If you'd like a local copy of the server program to analyze, use these commands:nc attack.samsclass.info 13010
Exploit this process and get a shell on the server. Then put your name in this file:curl https://samsclass.info/127/proj/p13x.c > p13x.c curl https://samsclass.info/127/proj/p13x > p13x
Create this file:/home/p13x/winners
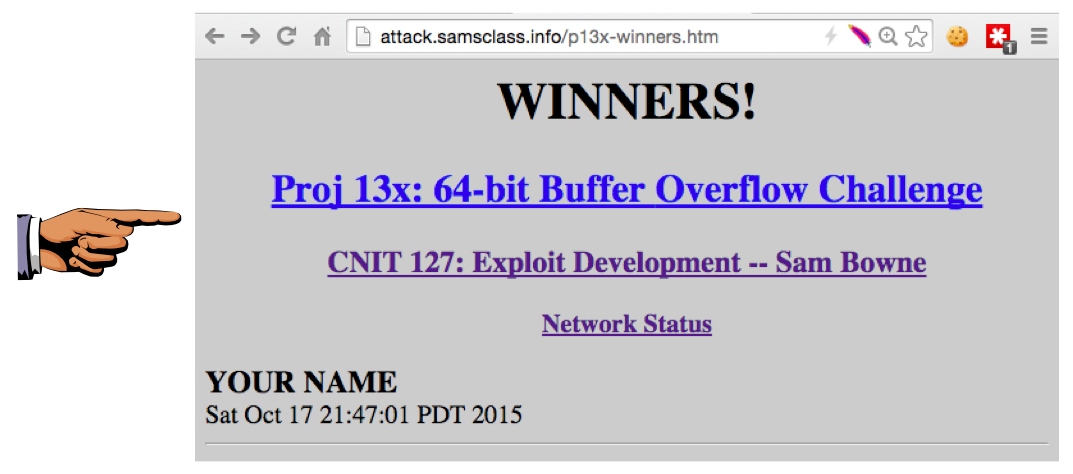
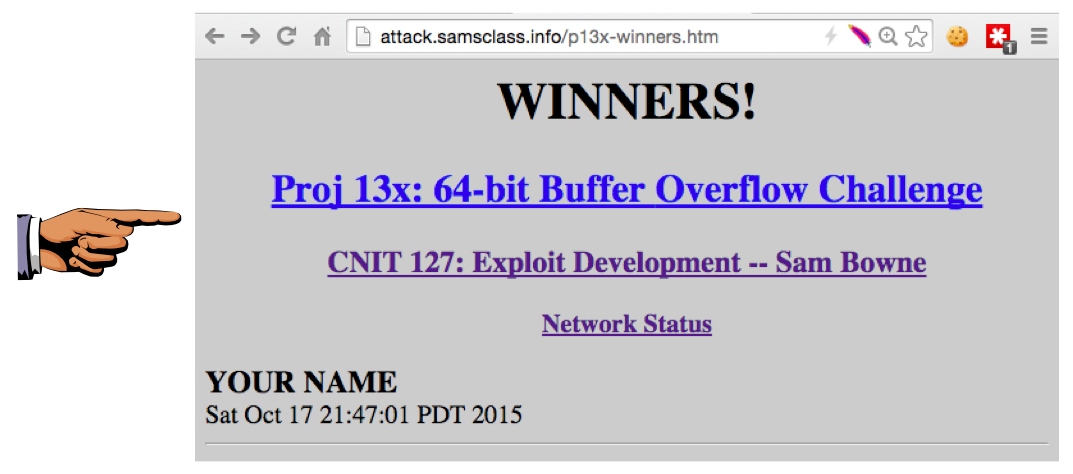
After one minute, your name will appear on the WINNERS page here:/home/p13x/updatenow
http://attack.samsclass.info/p13x-winners.htm
Troubleshooting
If your exploit fails, it might be that the port is in use. You can check the local network connections at this page:http://attack.samsclass.info/netstat.htm
That page is updated every 5 seconds.
Hints
- There are ten identical listening processes, on ports 13010 through 13019. Each process is automatically killed and restarted each minute.
- ASLR is enabled--you must write a script that reads the pointer, calculates the correct attack code, and sends it immediately.
- There is no firewall, so a simple port binding attack will work.
Capture a full-screen image.
YOU MUST SUBMIT A FULL-SCREEN IMAGE FOR FULL CREDIT!
Save the image with the filename "YOUR NAME Proj 13x", replacing "YOUR NAME" with your real name.