
Warning: This exposes your WebGoat machine to network attacks! Only do this with a test machine you are willing to risk, or on a closed network you trust.
On your Windows machine, open your WebGoat folder. Open the Tomcat folder, and the conf folder. Right-click the server_80.xml folder and click Open With..., Notepad, as shown below on this page.

In Notepad, scroll down to find this section:
<!-- Define a non-SSL HTTP/1.1 Connector on port 8080 -->
<!--
<Connector port="8080" maxHttpHeaderSize="8192"
maxThreads="150" minSpareThreads="25" maxSpareThreads="75"
enableLookups="false" redirectPort="8443" acceptCount="100"
connectionTimeout="20000" disableUploadTimeout="true" />
-->
<Connector address="127.0.0.1" port="80" maxHttpHeaderSize="8192"
maxThreads="150" minSpareThreads="25" maxSpareThreads="75"
enableLookups="false" redirectPort="8443" acceptCount="100"
connectionTimeout="20000" disableUploadTimeout="true"
allowTrace="true" />
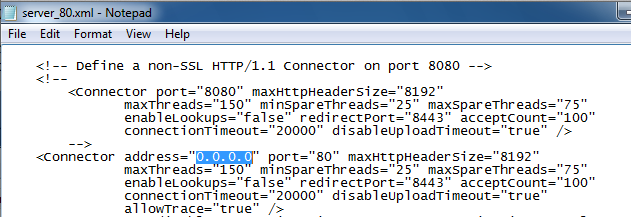
In Notepad, click File, Save. Close Notepad.
Go back to the WebGoat-5.3_RC1 folder and double-click the webgoat.bat file. Webgoat starts.
Click Start, type in CMD, and press Enter. In the Command Prompt window, type IPCONFIG and press Enter. Find the IP address for your "Local Area Connection".
In the Windows machine, open a browser and go to
http://192.168.198.129/WebGoat/attack
Note: Some versions of WebGoat don't use the capital letters, so if that doesn't connect, try this URL instrad:Use your machine's IP address, not the exact address 192.168.198.129. A login box should pop up--log in with username guest and password guesthttp://192.168.198.129/webgoat/attack
You should see the Webgoat page shown below.
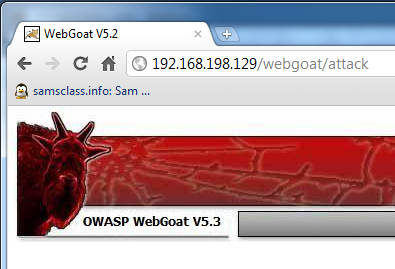
On your Linux machine, open a Web browser and go to
http://192.168.198.129/WebGoat/attackUse your machine's IP address, not the exact address 192.168.198.129.
You should see the same login screen, and the Webgoat page. If you do not, you have a problem with the networking between the machines. Try shutting off the Windows firewall, make sure you can PING from one machine to the other, and check your virtual network settings. Webgoat must be visible from the Linux machine before you can scan it.
root with password toor
startx
On your Linux machine, in a Terminal window, execute this command:
If it fails to install, and gives you this error message:apt-get install libssl-dev
The following packages have unmet dependencies:Execute these commands to get libssl-dev:
libssl-dev: Depends: libssl0.9.8 (= 0.9.8k-7ubuntu8.6) but 0.9.8k-7ubuntu8.8 is to be installed
E: Broken packages
On your Linux machine, in a Terminal window, execute these commands (note that libidn11 ends in the number eleven, not two lowercase L's):wget http://samsclass.info/125/proj11/libssl-dev_0.9.8k-7ubuntu8.8_i386.debdpkg -i libssl-dev_0.9.8k-7ubuntu8.8_i386.deb
apt-get install libssl-dev
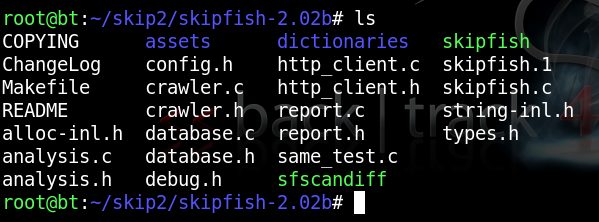
You should see several files in the directory, as shown below:apt-get install libidn11-dev
mkdir skipfish
wget http://skipfish.googlecode.com/files/skipfish-2.02b.tgz
tar xzf skipfish-2.02b.tgz
cd skipfish-2.02b
make
ls
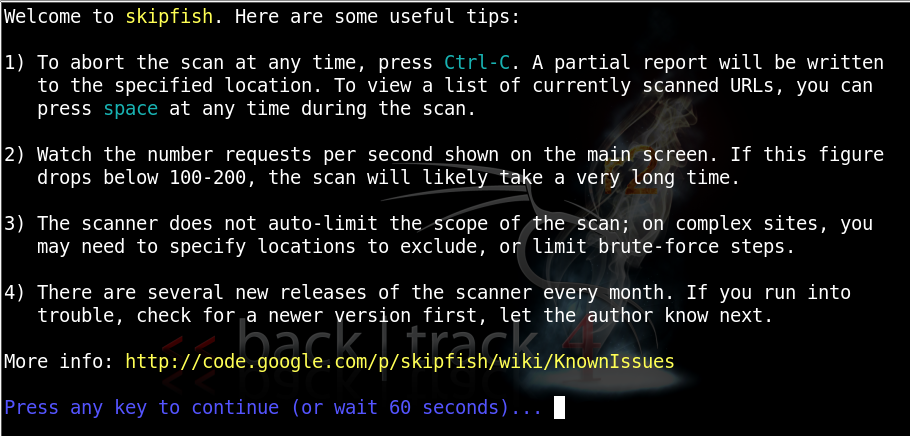
In the Terminal window, execute this command:
cp dictionaries/minimal.wl skipfish.wl
./skipfish -o /tmp/skip1 -A guest:guest -m 5 -LVY -X -u "http://192.168.5.93/WebGoat/attack"
Replace the IP address with the real address of your WebGoat target machine.
Note: each time you run Skipfish, you must specify a new directory for output (-o). If you run it again, use /tmp/skip2, etc.
When Skipfish starts, you will see this screen:
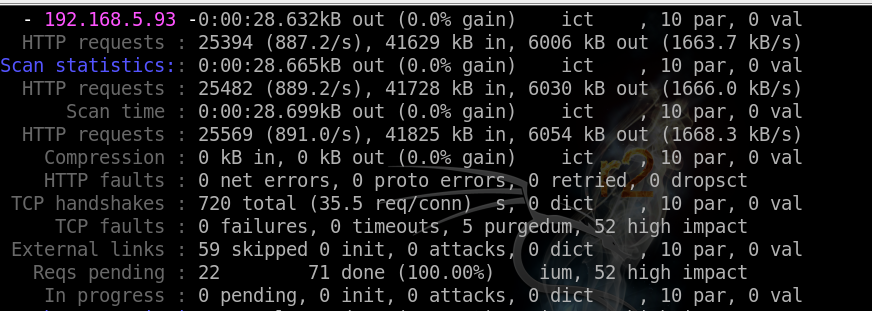
While it is running, you will see messages like this:
When it finishes, you will see this:
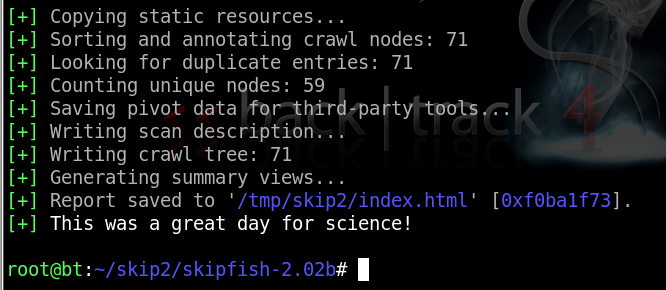
/tmp/skip3/index.html
At the top, a summary appears, showing counts of vulnerabilities with colored dots. The red dot indicates the most dangerouos problems:
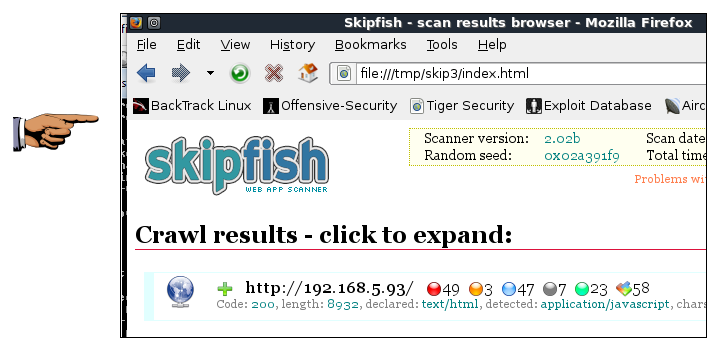
Save this screen shot with a filename of Proj 13 from Your Name.
Email the image to cnit.120@gmail.com with a subject of "Project 13 from YOUR NAME".
Scroll down to see a more detailed list:
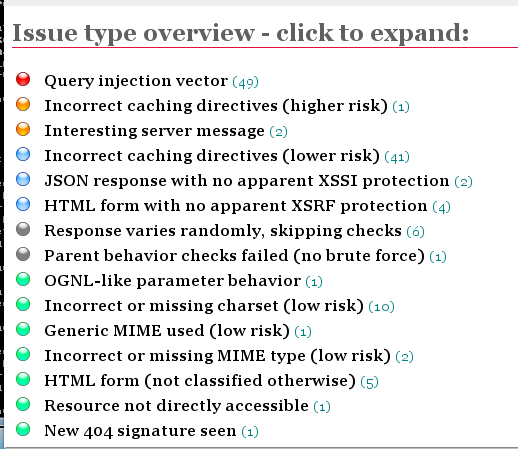
Click the red item to expand it, showing each URL tested, and the exact test that was performed:
