XOR operates on one bit at a time, with these results:
0 XOR 0 = 0
0 XOR 1 = 1
1 XOR 0 = 1
1 XOR 1 = 0
Characters are ASCII-encoded, like this:
A is 01000001
B is 01000010
C is 01000011
...
Consider A^B:
A is 01000001
B is 01000010
A^B= 00000011
However, A^s is printable:
A is 01000001
s is 01110011
A^B= 00110010
section .text
global _start
_start:
mov ecx, 5 ; number of characters to encrypt
loop1:
push ecx
mov ebx, msg ; start of message
add ebx, ecx
sub ebx, 1
mov al, [ebx] ; address of current character
xor eax, 3 ; 3 is the key
mov [ebx], al
pop ecx
loop loop1
mov edx, len
mov ecx, msg
mov ebx, 1
mov eax, 4
int 0x80 ; print message
mov eax, 1
int 0x80 ; exit
section .data
msg db "HELLO", 13, 10
len equ $ - msg
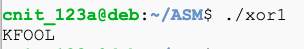
ASM 210.1: XOR with the Key (5 pts)
XOR the text below with a key of 11 to reveal the flag.
ASM 210.2: XOR without the Key (15 pts extra)
The key is between 1 and 40. XOR the text below to produce a readable flag.Hint: use procedures.