Proj 12x: Android Password Cracking with Nox (40 pts)
What You Need for This Project
- A Nox Android emulator, with Kali and adb connected to it,
which you prepared in previous projects. The host system can
be either two PCs or one Mac.
Purpose
To recover a PIN from an Android 5 device.
Don't use a more recent
Android version or it won't work.
Start Nox
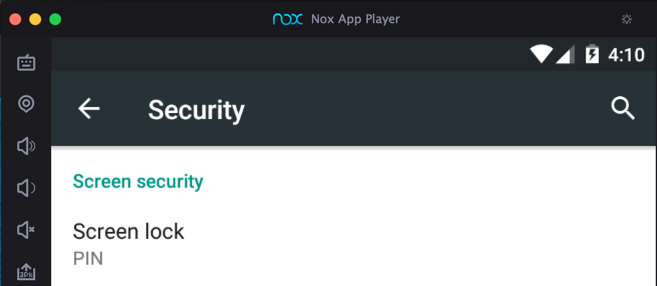
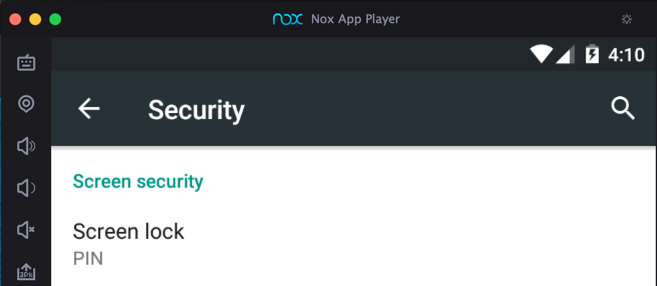
Start Nox. If there is no PIN,
Open Settings, Security,
"Screen lock" and assign a PIN
of 1234
as shown below.
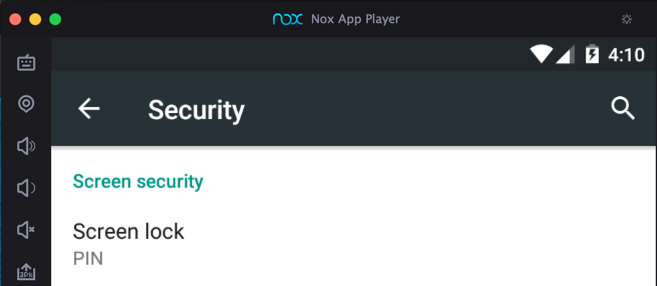
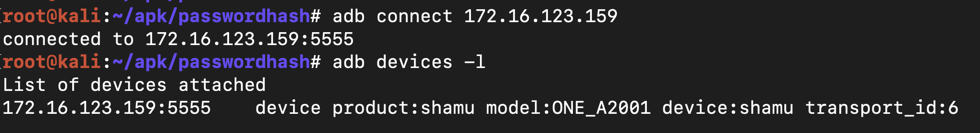
Connecting with ADB
As you did in previous projects,
connect to your Nox emulator from Kali,
as shown below.
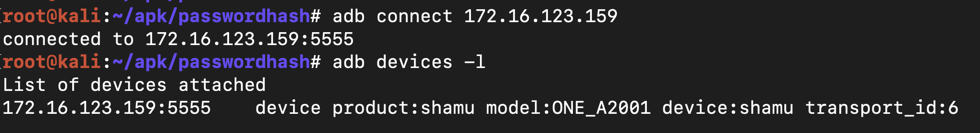
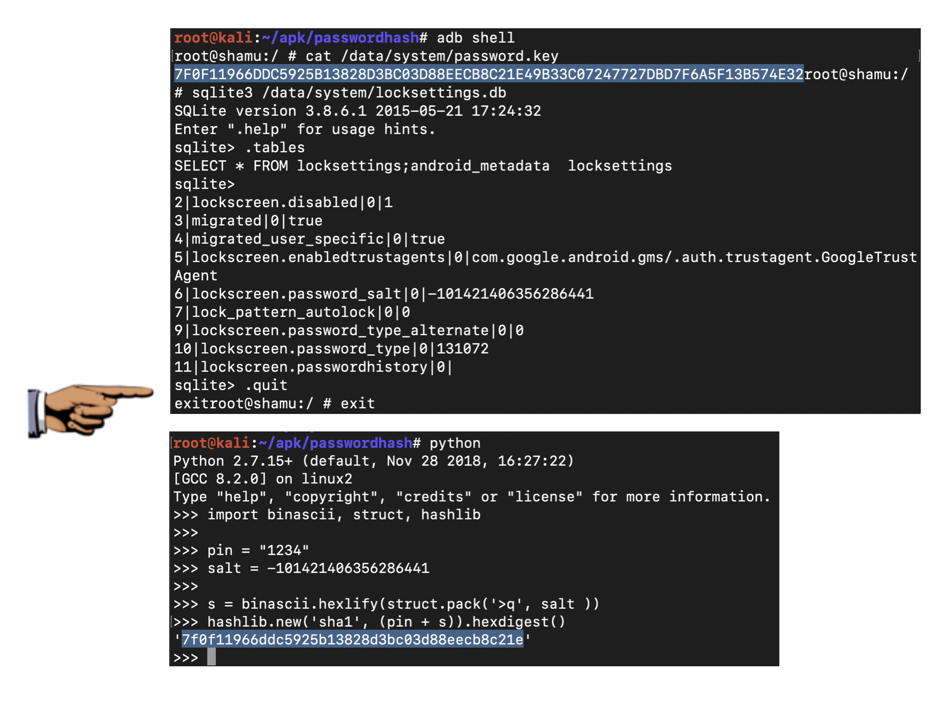
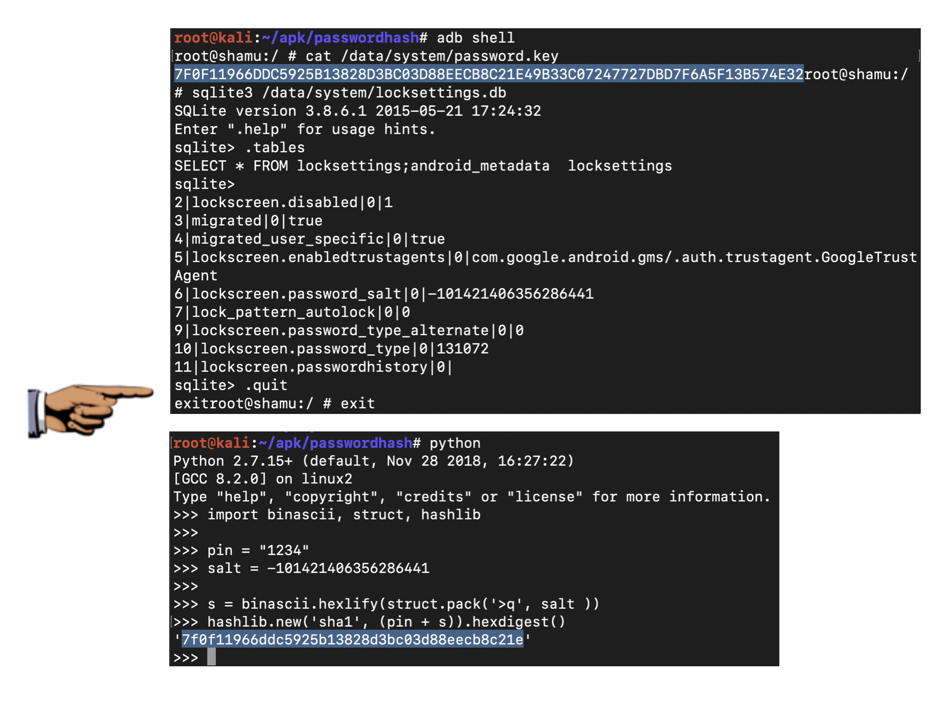
Gathering the Password Hash and Salt
On Kali, in a Terminal, execute these commands,
one by one:
adb shell
cat /data/system/password.key
sqlite3 /data/system/locksettings.db
.tables
SELECT * FROM locksettings;
.quit
exit
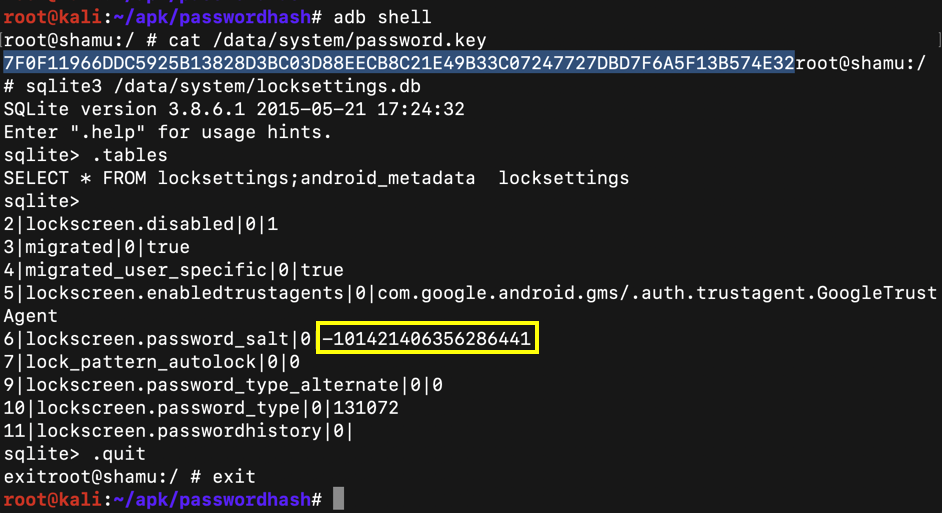
You now have the password hash and salt.
In the image below, the password hash is
highlighted, and the salt is outlined in
yellow.
Find the two values on your system. You will
need them below.
Calculating the Hash with Python
On Kali,
open a second Terminal window and
execute these commands,
replacing the PIN and salt
values with the correct values on your system:
python
import binascii, struct, hashlib
pin = "1234"
salt = -101421406356286441
s = binascii.hexlify(struct.pack('>q', salt ))
hashlib.new('sha1', (pin + s)).hexdigest()
The SHA-1 hash you calculated in Python
should match the first portion of the
Android hash you found on the phone,
as shown below.
12x.1: Saving a Screen Image (10 pts)
Put both Terminal windows on your desktop,
as shown above.
Make sure
you can see the required features listed below:
- A long password hash, printed out from the password.key file, as shown in the top image above.
- A SHA-1 hash, computed in Python, as shown in the bottom image above.
- The beginnings of the two hashes should match, with one using lowercase letters and the other using uppercase letters
- The hash value must not be identical to the one I calculated, shown in the image above
Save a full-desktop image. On a Mac, press Shift+Commmand+3. On a PC, press Shift+PrntScrn and paste into Paint.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
Save the image with the filename "YOUR NAME Proj 12x", replacing "YOUR NAME" with your real name.
12x.2: Challenge: 4-Digit PIN (15 pts)
I chose a different four-digit PIN. Find it from this
information:
root@shamu:/ # cat /data/system/password.key
7DBD9B2D8DD734510D2894AAA9FF6B0AD8DC69BFEFD0B48F82FCC55018F151C5310FCFFB
sqlite> SELECT * FROM locksettings;
6|lockscreen.password_salt|0|-101421406356286441
Include the PIN in the body of your email
when turning this project in.
12x.3: Challenge: 8-Digit PIN (15 pts)
I chose an eight-digit PIN. Find it from this
information:
root@shamu:/ # cat /data/system/password.key
59A364BD3954E5FF1DD524BD948CCC9F6C7EAD949A08F1A0C5983969D481672AA2EC344C
sqlite> SELECT * FROM locksettings;
6|lockscreen.password_salt|0|-101421406356286441
Include the PIN in the body of your email
when turning this project in.
Turning in your Project
Email the image and the recovered PINs to
to cnit.128sam@gmail.com with the subject line:
Proj 12x from YOUR NAME
Posted 3-20-19