PMA 122: PE Headers (50 pts extra)
What you need
Purpose
To examine how EXE files work,
and how the UPX packer modifies them.
Use the FLARE-VM
All these steps are done in your
FLARE-VM, which is Windows 10
plus many malware analysis tools.
Making a Hello Program
From the desktop,
double-click
FLARE,
"Developer Tools",
"Microsoft Visual C++ Build Tools",
"Visual C++ 2015 x86 Native Build Tools Command Prompt".
Execute these commands:
mkdir c:\pe
cd c:\pe
notepad hello.cpp
Enter this source code:
#include <iostream>
using namespace std;
void main()
{
printf("Hello!\n");
}
Save the file.
Execute these commands:
cl /EHsc hello.cpp
hello.exe
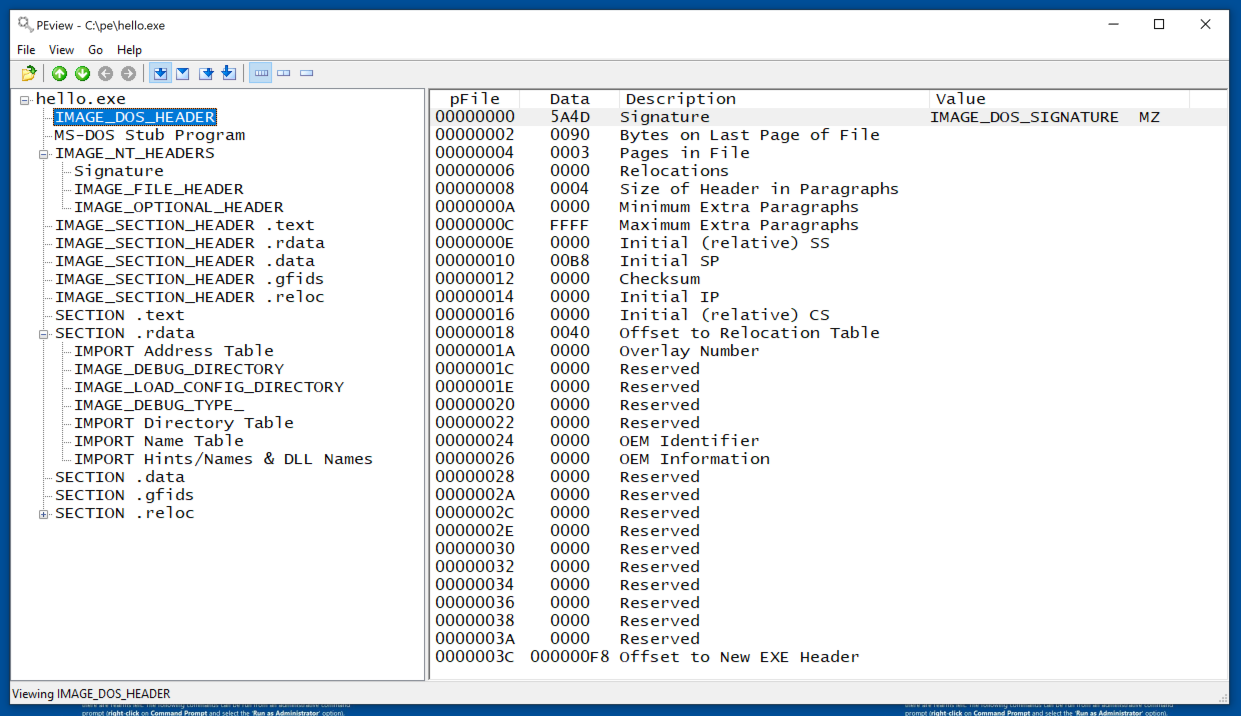
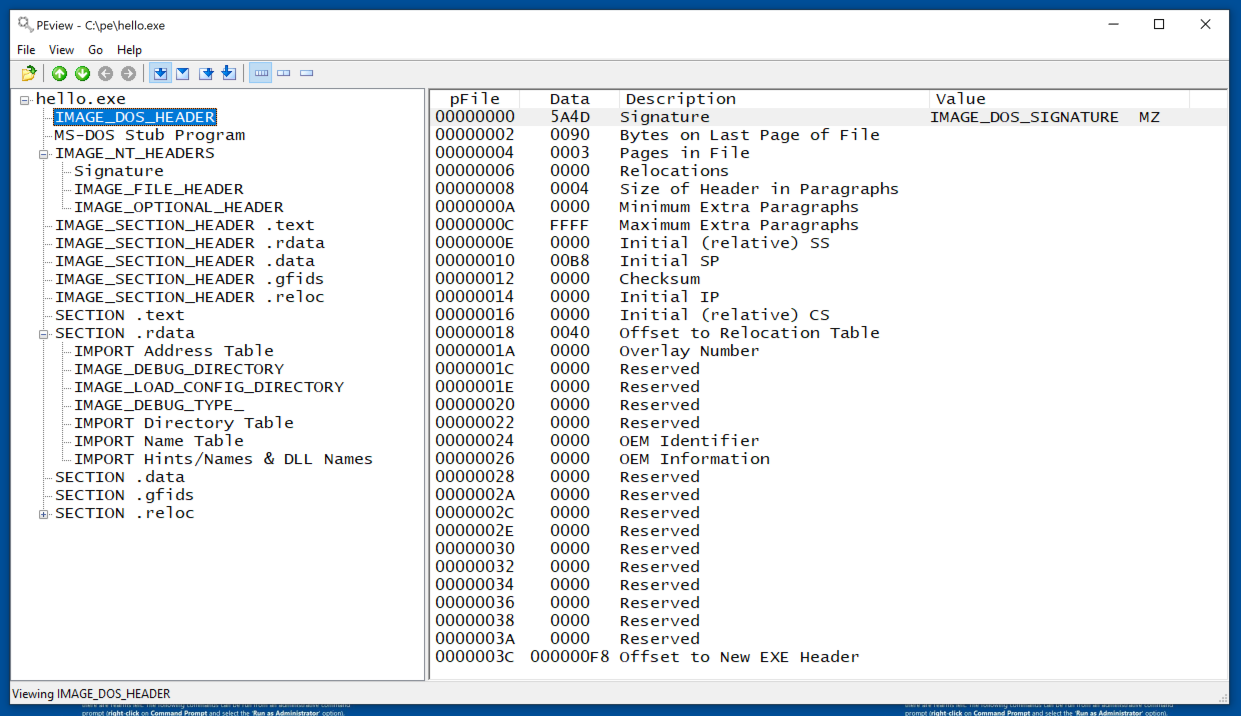
MS-DOS Header
At the lower left of the desktop, click the magnifying glass icon and type PEview. Launch PEview.
Open the C:\pe\hello.exe file in
PEview.
In the left pane, click
IMAGE_DOS_HEADER.
This header is now unused. The
only important features are the
first and last item,
as shown below.
- Signature: 5A4D or MZ -- the start of every PE file
- Offset to new EXE Header: value varies
MS-DOS Stub Program
This program merely prints a message
on obsolete MS-DOS systems and is unimportant
to us.
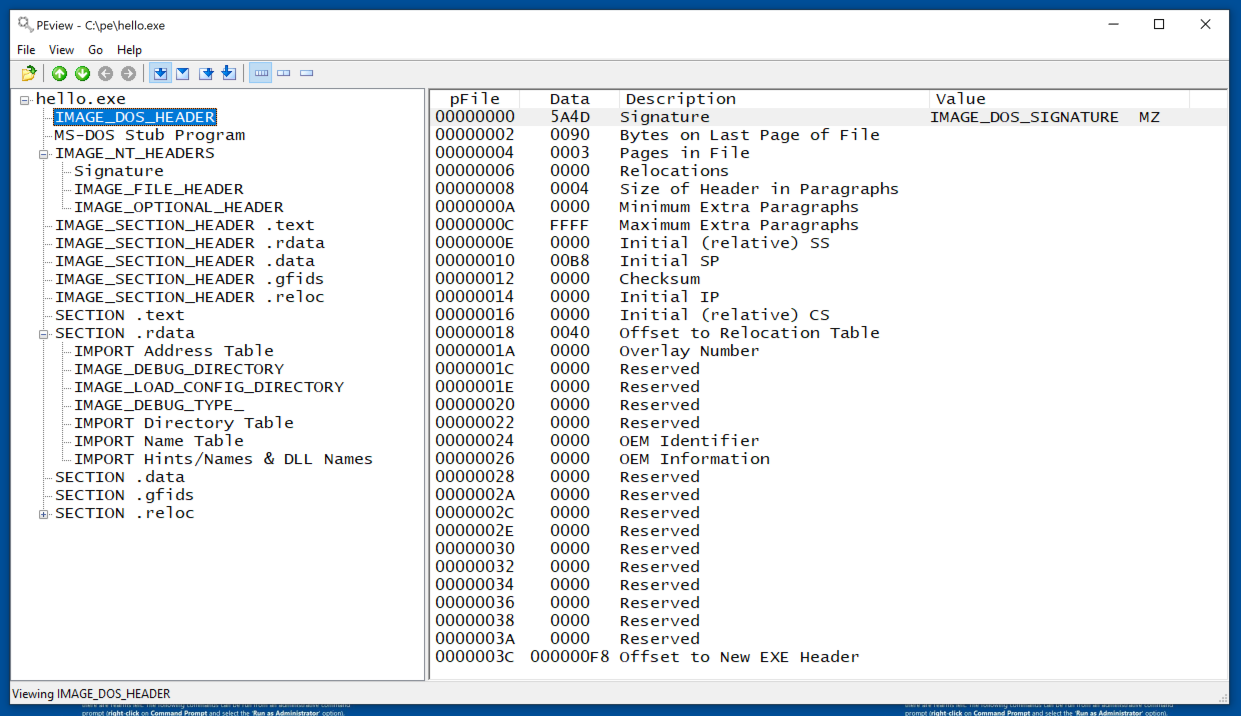
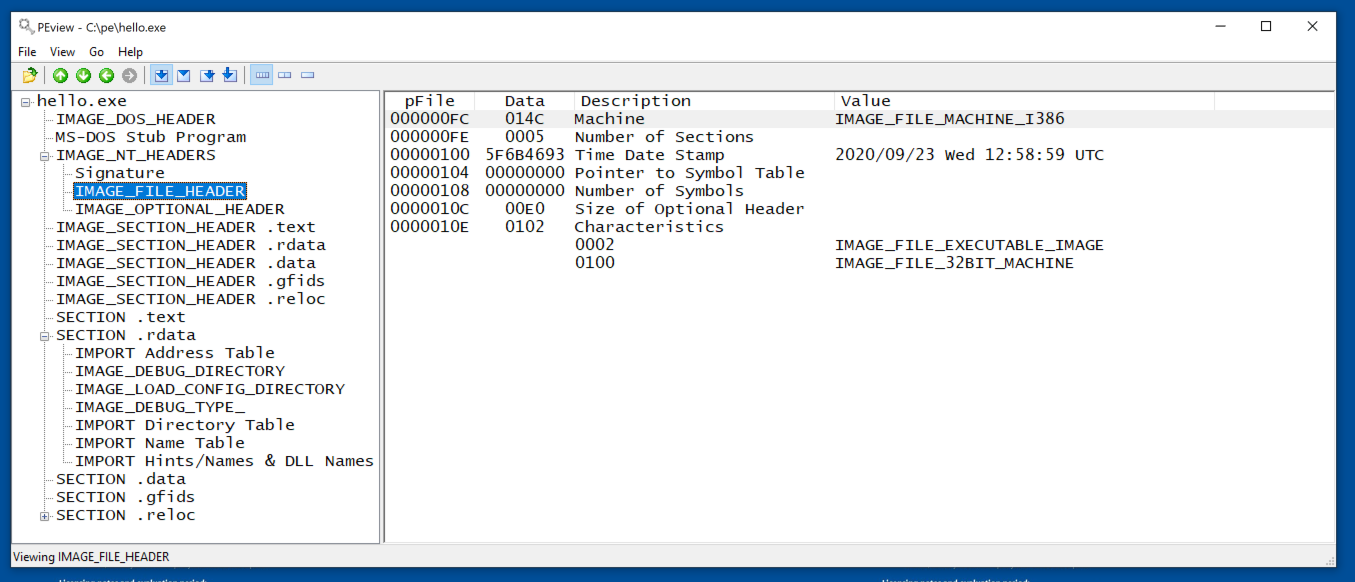
IMAGE_NT_HEADERS
This header is important.
Note these features,
as shown below.
- Signature: PE
- IMAGE_FILE_HEADER: The Time Date Stamp here is useful for attribution
- IMAGE_OPTIONAL_HEADER: this is very important, as detailed below.
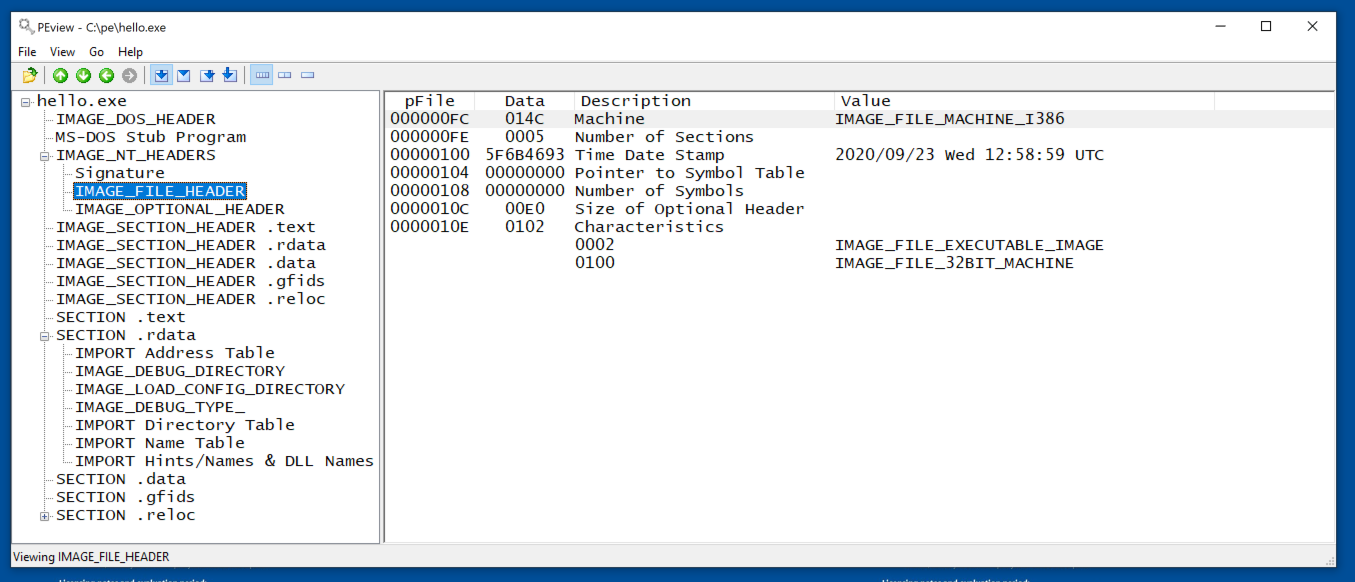
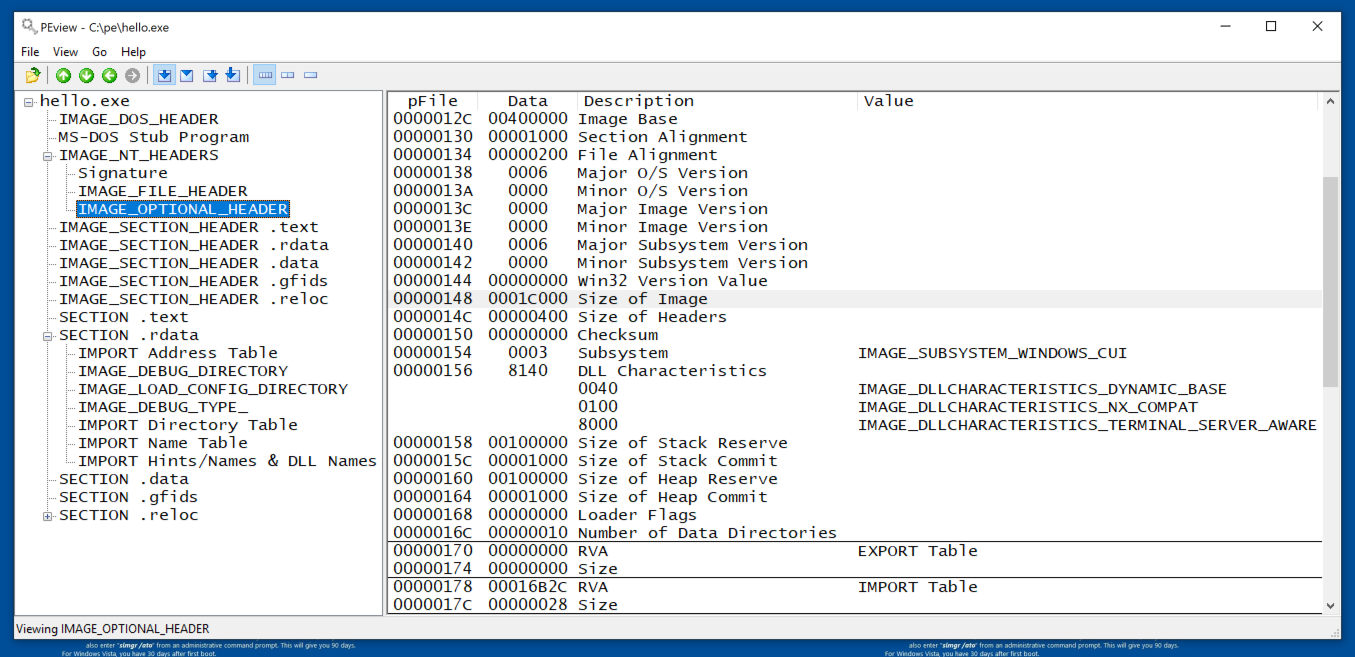
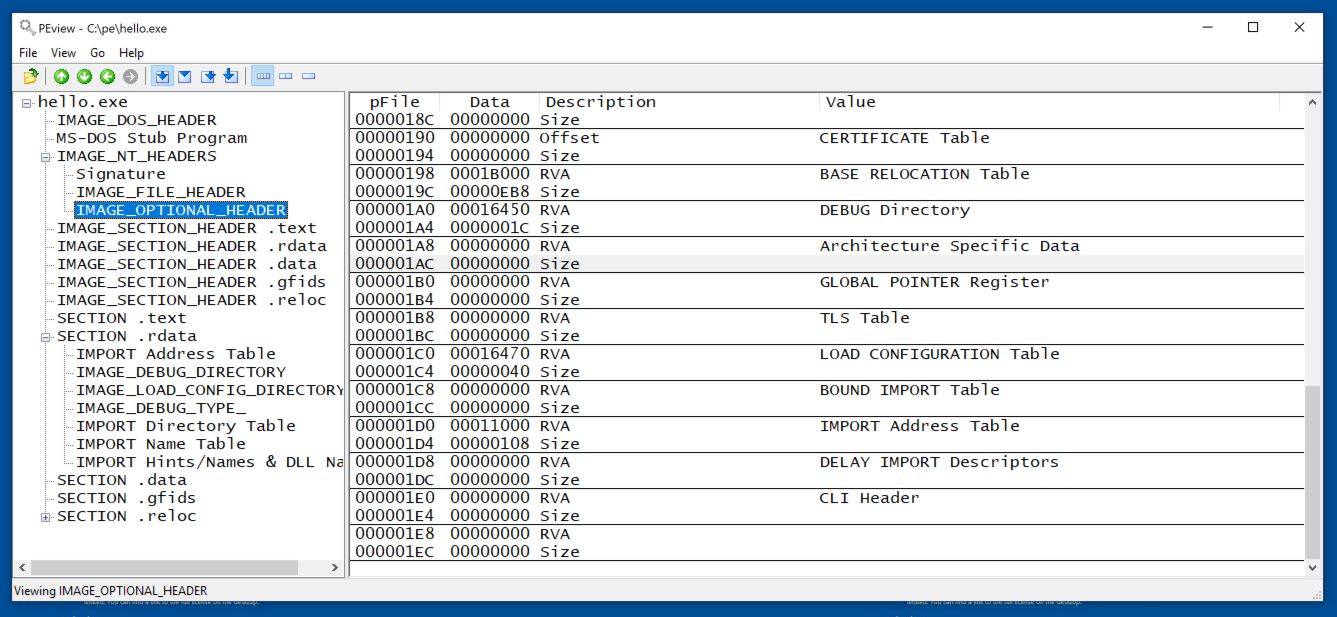
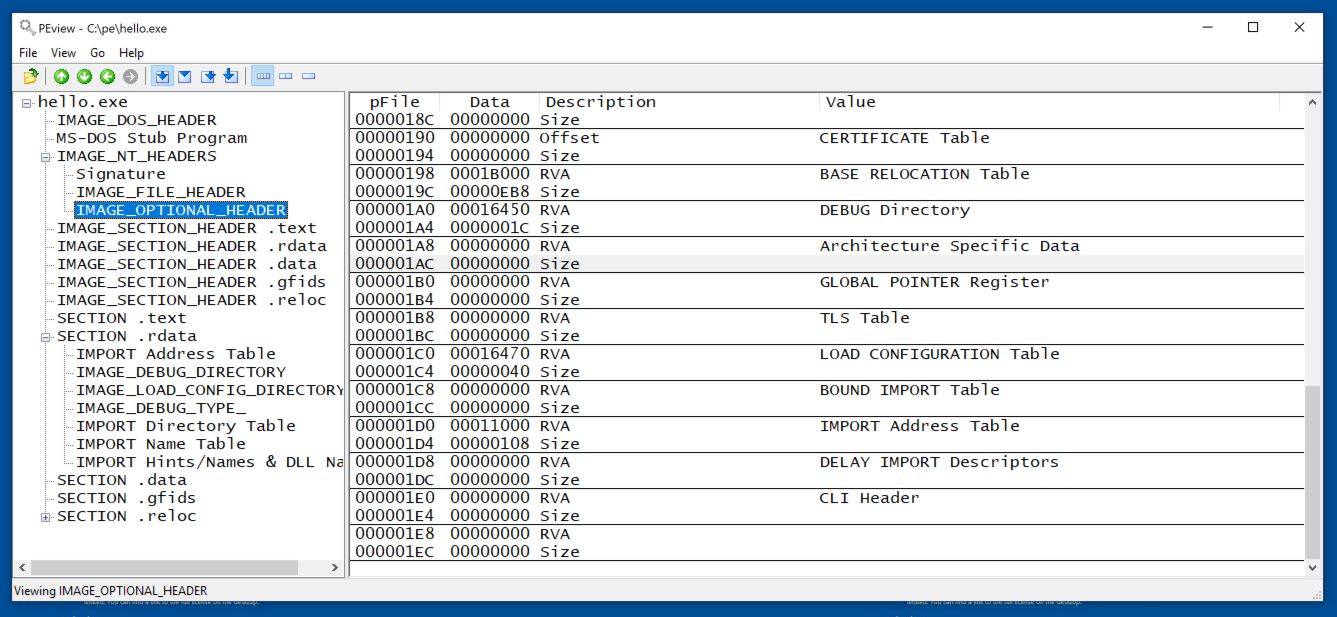
IMAGE_OPTIONAL_HEADER
Note these features,
as shown below.
- Image Base: The preferred RAM location the program will load into, often 400000
- Size of Image: the total size of all sections when loaded into memory
- IMPORT Table: RVA is the Relative Virtual Address, the location of the IMPORT Table relative to the base address of the image. In the image below, the value is 16B2C, which, added to the start of the image 400, results in an address of 16F2C in this file.
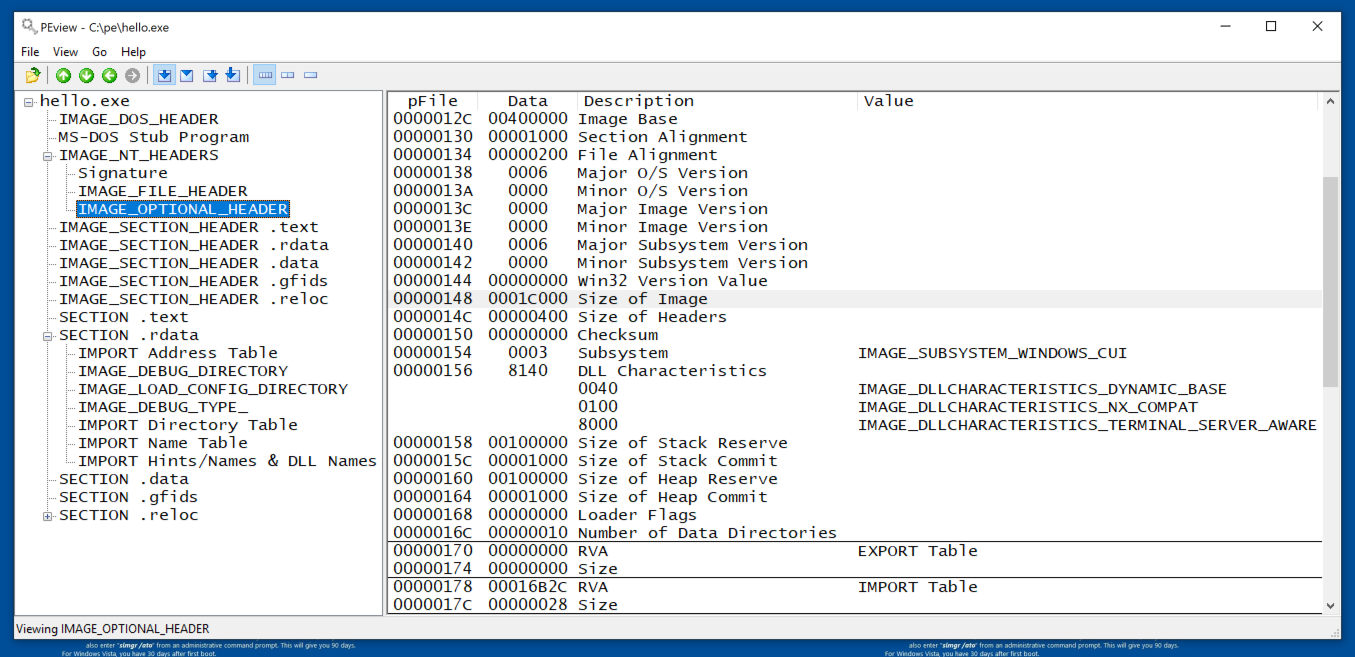
Scrolling down, we see the
Import Address Table, at RVA
11000. As we'll see below, that
matches the start of the .rdata
section.
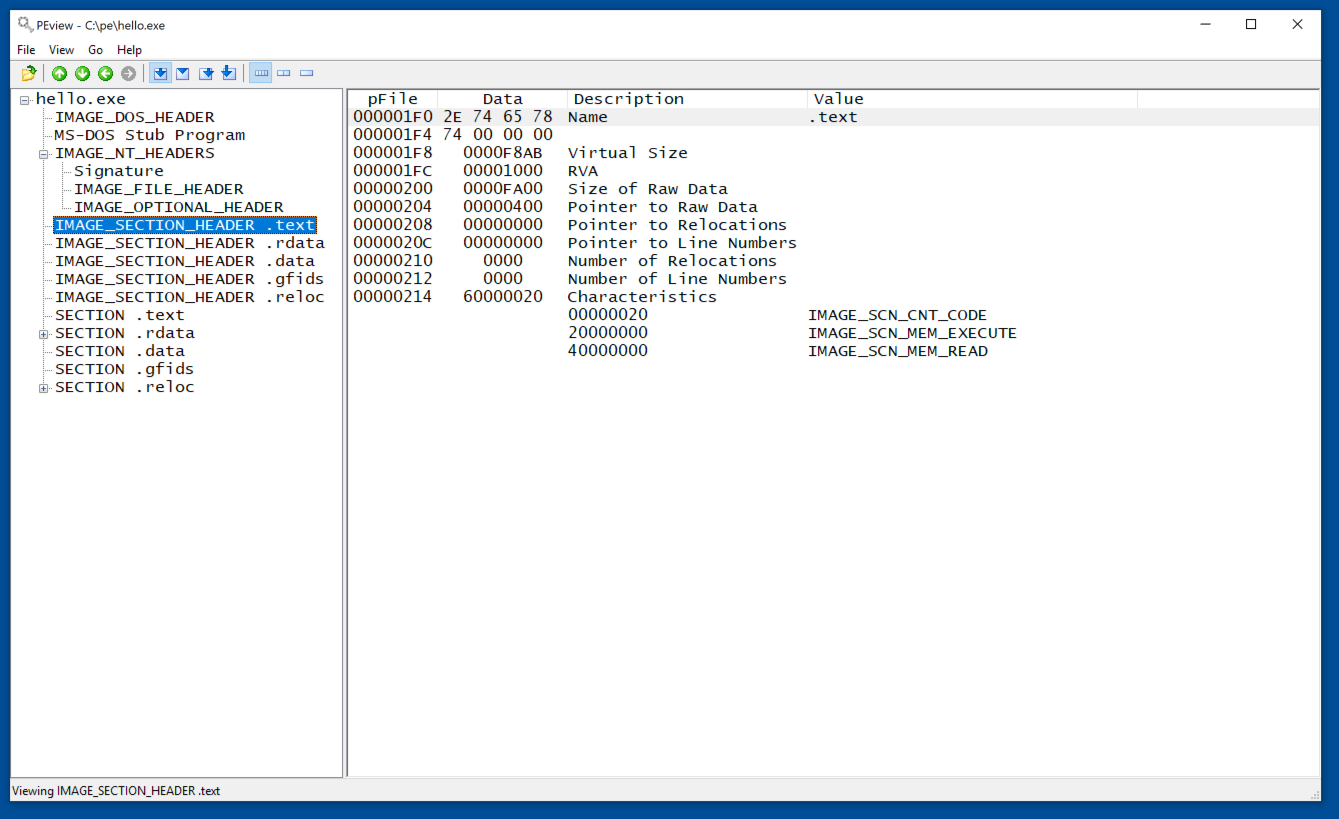
Section Headers
For each section, note these
features,
as shown below.
- Name: Limited to 8 bytes
- Virtual Size: the total size of the section when loaded into memory
- RVA: where the section is loaded into memory, relative to the base address of the image
- Size of Raw Data: size of the section on disk
- Pointer to Raw Data: location of the section within the EXE file
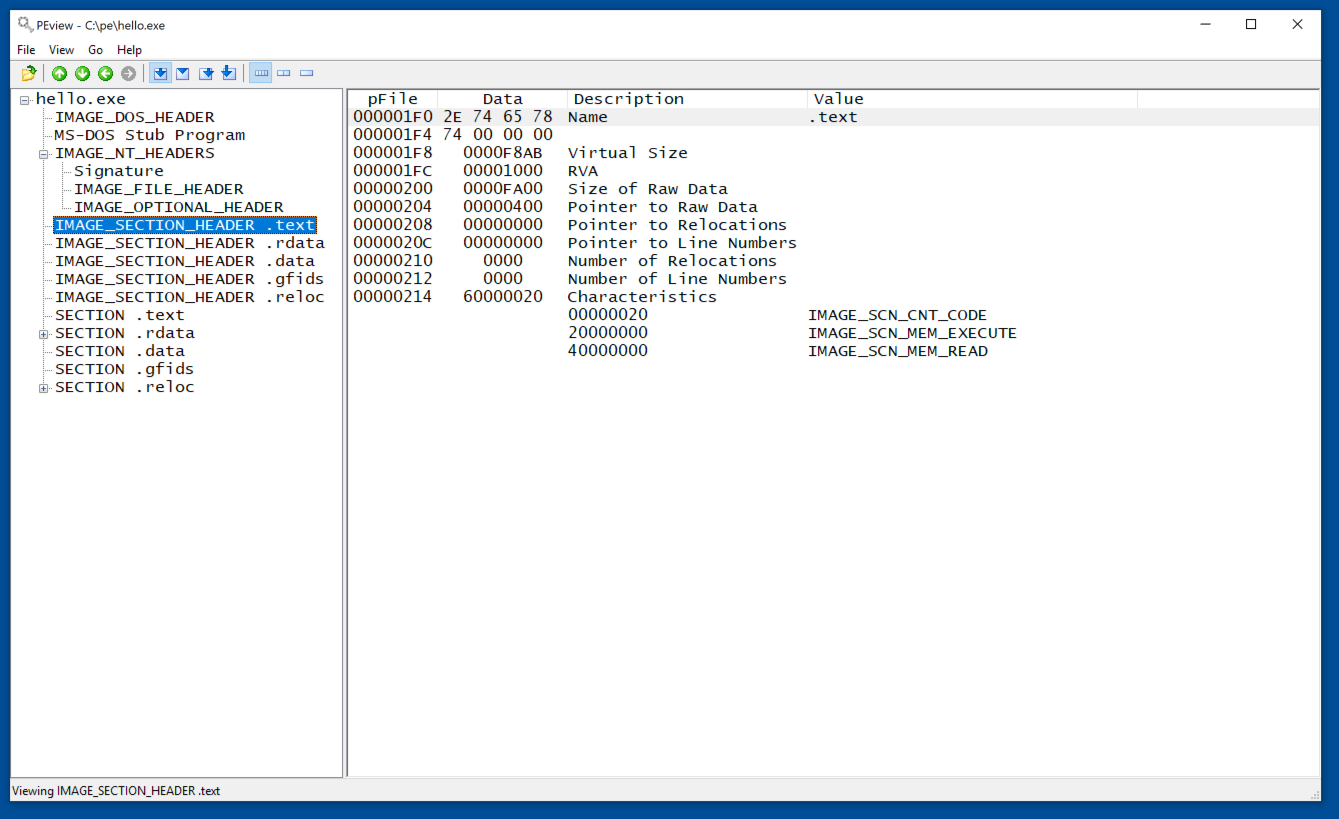
Calculating Memory Layout
Examine each secton in turn and find the RVA
and "Virtual Size" values of each one.
Then you can calculate the actual memory layou\t
of the program, as shown below.
| Section | RVA | Virtual
Size | | Memory Address |
|---|
| Image Base | | | | 400000 |
| .text | 1000 | F8AB | | 401000 |
| .rdata | 11000 | 611E | | 411000 |
| .data | 18000 | 11E0 | | 418000 |
| .gfids | 1A000 | AC | | 41A000 |
| .reloc | 1B000 | EB8 | | 41B000 |
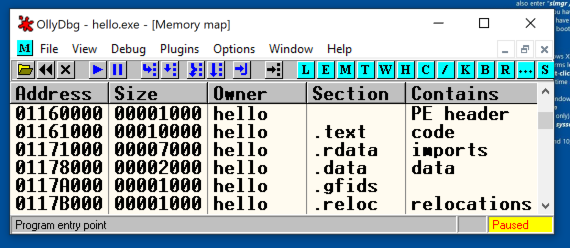
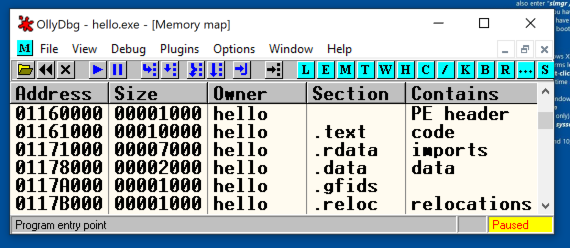
Memory Map
To verify the addresses,
open hello.exe in OllyDbg
and click View,
Memory.
As shown below, the
layout matches the pattern,
although the base address was
not 400000 on my system.
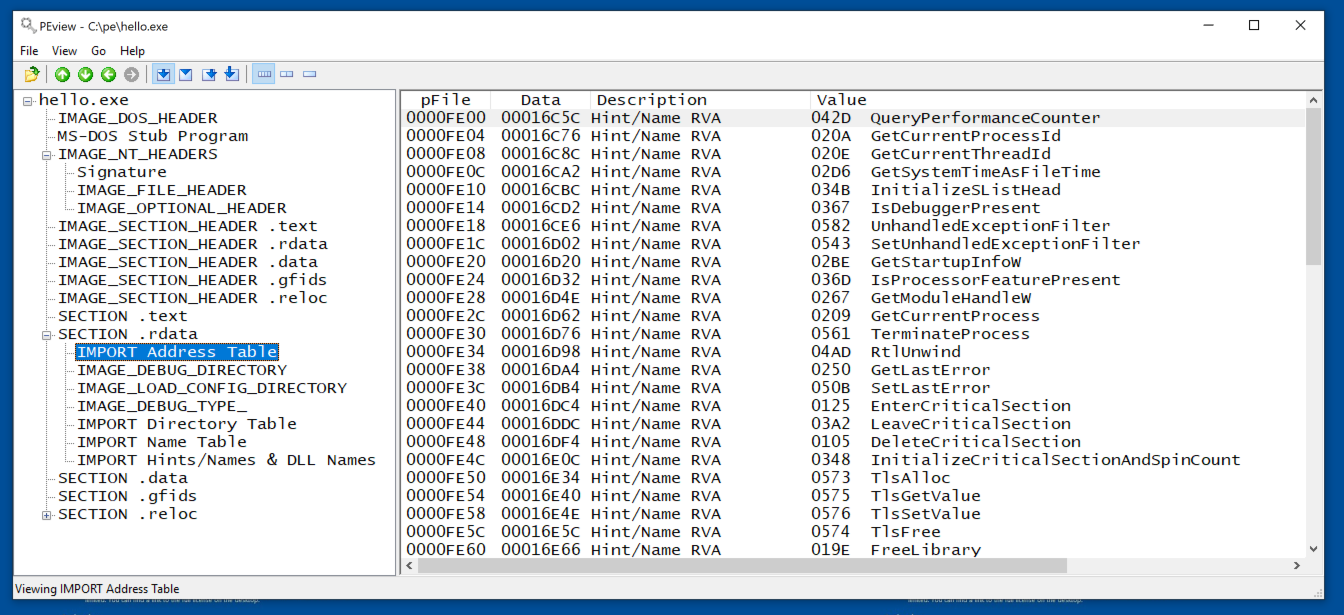
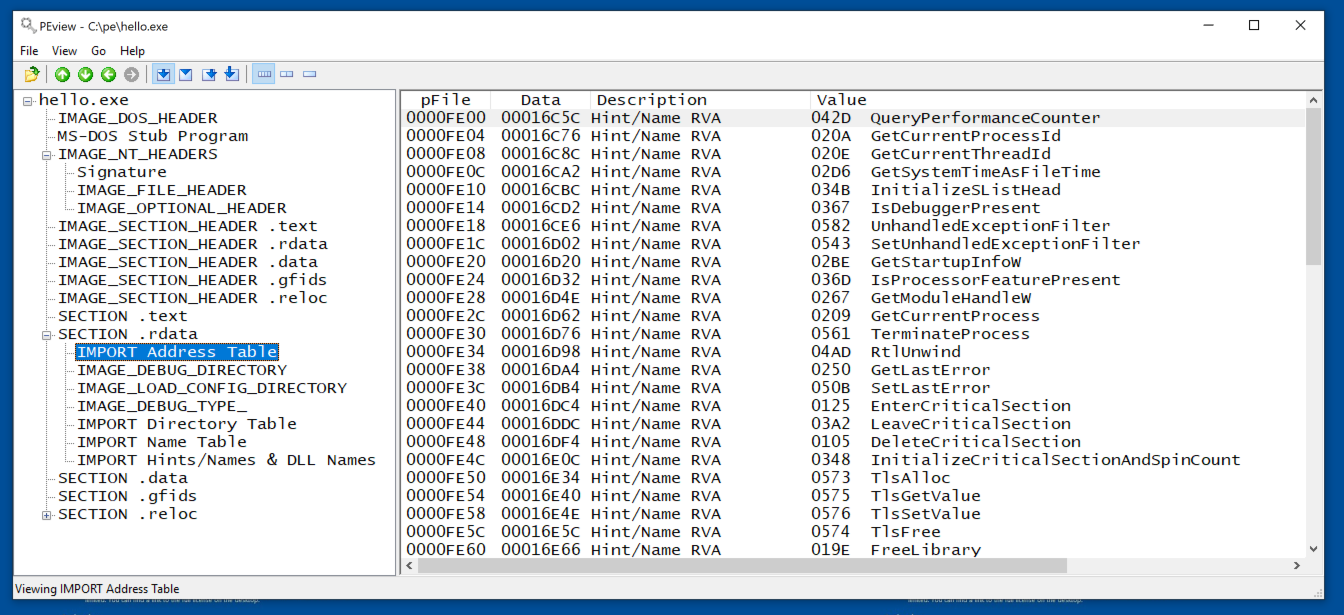
IMPORT Address Table
In the .rdata section,
the first item is the IMPORT
Address Table, starting at
address FE00, as shown below.
PMA 122.1: Missing Section (10 pts)
Download this file:
hello2.exe
Examine that file. It has four sections,
unlike the one we examined above.
What is the name of the missing section?
That's the flag.
|
PMA 122.2: Broken (20 pts)
Download this file:
peflagh.exe
The file is damaged and cannot run.
Fix it and run it to see the flag.
Hint: Use CFF Explorer. Examine the headers.
Invalid fields turn red.
|
PMA 122.3: Broken (20 pts)
Download this file:
peflag2h.exe
The file is damaged and cannot run.
Fix it and run it to see the flag.
Hint: If SmartScreen blocks the file, unblock
it in the file Properties.
|
Sources
PE Format from Microsoft
PE File Format Offsets - by Sunshine
Understanding the Import Address Table
Understanding Import Tables #2 - Manually add imports - by Sunshine
Posted 9-23-2020
SmartScreen hint added 9-29-20
Brackets around iostream HTML-encoded 9-30-20
Hint added to 122.2 9-26-22