M 712: Plaintext Network Transmissions by iPhone Apps (15 pts)
What You Need
- An iPhone. It need not be jailbroken,
- A computer of any type
Purpose
To view iPhone network transmissions and see
passwords sent without encryption.
Responsible Disclosure
I notified all the companies about this
on or before
Jan 12, 2020, as linked below each image,
and they did nothing.
Installing an Unsafe App
Install one of the apps shown below.
(Cclicking the image goes to the
Apple Store page for the app)
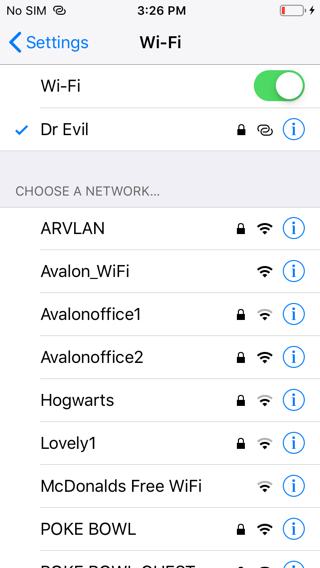
Joining a Simple Wireless Network
You need a simple wireless network
without host isolation, such as a home
wireless network, a mobile hotspot, or
DangerZone in Science 37 or 214.
Connect your computer and the iPhone to the
network.
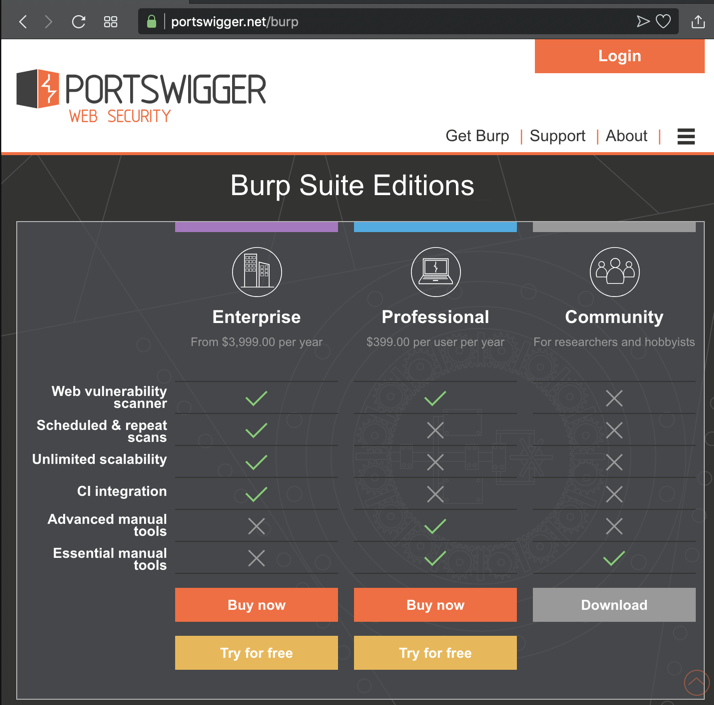
Installing Burp
If you don't have Burp installed
on your computer, go to
https://portswigger.net/burp
In the "Community Edition" column,
click Download",
as shown below.
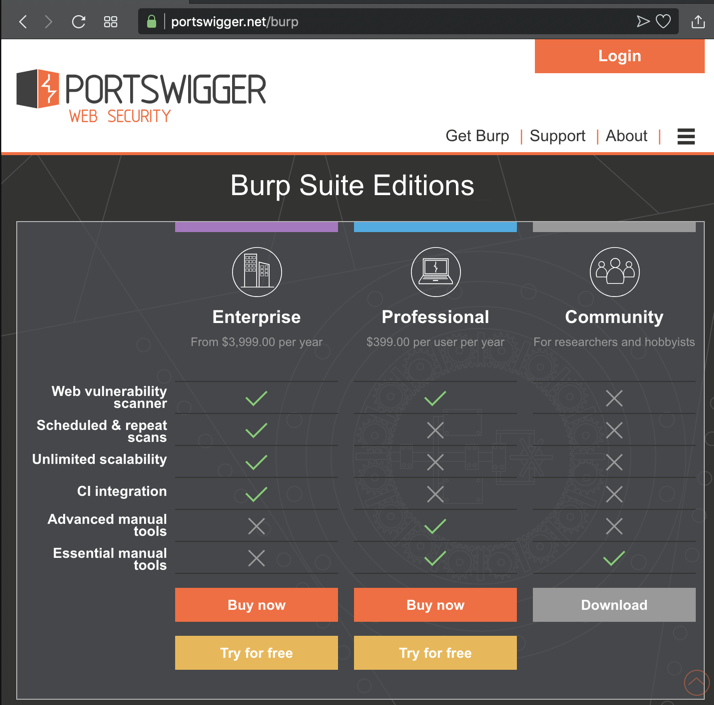
Install the software with the default options.
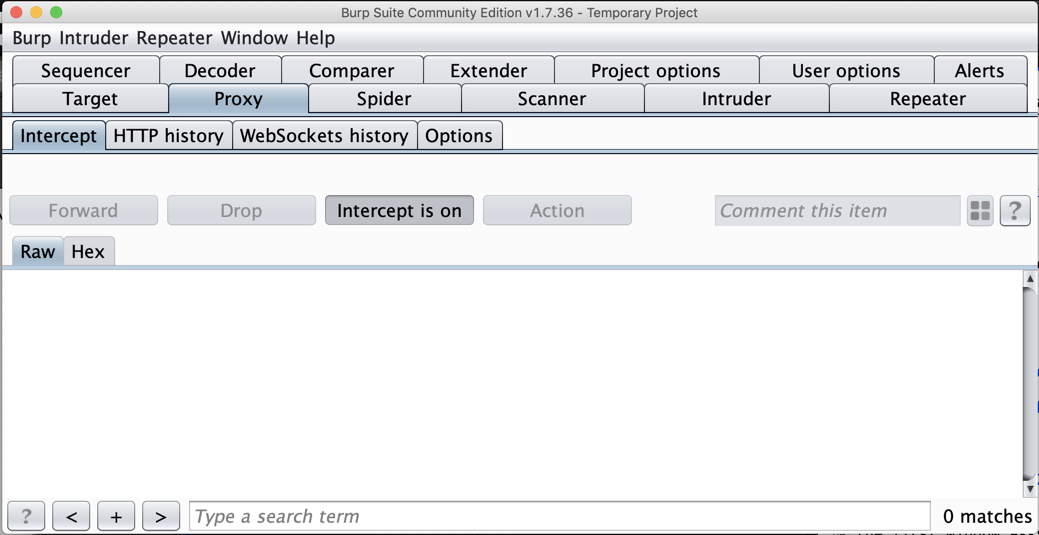
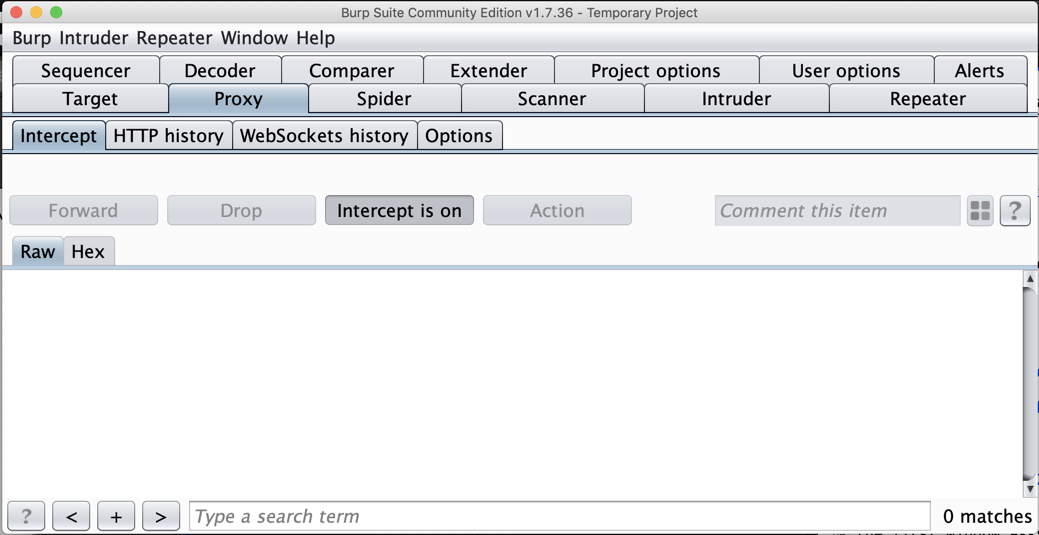
Starting Burp
When Burp starts,
the first window asks you to
create a project. Accept the default
option of "Temporary project" and
click Next.
In the next page, click the
Start Burp button.
The main
Burp window opens, as shown below.
Click the Proxy tab.
Click the Intercept sub-tab.
The third button
says "Intercept is on",
as shown below.
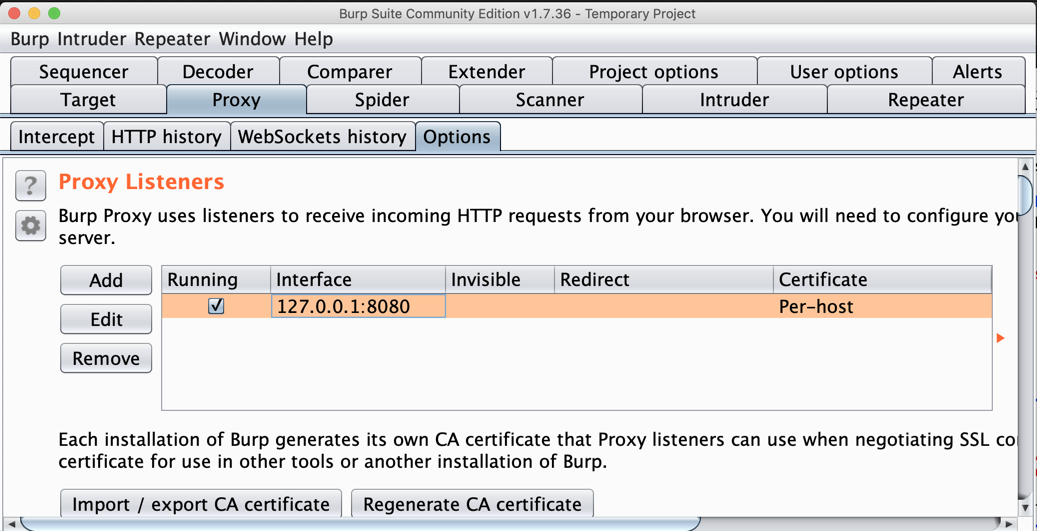
Configuring Burp
In Burp, click the
"Intercept is on" button. It changes
to "Intercept is off".
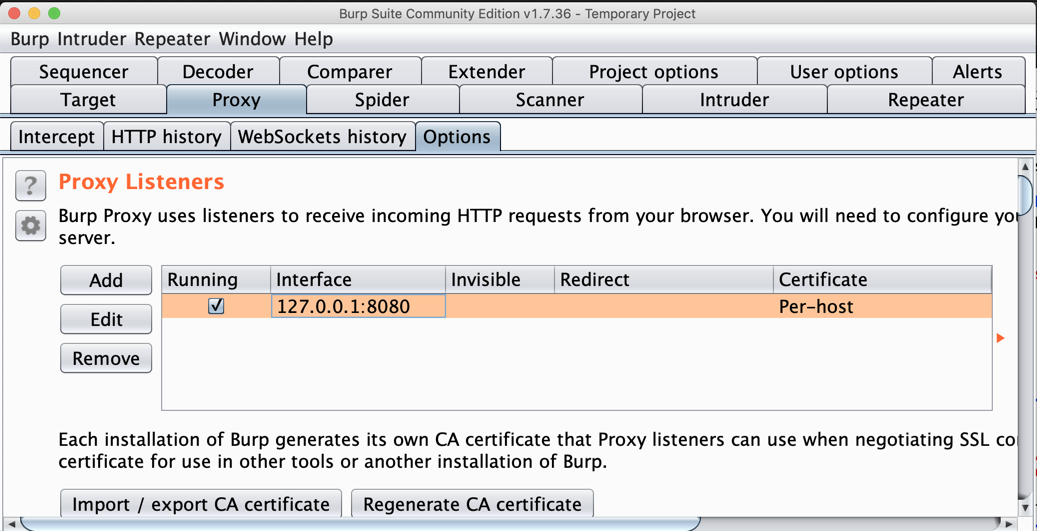
On the Proxy tab,
click the Options sub-tab.
In the central box, click the Interface address
to highlight it, as shown below.
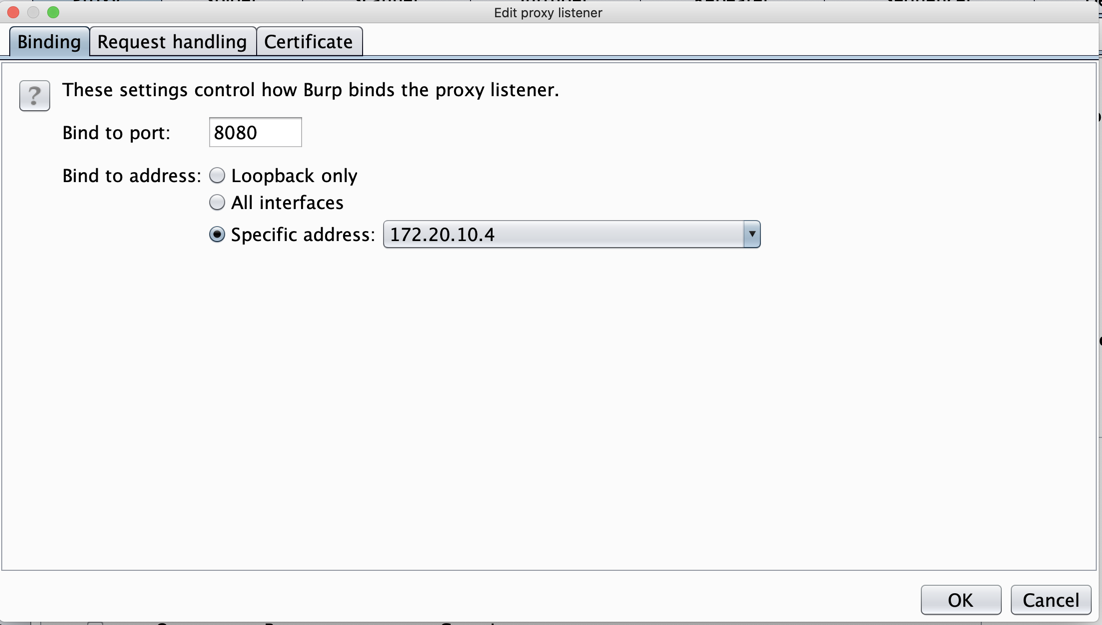
On the left side, click the Edit
button.
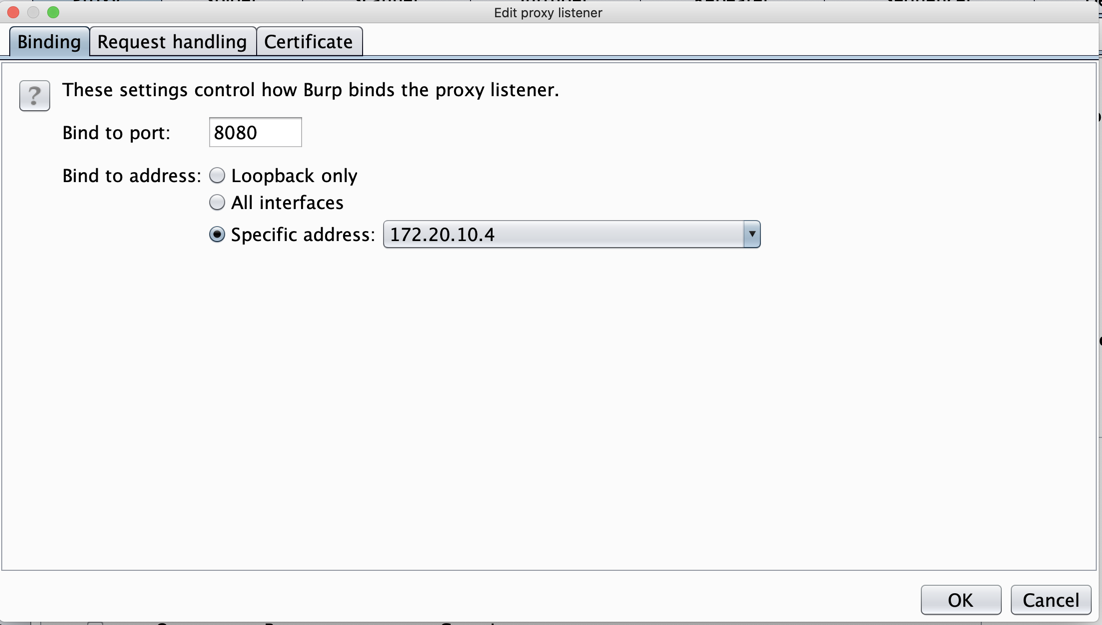
In the "Edit proxy listener" box,
click the "Specific address"
button, and select your computer's
IP address that is used to connect
to the Internet,
as shown below.
Click OK.
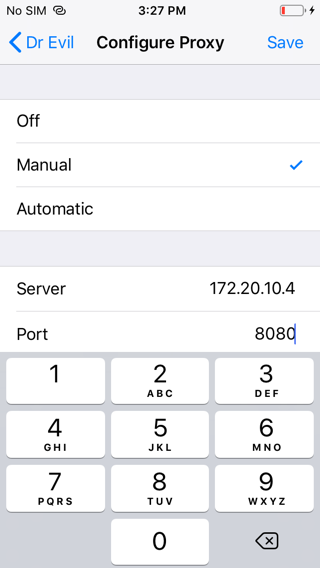
Setting the Proxy on your iPhone
On your iPhone, in Settings,
tap Wi-Fi.
The wi-fi network you are connected to
appears with a check mark,
as shown below.
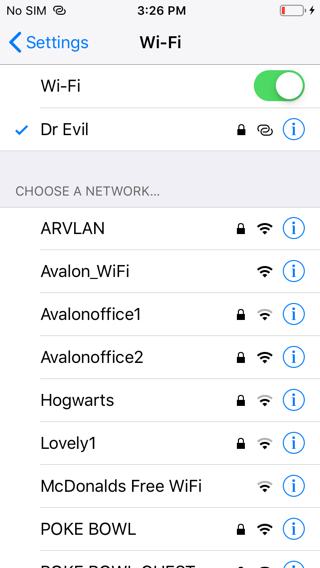
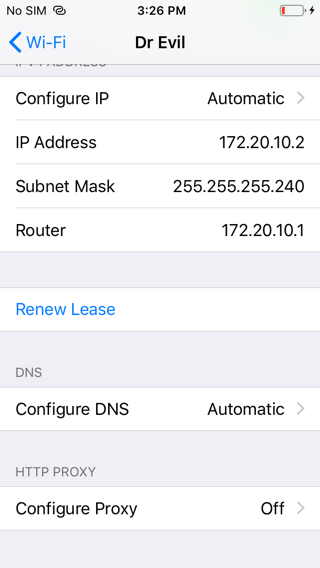
Tap the circled i next to
the wi-fi network you are connected to.
Scroll to the bottom and tap
"Configure Proxy",
as shown below.
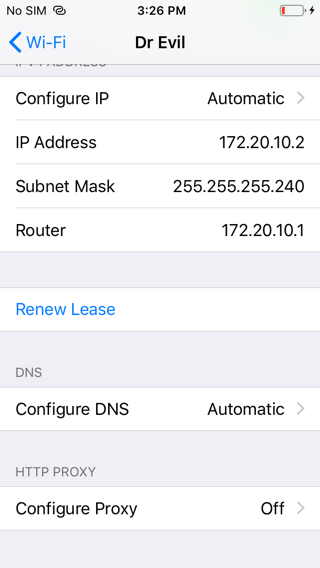
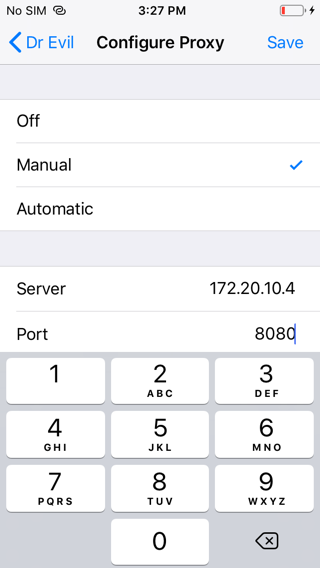
Set the proxy to Manual.
Enter the IP address Burp is listening
on and port 8080,
as shown below.
At the top right, click Save.
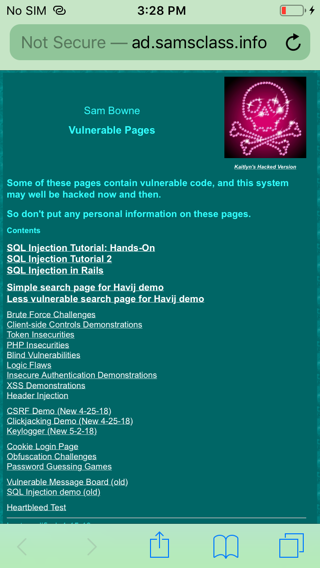
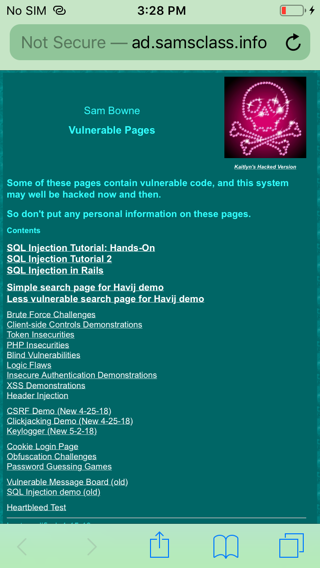
On your phone, open the browser and go to
http://ad.samsclass.info
as shown below.
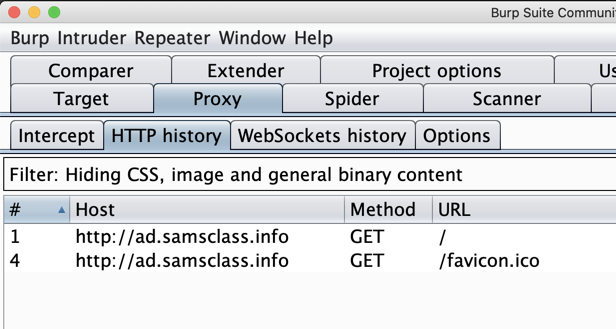
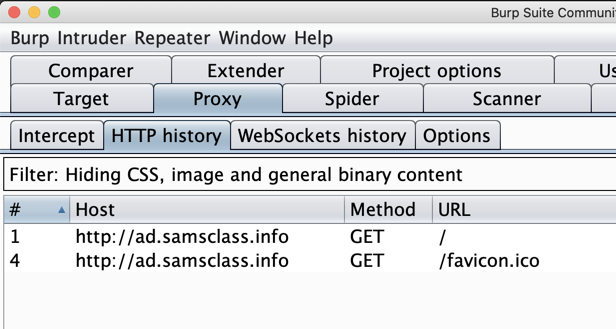
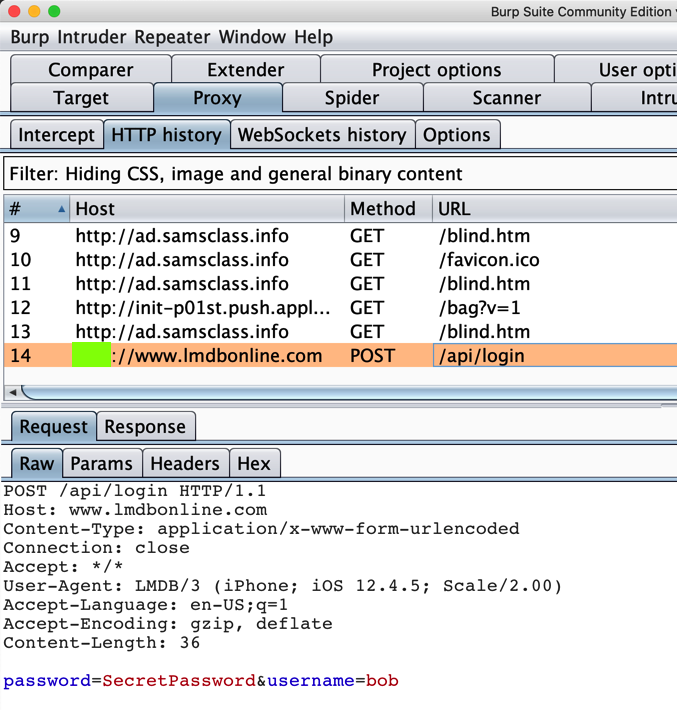
In Burp, click the
"HTTP history" sub-tab.
You should see traffic,
as shown below.
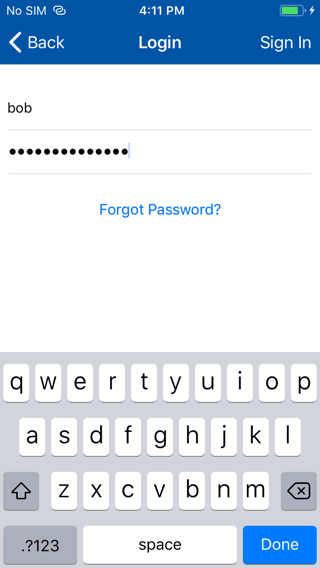
Viewing an Insecure Login
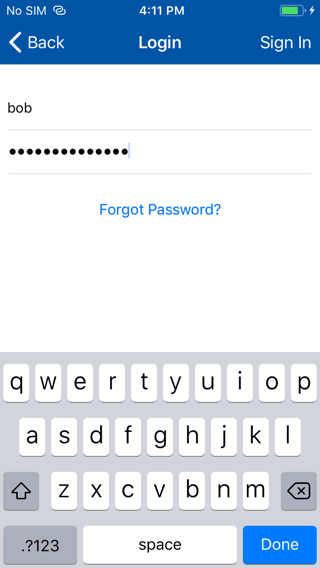
On your iPhone, open the app
and attempt a login with any
fake credentials,
as shown below.
Flag M 712.1: POST Request (15 pts)
In Burp, the POST request appears.
The flag is
covered by a green rectangle
in the image below.
|
Posted 2-12-2020