This makes it possible to recover the contents of files even after the directory information for them is lost, often by reformatting the disk. The filenames cannot be recovered by this technique, but the file contents can.
And it's outrageously easy to use. Simply invoking Foremost with no options looks for all possible file types and puts the files it finds in a folder named "output".
cd
cd Desktop
curl https://samsclass.info/121/proj/p15.zip > p15.zip
unzip p15.zip
If there is one, right-click it and click "Move to Trash".
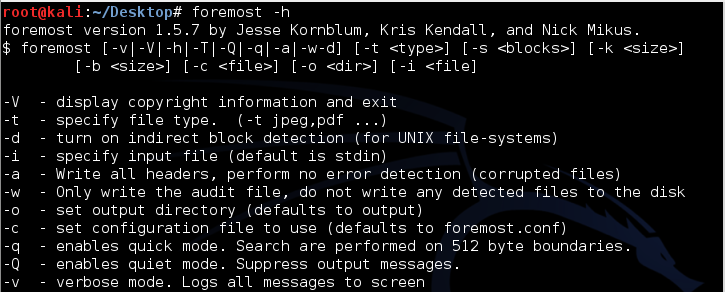
foremost -h
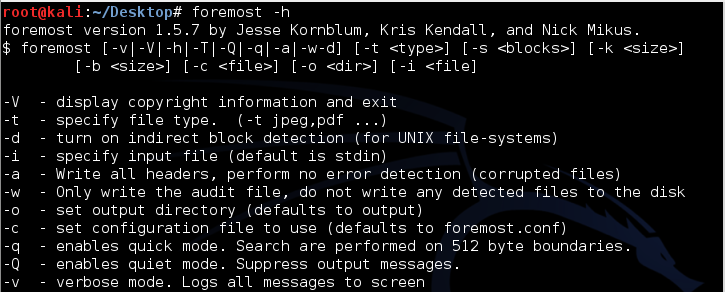
foremost p15.dd
That's it. Close or minimize your Terminal window.
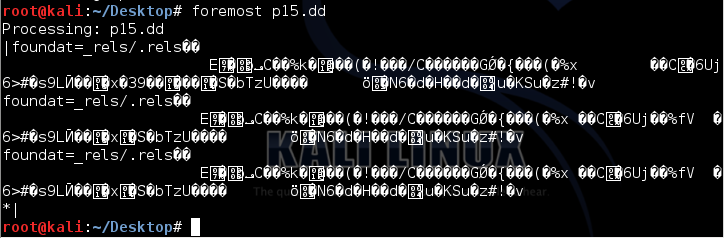
An "output" window opens, containing three items, as shown below.
The "jpg" and "zip" folders contain the recovered files, and the audit.txt file contains a list of all files recovered.
Double-click the audit.txt file.
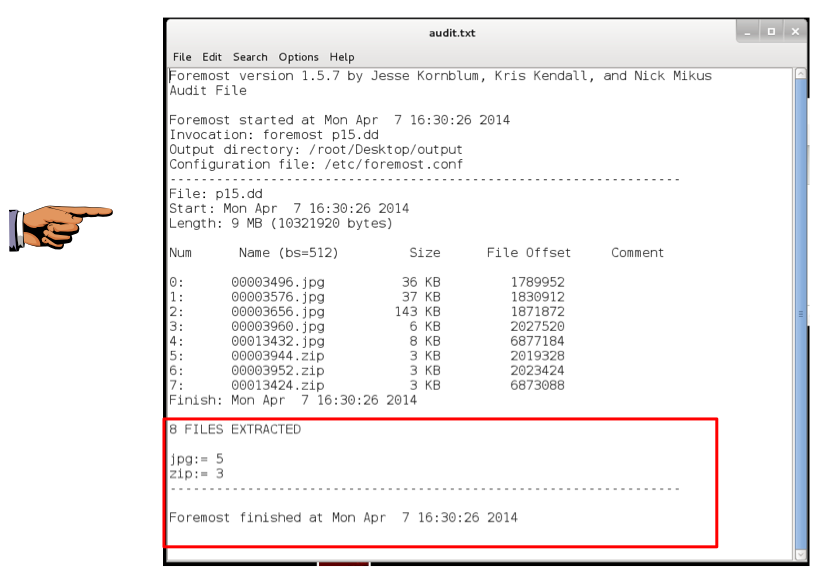
A list of the recovered files appears, as shown below.
Resize or scroll the window to show this text (your date and time will be different):
8 FILES EXTRACTED
jpg:= 5
zip:= 3
------------------------------------------------------------------
Foremost finished at Mon Apr 7 16:30:26 2014
Click on your host system's taskbar to make it the active system.
Press the PrintScrn key in the upper-right portion of the keyboard. That will copy the whole desktop to the clipboard.
YOU MUST SUBMIT A FULL-SCREEN IMAGE TO GET FULL CREDIT!
Open Paint and paste in the image.
Save the image with the filename "Your Name Proj 16a". Use your real name, not the literal text "Your Name".
In the "output" window, double-click the jpg folder.
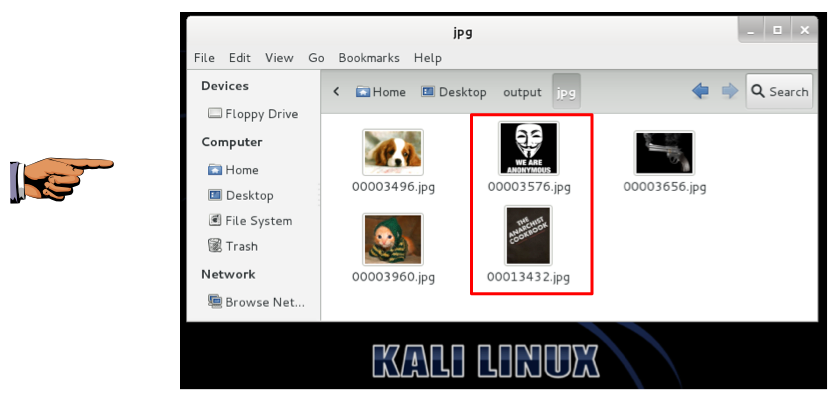
You should see five images, as shown below.
Notice that the images were recovered, but not the filenames--all the files have numerical names now.
Foremost recovered two files that ProDiscover did not--a Guy Fawkes mask, and an image of the "Anarchist Cookbook".
Click on your host system's taskbar to make it the active system.
Press the PrintScrn key in the upper-right portion of the keyboard. That will copy the whole desktop to the clipboard.
YOU MUST SUBMIT A FULL-SCREEN IMAGE TO GET FULL CREDIT!
Open Paint and paste in the image.
Save the image with the filename "Your Name Proj 16b". Use your real name, not the literal text "Your Name".
In the "output" window, double-click the zip folder.
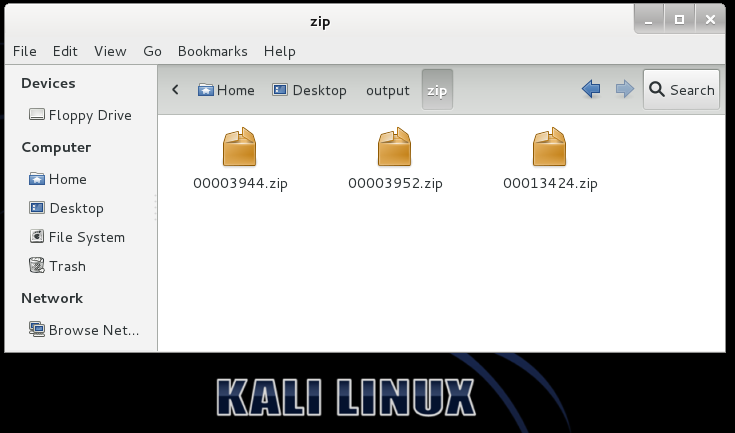
You should see three files, as shown below.
These files were recovered as ZIP files, because that's how Microsoft's XML files are structured.
Double-click one of the recovered ZIP files. Kali Linux can't open it.
The easiest way to view these files is to install LiberOffice on Kali.
In a Terminal window, execute this command:
rm -rf /var/lib/apt/lists
apt-get update
apt-get install kali-archive-keyring
apt-get install libreoffice -y
Right-click one of the Zip files and click Rename. Change the file extension to DOCX and press the Enter key.
Repeat the process for the other two ZIP files.
Double-click each of the DOCX files to open it in Libre Office Writer.
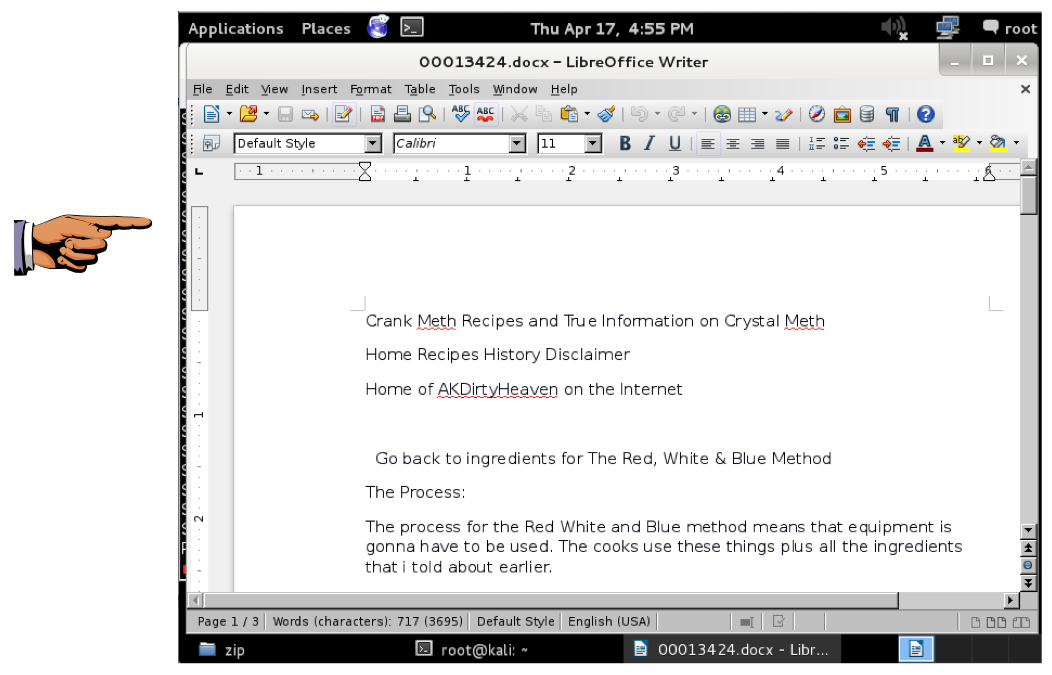
Two of the files are the ones ProDiscover found--the Hacker's Manifesto and the Bill of Rights.
Find the third file--a recipe for making Crank Meth, as shown below.
Press the PrintScrn key in the upper-right portion of the keyboard. That will copy the whole desktop to the clipboard.
YOU MUST SUBMIT A FULL-SCREEN IMAGE TO GET FULL CREDIT!
Open Paint and paste in the image.
Save the image with the filename "Your Name Proj 16c". Use your real name, not the literal text "Your Name".
Last Modified: 4-13-15