If you'd like a local copy of the server program to analyze, use these commands:nc attack32direct.samsclass.info 6010
Exploit this process and get a shell on the server. Then put your name in this file:curl https://samsclass.info/127/proj/p6x.c > p6x.c curl https://samsclass.info/127/proj/p6x > p6x
Create this file:/home/p6x/winners
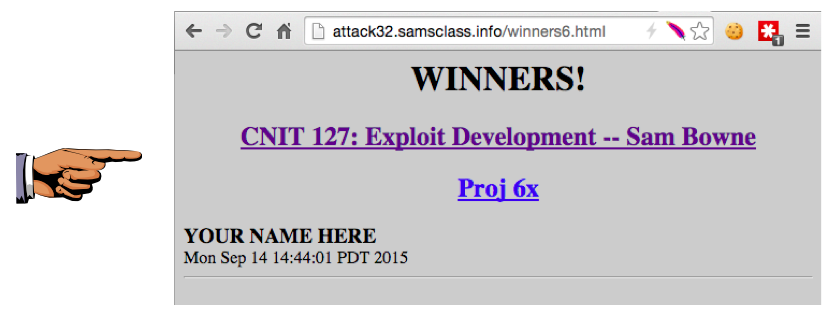
After one minute, your name will appear on the WINNERS page here:/home/p6x/updatenow
http://attack32direct.samsclass.info/winners6.html
NOTES:
Troubleshooting
If your exploit fails, it might be that the port is in use. You can check the local network connections at this page:http://attack32direct.samsclass.info/netstat.htm
That page is updated every 5 seconds.
If you kill the server, it will restart after one minute
There are two other identical servers running on ports 6011 and 6012
Every 15 minutes, all three servers are restarted
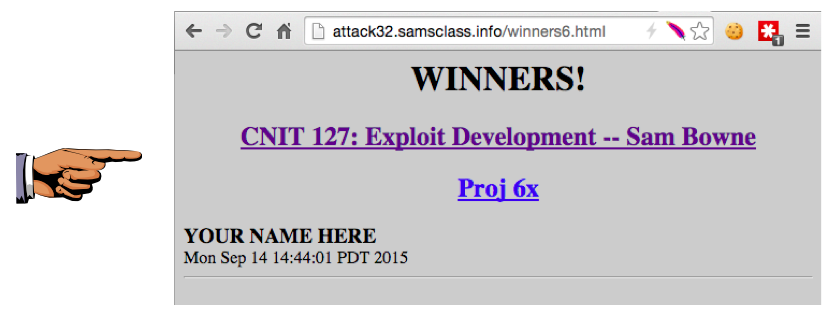
Capture a full-screen image.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
Save the image with the filename "YOUR NAME Proj 6x", replacing "YOUR NAME" with your real name.