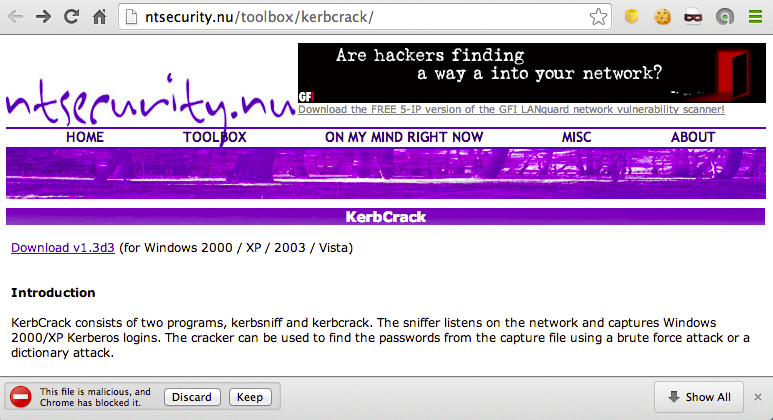
http://ntsecurity.nu/toolbox/kerbcrack/
By the way, Chrome called that file "Malicious":
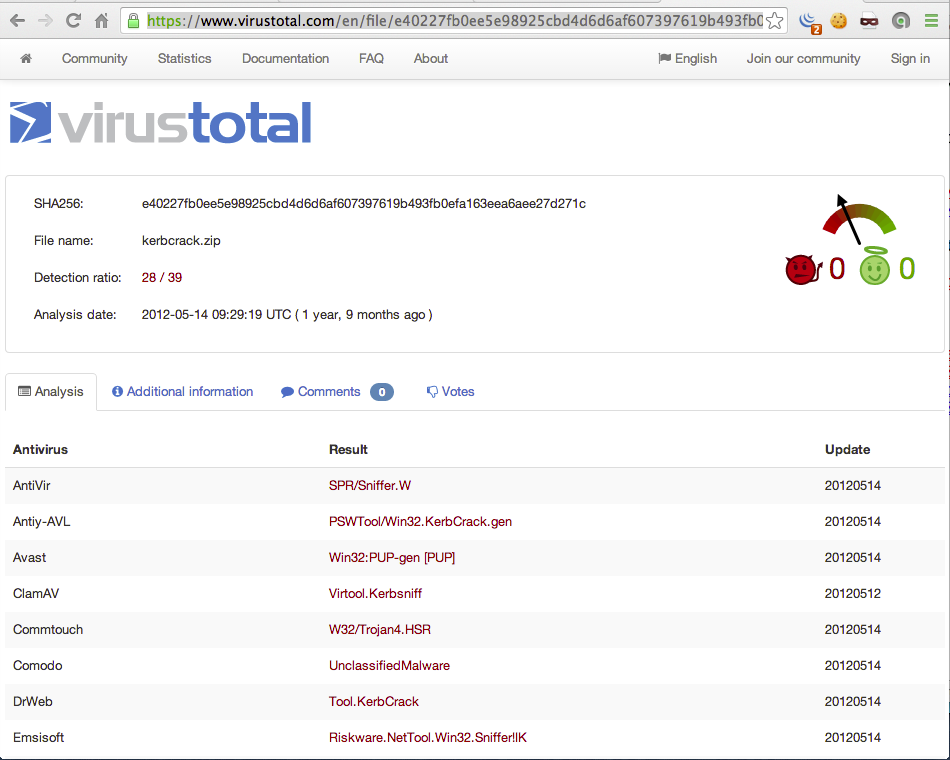
But virustotal shows that it is just detected as a hacking tool, not malware that does any additional harm.
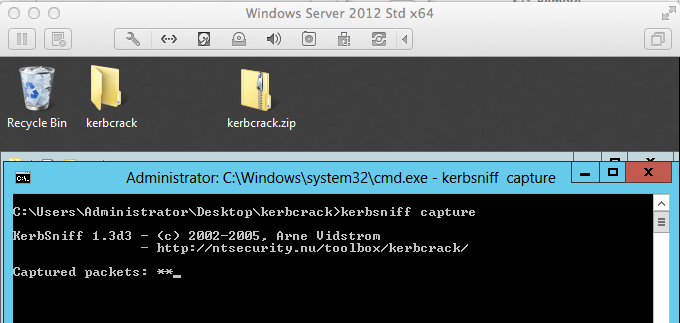
I put KerbCrack on my domain controller and unzipped it.
I started kerbsniff sniffing:
I then tried logging in to my Windows Server 2012 domain from a Win 8.1 client, but kerbsniff didn't pick anything up.
The KerbCrack documentation says it works for Win 2000 and XP, so I booted up a Windows XP VM and joined the domain.
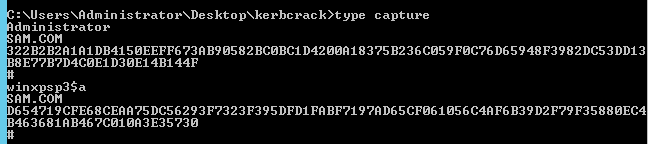
That worked! Kerbsniff captured two hashes (perhaps these are not exactly hashes, but pre-authentication encrypted timestamps; I'm not sure exactly what KerbCrack uses):
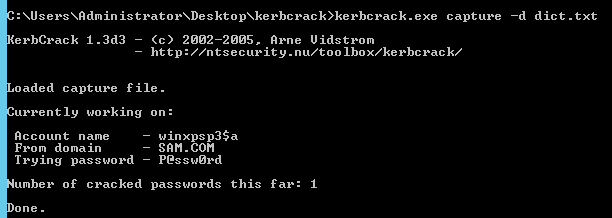
And when I ran them against a dictionary containing the correct password, the password was cracked.