Once the USB drive has been recognized, eject it and remove it.
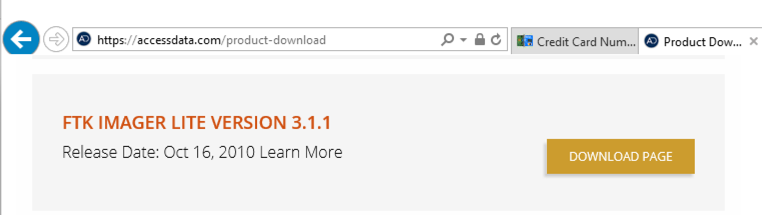
Expand the FTK Imager" section and scroll down to "FTK IMAGER LITE VERSION 3.1.1". Click the "DOWNLOAD PAGE" button, as shown below.
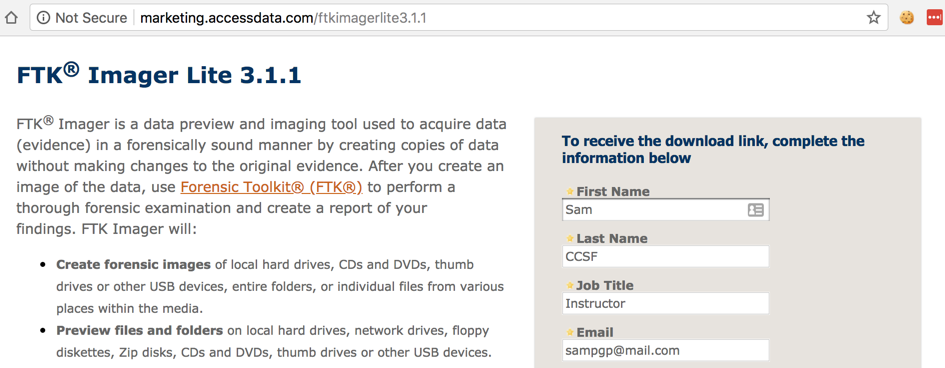
Fill in a form with your name and contact information, and a working email address, as shown below If you need a temporary email address, make one at "mail.com".
Open your email to download the file. Save the FTK Imager file in your Downloads folder.
https://ericzimmerman.github.io/
Click "Registry Explorer/RECmd Version 1.0.0.2", as shown below.
Open the Downloads folder.
Right-click RegistryExplorer_RECmd.zip, click "Extract All...", Extract. (Note: the download page says we should use 7-zip, but it seems unnecessary for this program.)
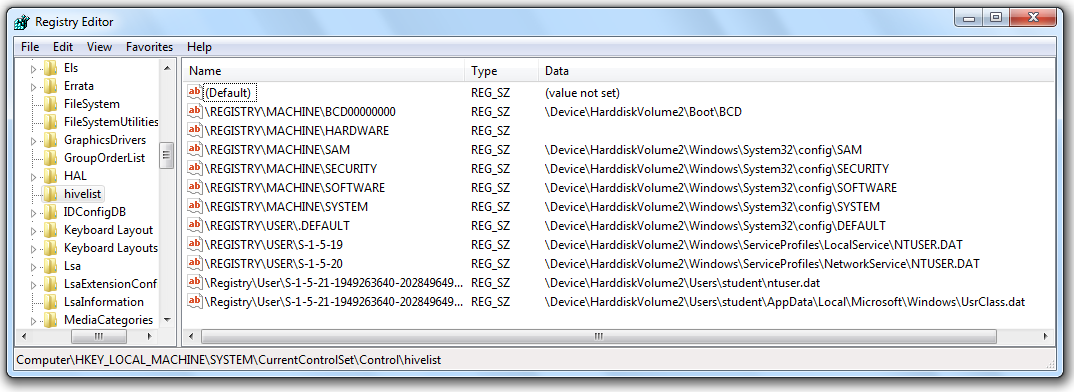
In Registry Editor, navigate to
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\HiveList
You should see a list of the files that store the Registry, as shown below. For this project, we want to capture those files, and not all the other files on the disk. FTK Imager will make that really easy!
If you haven't already extracted Imager Lite, right-click the "Imager_Lite_3.1.1.zip" file and click "Extract All...". In the 'Extract Compressed (Zipped) Folders" box, clck Extract.
In the "Imager_Lite_3.1.1" window, double-click the "FTK Imager.exe" file.
If a "Open File - Security Warning" box pops up, click OK.
If a "User Account Control" box pops up, click Yes.
In the "AccessData FTK Imager 3.1.1" window, click File, "Obtain Protected Files".
The "Obtain System Files" box opens. Notice the Warning at the top of this box. You are obtaining data from your own computer, not from an evidence image. At least one forensic examiner actually went to court and submitted data accidentally gathered from his own forensic workstation by ignoring this warning.
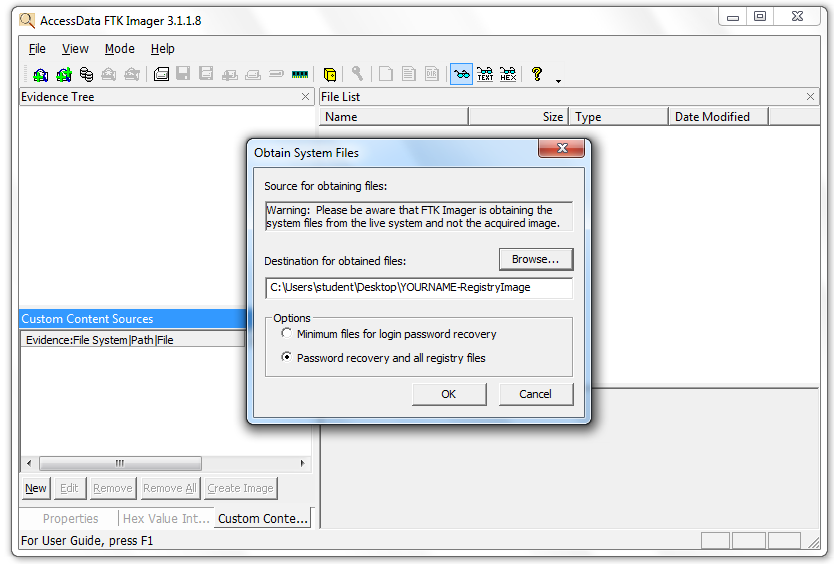
In the "Obtain System Files" box, click the Browse button and navigate to your desktop. Click the "Make New Folder" button, and name the new folder RegistryImage. Select the RegistryImage folder and click OK.
Click the "Password recovery and all registry files" radio button, as shown in the image above. Click OK.
Wait until the process finishes. It should only take a few seconds. Close FTK Imager.
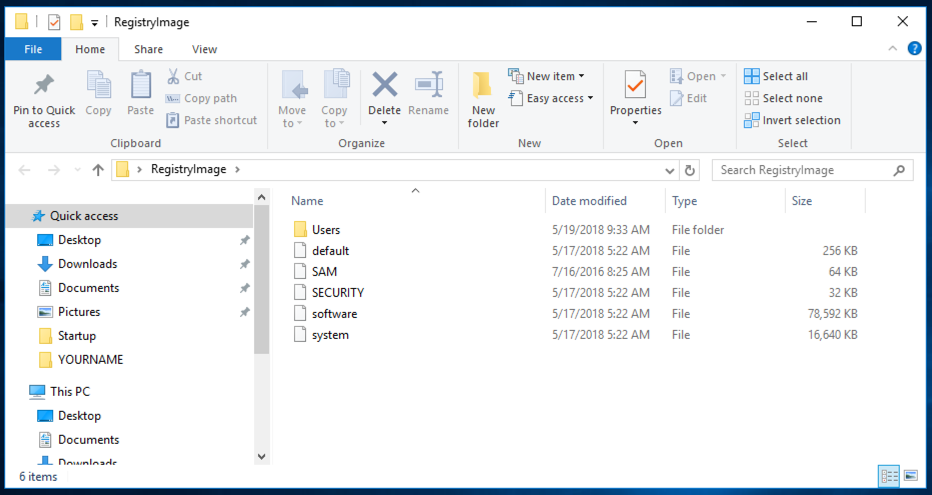
On your desktop, open the RegistryImage folder. It should contain the five files and one folder shown below. You should get used to seeing these names--they are the Hive Files, and a lot of forensics involves working with them.
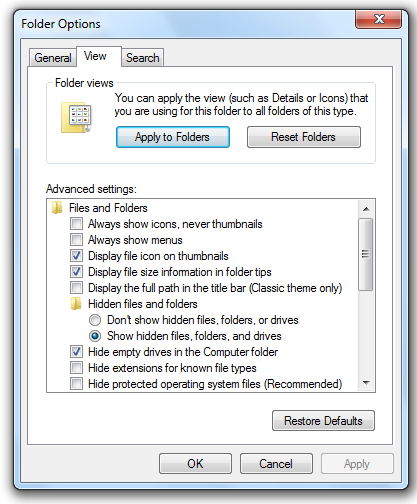
In the "Folder Options" box, on the View tab, click the "Show hidden files, folders, and drives" button and clear the "Hide protected operating system files (Recommended)" box, as shown below.
If a "Warning" box pops up, click Yes.
In the "Folder Options" box, click OK.
Click Start, "File Explorer".
Open the Downloads folder.
Open the RegistryExplorer_RECmd folder and double-click RegistryExplorer.
In Registry Explorer, click File, "Load Offline Hive". Navigate to your Desktop, and open this file:
RegistryImage\Users\Administrator\NTUSER.DAT
If a box pops up titled "Dirty hive detected!", click No.
If a box pops up titled "Load dirty hive?", click Yes.
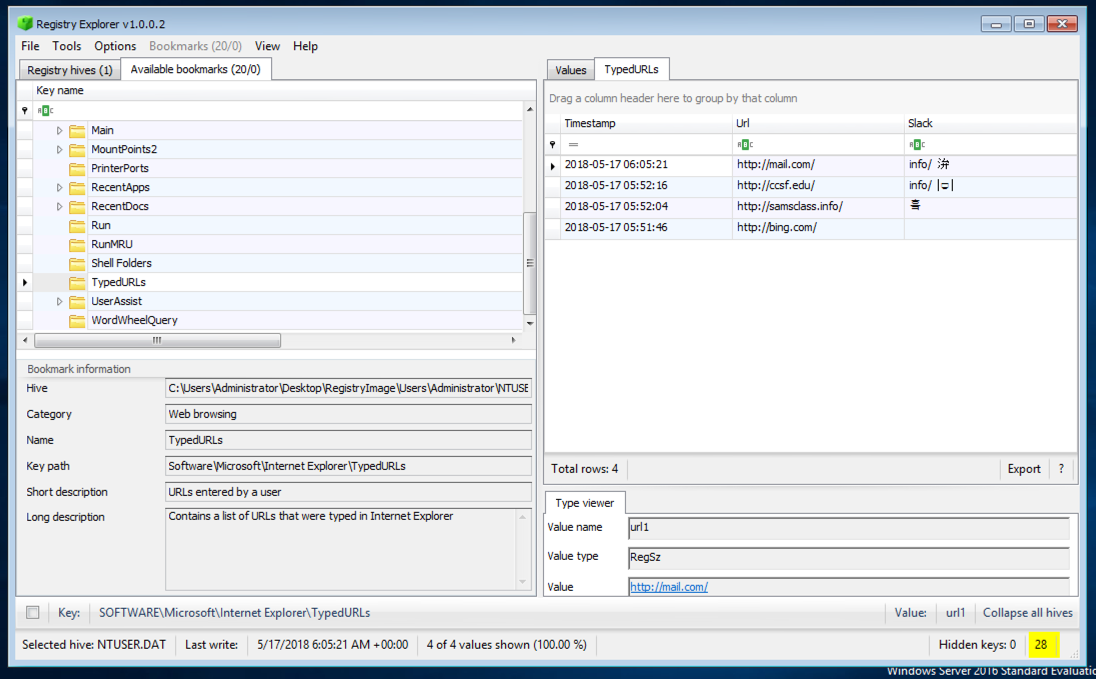
In Registry Explorer, in the top left pane, click the "Available bookmarks" tab. Scroll down and click TypedURLs.
The top right pane shows the URLS that have been visited, as shown below:
In Registry Explorer, in the top left pane, expand the UserAssist key.
Several subkeys with long names consisting of random letters and numbers appear, as shown below.
Expand one of the subkeys and click the Count subkey.
If the upper right pane of Registry Explorer is empty, expand another subkey and click its Count subkey instead, until you find a subkey containing values.
The upper right pane of Registry Explorer now shows strange unreadable "Value Name" entries. Believe it or not, these are obfuscated with ROT-13--moving each letter 13 values in the alphabet, an ancient and very weak form of encryption.
The upper right pane of Registry Explorer shows the deobfuscated "Program Name" values in the second column, as well as the number of the times the program has been run, the number of times it has been in focus, the "Focus Time", and the "Last Executed" time.
Hunt through the values until you find "Microsoft.Windows.Explorer" in "Program Name" column, as highlighted in the image below:
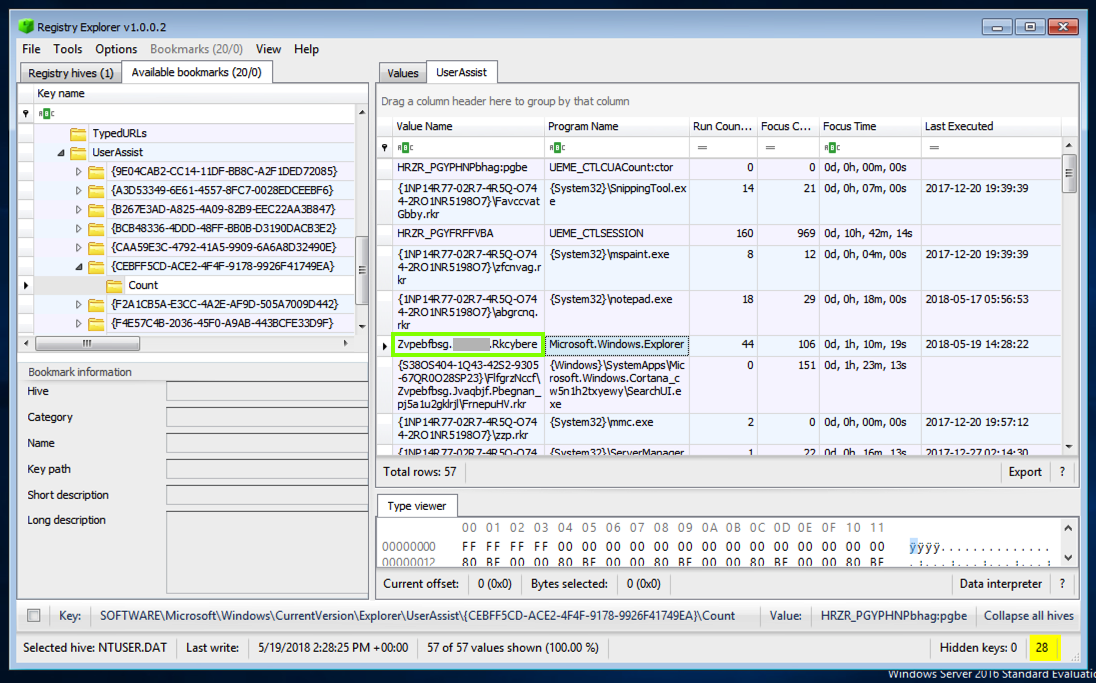
Find the second word in this obfuscated name, which is redacted in the image above, and enter it in the form below to record your score in Canvas.
If you don't have a Canvas account, see the instructions here.
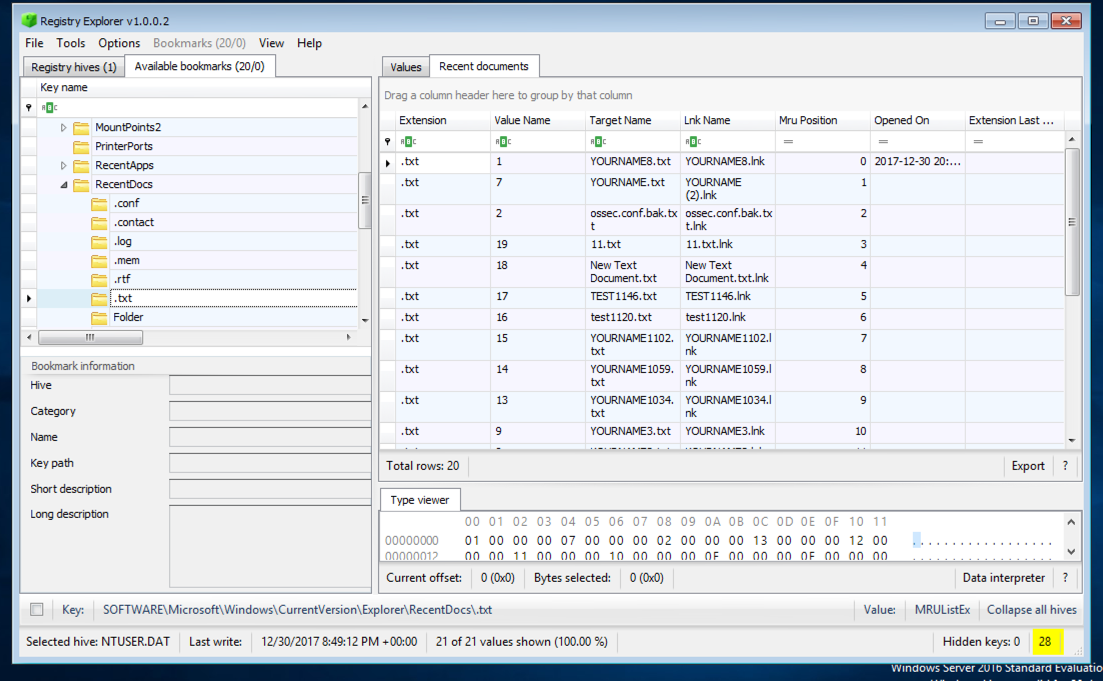
In Registry Explorer, in the top left pane, expand RecentDocs. A list of filename extensions appears. Click .txt.
The top right pane shows the .txt files that were used recently, as shown below:
However, this key is not visible in an acquired registry image. Instead, you will see two control sets, and you must determine which one was "Current" at the last login.
In Registry Explorer, click File, "Load Offline Hive". Navigate to your Desktop, and open this file:
RegistryImage\system
If a box pops up titled "Dirty hive detected!", click No.
If a box pops up titled "Load dirty hive?", click Yes.
In the left pane of Registry Explorer, click the "Registry hives" tab.
In the system hive, expand ROOT and click Select, as shown below:
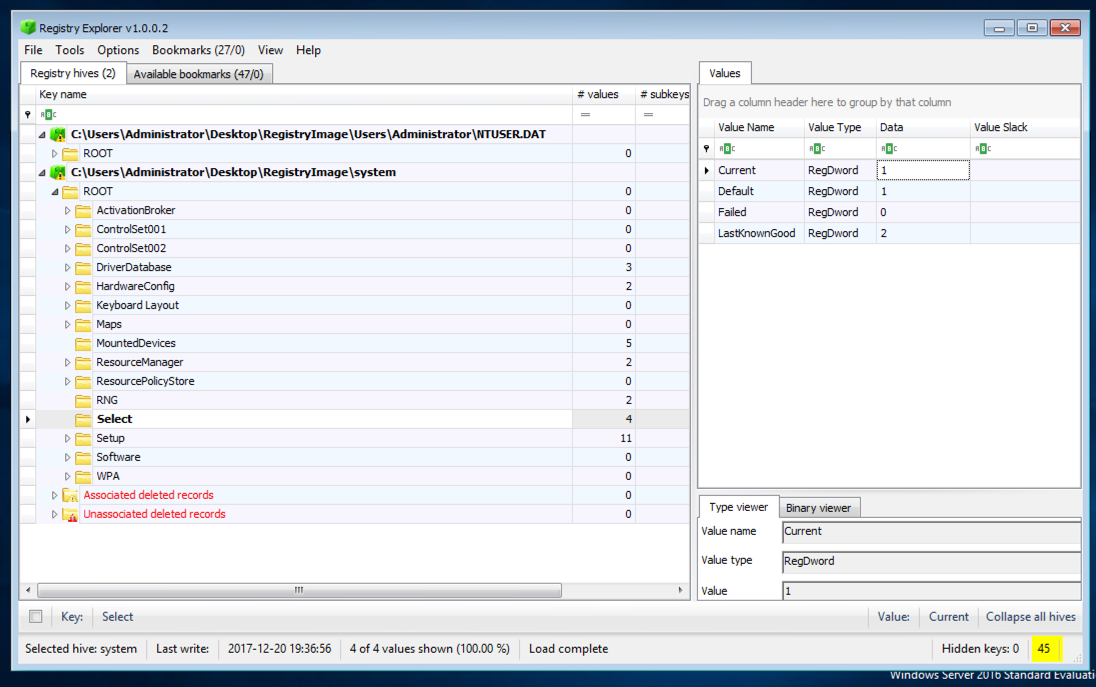
In the upper right pane, you see four values:
In Registry Explorer, in the top left pane, click the "Available bookmarks" tab.
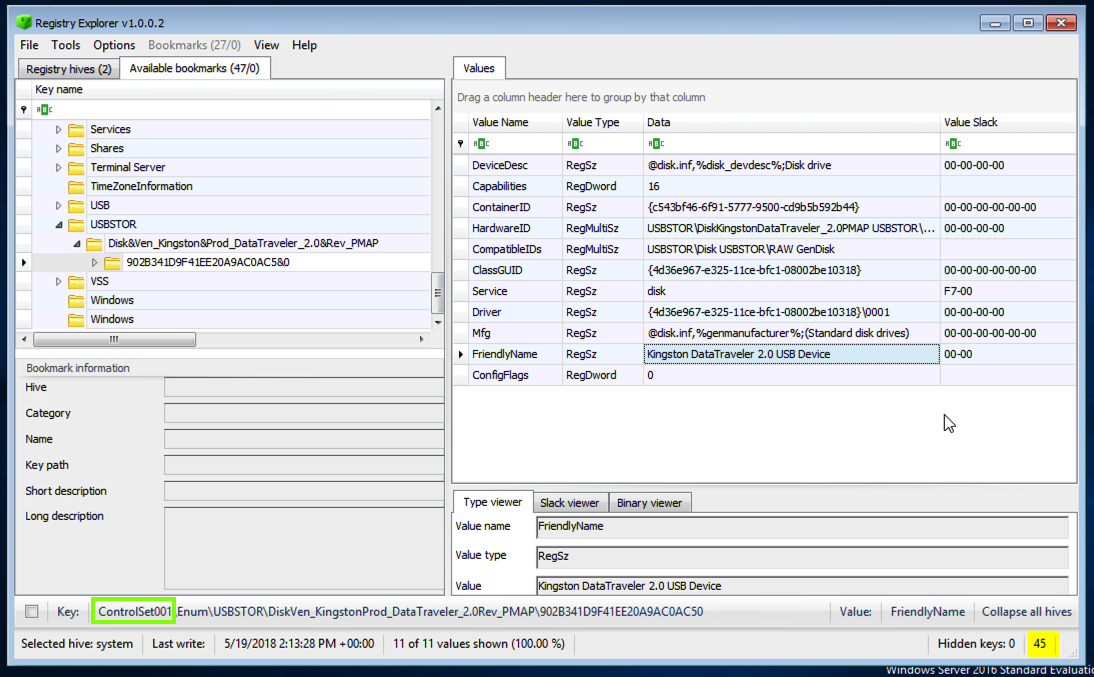
Expand the USBSTOR key. A key appears here for each USB storage device that has been connected, as shown below.
Expand the key and select the subkey with a long random name, as shown below.
In the upper right pane of Registry Explorer, find the "FriendlyName value.
This should be a readable brand name of the device, as shown below.
At the bottom of the Registry Explorer window, notice that it has automatically selected the correct ControlSet, as outlined in green in the image below.