Proj 7x: Analyzing Malicious Windows Programs (Lab 7-2) (15 pts.)
What you need:
- A Windows XP or Windows 7 machine with IDA PRO and the other tools we have been using
- The textbook: "Practical Malware Analysis"
Purpose
You will practice the techniques in chapter 7.
You should already have the lab files, but if
you don't, do this:
Downloading the Lab Files
In a Web browser, go here:
http://practicalmalwareanalysis.com/labs/
Download and unzip the lab files.
Follow the instructions for Lab 7-2 in the
textbook. There are more detailed solutions
in the back of the book. The only purpose of this
document is to explain what image to turn in.
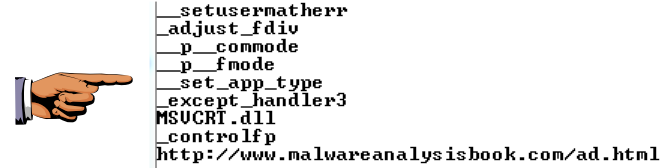
Unicode String
Use an appropriate tool to display Unicode
strings. You cannot do this with
IDA Pro Free.
When you display the URL shown at the
bottom of the image below,
capture a full-desktop image.
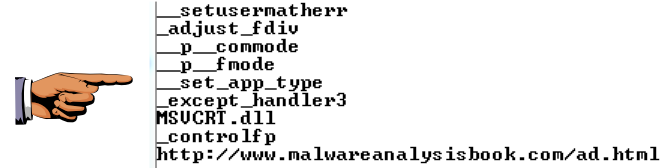
Save this image with the filename
"Proj 7xa from YOUR NAME".
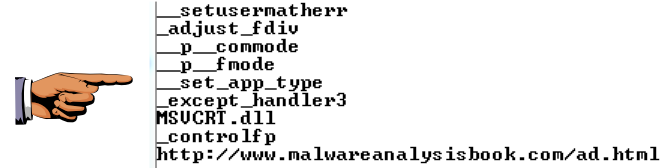
rclsid
Use IDA Pro Free to find the value of
rclsid. It's spread across
several lines of assembly code,
as shown below, but you can
reassemble it to form a single
128-bit value starting with 2DF0
and ending with 0046.
Save a full-desktop image showing the value of
rclsid, as shown below.
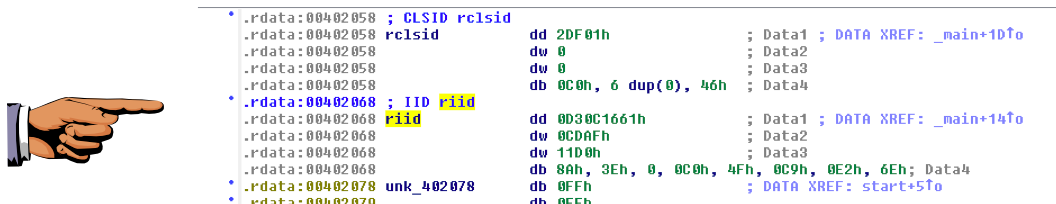
Save this image with the filename
"Proj 7xb from YOUR NAME".
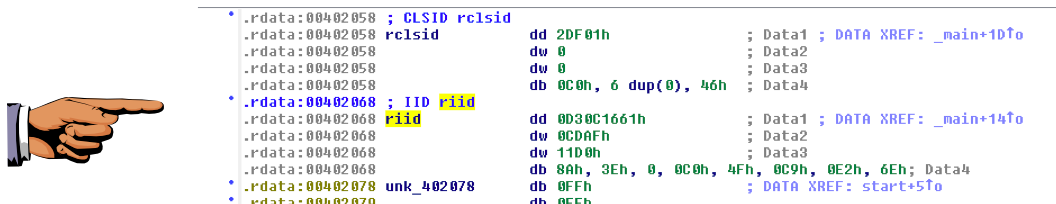
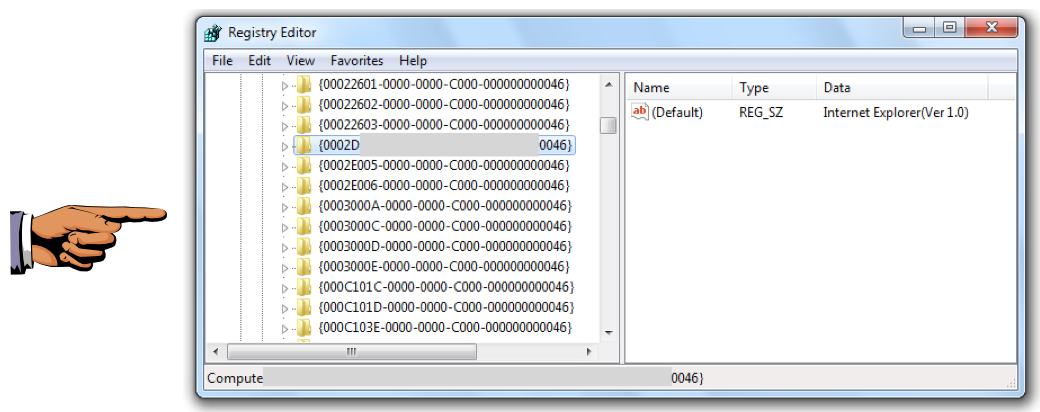
Registry
Find the rclsid in the Registry.
Save a full-desktop image showing its
value, including the fields grayed
out below.
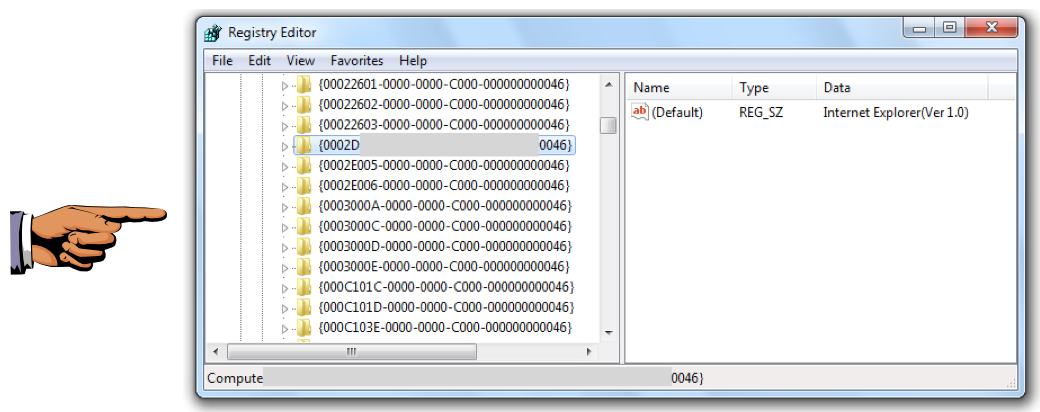
Save this image with the filename
"Proj 7xc from YOUR NAME".
Turning in your Project
Email the images
to cnit.126sam@gmail.com with the subject line:
Proj 7x from YOUR NAME
Last modified 9-30-13 4:43 pm