So I cannot deny that Lumosity is a very smart company! Perhaps they are so smart because they use their own products.
This practice may be illegal in the USA. Two American companies were sanctioned by the FTC in 2014 for making this same error:
FTC Final Orders with Fandango and Credit Karma Provide Guidance on Mobile App Security
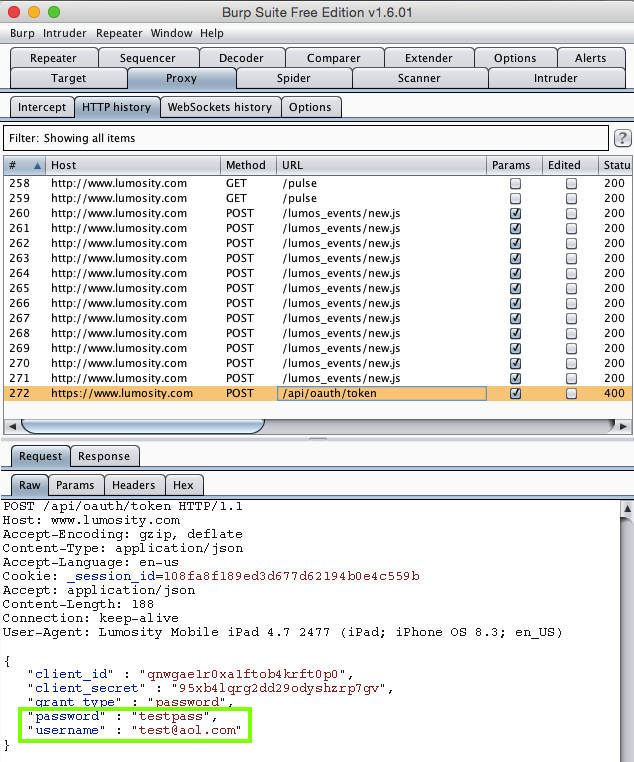
The MacBook Air is running Burp, a proxy listening on port 8080.
To test apps, I installed them on an iPad and connected it to the MacBook's Bluetooth network.
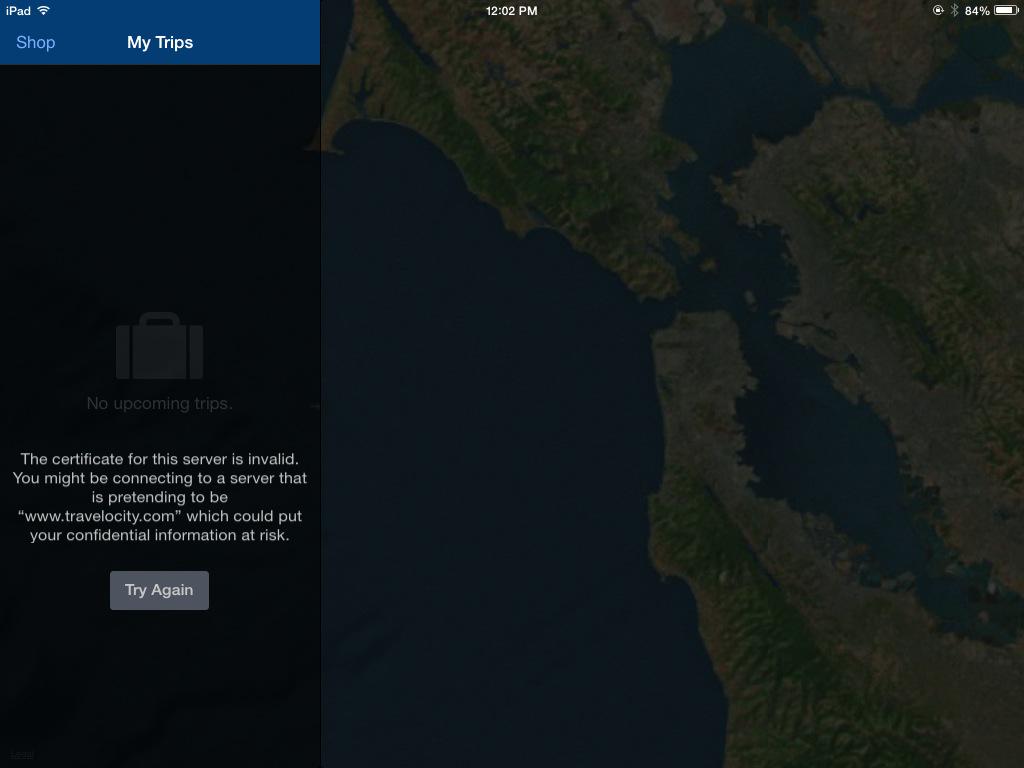
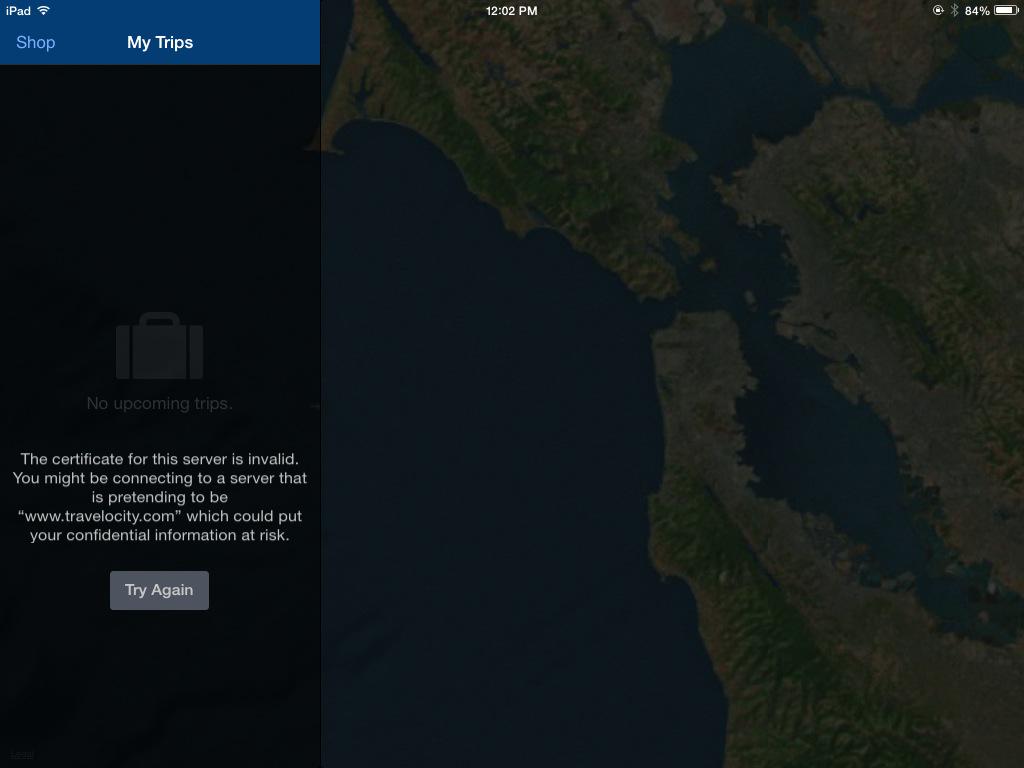
I did not install the PortSwigger certificate on the iPad, so HTTPS connections give a warning in a properly-written app, such as the Travelocity app:
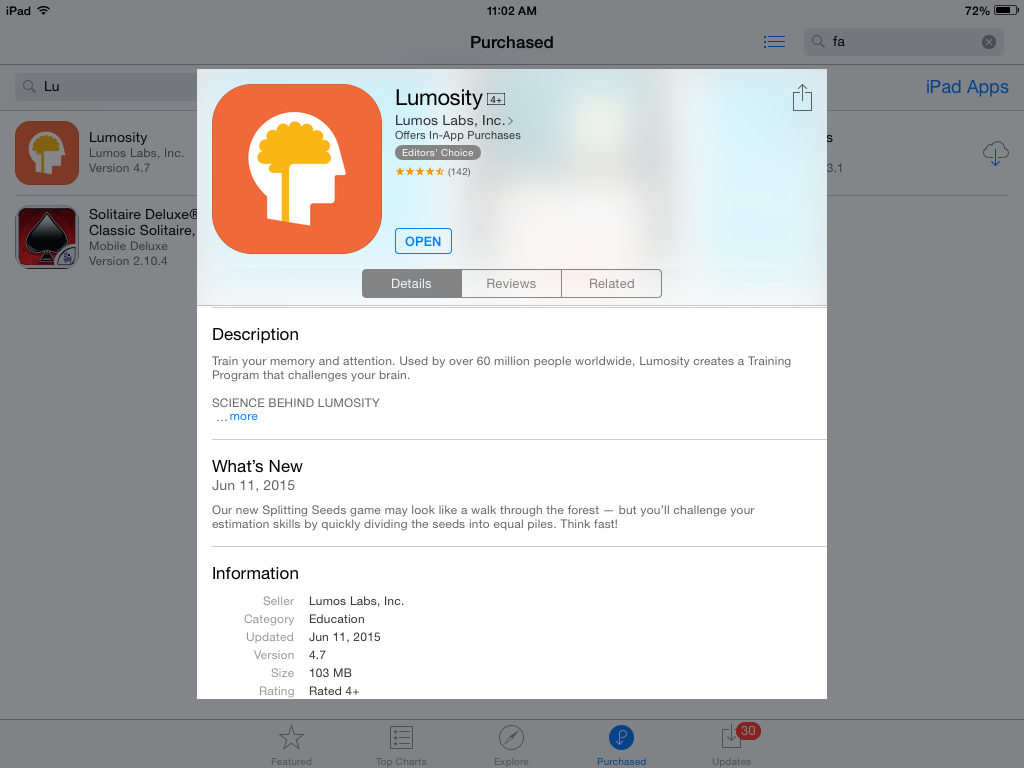
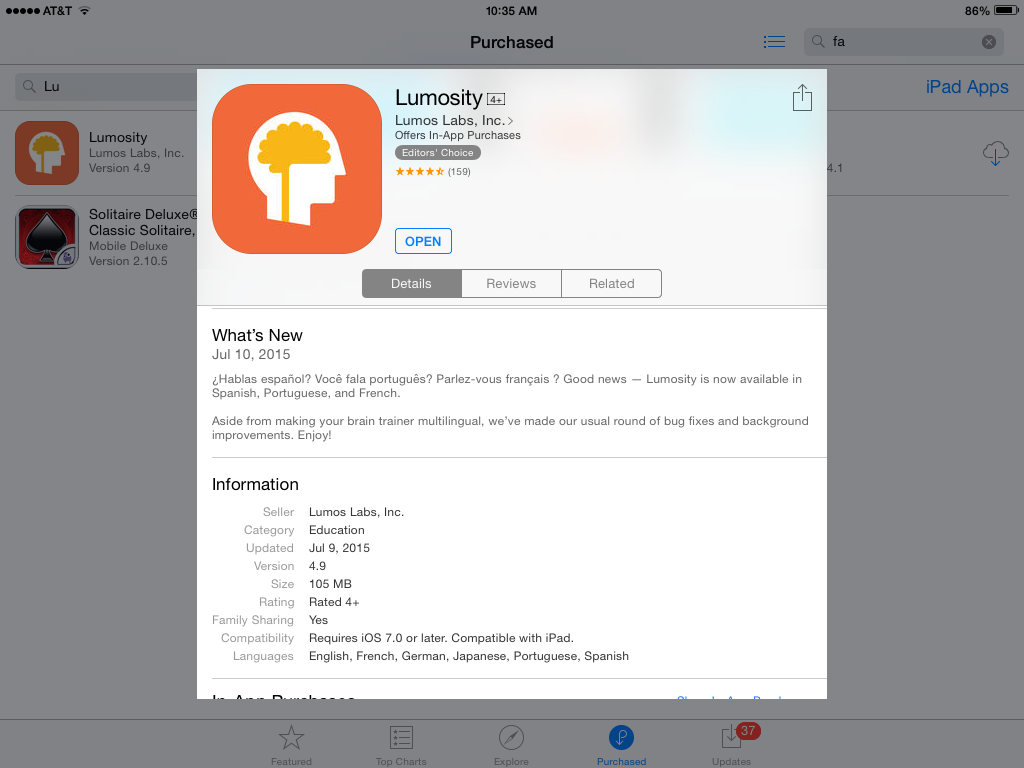
Here's the app I tested--"Lumosity for iPad":
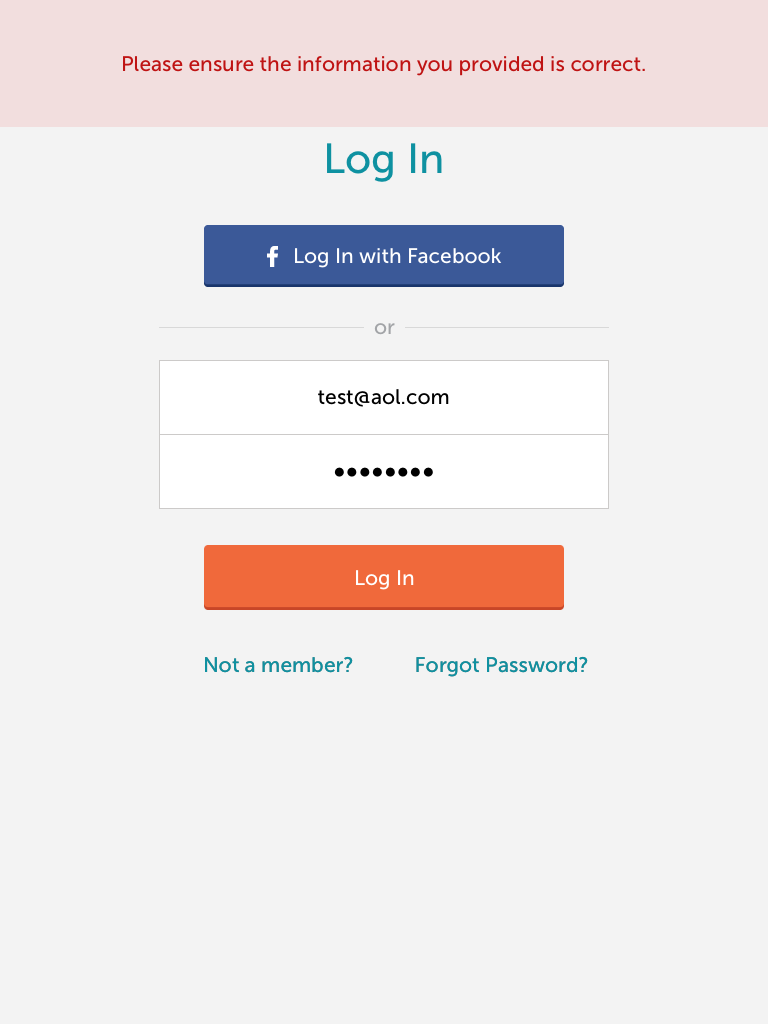
Sending test credentials:
Harvesting the data from Burp via MITM attack:
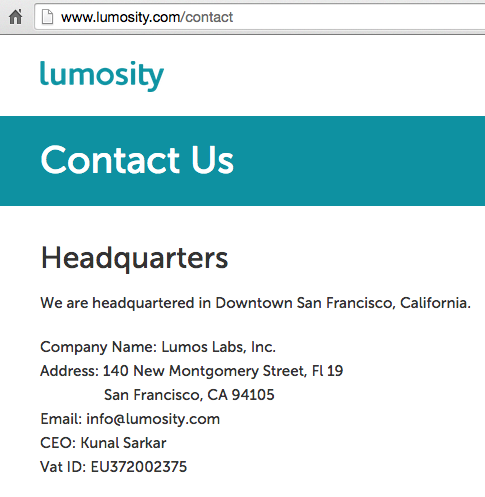
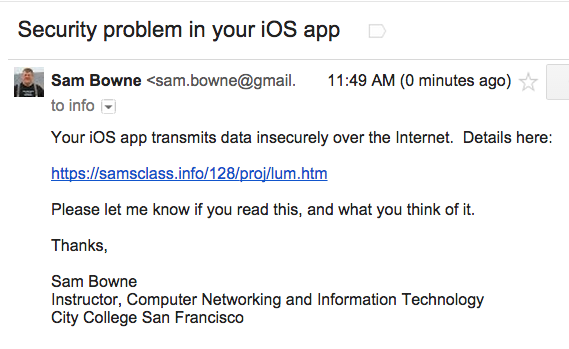
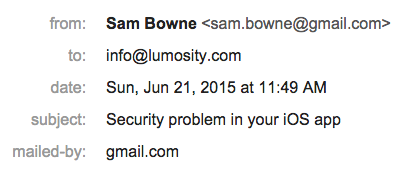
I sent this message on 6-21-15:
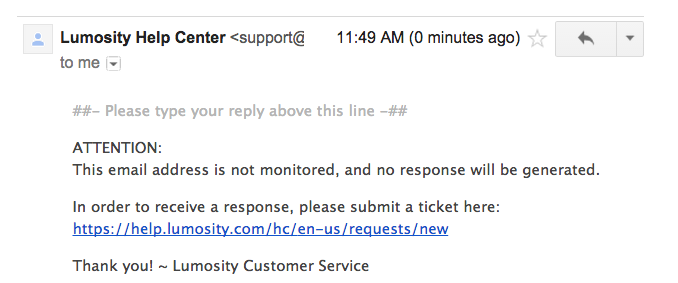
The contact link says you can submit a comment without making an account, but then requires you to make an account. I didn't want to make an account, so I tried Twitter:
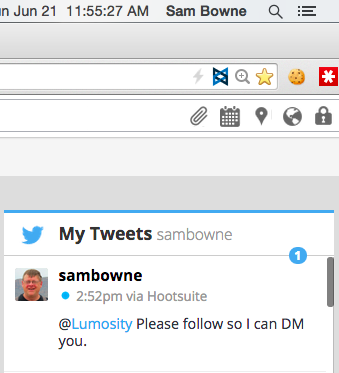
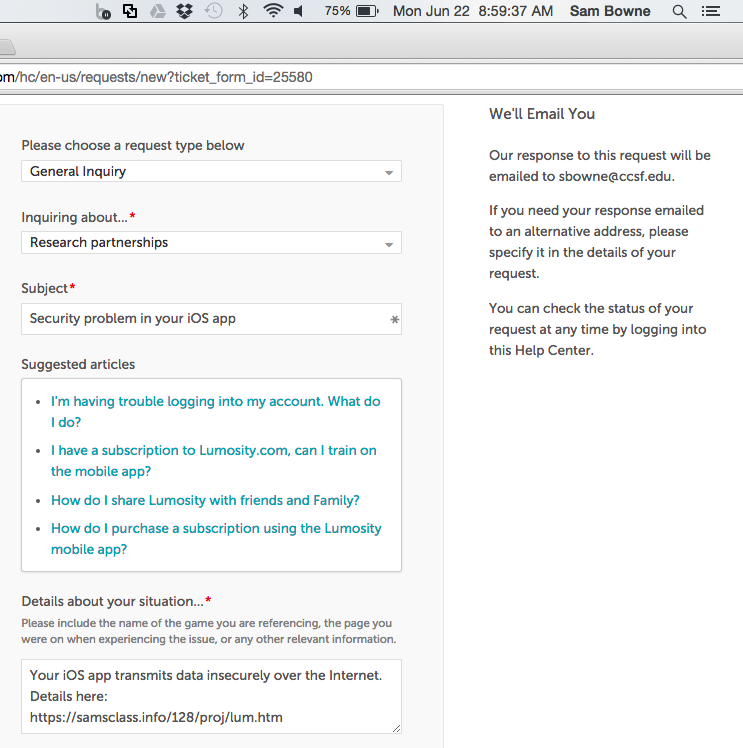
I got no response, so I created a Lumosity account and submitted a ticket:
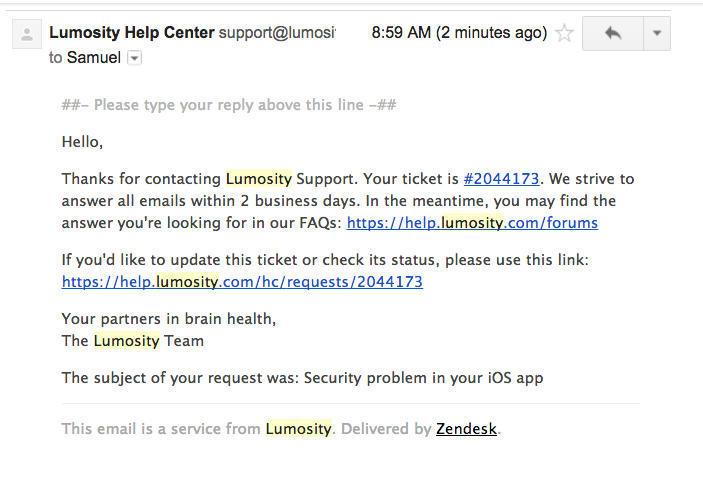
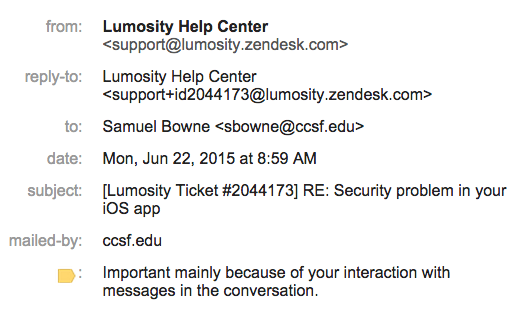
I got this response:
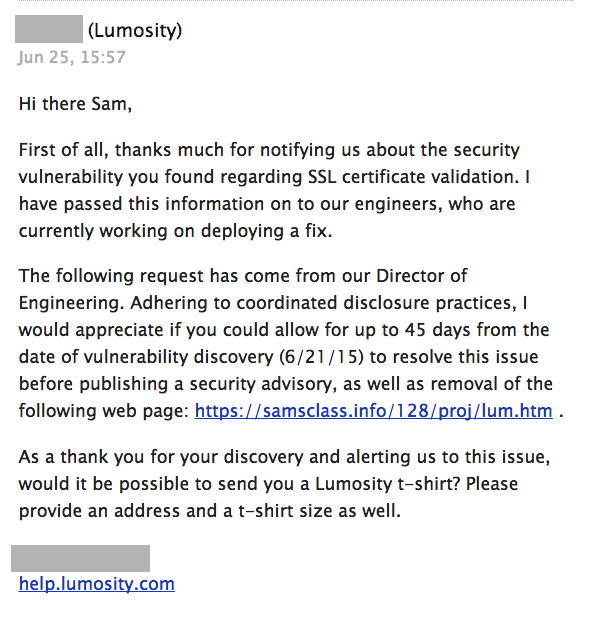
There are two Lumosity apps, one for the iPad and one for the iPhone, and they both have new versions numbered 4.8.
I tested the revised iPad app:
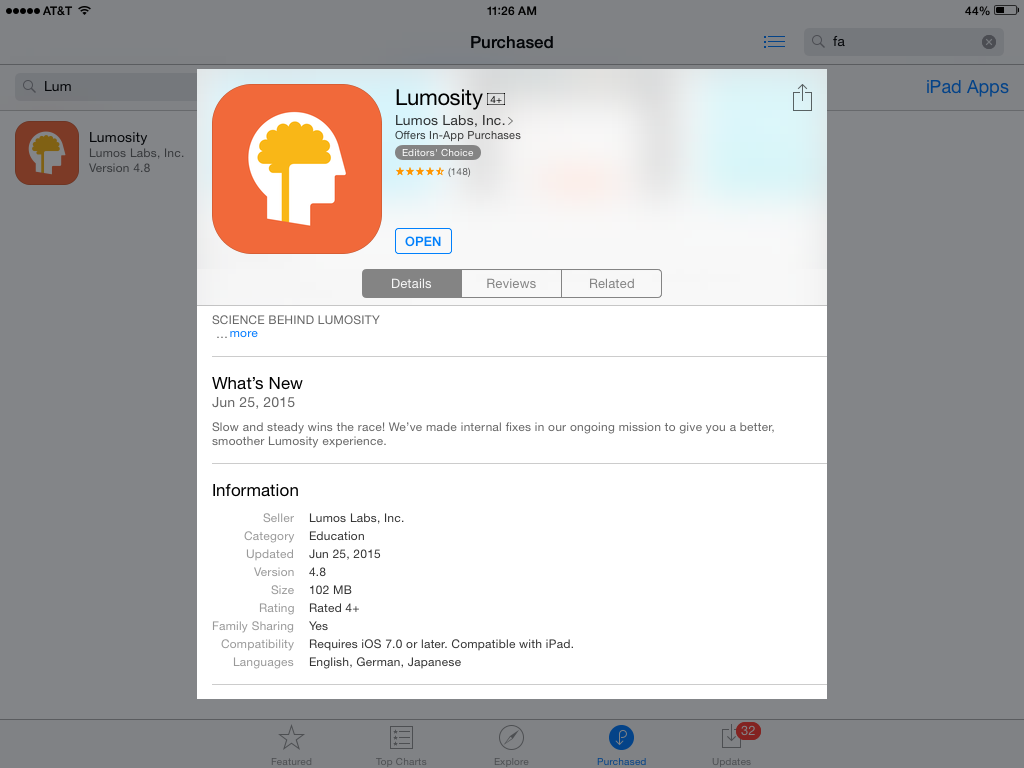
It's still vulnerable, which is not suprising since it was dated June 25, 2014, only a couple of days after I reported the problem to them.
The problem is fixed! It detects the MITM attack and shows the user an accurate and informative error message.
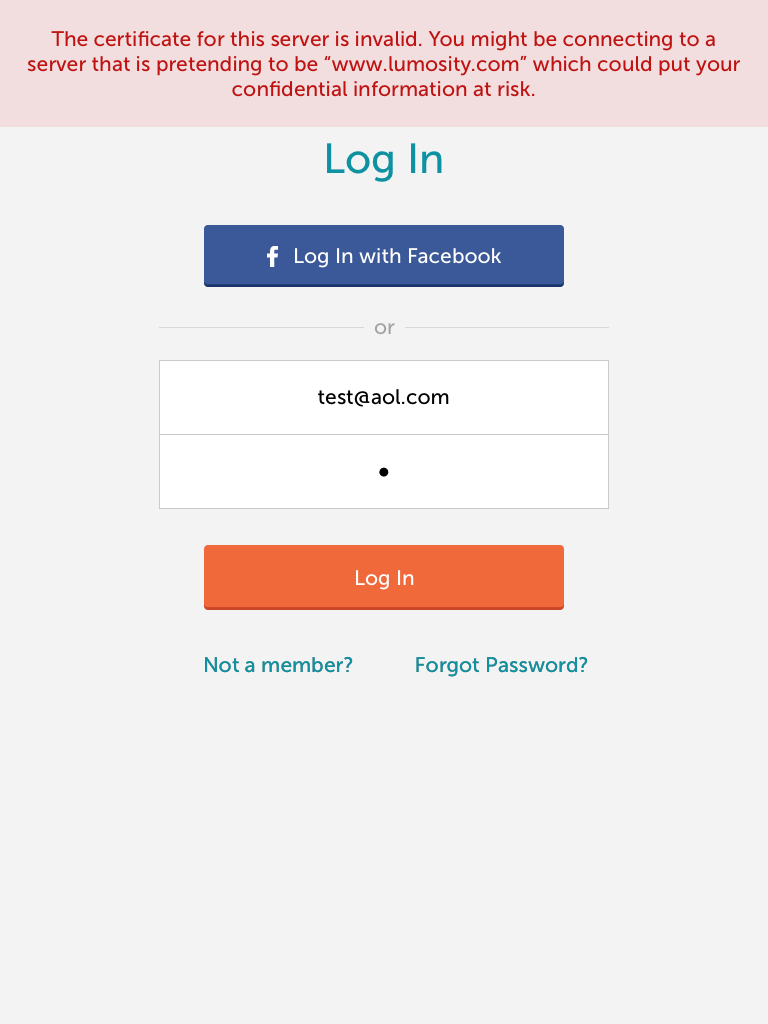
I also tested "Lumosity Mobile" for the iPhone, version 4.9. It's also fixed, displaying a similar error message :)