WARNING: Slow Project
Qark takes about 30 minutes to run. If you don't want to wait, skip this project.
sudo apt update
sudo apt install git unzip python3-pip python3-full default-jdk -y
wget https://github.com/linkedin/qark/archive/refs/heads/master.zip
unzip master.zip
python3 -m venv qark-venv
source qark-venv/bin/activate
pip3 install qark
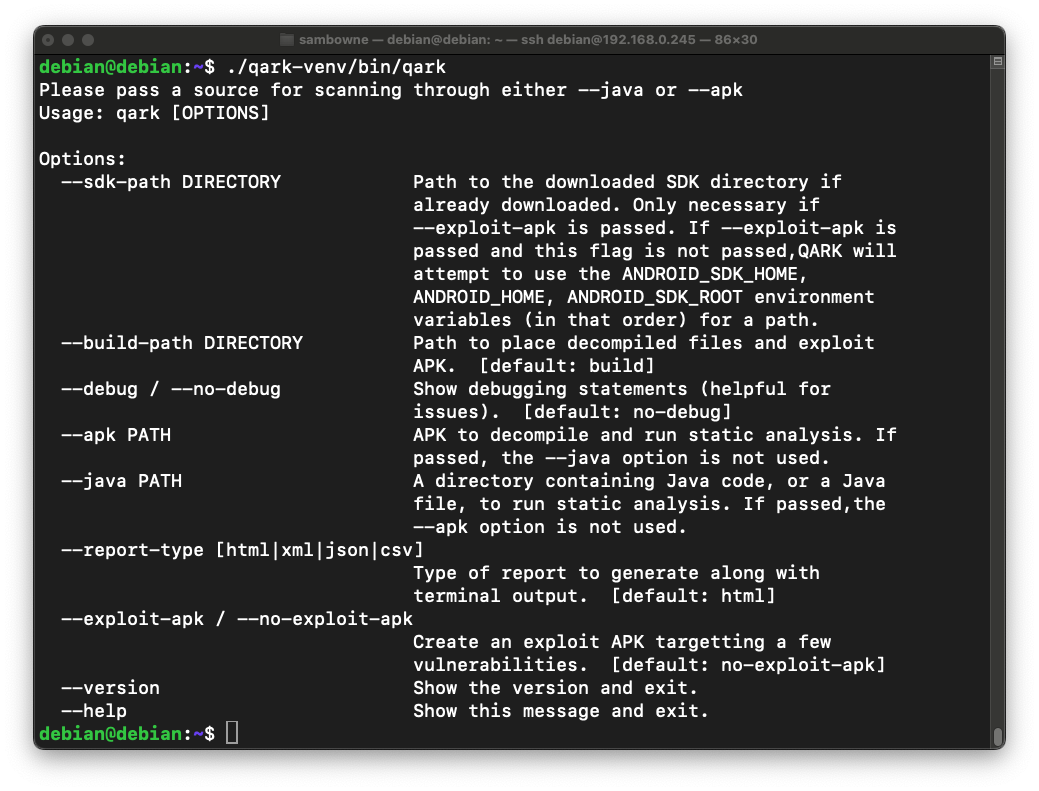
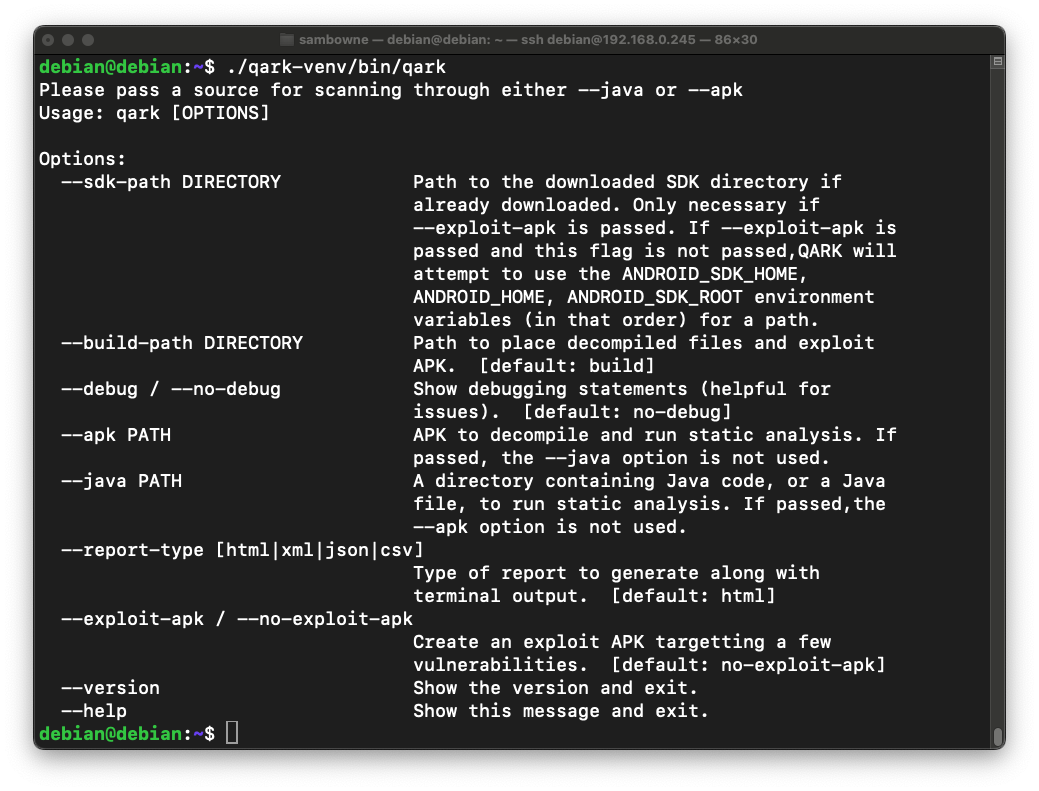
qark
If you see a message saying "qark not found", reboot your Debian machine.
wget https://samsclass.info/128/proj/genie.apk
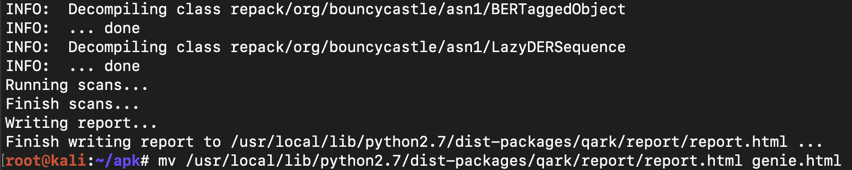
qark --apk genie.apk
After the report is generated, move it to a more convenient location and name with this command:
mv /home/debian/qark-venv/lib/python3.11/site-packages/qark/report/report.html genie.html
Navigate to the genie.htm file, as shown below, and double-click it.
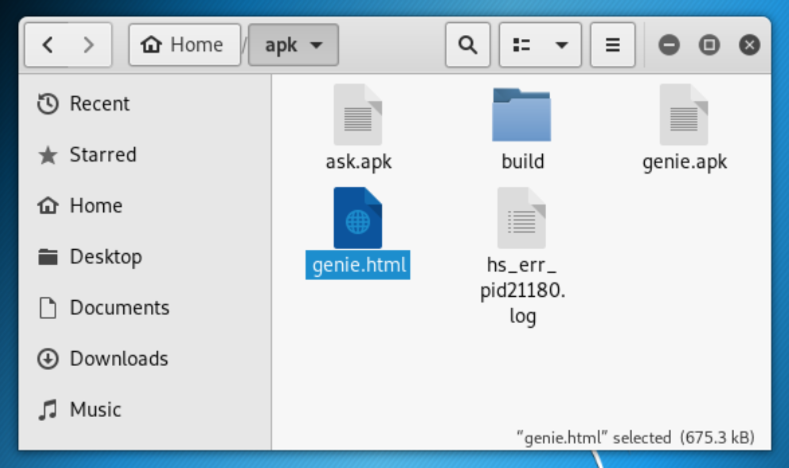
If you are using a headless server, use an scp command like the one below to move the report to your host machine and open it there.
scp debian@192.168.0.245:genie.html .
Type Ctrl+F and search for cert to find the SSL certificate validation error, as shown below.
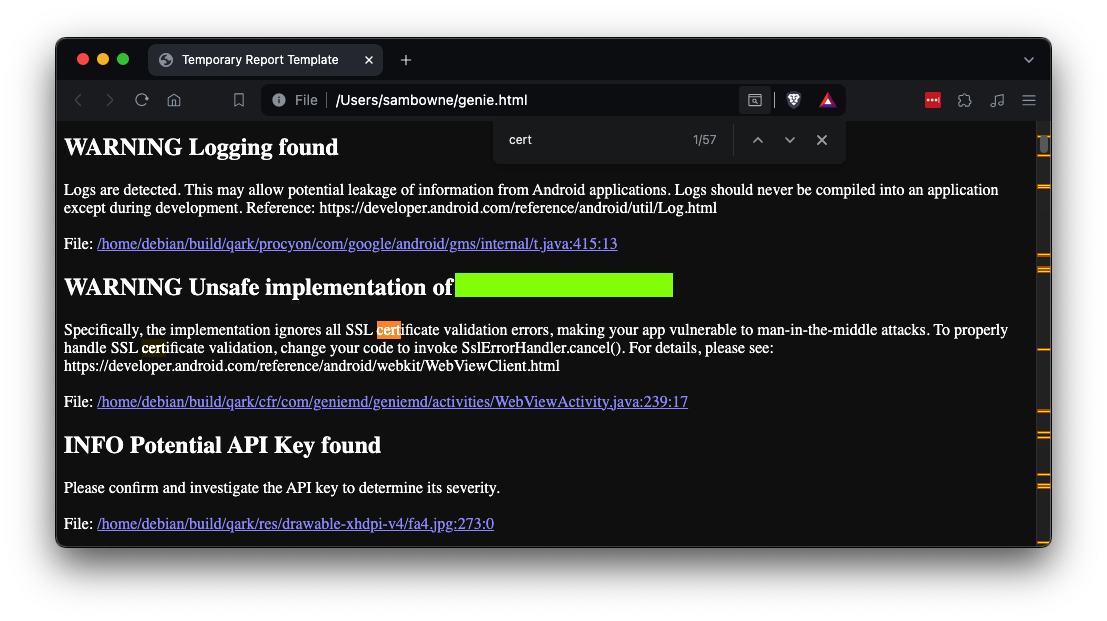
M 301: Unsafe implementation (15 pts)
Find the text covered by a green box in the image above. That's the flag.