M5: AndroBugs (10 pts)
What You Need for This Project
- A Kali virtual machine
- You should have that already set up from previous projects
Purpose
To practice using AndroBugs,
a really fast Android vulnerability scanner.
Installing AndroBugs
On Kali, in a Terminal,
execute these commands, to install
AndroBugs and scan the GenieMD APK file.
git clone https://github.com/AndroBugs/AndroBugs_Framework.git
cd AndroBugs_Framework
wget https://samsclass.info/128/proj/genie.apk
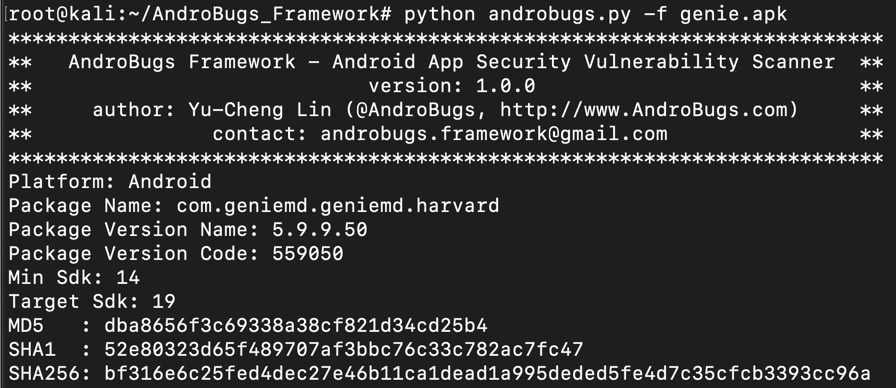
python androbugs.py -f genie.apk
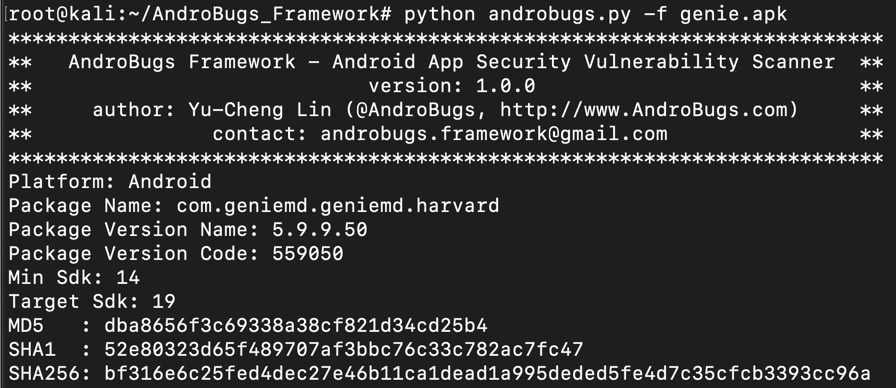
The scanner starts,
as shown below.
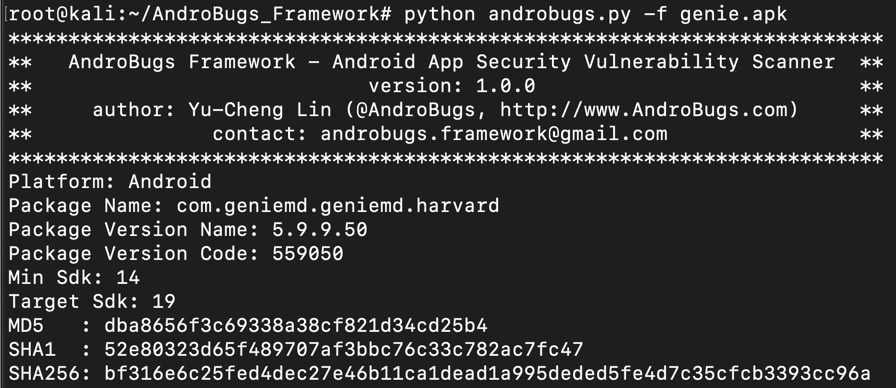
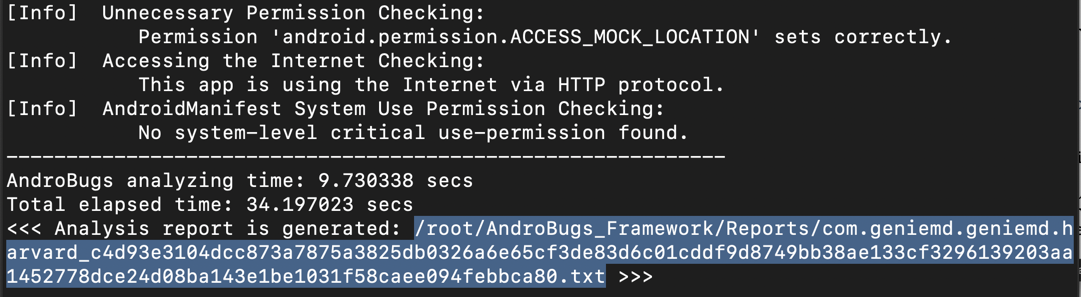
Within a minute, the scan finishes.
It prints out a long report
filename. Carefully copy the whole report name,
which is highlighted in the image below.
Viewing the Report
On Kali, in a Terminal, execute this command,
replacing filename with the correct filename
on your system:
nano /root/AndroBugs_Framework/Reports/com.geniemd.geniemd.harvard_c4d93e3104dcc873a7875a3825db0326a6e65cf3de83d6c01cddf9d8749bb38ae133cf3296139203aa1452778dce24d08ba143e1be1031f58caee094febbca80.txt
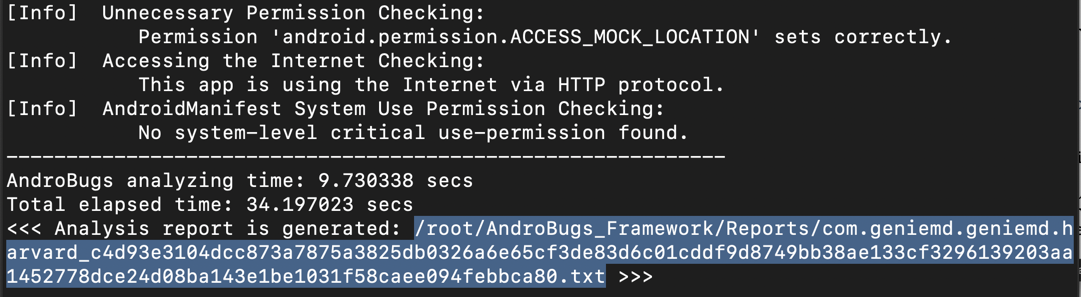
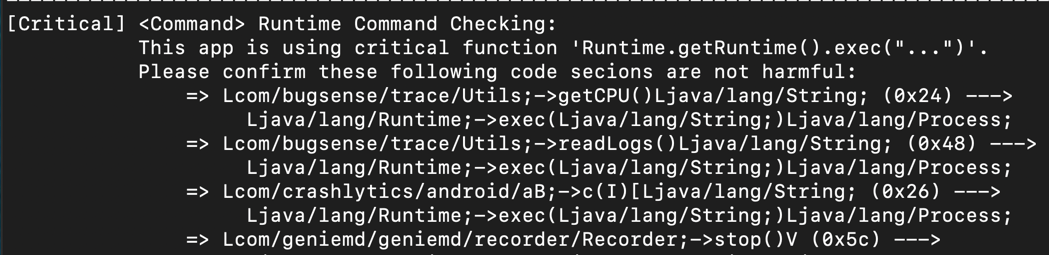
[Critical] <Command> Runtime Command Checking
This is the first vulnerability found, and it's
pretty scary.
These functions use Java to construct
Android shell commands, which frequently leads
to command injection flaws.
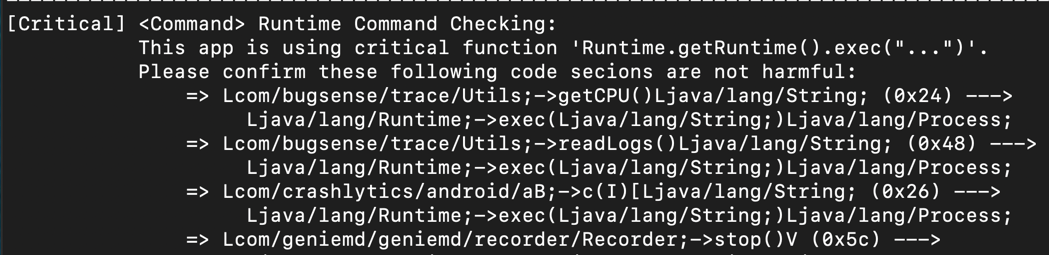
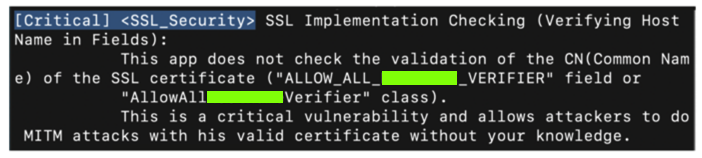
SSL Validation Flaws
Scroll down to find the SSL validation
error we exploited in a previous project.
This scanner provides a lot of information about
flaw, as shown below.
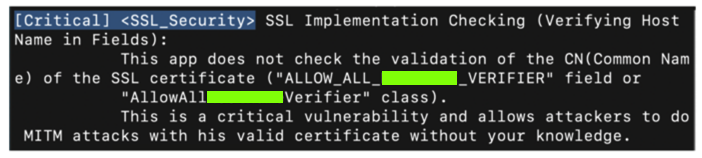
Find the text covered by a green box
in the image above. Enter it into
the form below to record your success.
M15: Recording Your Success (10 pts)
Use the form
below to record your success.
Converted to a CTF 2-28-19