Rate My Professors iOS App Stores Passwords Insecurely
Background
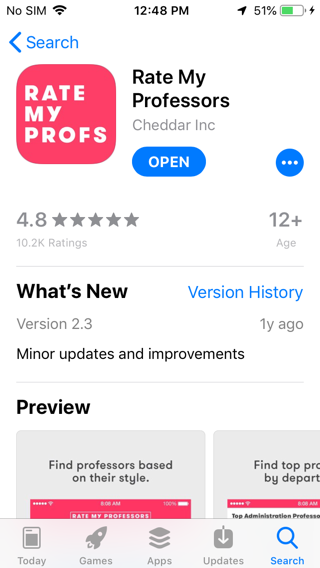
The
Rate My Professors iOS app has a
security problem--it stores
passwords without
encryption on
the phone.
I tested this app:
Insecure Storage
Storing passwords without encryption
is unacceptable for any app, according to the
OWASP https://github.com/OWASP/owasp-masvs,
specifically, these items:
-
2.1 MSTG-STORAGE-1: System credential storage facilities need to be used to store sensitive data, such as PII, user credentials or cryptographic keys.
- 2.5 MSTG‑STORAGE‑5: The keyboard cache is disabled on text inputs that process sensitive data.
- 2.10 MSTG‑STORAGE‑10: The app does not hold sensitive data in memory longer than necessary, and memory is cleared explicitly after use.
The
Mobile Top 10 2016-M4-Insecure Authentication
explanation says:
"...mobile applications should never store a user’s password on the device; Ideally, mobile applications should utilize a device-specific authentication token..."
In 2018, the German chat platform Knuddels.de
was fined €20,000 for storing
user passwords in plain text.
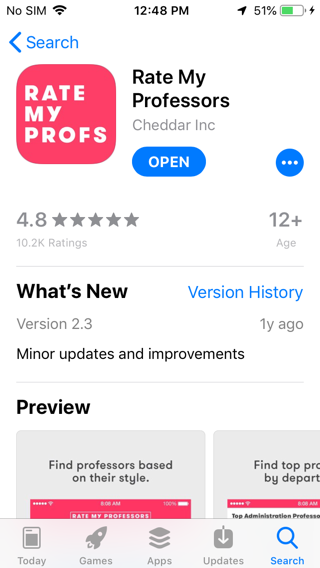
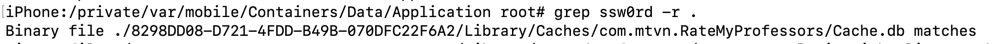
Testing Method for Local Storage
I found this flaw using OWASP's
recommended dynamic testing
procedure:
The following steps can be used to determine how the application stores data locally on a jailbroken iOS device:
- Trigger the functionality that stores potentially sensitive data.
- Connect to the iOS device and navigate to its Bundle directory (this applies to iOS versions 8.0 and above): /var/mobile/Containers/Data/Application/$APP_ID/
- Execute grep with the data that you've stored, for example: grep -iRn "USERID".
- If the sensitive data is stored in plaintext, the app fails this test.
I used a jailbroken iPhone running iOS
12.4.4 with no passcode.
I created an account. As shown below, the
password was stored on the iPhone.
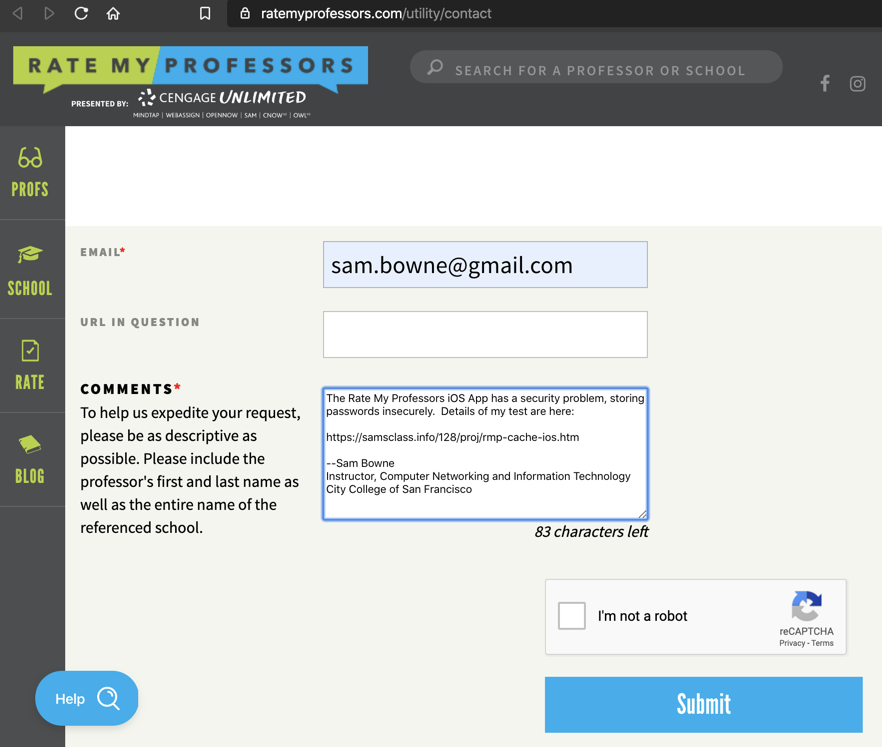
Notification
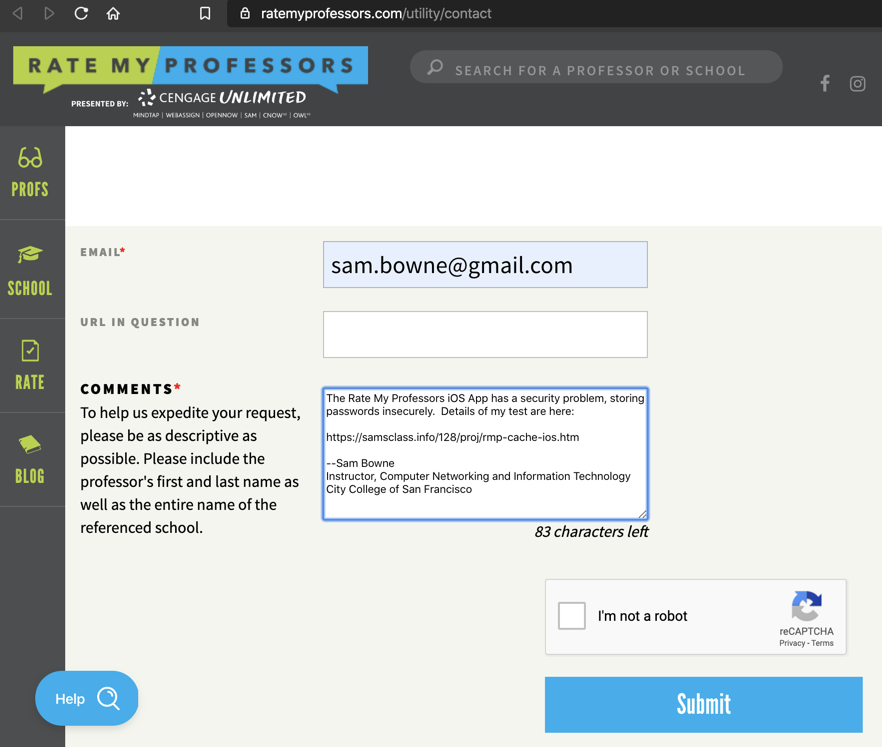
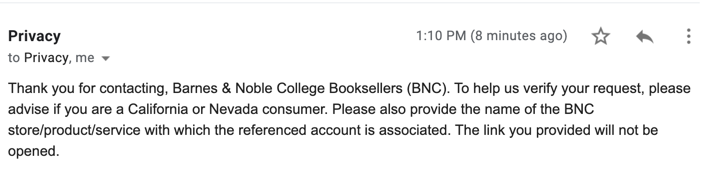
I sent this message on 1-12-2020:
I got this reply on 1-13-2020.
Clearly they don't care and won't be
fixing it.
Posted 1-12-2020 by Sam Bowne
Updated with vendor response and more OWASP items added 1-13-2020