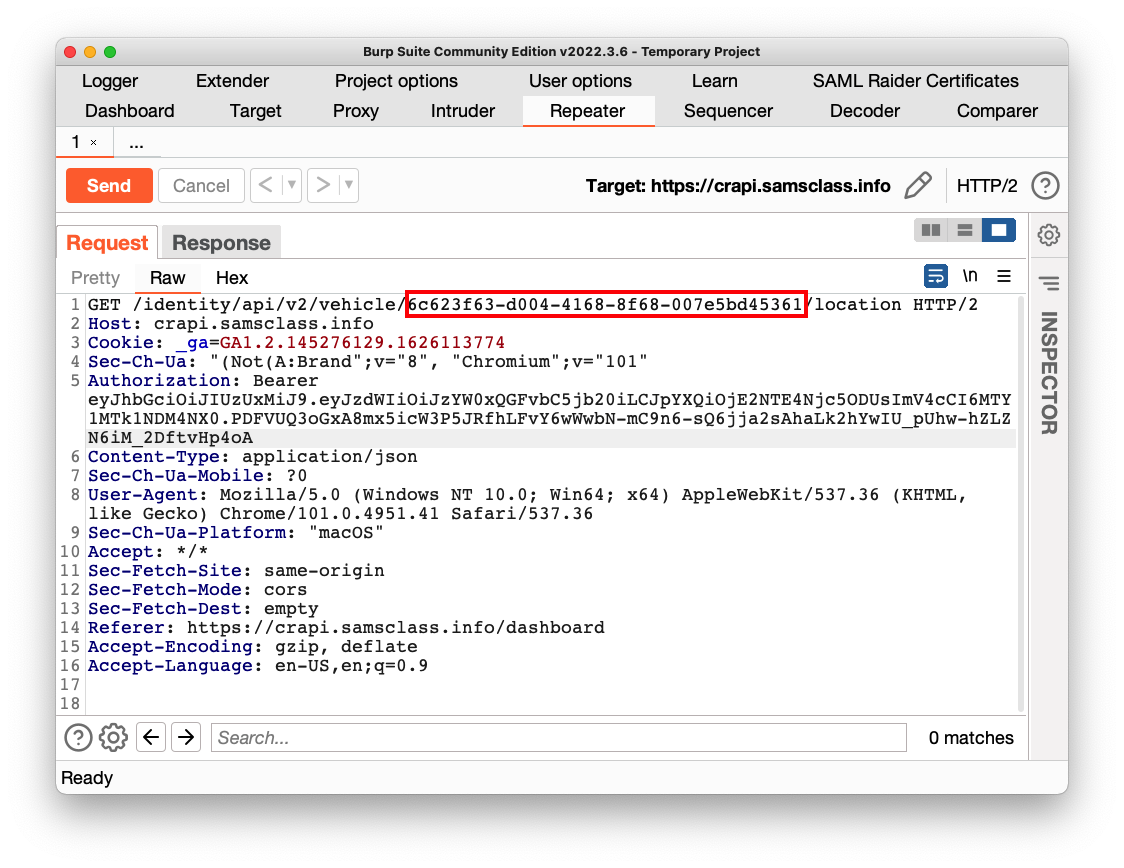
Send the request. As shown below, the location of the other person's vehicle is returned, with their name. This is a Broken Object-Level Authorization (BOLA) vulnerability!
Flag AP 104.1: Message (10 pts)
Send the request. The flag is covered by a green rectangle in the image below.
Posted 5-6-22
Flag changed 7-18-23