If you have Kali 2016.2 and run updates, it changes the default gcc compiler option to -pie, so it produces Position Independent Executables.
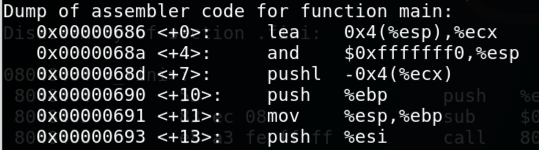
This causes gdb to report all addresses near zero, like this:
That breaks the process of Exploit Development we're using in our projects, since we can't inject addresses containing that many zeroes into strings.
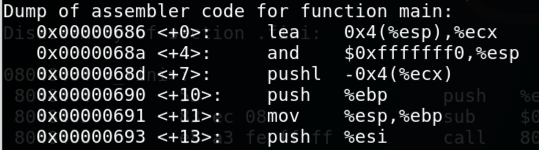
The solution is to explicitly turn off PIE during compilation, as shown below.
-pie
switch when invoking gcc,
as shown below.
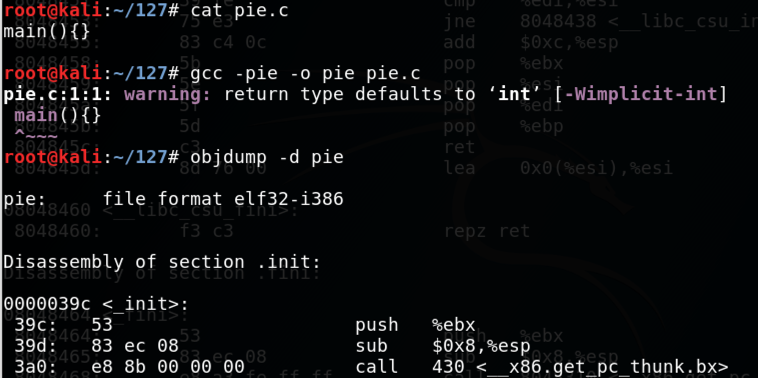
-no-pie
switch when invoking gcc,
as shown below.
For the existing projects in CNIT 127, use the
-no-pie
switch.
It may be interesting to develop exploit for PIE executables, but I haven't done that yet.