If you are using some other machine, such as a Google Cloud Windows 2016 Server, do these steps to install Java.
Jasmin launches, with a cringe-worthy pinup on it, or a picture of flowers.
Click the "New File" button.
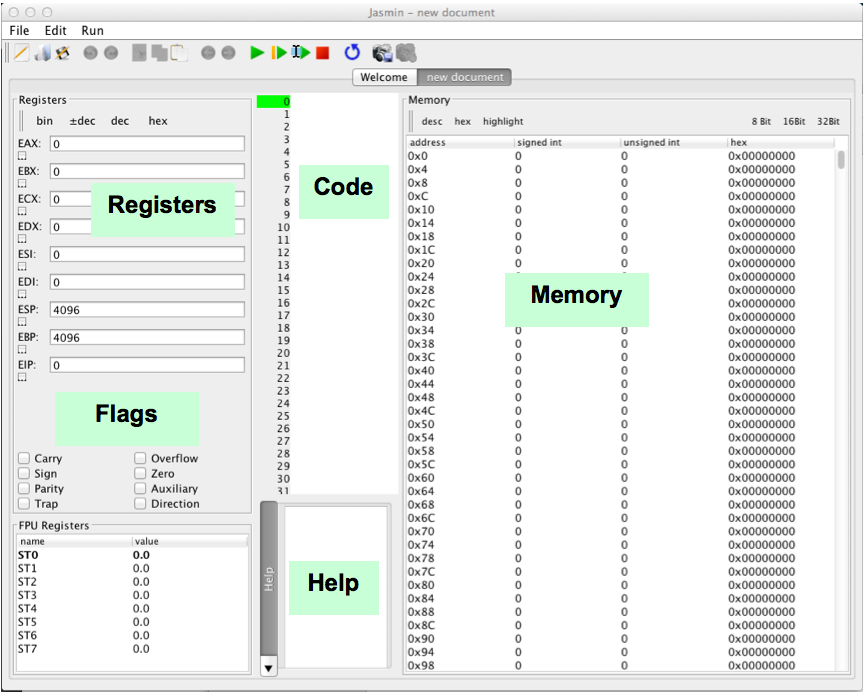
Look over the window, referring to the diagram below:
Find and examine these sections:
The ESP (Extended Stack Pointer) contains the address of the top of the Stack.
The EIP (Extended Instruction Pointer) contains the address of the the next instruction to be processed.
With the Memory pane scrolled to the top, as shown in the image above, you see memory that the program will use to store data during processing.
Scroll this pane to the bottom to see the Stack, which starts at address 0x1000 and grows downward.
mov eax, 4
mov ebx, 6
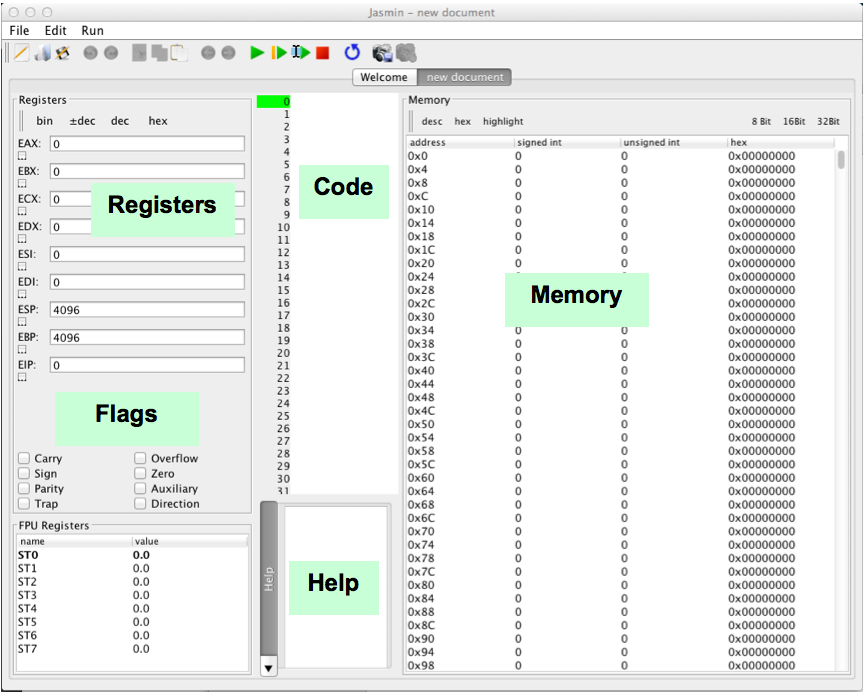
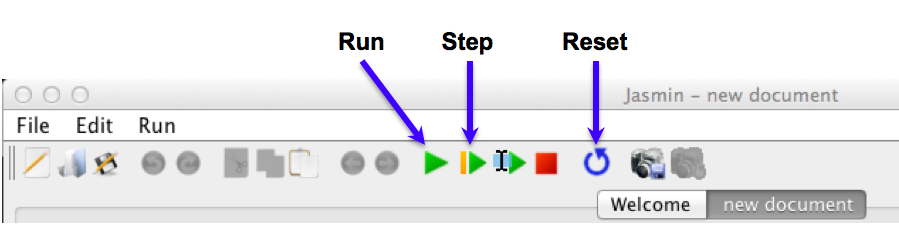
At the top of the Jasmin window, click the green Run button, as shown below.
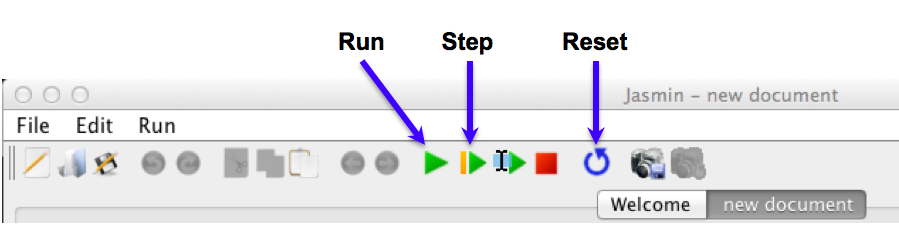
The program runs. When it stops, notice these things, as shown below:
Troubleshooting
If you make an error in an instruction, the program will stop prematurely. Fix the instruction, and click the Reset button. Then you can run it again.
mov eax, 4
mov ebx, 6
mov [eax], ebx
mov ecx, eax
add ecx, ebx
mov [eax+4], ecx
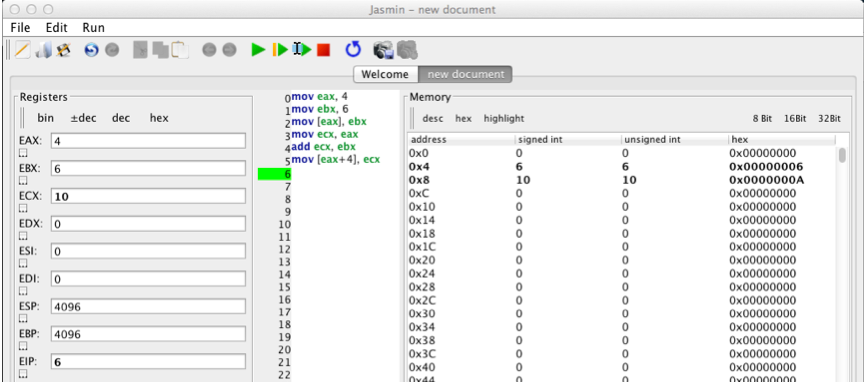
Run the program. When it completes, you should see these results, as shown below:
mov eax, 4Move the value 4 into eax mov ebx, 6Move the value 6 into ebx mov [eax], ebxMove the value in ebx (which is 6) into the memory location pointed to by eax (memory location 4) mov ecx, eaxMove the value in eax (which is 4) into ecx add ecx, ebxAdd the value in ebx (which is 6) to the value in ecx (which is 4), and put the result into ecx (the result is 10) mov [eax+4], ecxMove the value in ecx (which is 10) into the memory location four past the location pointed to by eax (memory location 8)
In the Code section, type in these instructions.
mov eax, 4
mov ebx, 6
push eax
push ebx
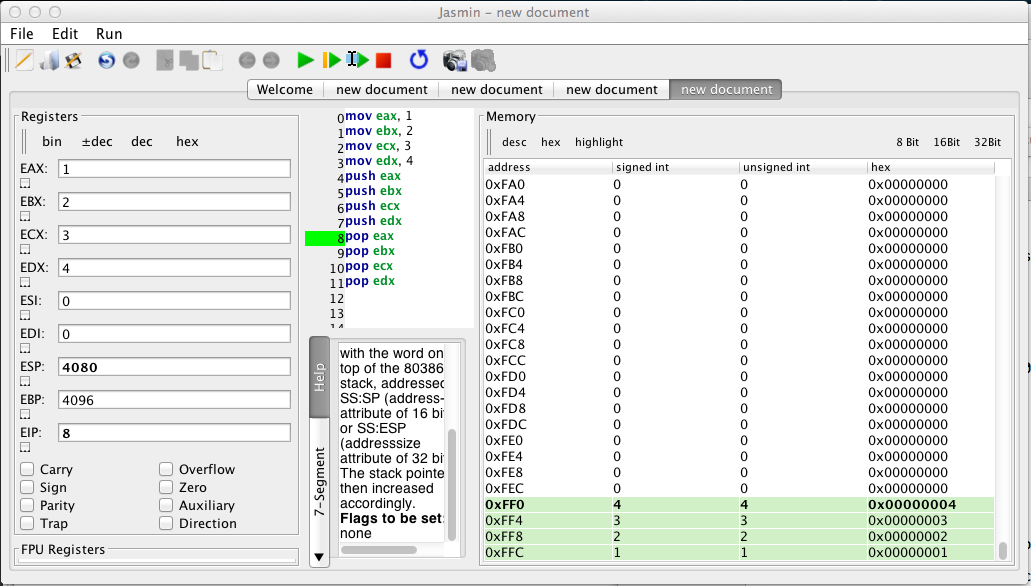
4096 is 0x1000 in hexadecimal--this is where the Stack ends.
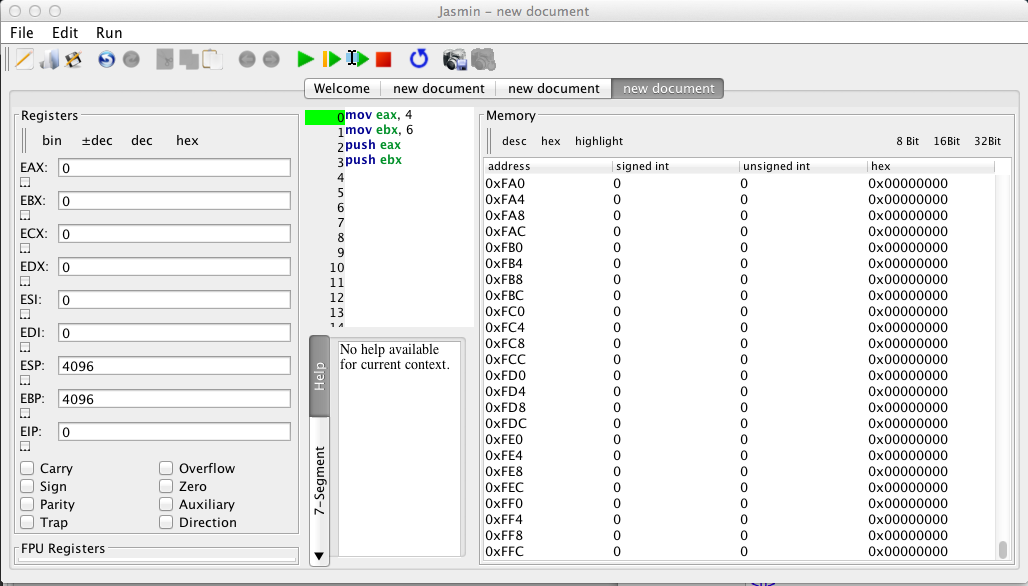
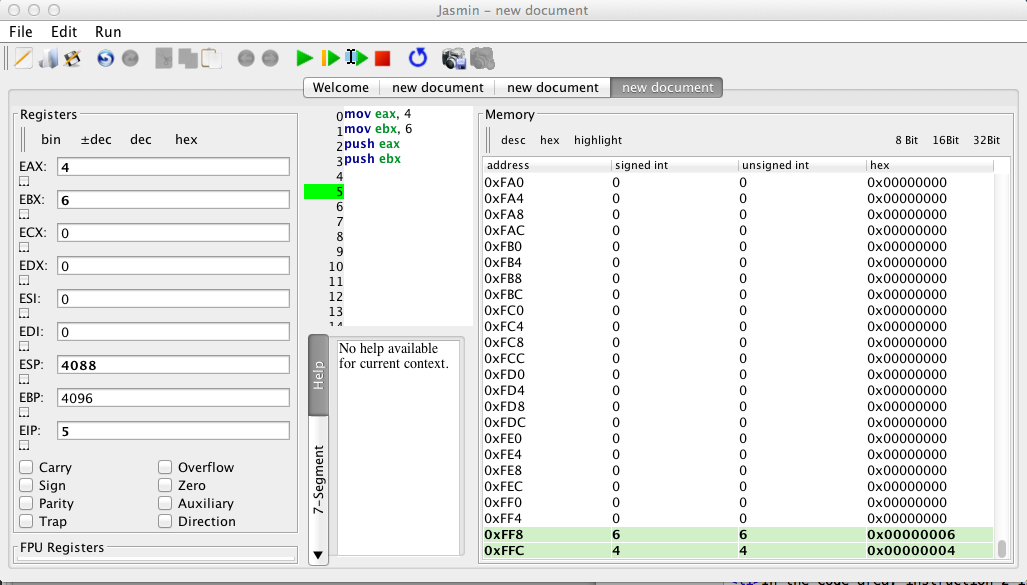
Scroll down in the Memory pane to see the last values. As show above, the last location is at 0xFFC. This value is 32 bits long, so it contains four bytes, at locations 0xFFC, 0xFFD, 0xFFE, and 0xFFF. The ESP points to the next byte, 0x1000.
These instructions move the number 4 into eax, and the number 6 into ebx. Then both values are pushed onto the stack.
Notice these things, as shown below:
mov eax, 4
mov ebx, 6
push eax
push ebx
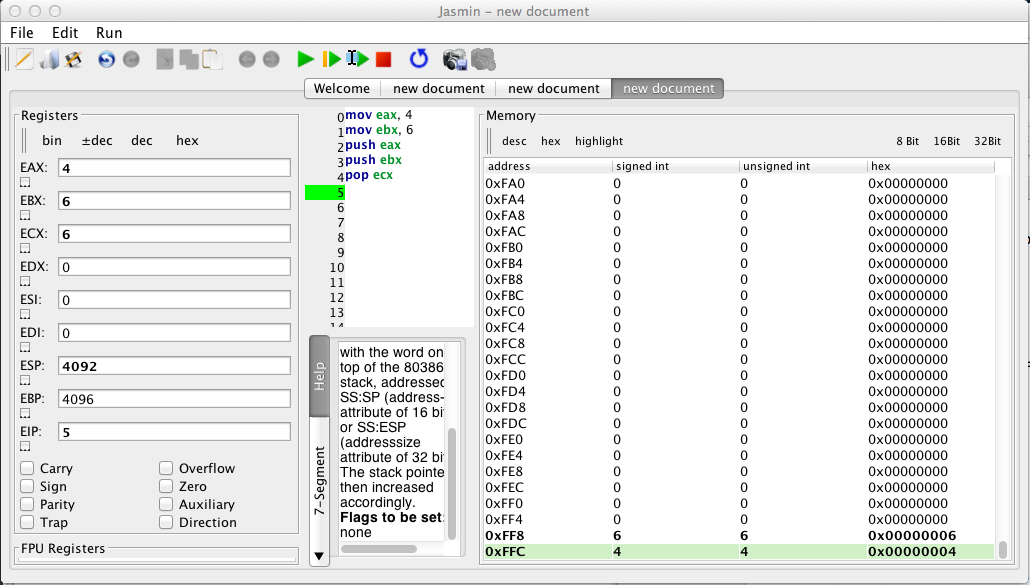
pop ecx
Notice these things, as shown below:
In the Code section, type in these instructions.
mov eax, 1
mov ebx, 2
mov ecx, 3
mov edx, 4
push eax
push ebx
push ecx
push edx
pop eax
pop ebx
pop ecx
pop edx
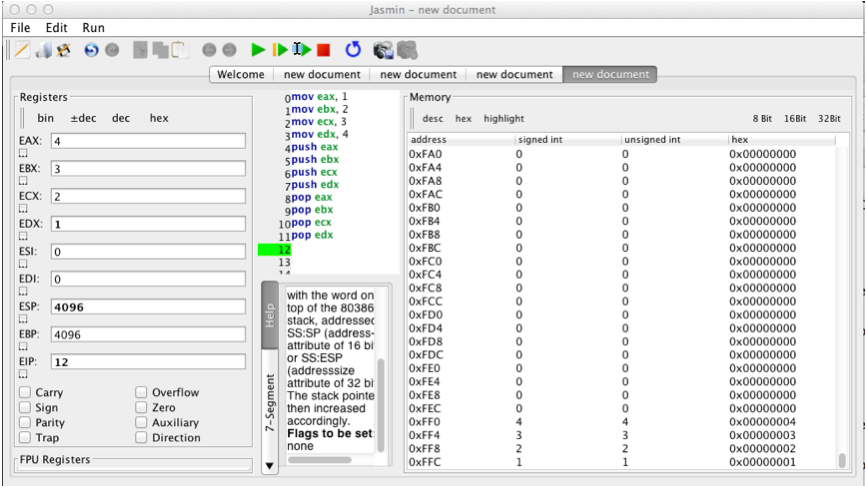
However, since the stack is a FILO (First In, Last Out) structure, this reverses the order of the values.
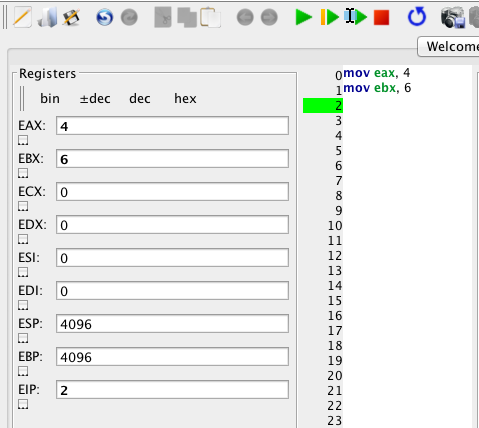
Push the Step four times to execute only the first four instructions, as shown below:
You see the values 1, 2, 3, and 4 loaded into the EAX, EBX, ECX, and EDX registers, as shown below.
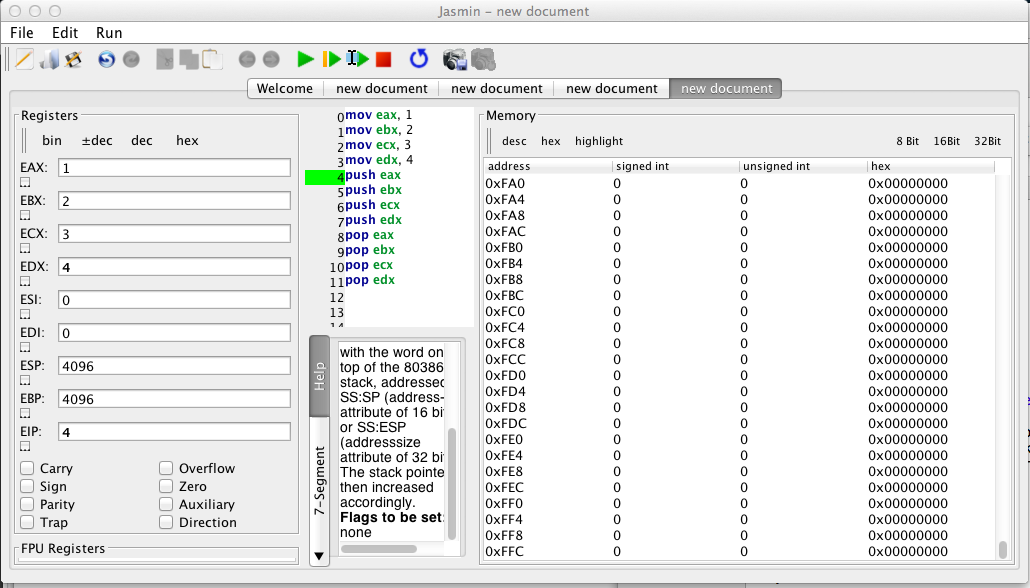
Push the Step four more times to execute only the next four instructions.
You see the values 1, 2, 3, and 4 pushed onto the stack, as shown below.
Push the Step four more times to execute the remaining four instructions.
Now the registers contain these values:
In the top center of the Jasmin window, click the leftmost green arrow to run the code.
In the bottom-center pane of Jasmin, click Console to see the output. The message is mostly 'X' characters, as shown at the bottom of the image below.
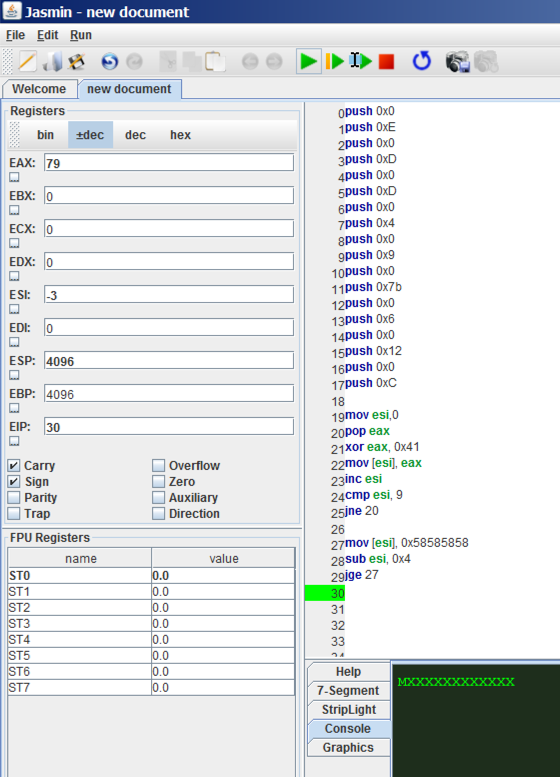
The code loads encrypted values onto the stack, decrypts them to place a secret message in ASCII into memory, and then overwrites the memory with 'X' characters.
Use Jasmin to run the code until it has decrypted the message, but has not erased it yet.
That message is the flag.
In the top center of the Jasmin window, click the leftmost green arrow to run the code.
In the bottom-center pane of Jasmin, click Console to see the output. The console is empty, as shown below.
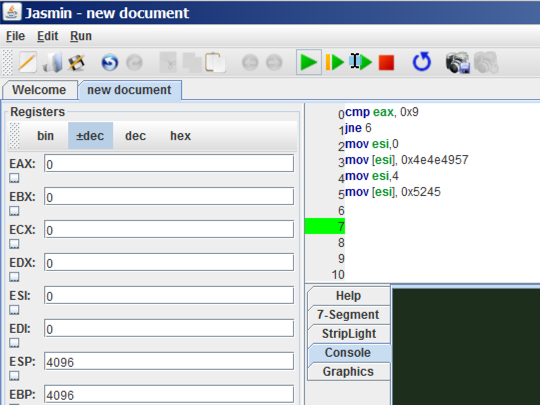
Figure out how to make the message visible. That message is the flag.