On your Linux system, with adb connected to your Android device, execute these commands:
sudo apt update
sudo apt install curl git -y
git clone https://github.com/dineshshetty/Android-InsecureBankv2.git
cd Android-InsecureBankv2
adb install InsecureBankv2.apk
cd AndroLabServer
pip install -r requirements.txt
pip uninstall backports.functools_lru_cache
pip install backports.functools_lru_cache==1.2.1
python app.py
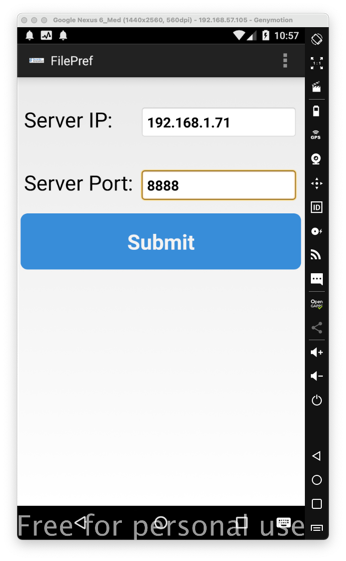
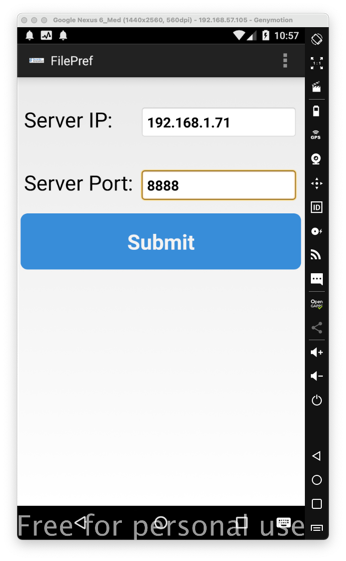
At the top right, tap the three-dot menu icon, then tap Preferences.
Enter your Debian machine's IP address, as shown below, and click Submit.
M 504.1: Insecure Network Transmission (10 pts)
Configure Burp to proxy the network traffic from your Android device.In the InsecureBankv2 app, enter these credentials, as shown below.
Click the Login button.
- Username: jack
- Password: Jack@123$
In Burp, in the server's response, find the text covered by a green box in the image below. That's the flag.
M 504.2: Insecure Logging (10 pts)
In the InsecureBank app, at top right, tap the three-dot menu icon, then tap Restart.Open a second Terminal window to your Linux server and execute this command to monitor the Android log:
In the InsecureBankv2 app, enter these credentials, as shown below.Click the Login button.
- Username: jack
- Password: Jack@123$
In the log, find the text covered by a green box in the image below. That's the flag.
M 504.3: Insecure Exported Activities (10 pts)
In the InsecureBank app, at top right, tap the three-dot menu icon, then tap Restart.Connect with Drozer.
Execute these commands to see the package name, its attack surface, and details about the exported activities:
As shown below, none of the activities require any permissions.
On your Android device, tap the Home button to minimize all windows.
You can launch the Login activity with this Drozer command:
Try launching all the activities. Obviously, some of them should not be available before logging in.Find the screen containing the flag, covered by a green box in the image below.
M 504.4: Insecure Broadcast Receiver (10 pts)
In Drozer, execute this command to see the exported broadcast receiver and its intent filter:As shown below, the receiver name is MyBroadcastReceiver and it processes actions with the name theBroadcast. No permission is required to send an intent to this receiver.
To understand this receiver, we need to examine the source code. Open the InsecureBankv2.apk file in jadx-gui, which you prepared in a previous project.
View the source code for MyBroadcastReceiver, as shown below. The flag for M 504.4 is covered by a green box in the image below.
Look at the code outlined in red in the image above.
The Intent contains two string values: phonenumber and newpass.
The receiver sends an SMS message using these values.
Execute this Drozer command to trigger the intent (this attack is called intent injection):
As shown below, this sends an SMS from your device. This could be used to trick you into using a premium rate service and losing money.
If you were logged in, the action you performed above changed your password. To get back to the original state, remove and reinstall the application.
M 504.5: Intent Sniffing (5 pts)
In Drozer, execute this command to monitor the intents sent with action theBroadcast:On your Android device, in the InsecureBankv2 app, log in and execute the Change Password action.The flag is covered by a green box in the image below.
M 504.6: Root Detection (15 pts)
On a rooted Android device, such as Genymotion, the InsecureBank app and log in. You see a message saying "Rooted Device!!", as shown below.
The root detection searches for two files, named su and Superuser, outlined in blue in the image below.
Decompile the app with apktool, and change those two filenames to tu and Tuperuser.
Rebuild and sign the app. Uninstall the original app, install the modified one, and sign in.
You will see a different message, covered by a green rectangle in the image below. That's the flag.