Project 2C: Katoolin (10 pts extra)
What you need
- A Debian server on the Google Cloud, which you set up in a previous project
Purpose
To use Katoolin and other software to convert the
Debian server into an attack platform with
some Kali tools, including Metasploit.
Google Cloud Server
If you don't have a Google Cloud Server
set up, see
these instructions.
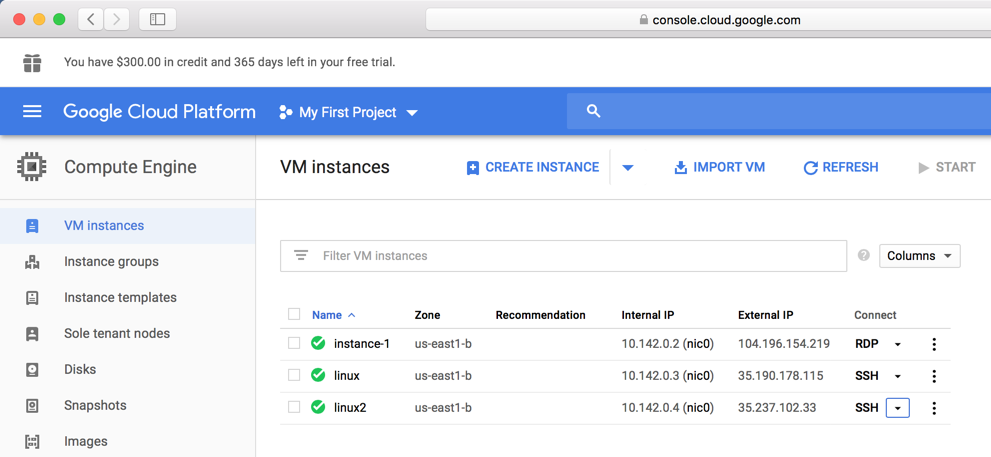
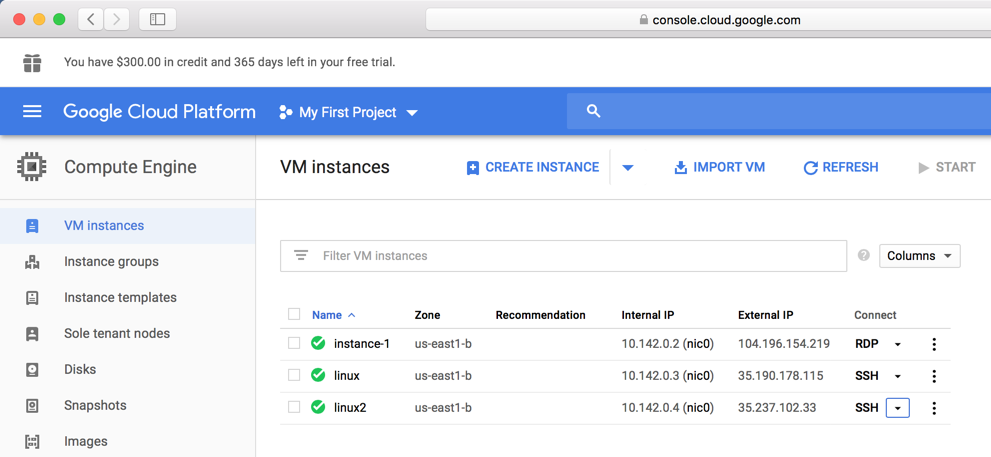
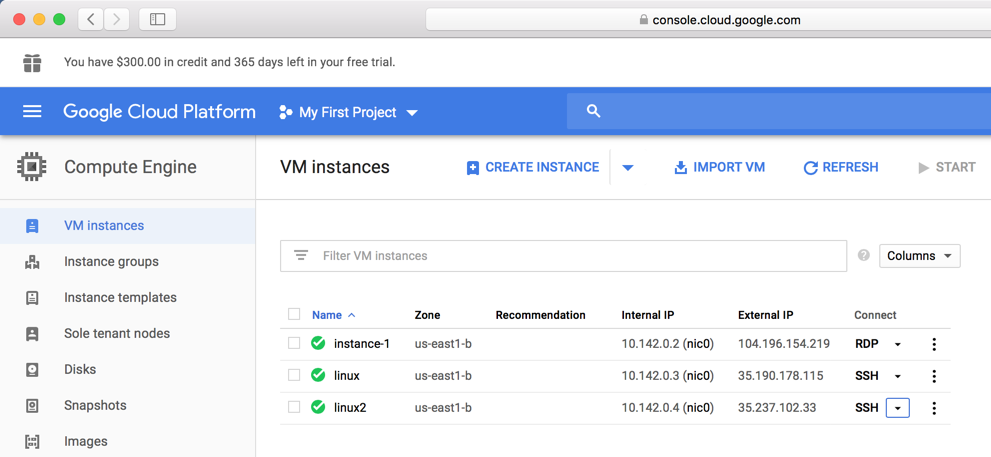
Google Cloud Platform Console
Open a Web browser to this URL:
https://console.cloud.google.com
Log in to Google, and you should
see your
Google Cloud Platform Console.
On the left side, click "Compute
Engine".
as shown below.
Installing Katoolin
Execute these commands:
sudo apt update
sudo apt install git dirmngr -y
git clone https://github.com/LionSec/katoolin.git
sudo cp katoolin/katoolin.py /usr/bin/katoolin
sudo chmod +x /usr/bin/katoolin
sudo katoolin
Katoolin opens,
as shown below.

Using Katoolin to Add Kali Repositories
From the Katoolin kat > prompt,
enter these options:
- 1 Add Kali repositories & Update
- 1 Add kali linux repositories
- 2 Update
- Ctrl+C Quit Katoolin
You should see the "imported: 1" message,
as outlined in red in the image below.
If you see a "No data" error, repeat the
command, as I did in the image below.

Installing Metasploit and Nmap
Execute these commands:
sudo apt install metasploit-framework -y
sudo apt install nmap -y
Using Katoolin to Remove Kali Repositories
To avoid breaking the server, we need to remove
the Kali repositories when installing normal
software.
Execute this command to start
Katoolin:
sudo katoolin
From the Katoolin kat > prompt,
enter these options:
- 1 Add Kali repositories & Update
- 3 Remove all kali linux repositories
- Ctrl+C Quit Katoolin

Finding your Windows Cloud Server's IP Address
In your
Google Cloud Platform Console,
find your Windows cloud server's
IP
address, as outlined in red in the image
below.

Scanning your Windows Server
Execute these command, replacing the IP
address with
your Windows cloud server's
IP
address.
sudo nmap 10.142.0.2
Your server has the usual Microsoft
ports open, as shown below.
Find the service name, which is
covered by a green box in the image below.
Enter it into the form below.

2C.1: Recording Your Success (10 pts extra credit)
Use the form
below to record your score in Canvas.
If you don't have a Canvas account, see
the instructions
here.
Sources
https://github.com/LionSec/katoolin
Installing metasploit on a cheap Debian VPS
deb2kali
A Script to Convert Debian Linux (8.1) into Kali Linux
configure multiple sshd instances on debian 8 (jessie) systemd
systemd unit file for dropbear
How to automatically execute shell script at startup boot on systemd Linux
How to Install VNC w/ GNOME on Debian VPS
How to Install and Configure VNC on Debian 9
Posted 9-6-18
Added installation of dirmngr 10-10-18