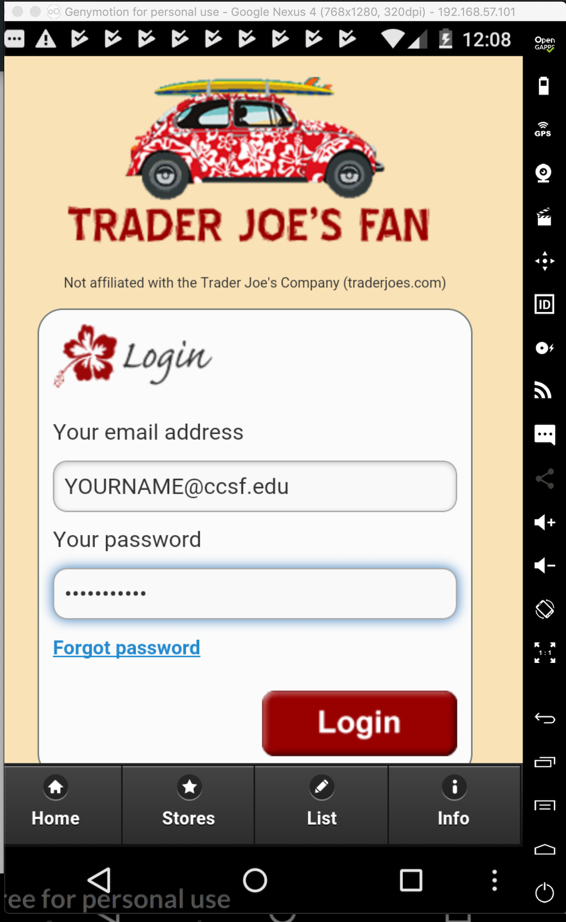
Trader Joe's Fan
Equity Pandit
(Use "Create Account" page to see password)
Stock Screener: Stock Analyst
(Uses SHA-1 hash of password)
Drink Mixer FREE drink recipes
Recipes by Ingredients

Diet Plan
So please use one of these apps instead. They all used plaintext network transmission on Feb 10, 2019, but eventually they may be fixed or removed.
Trader Joe's Fan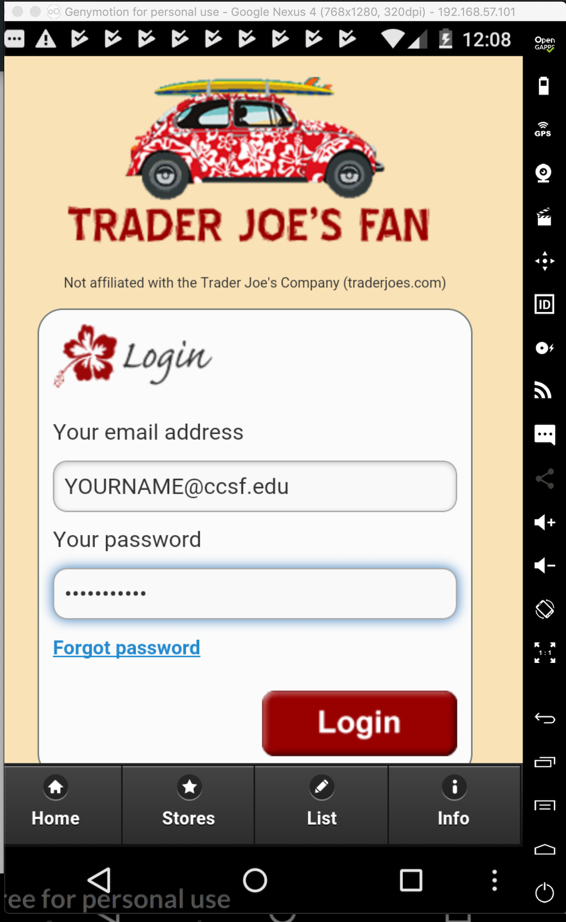 |
Equity Pandit(Use "Create Account" page to see password)
|
Stock Screener: Stock Analyst(Uses SHA-1 hash of password)
|
Drink Mixer FREE drink recipes |
Recipes by Ingredients |
Diet Plan |
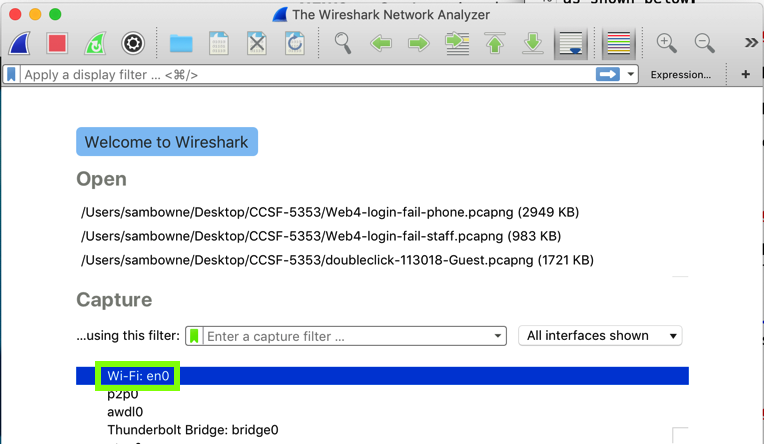
In the main Wireshark window, double-click the network interface that is being used to reach the Internet. On my system, it is "Wi-Fi: en0", outlined in green in the image below.
Wirehark starts displaying packets. At the top, in the Filter bar, enter this display filter:
http
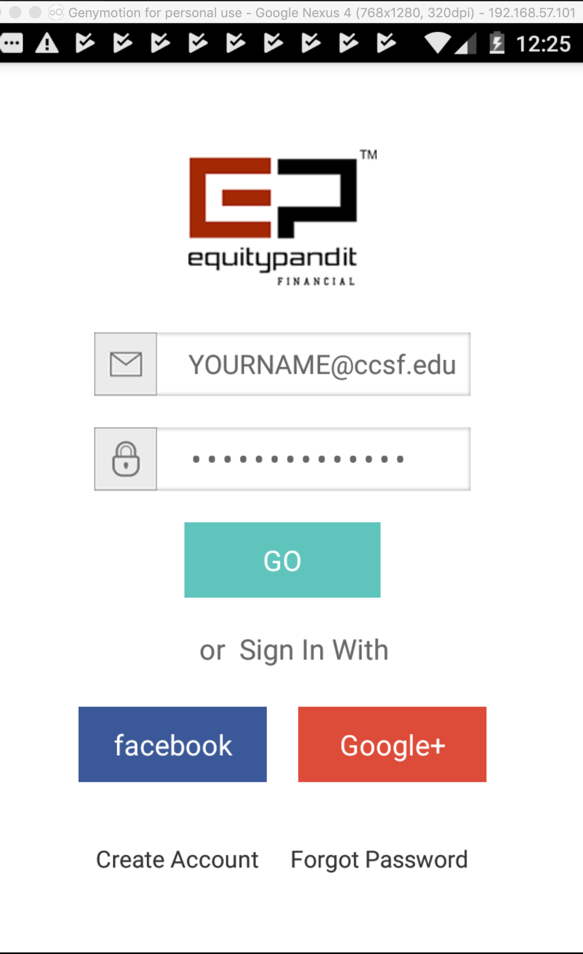
On your Android device, in the vulnerable app, submit these login credentials, as shown below
Wireshark shows a captured POST request, as shown below.
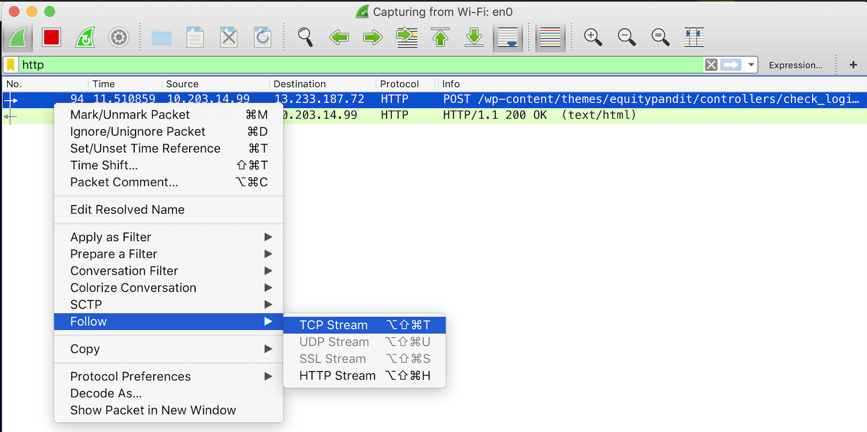
In the top pane of Wireshark, right-click the POST request, and click Follow, "TCP Stream", as shown above.
Troubleshooting
If you don't see any packets, try these fixes:
- Click the red square button to stop the capture
- From the menu, click Capture, Options
- Choose a different network adapter
- If the "Link-layer header" is set to "802.11...", scroll to the right and uncheck the monitor box
The request appears, containing YOUR NAME, as shown below.
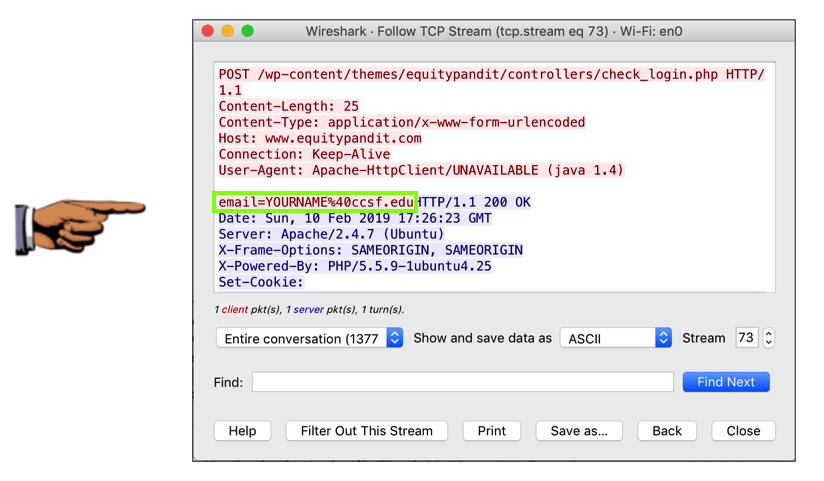
Save a full-desktop image. On a Mac, press Shift+Commmand+3. On a PC, press Shift+PrntScrn and paste into Paint.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
Save the image with the filename "YOUR NAME Proj 7x", replacing "YOUR NAME" with your real name.