NIST 800-53 requirements ATM SC-20 and IPv6 DNS Servers
Today @lil_lost
asked about this topic. Here are my thoughts:
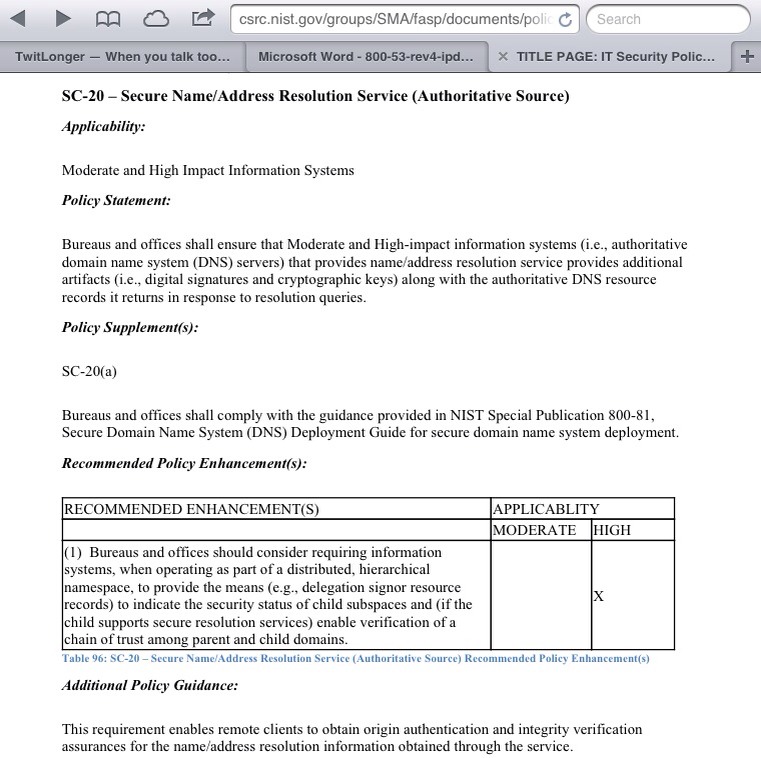
Here's the SC-20 requirement:
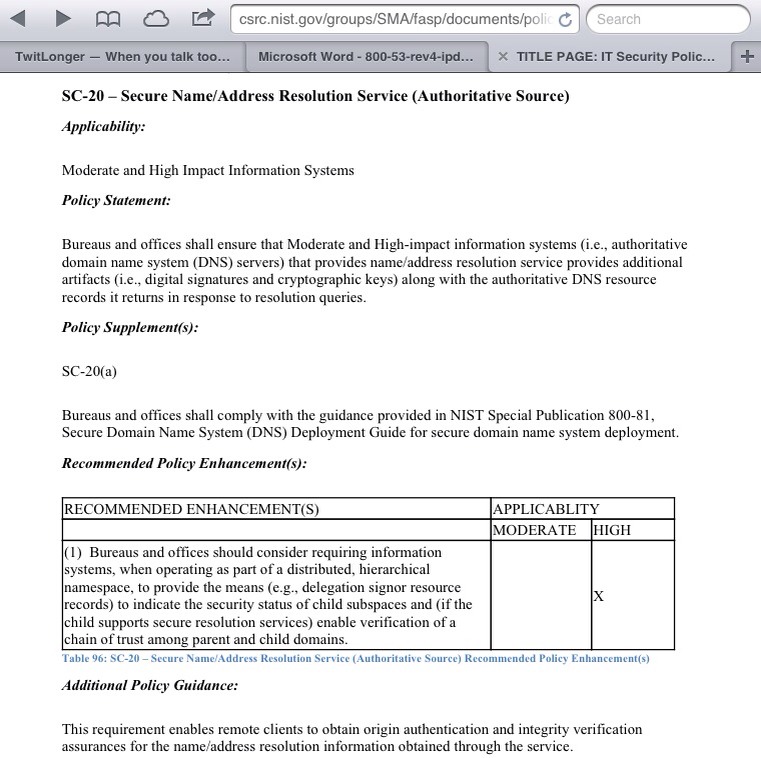
From
http://csrc.nist.gov/groups/SMA/fasp/documents/policy_procedure/PHB_09172007compat_Final_651.doc#_Toc193514597
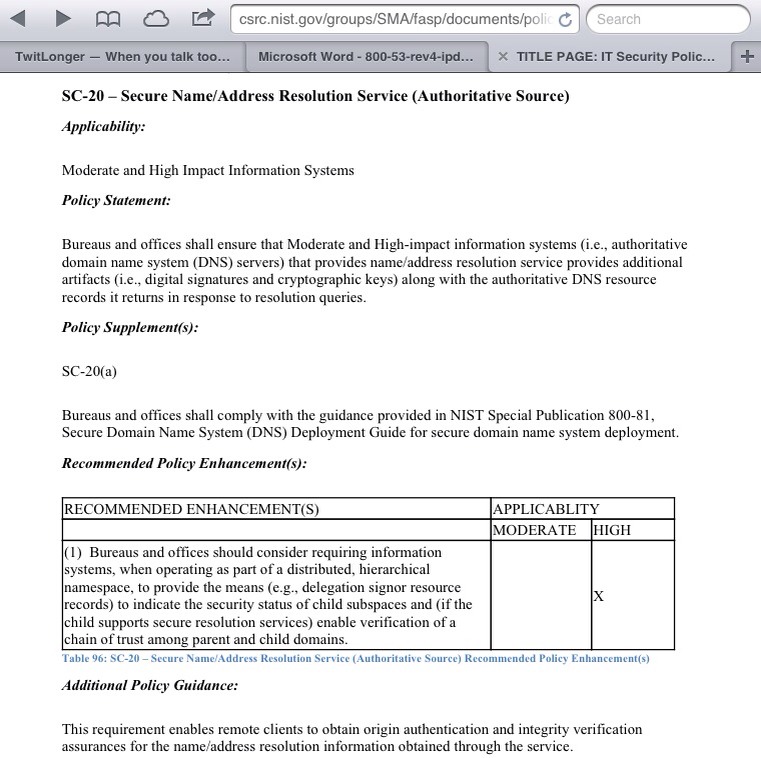
NIST SP 800-81 "Secure Domain Name System (DNS) Deployment Guide"
specifies a lot of security measures, including DNSSEC:
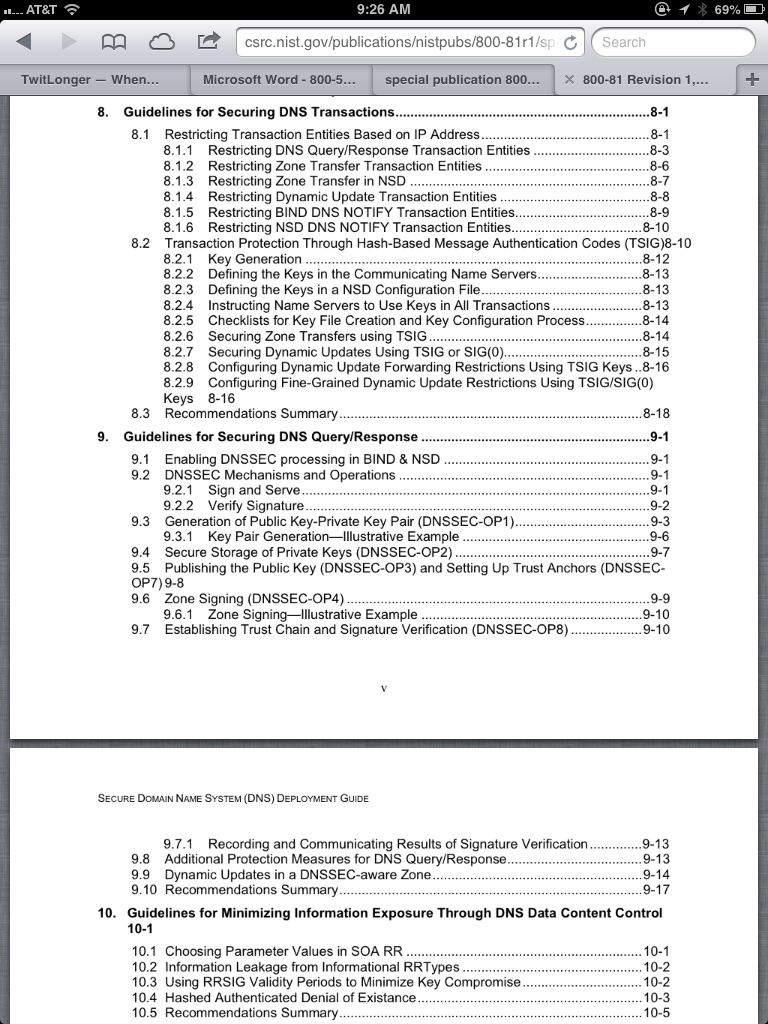
From
http://csrc.nist.gov/publications/nistpubs/800-81r1/sp-800-81r1.pdf
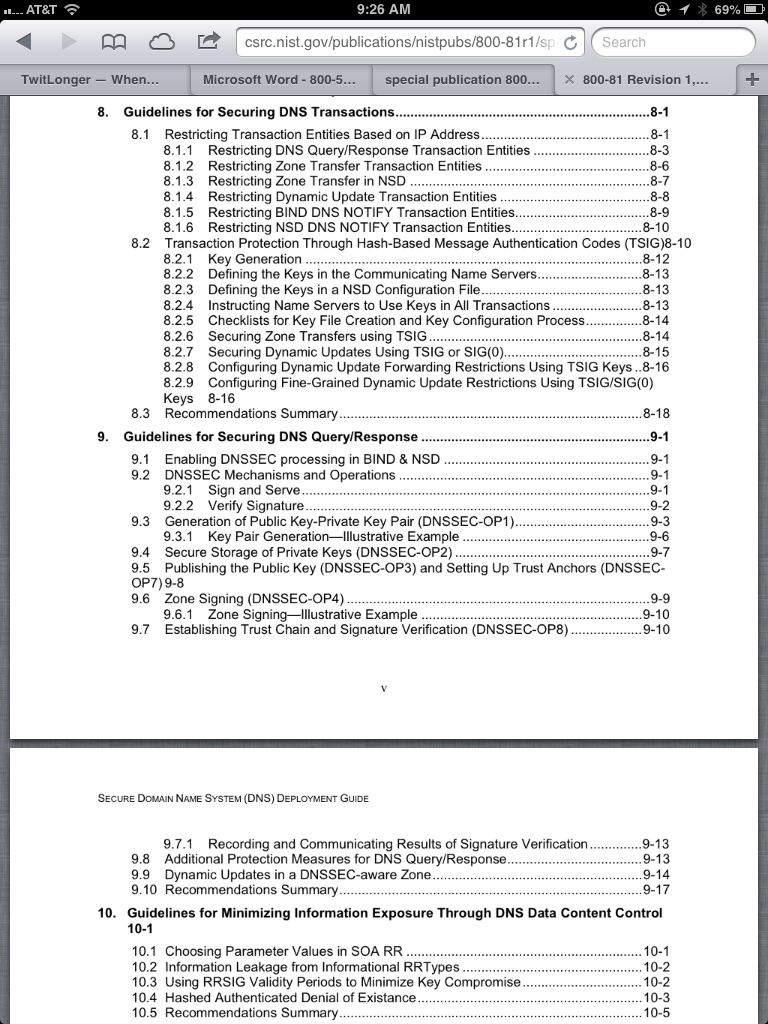
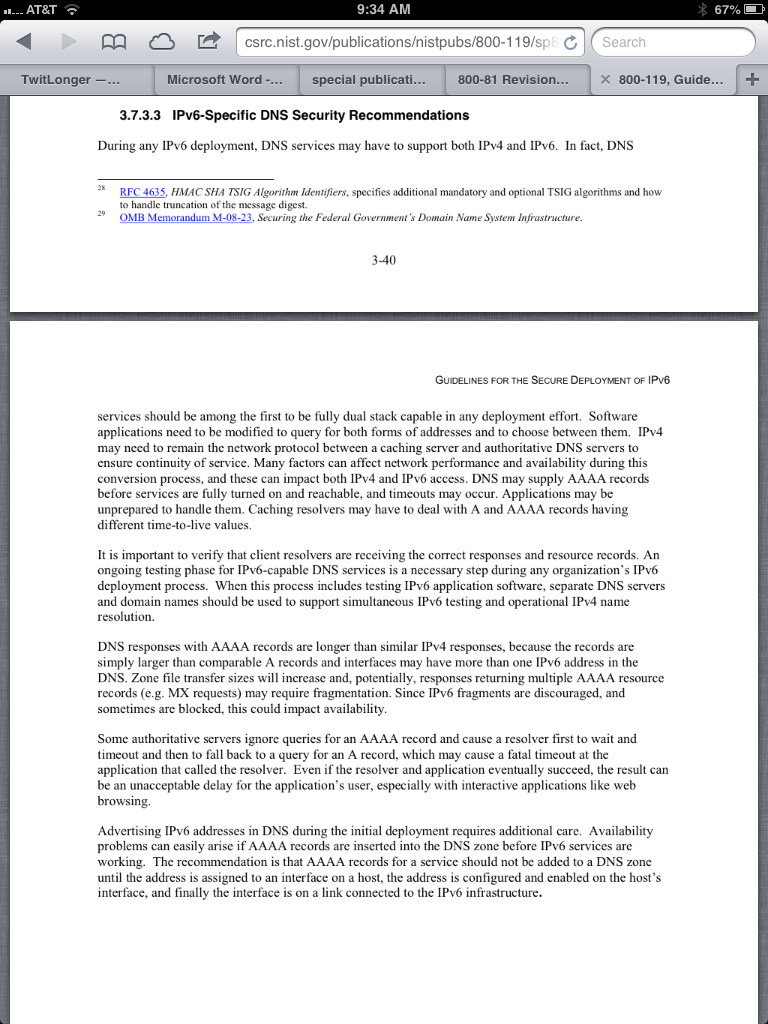
NIST Special Publication 800-119: "Guidelines for the
Secure Deployment of IPv6" covers DNS deployment in
section 3.7, with this summary:
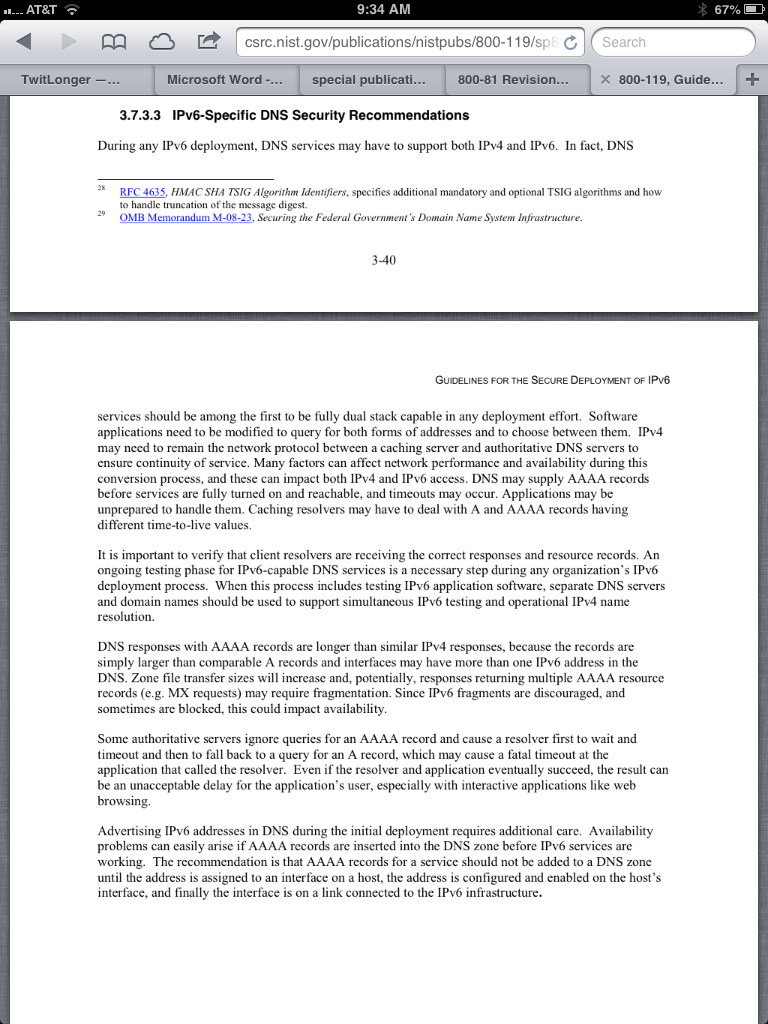
From
http://csrc.nist.gov/publications/nistpubs/800-119/sp800-119.pdf
The main security issues in deploying IPv6 DNS servers are:
- Deploying DNS server addresses to client machines via IPv6 is difficult, because of differences in implementations of SLAAC (Stateless Address Autoconfiguration) and DHCPv6. At present, if you want to service Windows machines, Macs, and Linux machines, the best solution is to deploy addresses using both SLAAC and DHCPv6, which can result in multiple addresses on some clients, as explained here: http://www.howfunky.com/2012/05/north-american-ipv6-summit-advanced.html
- Planning a system to assign IPv6 addresses to servers, clients, and subnets is very complex, and typically takes years and several generations of deployment to get right. Some guidance is available here: http://www.getipv6.info/index.php/Planning_IPv6_Deployment
- Using the wrong address types in AAAA records, such as link-local addresses (fe80::)
- Old clients, mainly Macs, had the problem of "IPv6 brokenness"--when a DNS query returned both A and AAAA records, they would attempt to access the resource over IPv6, fail, and not try over IPv4 at all. In 2011, this problem affected about 0.2% of clients, but by June 6, 2012, it was no longer a significant problem.
- Packet amplification DoS attacks become more powerful when DNS servers deploy IPv6 and/or DNSSEC because the responses are larger.
- If DNS responses are larger than 512 bytes, various problems can occur, as detailed here:
Preparing for a world consisting of larger DNS responses. | Internet Systems Consortium
Here are some serious IPv6 security issues that must be considered,
although they are not DNS-specific:
- Automatically configured tunnels such as Teredo and ISATAP can lead to misdirected traffic and man-in-the-middle attacks
- IPv6 traffic may not be properly filtered by firewalls and other security devices, especially when tunneled
- IPv6 addresses may not be properly handled by custom applications, configuration utilities, and log files
- IPv6 introduces new network attacks, such as Neighbor Discovery DoS attacks and attack obfuscation with Extension Headers. As these attacks become known, they will require updates to firewalls, IDS devices, and other systems.
Posted 10:18 am 12-12-2012 by Sam Bowne